A vulnerability management solution like Nexpose is often used by organizations to provide risk-based insight for potential and real threats. Nexpose provides product reporting capabilities that help organizations clearly prioritize their risk based on such aspects as exploitability, availability of malware kits and weighted and temporal risk scores. Frequently, organizations leverage this rich threat data in XML format in conjunction with other enterprise security tools such as SIEM, GRC, IPS, network topology and risk analysis solutions or custom-built internal systems. More than 20 technology partners have already leveraged our existing XML Export capabilities to build deep integrations with their products to provide deeper security insight based scan, asset, vulnerability check results, vulnerability definitions, and vulnerability remediation details.
Nexpose 5.2, released today, includes a new version of the XML Export to give users additional attributes to leverage for their integration needs. Also, for the first time the Nexpose Community edition has the ability to generate the XML Export format.
What's new in XML Export 2.0?
Previously existing reports created with XML Export will use the same schema as in previous versions of Nexpose.
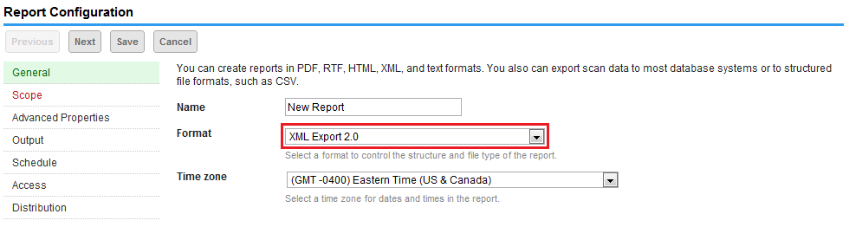
After upgrading to Nexpose 5.2, users can generate reports using the new XML Export 2.0 format through the Web User Interface or Nexpose API. There is a new schema available, ReportXMLExportSchema-2.0.xsd, that includes the new elements or attributes. To ease with the transition to the new format all new XML elements and attributes are reflected as optional elements (or attributes) in the schema. Existing elements and attribute names have not changed and the structure of the XML hasn't greatly changed. This should help minimize the effort to upgrade the client code to use the latest version and improve backward compatibility with older versions of Nexpose.
To provide more granularity and improve performance users can apply new filters to the vulnerability test results included in the XML file. This allows users to include only the test results that are important to them. For example, include all test results or show only the results for vulnerabilities found/vulnerable versions/potential vulnerabilities.
Below are the all the enhancements introduced in the new XML Export 2.0 format. They include the node element, test element, and vulnerabilities elements.
Node type <node>
| Attribute name | Type | Description |
|---|---|---|
| scan-template | String | The name of the scan template used during the scan. |
| site-name | String | The name of the site that contains this node. |
| site-importance | Enumeration | The site importance: Very Low, Low, Normal, High, Very High |
| risk-score | Number | The asset risk score. |
Example Code
<nodes>
<node status="alive" hardware-address="523700462C68" risk-score="164409.19" scan-template="Full audit" site-importance="Normal" site-name="Full Scan Lab Network" device-id="65" address="10.2.109.244">
</nodes>
Node test type <test>
| Attribute name | Type | Description |
|---|---|---|
| pci-compliance-status | Enumeration | PCI Compliance: pass or fail |
| vulnerable-since | Date | The date the vulnerability was first detected. |
| scan-id | Number | The ID of the scan in which this test was run. |
Example Code
<test status="vulnerable-exploited" vulnerable-since="20120129T164138717" scan-id="1" pci-compliance-status="fail">
Vulnerability type <vulnerability>
| Attribute name | Type | Description |
|---|---|---|
| riskScore | Number | The vulnerability risk score. |
| Element Name | Type | Description |
|---|---|---|
| malware | Malware type | The malware associated with the vulnerability definition. |
| exploits | Exploit type | The exploits associated with the vulnerability definition. Each exploit will be its’ own element. |
Example Code
<vulnerability title="MS10-050: Vulnerability in Windows Movie Maker Could Allow Remote Code Execution" riskScore="452.7847" modified="20111209T000000000" added="20100811T000000000" published="20100810T000000000" cvssVector="(AV:N/AC:M/Au:N/C:C/I:C/A:C)" cvssScore="9.3" pciSeverity="5" severity="9">
Exploit type <exploit>
| Attribute name | Type | Description |
|---|---|---|
| id | String | The external exploit identifier |
| type | Enumeration | The source for the exploit: exploitdb or metasploit |
| title | String | The title of the exploit. |
| link | String | A URL for an exploit as published by Metasploit or The Exploit Database. |
| skillLevel | Enumeration | The skill level needed to perform the exploit: Novice, Intermediate, Expert |
Example Code
<exploits>
<exploit title="Microsoft DirectShow (msvidctl.dll) MPEG-2 Memory Corruption" type="metasploit" link="http://www.metasploit.com/modules/exploit/windows/browser/msvidctl_mpeg2" sklLevel="Intermediate"/>
</exploits>
| Element Name | Type | Description |
|---|---|---|
| name | String | The name of the malware kit. One name element will be specified for each malware kit. |
Example Code
<malware>
<name>Fragus Black</name>
<name>Fragus 1</name><name>Eleonore</name><name>Yes Exploit</name>
<name>Phoenix</name><name>T-Iframer</name>
<name>Salo</name><name>Unique Pack Sploit</name>
<name>Crimepack</name><name>Impassioned Framework</name>
</malware>
For more information see the Report_XML_Export_Schema_2.0, which you can download from the Support page in the Web interface of Nexpose.
Deprecation of XML Exports
At Rapid7 we are deeply committed to providing the best possible integrations between Nexpose and other security solutions. For this reason we will be continuing to make enhancements to the XML Export format over time. With these incremental enhancements, older reporting versions become obsolete and as such we will end of life those older formats over time.
| Report Format | Description | End Of Life Date |
|---|---|---|
| XML Export | This report format is a subset of the data in XML Export 2.0. | 12/31/2012 |
| Nexpose™ Simple XML Export | This report format provides less data than is available in the XML Export. | 12/31/2012 |
We welcome any ideas to continually improve our XML Export capabilities and look forward to your feedback and comments.
Nate Crampton,
Product Manager
Article Tags
Related blog posts

Vulnerabilities and Exploits
CVE-2026-0826: How an Old Bug Can Feed AI-Powered Impersonation
Douglas McKee, Director, Vulnerability Intelligence

Vulnerabilities and Exploits
CVE-2026-0826: Critical unauthenticated stack buffer overflow in HP Poly VVX and Trio VoIP Phones (FIXED)
Stephen Fewer

Vulnerabilities and Exploits
Authenticated RCE via Argument Injection in Gogs (NOT FIXED)
Jonah Burgess

Threat Research
Q1 2026 Threat Landscape Report: Zero-clicks, geopolitical tensions, and some wins for law enforcement
Rapid7 Labs