At Rapid7 security is everything, and that doesn't exclude the UX team. Yes, we want to give you beautiful interactions, seamless workflows and screens that make you go ‘Wow!' But security is always there gently guiding our design decisions, which can sometimes cause conflict between security best practices and the best user experience.
Following on from an excellent post from Roy Hodgman, one of the most common examples of the impact of security on user experience is authentication: login forms, password creation and all the secure, if sometimes tedious, steps we as users know we have to take to keep our data secure.
So much to remember
There are many figures out there, but the average user in the US is believed to have over twenty online accounts (some reports claim this figure is over a hundred). Even if we stick with the relatively conservative number of twenty, that's twenty email/username and password combinations to remember. Being realistic we know that people reuse passwords, we all know we shouldn't, but it happens, so this figure is most likely a little lower than the number of accounts users actually hold.
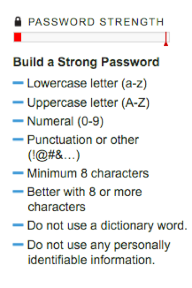
Then we have to contend with password policies (see figure 1). Eight or more characters is a standard rule for most passwords due to complexity; there are 6.63 quadrillion possible 8 character passwords, which is a lot to try. Unfortunately, as we increase the complexity of the password we also increase the risk of forgetting or mistyping it. Password1 is easy to remember whereas TizM9$3f%, although the same number of digits, is much harder to remember.
Taking all of this into account, as a UX designer, I know that people will forget their password(s), or which email address they've used_. “Is it my work email? My home email? I changed my password last week, what did I change it to?”_
Designing for the wrong credentials**
At Rapid7 we follow current best practices. When you mistype your password or email address you get an error. This error is normally in the form of:
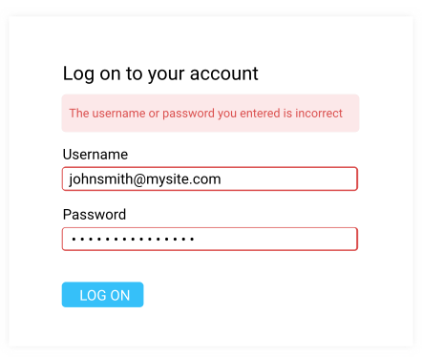
Now, as a UX designer who wants to give you the simplest, best experience, what I'd like to be able to say is:
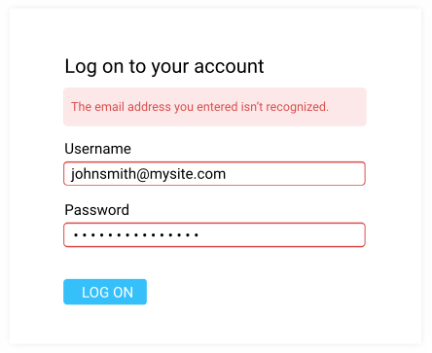
Or even better:
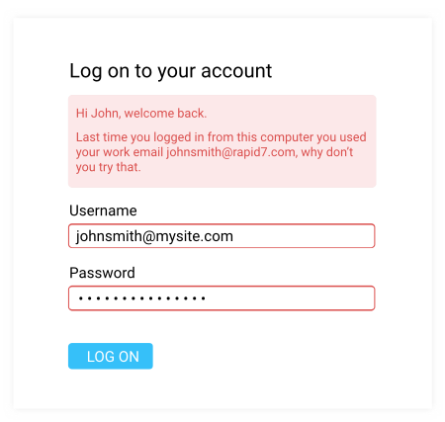
Unfortunately, these messages also say “Hi Attacker, the email address you're trying doesn't have an account so don't try it,” or worse, “Hi Attacker, this email address does have an account here, why don't you try and use it to get in?”
Of course we always include the backup action of a “Forgot your password?” link, which takes you through a longer authentication process and allows you to reset the password you've forgotten.
Is this going to be forever?
Hopefully not. The world is moving quickly, and as designers we need to pay attention. It is our hope that we can continue to streamline login processes across the web, using new technologies and ideas, so that maybe one day the concept of forgotten or mistyped passwords is something we complain to our grandchildren about, because they will never understand the pain.
Technologies that could pave the way for a password-free world include:
Biometrics
Using biometrics, in an ideal world, means users will never have to remember a password again. Currently, a lot of smartphones contain fingerprint scanners to speed up the process of unlocking your phone. However, we still need the password/pin backup as technology hasn't quite reached 100% accuracy. Windows Hello uses facial recognition to log you into your account and authorize payments, again, however, this isn't quite ready for everyday use as you need specific camera technology to take advantage of this feature.
Cell Phones
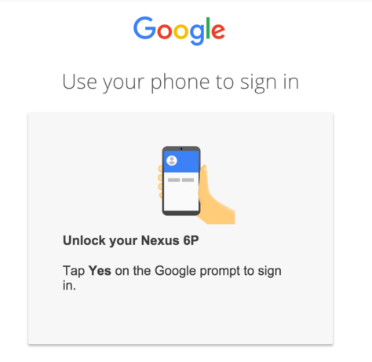
Google was reported to be trialing cell phone authentication in place of passwords in December, something Yahoo has also reportedly investigated. This password-free system requires the user to download an application, and connect their mobile phone to their account. The next time the user tries to login to their account they will receive a notification to their phone to check it's a valid login, and the user can then click “Yes” or “No.”
There are, however, issues with this being the only means to login. Cell phone batteries have a somewhat unreliable duration – what happens if your phone is dead? Can you login, or do you have to charge your phone before you can read your email?
Also, what happens if someone steals your phone? While we like to think of our phones as being private and secure, the recent news reports surrounding the FBI and Apple have shown that no system is 100% safe and that if someone really wants to get into your phone they might just find a way to do so.
At Rapid7
…we'll continue to ensure that there is a balance between usability and security. For now you'll have to remember those pesky passwords, but know that we are continuously monitoring the latest authentication techniques, and considering their adaption within our products. That way, you'll have fast access to your security information when you need it, but your information security will always be paramount.
If you have any feedback for us on our current authentication process let us know in the comments below or email [email protected].
Thank you for reading!
Ceara McCurdy
UX Designer II, Rapid7
Further Reading:
Cell Phone Authentication:
http://techcrunch.com/2015/12/22/google-begins-testing-password-free-logins/
http://www.engadget.com/2016/01/15/googles-creepy-plan-to-kill-the-password/
Biometrics:
http://www.techradar.com/how-to/software/how-to-use-windows-hello-1301455