InsightIDR Accelerates Threat Detection from Hours to Seconds for Barton Associates

Industries
Company Size
Products
Customer Website
About Barton Associates
Barton Associates is a leading healthcare recruitment and staffing company. Founded in 2001, the firm provides locum support for leading healthcare organizations (HCOs) across the US in a variety of practice areas. This market for short-term medical practitioners is now estimated to be worth as much as $4 billion. From humble beginnings in a small office on Massachusetts’s North Shore, Barton Associates has grown to more than 700 employees in 10 offices across seven states.
For Daniel Goldenberg, director of IT infrastructure at the firm, part of his role is to find a way to face down the growing online threat to data-centric organizations like Barton Associates. Recruitment firms are particularly highly prized as they contain large stores of wide-ranging personally identifiable information (PII) and financial details on their clients, as well as corporate data from employers.
Challenge
Recruitment firms are particularly highly prized as they contain large stores of wide-ranging personally identifiable information (PII) and financial details on their clients, as well as corporate data from employers. A major data breach could have a huge impact on customer confidence in the brand, as could a ransomware-related outage that leaves job-seekers and employers unable to connect.
Like many organizations, Barton Associates has been on a journey to cloud computing adoption in a bid to drive improved business agility and cost savings. Over the past few years, Goldenberg has seen the firm transform from one powered entirely by on-premises servers to one almost completely cloud-based, with Amazon Web Services (AWS) and other cloud providers helping to help optimize the business.
However, he realized that outsourcing to the cloud does not mean being able to hand over responsibility for cybersecurity. So a search began for a provider that could offer automated threat detection and response and vulnerability management capabilities tightly integrated into Barton Associates’ cloud infrastructure.
Solution
The firm chose InsightIDR for their detection-focused cloud SIEM after careful consideration, which included a few “test drives” with leading competitors.
“We did an evaluation across the board with a couple of major SIEM players. We understood the pros and cons, and with the Rapid7 Insight platform, we felt like we got a lot out of the box,” explains Goldenberg.
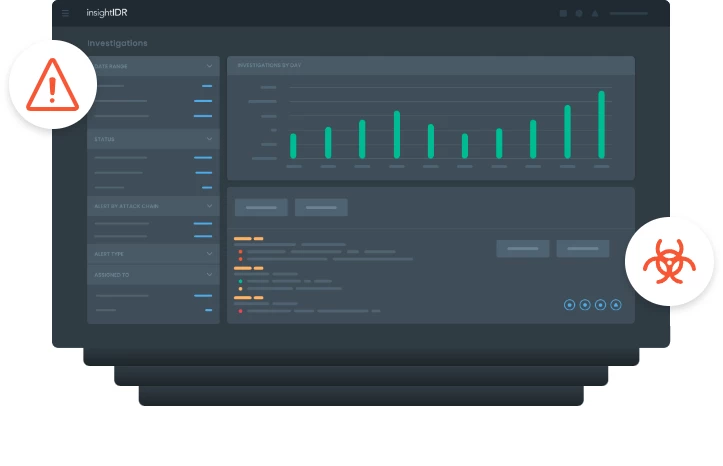
InsightIDR is Rapid7’s flagship threat detection and response SIEM, enabling organizations to respond with speed and confidence to attacks by spotting the behavior behind security breaches. It centralizes security data from across the organization, applying behavior analytics and threat intelligence to drive insight via an intuitive graphical interface. Machine learning baselines user behavior to alert on use of stolen credentials or anomalous lateral movement, while Rapid7 global intelligence feeds into Attacker Behavior Analytics (ABA) for detection of external attacks.
Barton Associates also chose Rapid7's InsightVM platform, which uses the same underlying agent to provide real-time insight into vulnerabilities. Risk-based attacker analytics help firms to automatically prioritize the most urgent ones and the focus is on collaboration across IT to ensure any issues are remediated seamlessly.
Rapid7 means rapid response
Goldenberg and his team were delighted with the results, generating insight from the platform “very quickly” across the firm’s dynamic cloud environment.
“Integrating into our kind of cloud has been huge. The Insight Agent is deployed right on as we're spinning up each server,” he explains. “We need that insight on all new endpoints that are popping up to keep track from a regulatory and a security standpoint. It makes sure that we're locking things down appropriately—fully patching everything and ensuring that it's a clean box going into production.”
The IT security environment before and after Rapid7 “is not even a comparison,” Goldenberg adds, explaining that automated alerts on lateral detection, abuse of privileges, and other events have helped him greatly accelerate incident response.
“We started off with a hammer and chisel, looking at everything very manually. Now you have everything orchestrated and automated,” he says. “I can jump on a laptop and take care of an incident or escalate it to an engineer right then and there. It's taken the detection time from what could have been hours or days down to seconds.”
Goldenberg was also quick to praise Rapid7’s honesty and the close working relationship forged with his team. “With Rapid7, you're engaging with a professional team where you know exactly what you're going to get out of the partnership,” he concludes. “There are no surprises that you sometimes get when working with some consulting partners or vendors.”
InsightIDR was XDR before XDR was a thing