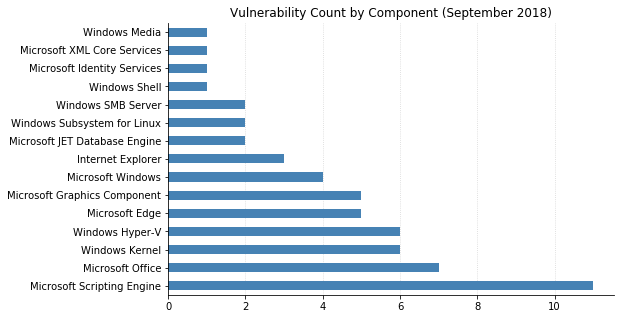
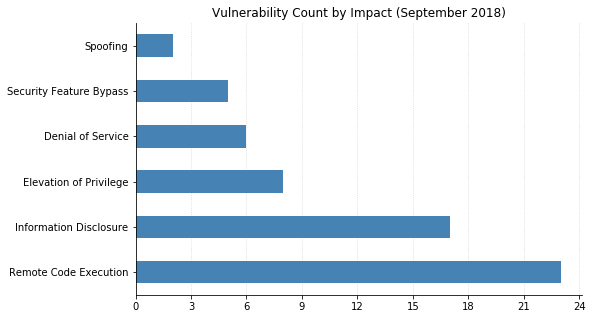
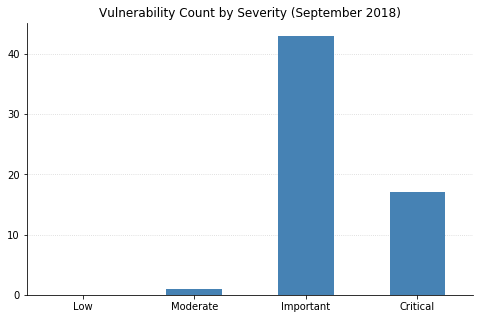
More than 60 vulnerabilities were addressed by this month's patches, including CVE-2018-15967 (a privilege escalation/information disclosure vulnerability in Adobe Flash Player). Over a quarter of these are considered Critical, which means there may be at least one way that malicious code could propagate without any user action.
Today's updates fix four publicly disclosed vulnerabilities. CVE-2018-8440, a privilege escalation bug affecting all versions of Windows from 7 to 10, was widely publicized two weeks ago along with proof-of-concept exploit code. It didn't take long for malicious actors to incorporate this into real-world attacks, with users having no recourse until today's patches came out. Although an attacker would need to convince a user to download and open a specially crafted file to exploit this, if successful they'd be able to gain full system privileges on the machine.
The other three publicly disclosed vulnerabilities did not have any reports of exploits currently in the wild. However, CVE-2018-8475 is a Remote Code Execution (RCE) vulnerability in the way Windows handles certain image files, which is a very tempting vector for social engineering attacks. CVE-2018-8409 allows denial of service (DoS) against applications using the System.IO.Pipelines library (a high performance I/O library for .NET), and CVE-2018-8457 is an RCE affecting both Internet Explorer and Edge.
Two other serious RCE vulnerabilities being addressed this month are CVE-2018-8332, which could be exploited by convincing a user to browse to a website or open a document containing a malicious embedded font, and CVE-2018-8430, which is a flaw in how Word handles PDF files.
Two advisories published by Microsoft this month do not reference a fix: CVE-2018-8474 (a Security Feature Bypass in Lync for Mac 2011). Exploitation could result in a user's system to open an attacker-specified website in a browser, or automatically download a file if the file type is on the safe file type list. Although not officially deprecated until next month, Microsoft has stated they will not fix the vulnerability, and instead recommends that users upgrade to Skype for Business on Mac. ADV180022 provides a workaround for CVE-2018-5391, also known as "FragmentSmack," a DoS vulnerability that was patched in the Linux kernel in August but also affects Windows systems. Microsoft is currently working on a fix, but in the meantime users can disable packet reassembly (which may result in packet loss due to out-of-order IP packets being dropped).
Microsoft has also continued to update their guidance for the speculative execution side-channel attacks. Today's revisions include mitigation against Spectre for Windows 10 1803 on ARM64 and L1TF updates for Server 2008.
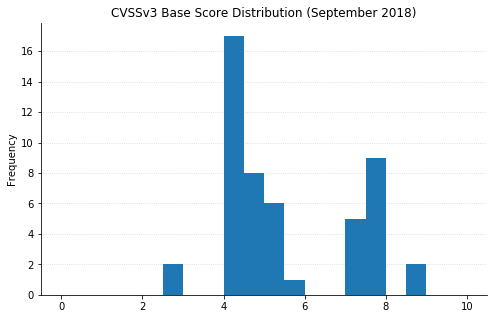
Note: not all CVEs had CVSSv3 data available at the time of writing