Approximately a year ago, the Internet saw the beginnings of what would become the largest distributed denial of service (DDoS) attacks ever seen. Peaking at nearly 400Gbs in early 2014, these attacks started when a previously undisclosed vulnerability that would ultimately become CVE-2013-5211 was discovered. While these attacks were devastating and they received plenty of press, the style of attack was not new. In fact, it had been occurring routinely for years prior and continues to this day.
Denial of service (DoS) attacks are quite general -- anything that allows an attacker to deny access to a particular resource from its intended users is considered a denial of service attack. A distributed denial of service (DDoS) attack is a variant whereby the attack is made possible or more practical by utilizing more than one attacking system. One of the most common types of DDoS attack is one that simply overwhelms the target with network traffic/requests. One particularly nasty variant of this is what is called the distributed reflected/reflective denial of service (DRDoS) attack, where one or more attacking systems send UDP traffic to systems vulnerable to traffic amplification vulnerabilities but used forged source IP addresses belonging to the intended targets of the DRDoS attack. These traffic amplification vulnerabilities are almost exclusively related to UDP protocols where the size/number of responses are larger than the UDP request that caused them. The DRDoS attack takes advantage of the fact that there is an amplification factor -- since the number/size of the responses generated by a single request is larger, an attacker can use this to direct more traffic at a target than the attacker's resources would otherwise allow. Done at sufficient scale with a high enough amplification factor, DRDoS attacks of this nature can be crippling to even the most well equipped and well funded organizations.
There are numerous problems one will encounter when trying to weather or defect a DDoS attack, but a DRDoS attack in particular adds an interesting twist -- if you are suffering a DRDoS attack, the attack is only possible because other systems, presumably not under your control, are vulnerable to traffic amplification vulnerabilities. In other words, you become affected because of another organization's vulnerabilities.
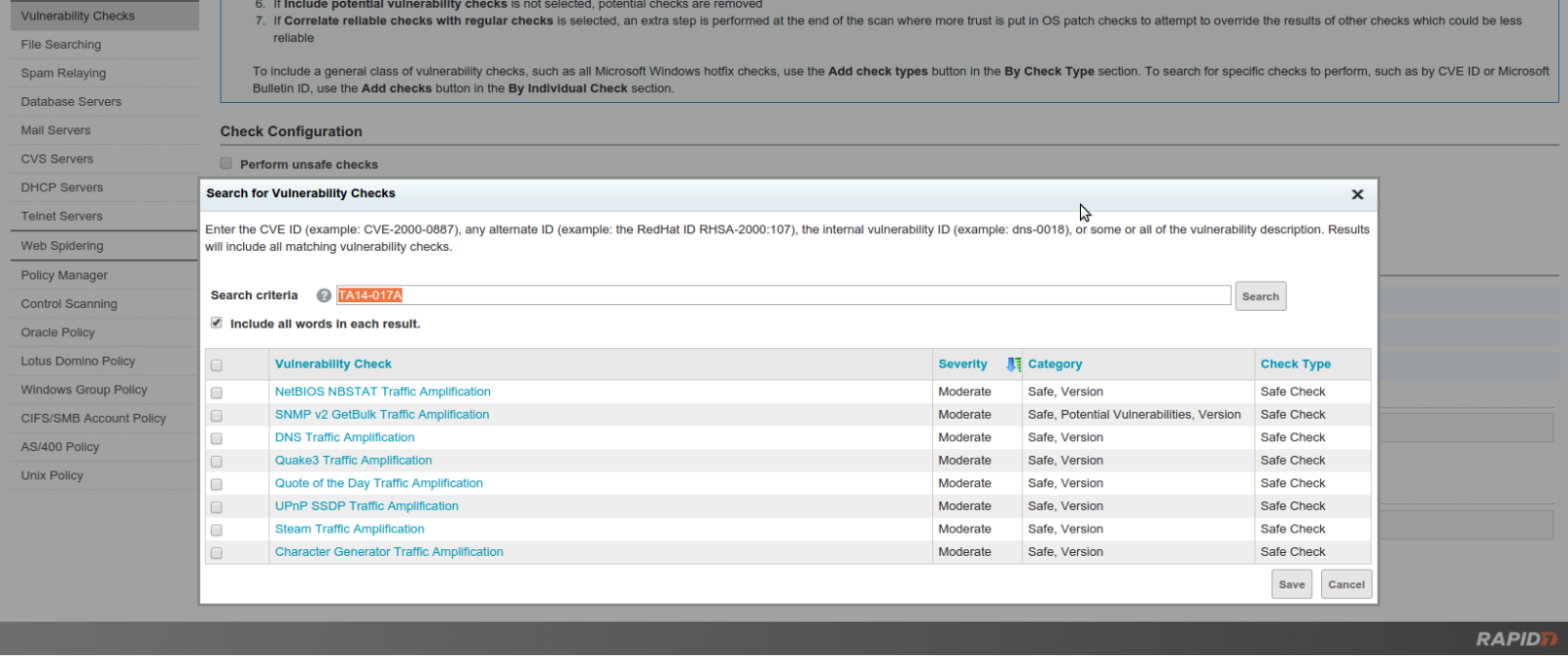
In an effort to help address this problem, the 12/10/2014 release of Nexpose adds coverage for the UDP protocols commonly used to conduct DRDoS attacks as outlined in US-CERT's TA14-017A advisory from earlier this year. To take full advantage of this coverage, you should ensure that you obtain both the content and product updates from 12/10/2014 and scan with the Full Audit or similar template. If you like, you can add just these checks to your own custom scan template by simply searching for any vulnerability referencing TA14-017A:
By scanning your assets for these traffic amplification vulnerabilities and appropriately addressing any affected endpoints you can help ensure that your assets are not used to perform DRDoS attacks against others.
Enjoy!