For many of us, work days peppered with conference room meetings and lingering conversations at coffee stations, water coolers, and break areas are now but memories and have been replaced by countless Zoom drop-ins, innumerable Slack/Teams notifications, and—yes, regrettably—a marked increase in email/social media interactions.
While this rapid transition from “mostly physical” conversations to “mostly digital” communications has required some adjustment for a remote-capable workforce, attackers required no adjustment time at all. Individual assailants and organized teams were at the ready to use their well-honed techniques to take advantage of our new need to double-click/tap on every new buzz, bing, and notification.
We enter this brave new work pattern with knowledge from the 2019 Verizon Data Breach Investigations Report that phishing is still an attacker’s best friend when it comes to gaining a foothold, and statistics from an IBM X-Force report that 50% of credentials harvested via phishing are collected within the first 60 minutes of a campaign.
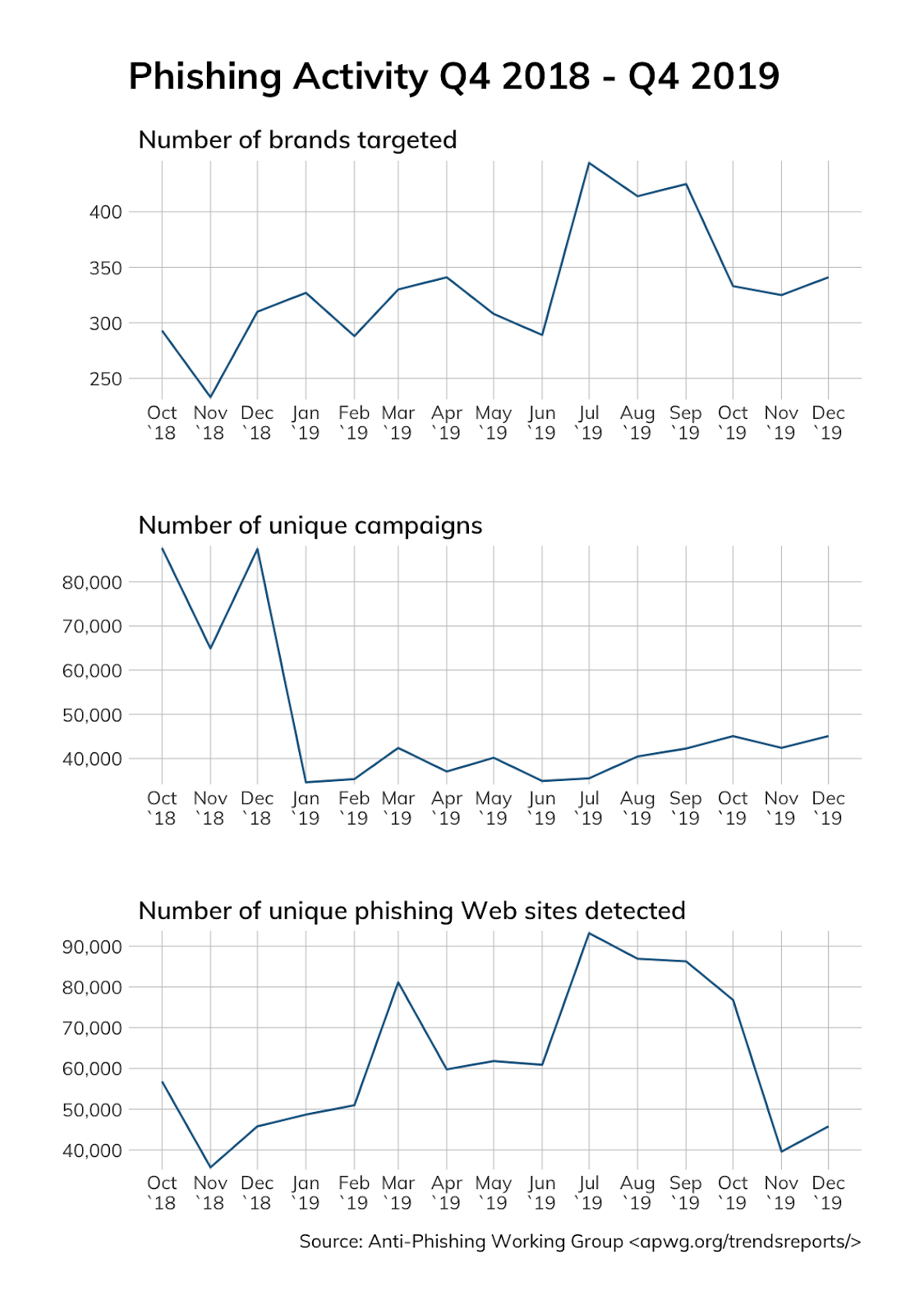
Trends in 2019 from the Anti-Phishing Working Group (right) further reinforce the pace, determination, and capability of attackers and show there are between 250 and 500 primary brands targeted or used in campaigns per month, and over 40,000 campaigns are run monthly using nearly as many unique phishing websites.
To make matters worse, attackers are also capitalizing on fears and concerns associated with the global pandemic.
In early April, Google saw 18 million daily malware and phishing emails related to COVID-19 in addition to more than 240 million COVID-related daily spam messages.
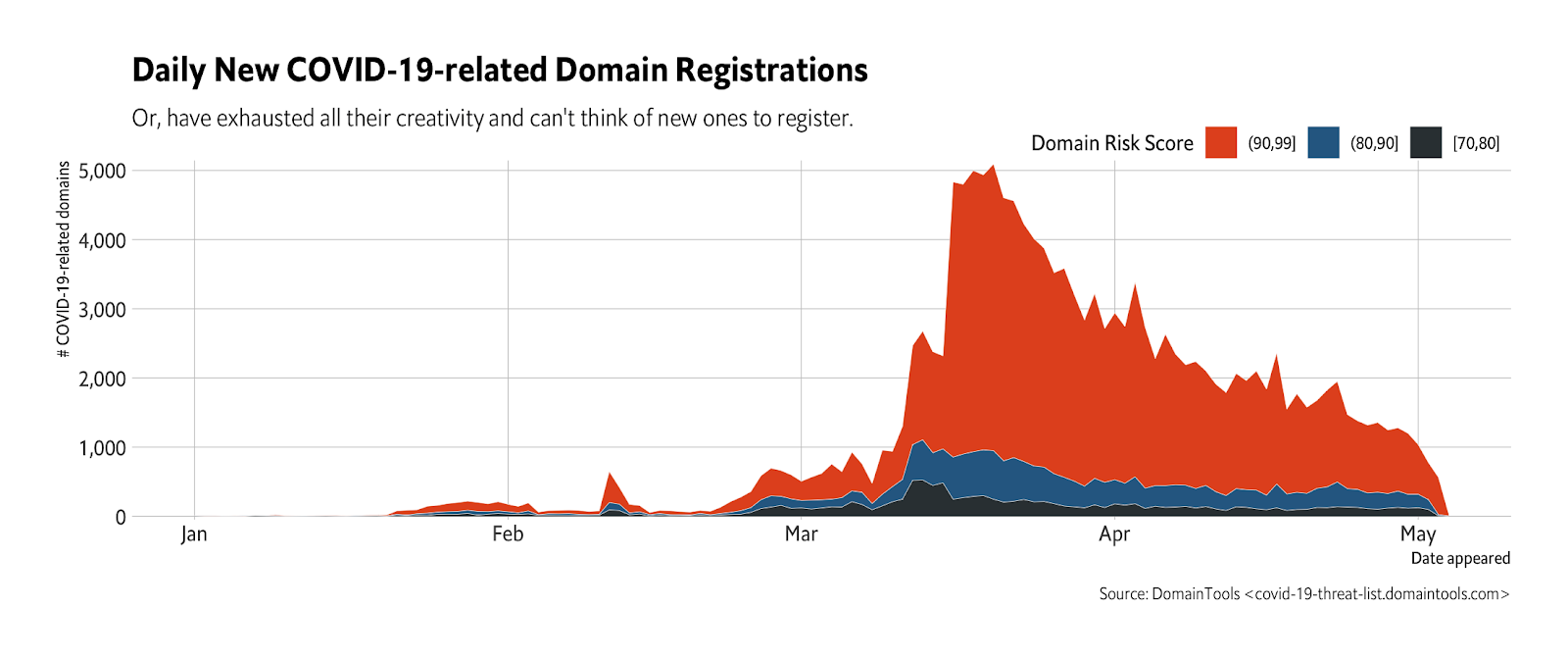
DomainTools has also set up a special tracking site and is releasing daily updates to a database of COVID-related domains (paired with risk scores) in an effort to help defenders mitigate against phishing and other types of cyber-attacks. While the pace of new, malicious domain creations has slowed (below), there are over 153,000 able to be used.
Since it is difficult (impossible, really) to prevent novel phishing campaigns from reaching an organization's workforce, speedy detection, response, and containment is of the essence.
With that in mind, Rapid7 is providing:
- Free access to InsightConnect
- Automation playbooks for remote security teams
- Best practices and assistance on how to get started with automation
- A community forum to provide feedback and collaborate on new automation tasks
A major component of this initial release is our “Phishing Tackle Box,” which provides a set of automated workflows and prebuilt integrations with email systems, Slack, and Microsoft Teams to optimize response times, tasks, and collaboration when an organization has been targeted by a phishing attack.
Pre-built InsightConnect workflows digest all indicators (domains, URLs, IP addresses, etc.) from incoming mail and check them against public and organization-accessible threat indicator lists and APIs.
When IoCs associated with malicious campaigns are identified, many actions can take place automatically, whether it be notifying automation-shy security teams in their collaboration platform of choice or automatically configuring systems to reject new emails from certain senders and domains, delete existing ones, and identify accounts that may have opened them and/or been compromised.
Provided proper processes have been developed and workers are aware of them, complete user containment can be automated if a compromise has been detected, with containment steps ranging from simple password resets to temporary removal of access to critical systems, network, and data.
The Work-from-Home Automation Playbooks are designed to help optimize your response, containment, and remediation times, whether you start with a Slack- or Teams-based workflow or migrate to full automatic actions as you become more comfortable and experienced with automation.
Article Tags
Related blog posts

Products and Tools
Rapid7 completes IRAP PROTECTED assessment for Insight Platform solutions
Rapid7

Security Operations
How to Develop a SOAR Workflow to Automate a Critical Daily Task
Ryan Fried

Products and Tools
360-Degree XDR and Attack Surface Coverage With Rapid7
Margaret Wei

Products and Tools
Deploying a SOAR Tool Doesn’t Have to Be Hard: I’ve Done It Twice
Ryan Fried