INSIGHTAPPSEC
Efficiently Reduce Risk in Modern Web Applications
InsightAppSec performs black-box security testing to automate identification, triage vulnerabilities, prioritize actions, and remediate application risk.
- Dynamic Application Security Testing (DAST)
Get actionable, accurate insights with an industry leading attack framework and library - Replay attacks & validate fixes
Speed up remediation and reduce dev team back-and-forth by providing self-service access - Integrate into dev workflows
Better prevent risk early by adding security testing as part of the build pipeline and integrating dev and sec team workflows
Secure the Modern Web
Automatically assess modern web apps and APIs with fewer false positives and missed vulnerabilities.
Collaborate with Speed
Fast-track fixes with rich reporting and integrations, and inform compliance and development stakeholders.
Scale with Ease
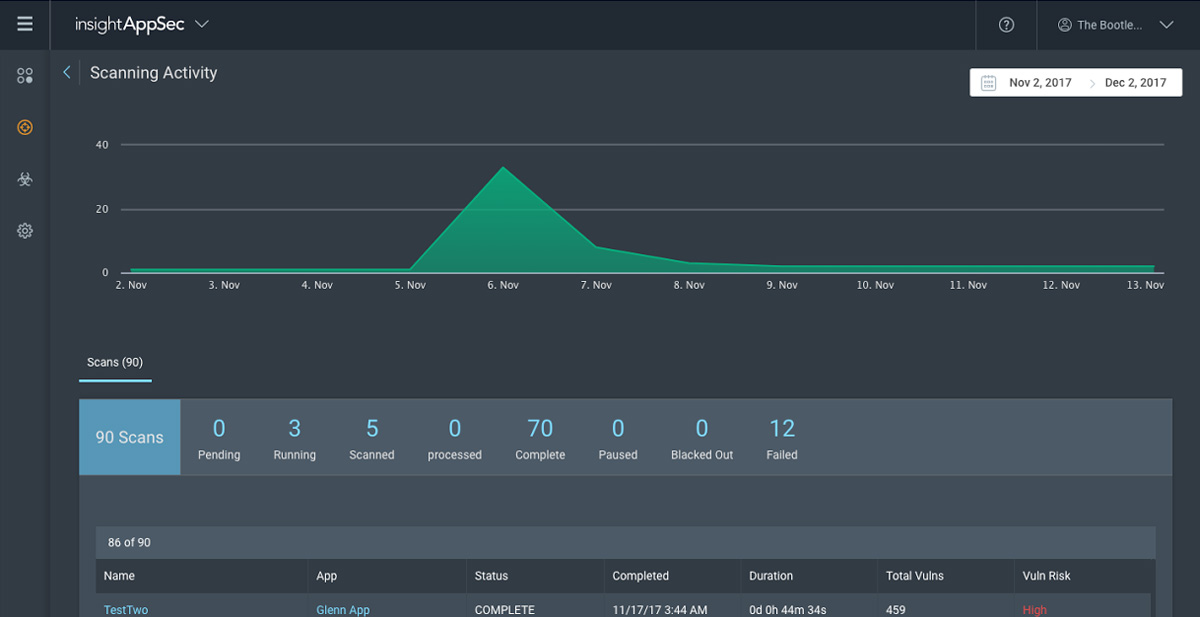
Effectively manage the security assessment of your application portfolio, regardless of its size.
Key Features
Automatically crawl and assess web applications to identify vulnerabilities like SQL Injection, XSS, and CSRF.
Accomplish More with InsightAppSec
Accurate and reliable Dynamic Application Security Testing (DAST)
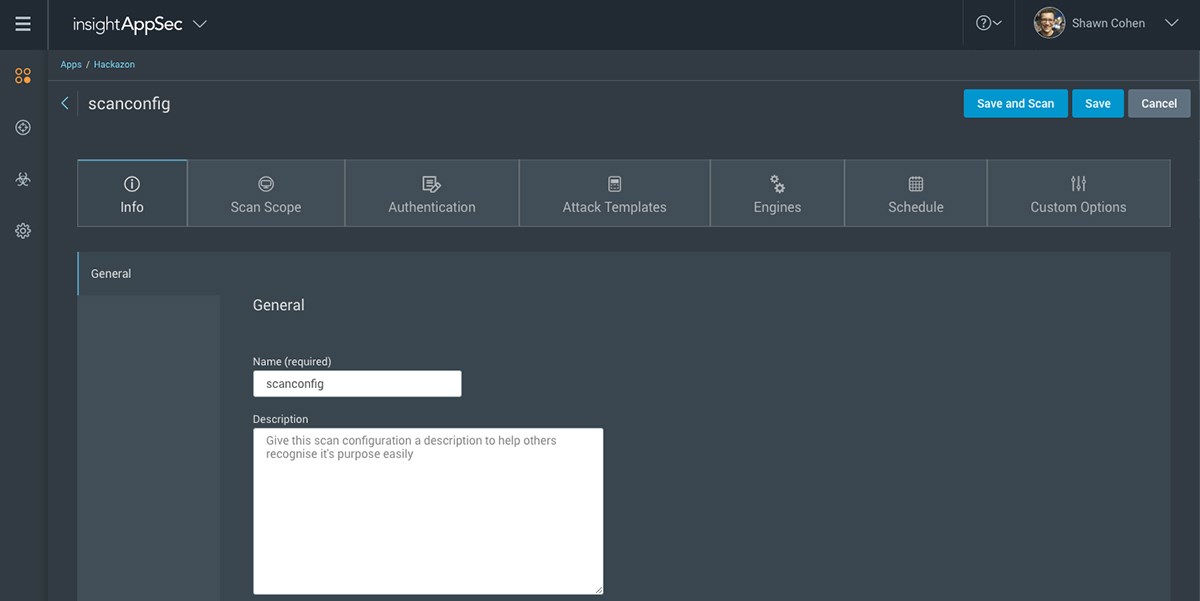
Start Scanning in as Few as Five Minutes
The modern UI and intuitive workflows built on the Insight platform make InsightAppSec easy to deploy, manage, and run. Scan applications hosted on closed networks with the optional on-premise engine.
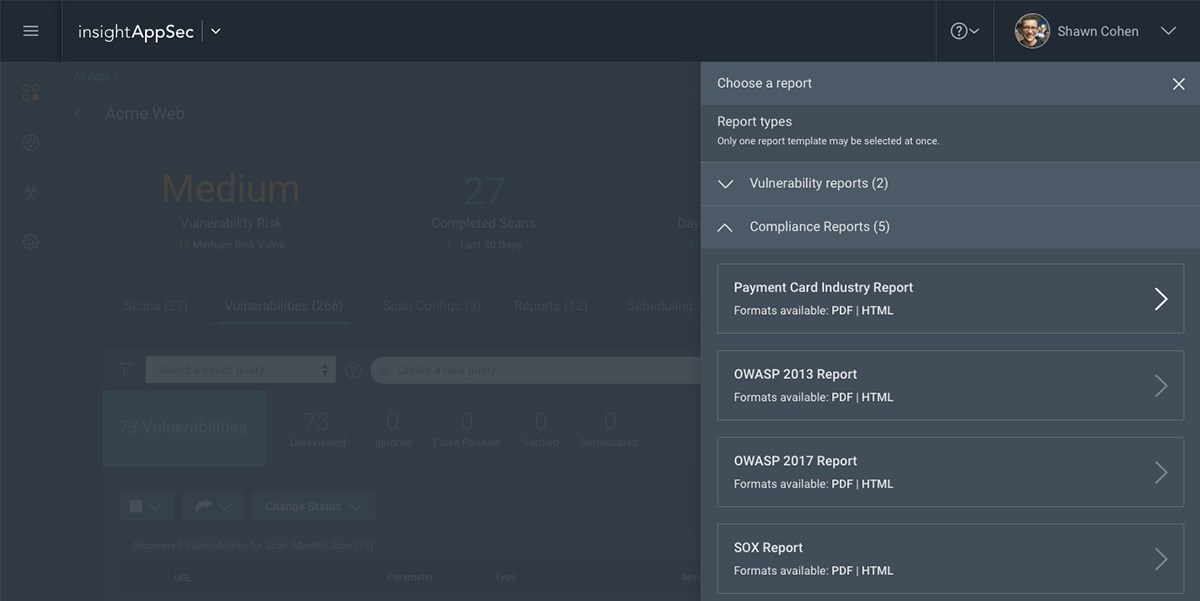
Learn MoreUnderstand Your Compliance Risk
InsightAppSec assesses and reports on your web app's compliance to PCI-DSS, HIPAA, OWASP Top Ten, and other regulatory requirements.
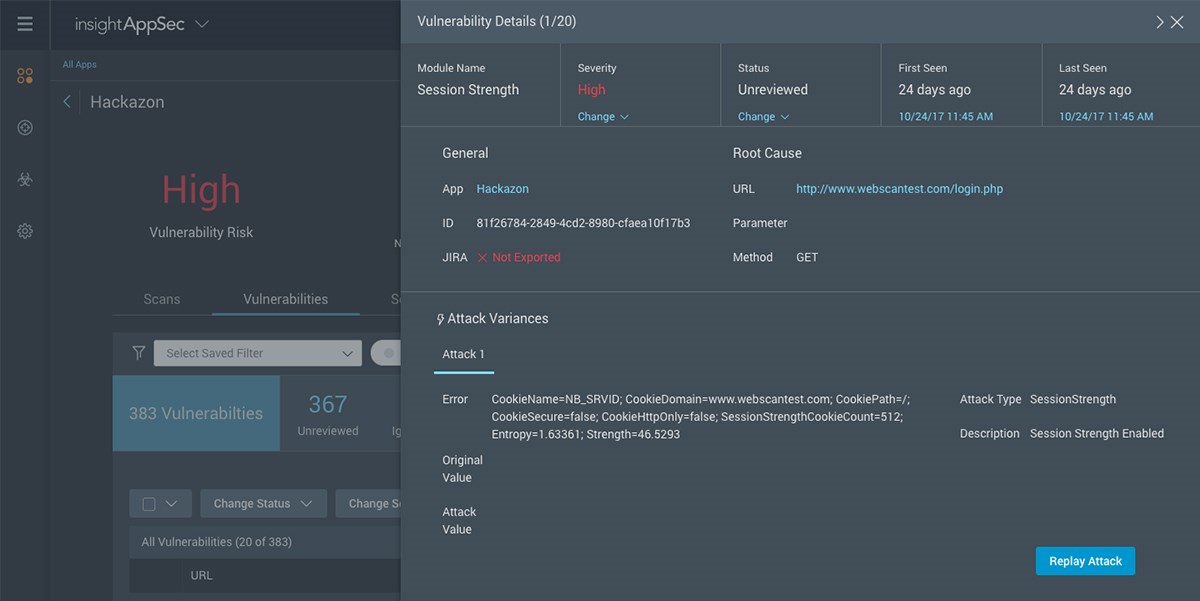
Learn MoreWork Better with Development
Rich technical detail and context for each vulnerability finding speeds remediation efforts, while integrating with Atlassian Jira gives developers full visibility within their existing workflows. Even better, the Attack Replay feature lets developers validate vulns and test source code patches on their own.
Learn MoreTechnology Integrations
Enhance InsightAppSec's capabilities, more effectively leverage vulnerability findings, and reduce friction between security and DevOps by integrating InsightAppSec with components in the DevOps toolchain.
Learn how InsightAppSec can integrate with your:
ITSM/ITOM & DevOps tools
Our Services
Managed AppSec
Leverage Rapid7 experts to manage your application security risk. Our professionals run your scans, validate vulnerabilities, and prioritize findings.
Learn MoreDeployment Services
Lean on Rapid7 product consultants with decades of security experience to set up your application security program up for success.
Learn MoreTraining and Certification
Get the most out of your application security tools with specialized training and certification for InsightAppSec.
Learn MoreTotal Risk Coverage Program
Take a holistic approach to securing your web apps, from the identification and remediation of vulnerabilities to the detection and prevention of real-time attacks.
Learn MoreScan your own app with an InsightAppSec free trial
Rapid7 creates innovative and progressive solutions that help our customers confidently get their jobs done. As such, the development, release, and timing of any product features or functionality described remains at our discretion in order to ensure our customers the excellent experience they deserve and is not a commitment, promise, or legal obligation to deliver any functionality. In addition, this information is intended to outline our general product direction and should not be relied on in making a purchasing decision.