All the perimeter protection in the world won't stop an attack that doesn't get checked by the security measures around your perimeter, assuming the perimeter is still a viable term in today's distributed, mobile, and virtual world. If an attacker were to drop a USB stick in a public area of your company, what are the chances that USB stick eventually finds a USB port? Pretty good. Granted that study was from a few years back, but I would speculate that the numbers haven't appreciably changed if you consider the success phishing campaigns still achieve, per the 2014 Verizon Data Breach Incident Report "...a phishing campaign of only ten messages has a better-than 90% chance of getting a click..."
The common element here is the human factor and trying to change their behavior. Back in January of 2013 several power plants were impacted by USB borne attacks. The technician "...unknowingly inserted an infected USB computer drive into the network, keeping a plant off line for three weeks." Three weeks of no power production can put a nice dent in the annual revenue and productivity numbers of any business. More recently a research team based in Berlin (Karsten Nohl and Jakob Lell) created BadUSB and presented at 2014 BlackHat to demonstrate the vulnerability of the commonly used USB port on most laptops. Rapid7 Security Strategist Trey Ford commented in this article that "...USBs have been used in a variety of attacks ranging from masquerading as CD ROMs (launching files via OS auto run permissions) to posing as keyboards, as well as being used to infect machines across air-gaps."
What does this all mean and what can you do about it? While disabling the USB port on all machines may cause a riot within your company, locking down USB ports on critical assets may be something you wish to do. The question is how do you verify that change happened and stays up to date? Rapid7's ControlsInsight allows you to tackle the USB challenge in several ways.
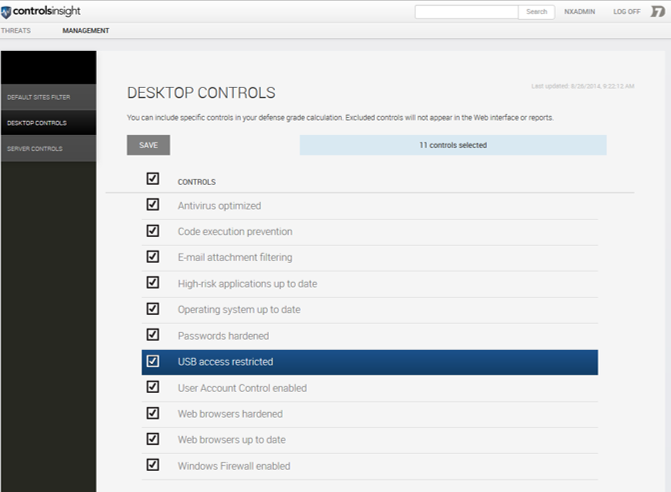
Option 1 is to lock down USB ports on all Windows desktops and use ControlsInsight to monitor and report on this:
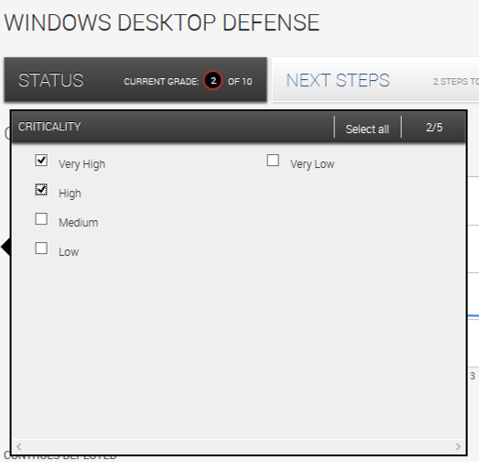
Option 2 is to perform the same lockdown, but filter which assets you are going to actively monitor and enforce this policy using ControlsInsight and the recently released RealContext™ filtering. In the image below, the administrator can choose to report on only High or Very High criticality assets and ensure these are the ones that have a more restrictive USB policy. The High and Very High criticality comes automatically from your tags created in Nexpose, you can also filter based on site, location, asset owner, or other custom tags.
USB drives are still a commonly used, and abused, tool in the home and office environment. They provide value but can be a path around your traditional security measures. Looking at ways to securely utilize USB in your world may save you 3 weeks of no power from your local utility.
Article Tags
Related blog posts

Vulnerabilities and Exploits
CVE-2025-20333, CVE-2025-20362, CVE-2025-20363 - Multiple critical vulnerabilities affecting Cisco products
Ryan Emmons

Vulnerabilities and Exploits
CVE-2025-10035 - Critical unauthenticated RCE in GoAnywhere MFT
Stephen Fewer

Vulnerabilities and Exploits
CVE-2025-7775: Critical NetScaler vulnerability exploited in-the-wild
Stephen Fewer

Vulnerabilities and Exploits
CVE-2025-6543: Zero Day Exploitation of NetScaler ADC and NetScaler Gateway
Stephen Fewer