The first Microsoft patches of 2018 came early, with new updates released late Wednesday, January 3rd. Although this was due to the (somewhat) coordinated disclosure of the Meltdown and Spectre vulnerabilities, last week’s updates also contained fixes for 33 additional CVEs. These days, Microsoft releases their OS updates as monolithic packages, so many security fixes get bundled together. This means that most of this month’s security fixes – aside from Flash, Office, and .NET – were already out as of last week.
AMD Issue
There are pros and cons to this approach. One major drawback is that if an issue is found due to one fix, it can block security fixes for unrelated vulnerabilities. Unfortunately, this is the case this month: it turns out that some AMD systems have been rendered unbootable by last week’s updates. Microsoft says they are working with AMD to resolve the issue, but in the meantime the following updates will not be delivered to devices with impacted AMD processors:
- January 3, 2018—KB4056897 (Security-only update)
- January 9, 2018—KB4056894 (Monthly Rollup)
- January 3, 2018—KB4056888 (OS Build 10586.1356)
- January 3, 2018—KB4056892 (OS Build 16299.192)
- January 3, 2018—KB4056891 (OS Build 15063.850)
- January 3, 2018—KB4056890 (OS Build 14393.2007)
- January 3, 2018—KB4056898 (Security-only update)
- January 3, 2018—KB4056893 (OS Build 10240.17735)
- January 9, 2018—KB4056895 (Monthly Rollup)
Antivirus Incompatibilities
There is another major gotcha with this month's updates. They will not be available to devices that do not have a specific registry key set. This registry key is meant to be set by "compatible" antivirus software. (This is because some antivirus products make unsupported calls into the kernel, which can make systems unbootable with last week's patches.)
Microsoft states:
Customers will not receive the January 2018 security updates (or any subsequent security updates) and will not be protected from security vulnerabilities unless their antivirus software vendor sets the following registry key
Something to keep in mind if you're having difficulties patching.
Browser Vulnerabilities
It’s worth a reminder that even though exploitation of Meltdown or Spectre requires local access (i.e. the ability to run code under an authenticated account), this still means that JavaScript running in a browser is a potential vector. This month’s fixes mitigate this for IE and Edge.
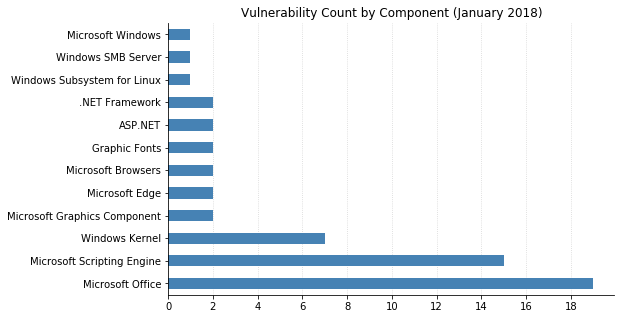
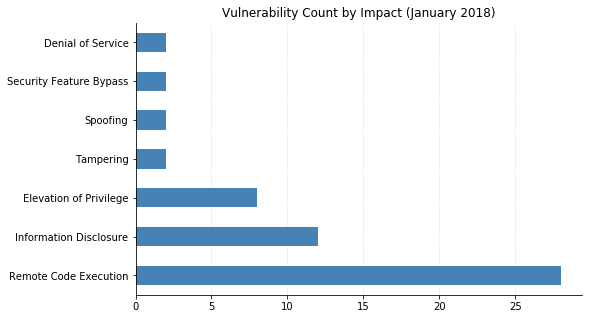
In addition to these mitigations, there is the usual bevy of browser vulnerabilities fixed with this month’s updates. The worst of these seem to be CVE-2018-0762 and CVE-2018-0772; both are Remote Code Execution (RCE) vulnerabilities affecting Microsoft browsers, as well as applications or Office documents that host the browser rendering engine via ActiveX. 17 other CVEs were patched, with impact ranging from Security Feature Bypass to Elevation of Privilege to Information Disclosure. However, the majority (13 altogether) are RCE vulns.
Office
19 separate vulnerabilities were patched for Microsoft Office today. CVE-2018-0797, an RCE flaw that can be exploited if a user opens a malicious RTF file, is the only one considered Critical. Nonetheless, two other RCE vulnerabilities (CVE-2018-0793 and CVE-2018-0794, in Outlook and Word respectively) have been assessed as being more likely to be exploited by attackers. CVE-2018-0802, another Office RCE vulnerability, is known to have been exploited in the wild (despite Microsoft’s assessment of “Exploitation Unlikely”).
Note that several of these Office vulnerabilities (including CVE-2018-0797) affect SharePoint Enterprise Server.
Miscellanea
Most of the other vulnerabilities that Microsoft considers more likely to be exploited this month are Information Disclosure. These can allow an attacker to glean information that can be used for social engineering, or in some cases (such as CVE-2018-0750, further compromise a system. CVE-2018-0744 is a privilege escalation flaw that could allow an attacker to execute code in kernel mode.
CVE-2018-0743, an integer overflow bug, is the latest vulnerability in the Windows Subsystem for Linux and also allows elevation of privilege.
Summary
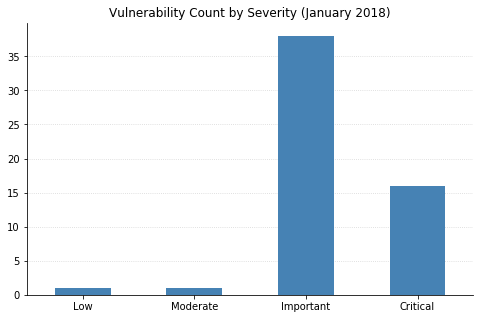
The charts below are based on the 56 Microsoft vulnerabilities published by January 9th, and do not include the Spectre/Meltdown (ADV180002) or Adobe Flash (ADV180001) CVEs.
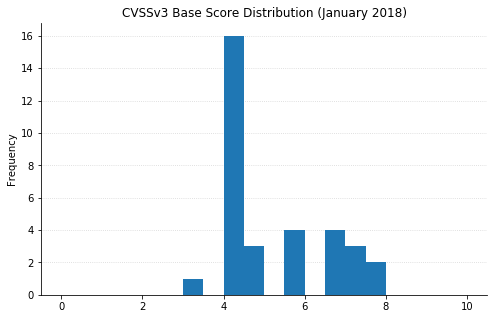
(Note: Not all CVEs had CVSSv3 data available at the time of writing.)


