One of the most valuable features of ControlsInsight is its ability to prioritize security control improvement guidance as a sequence of next steps. It does this by grading each security control configuration and ordering the guidance for each configuration by grade. ControlsInsight calculates the grade for each security control configuration based upon the coverage of that configuration across all assessed assets and a weight assigned to that configuration.
Coverage
Coverage is the measure of fully implemented security controls across all scanned assets. An assessment of each asset results in a state being assigned to each security control configuration for that asset. The configuration states currently assigned by ControlsInsight are listed in the table below:
| Configuration State | Description |
|---|---|
TRUE | The evaluated condition matched the criteria of an implemented security control |
FALSE | The evaluated condition did not match the criteria of an implemented security control |
UNKNOWN | The condition could not be evaluated due to missing or insufficient data |
NOT APPLICABLE | The condition was not evaluated because it does not apply to the asset |
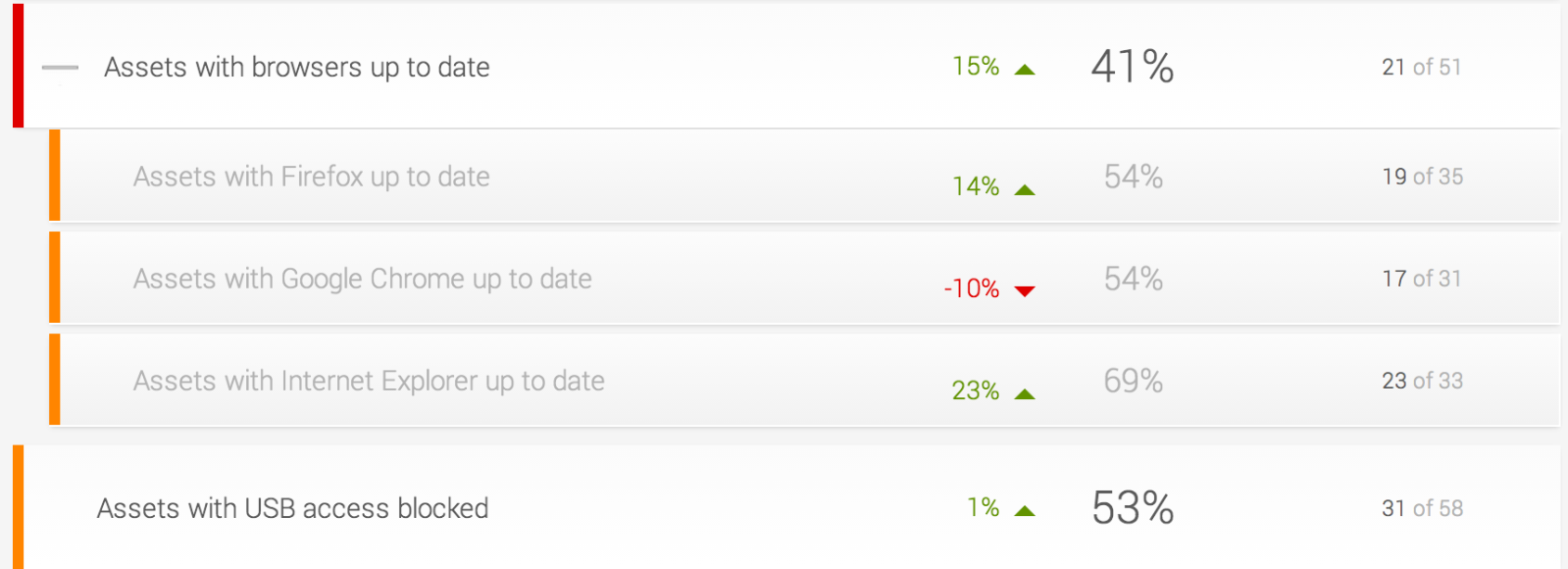
Coverage is listed on the Status panel. In the following screenshot, 58 assets have been scanned and assessed. The Assets with USB access blocked security control has 53 percent coverage or 31 of 58 assets assessed as TRUE. The Assets with browsers up to date security control has 41 percent coverage or 21 of 51 assets assessed as TRUE. Note that there are seven assets with no browser installed and the configurations for these assets have the NOT APPLICABLE configuration state, which is completely ignored when calculating the coverage of a security control.
Weight
The ControlsInsight data model defines a relative weight for each security control. These weights are determined by Rapid7 research including security industry standards such as NIST Recommended Security Controls (https://www.nist.org/nist_plugins/content/content.php?content.18), SANS Top 20 Critical Security Controls (https://www.sans.org/critical-security-controls/guidelines.php), and Australian DSD Top 35 Mitigations (https://www.dsd.gov.au/infosec/top-mitigations/top35mitigationstrategies-list.htm). Security control weights are actually applied at the configuration level so that security control configuration grades may be compared across security controls.
Next Steps
Calculation of grades for each security control use the coverage and weights explained above. These grades are used to order the recommended guidance in the step-by-step list as seen below. The combination of coverage and weight help ensure that the guidance with the biggest impact on overall security appears at the top of the list of steps.
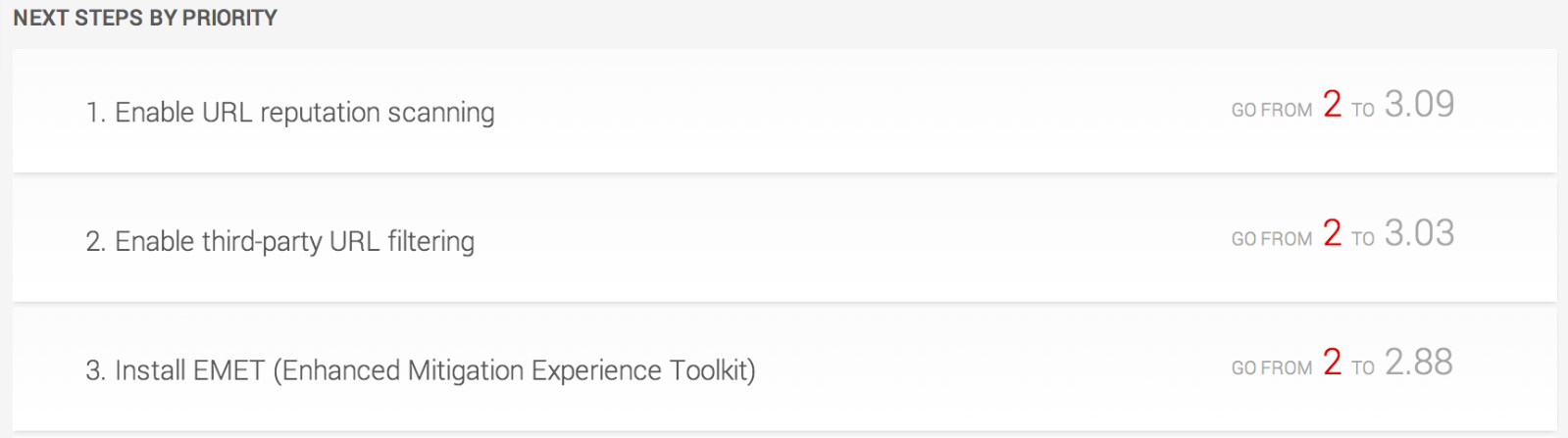
Additionally, the improvement in the overall grade that could be achieved by applying the recommended guidance is listed for each step. In the example illustrated by the screenshot, the overall grade could be improved to 3.09 if Enable URL reputation scanning security control as indicated by the guidance is implemented.