Thanks to well-structured industry reports like the annual Verizon DBIR, Kaspersky "Carbanak APT" report, and annual "M-Trends" from FireEye, the realities of modern attacks are reaching a much broader audience. While a great deal of successful breaches were not the work of particularly sophisticated attackers, these reports make it very clear that the techniques once only known to espionage groups are now mainstream.
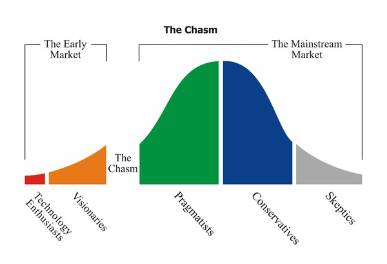
Lateral movement technologies have crossed the chasm
I have written before about the need for businesses to adopt disruptive technologies and have a plan to monitor them, but this is about the other side of the "war". The hacker community is the early adopter group who uses disruptive technologies in research, penetration tests, red teaming, and unfortunately due to a few "bad apples", to steal data. Every time a new technology is made available, and especially if it is widely distributed, our friends in this world start thinking about either exploiting it, using it for unintended purposes, or both. A lot of people fear this group and their unique perspective on technology, but we are hopeless to ever keep pace with attackers without these tinkerers and their good intentions.
We have been hearing for a few years that the initial network compromise is the hardest part because moving from system to system undetected is, by comparison, rather simple. Many ignored this claim as something only possible for the highest tier of hackers with nation-state funding and espionage in their veins, but we just cannot ignore it anymore. The reports are surfacing with one consistent theme: lateral movement tools are being used by too many of the criminals now to accept our inability to detect them.
Since the technology boom of the nineties, a required reading in a lot of business schools is Geoffrey Moore's "Crossing the Chasm." Its purpose is to help marketers focus on the group of people most likely to become customers at each phase of the technology adoption lifecycle, but it has significance outside of just marketing groups. The "chasm" of significance is the stage at which so many Betamaxes and HD DVDs fail, i.e. progressing from technology lovers buying them to mainstream adoption. The vast majority of technologies fail to get the momentum necessary to cross this chasm. While the technology here is not a traditionally marketed product, "hacker tools", such as mimikatz, PowerShell, and Windows Credential Editor, have crossed it and the momentum came from the consistency of those tools' undetected use in profitable breaches.
Under 200 days before detection is not really an improvement
Nowhere in the M-Trends reports has there been any celebration of the decreased number of days before breach detection from a median of 229 in 2013 to 205 in 2014 and 146 in 2015, but unfortunately some media coverage found solace in improving upon an unsettling anchor. Even if there were any indication we could keep this pace (which there isn't), we wouldn't get the median down to a few days until after 2020. This is why we need to pay more attention to the forensics teams and hacker community to understand the factors causing such a delay in detection. Obviously, some of the organizations getting breached will not have taken security seriously, but anyone looking to see that number drop precipitously needs to focus on incident detection and response. I explained reasons detection is so important previously, but it is more than just that. We need to stop telling ourselves that breached organizations had no chance because it was the work of undetectable, super-advanced malware or some elite group of super-spies. Malware developers will continue to get more creative and disruptive technologies will continue to go mainstream, so we need to continually challenge ourselves to develop new means of detection.
Attackers are impersonating the people of authority
The first major challenge in detecting the modern cybersecurity attacks is that humans are more interactively involved. Spear phishing may initially compromise a low-privilege user on the network, but that is just a stepping stone. Privileged accounts are a target, but not only because of systems to which they provide access: these accounts belong to your administrators and administrators behave in very interesting ways. When we get locked out of our machines, a desktop administrator can reset our passwords, remotely access the machine, or perform some other administrative change. When we are working remotely and some VPN issue prevents us from accessing an internal document, these administrators could theoretically add our home IP to a whitelist or provide another remote means of access. There are countless activities and tools our administrators need to do their jobs that are doubly valuable to intruders:
- They provide access to all network systems with permitted remote access tools
- It is rare for others in the organization to question their behavior at the moment it occurs
This is what made the T-1000 so terrifying in "Terminator 2". It could replicate anyone we would trust, but it primarily impersonated prison guards and a police officer. Why did it do this? This behavior provided unquestioned access to the necessary tools and, when viewed in isolation, a great deal of its behavior (like carrying a weapon, chasing others, or commandeering cars) could be explained away by eyewitnesses. Sure, as we watch the movie and see the string of events it caused, it seems ridiculous to use this analogy, but amid the noise of a crime-ridden city of millions of people, the pattern would take a lot longer to understand than the killing spree of a Mr. Universe wearing a leather jacket and carrying a shotgun in the original "Terminator".
Traditional classification of activity as black/white is ineffective here
This impersonation and targeting of administrators and their tools is a major reason traditional monitoring solutions are so challenged today. If you blacklist and alert on every single administrative action that could be malicious, your team is going to be overwhelmed by alerts and become so numb to the onslaught that illegitimate behavior will be ignored because of experiences of previous time-wasting investigations. If you whitelist every administrator and every tool they use, attackers need only harvest a single administrator credential and use a whitelisted administrator tool and they can easily remain on your network, exploring the systems and stealing valuable data for 146 days or, in the worst case FireEye shared, over eight years.
You need to blend the monitoring of all your users' and administrators' behavior with a recognition of how they leverage dual-purpose lateral movement tools to identify deviations from the norm. Combined with alerts for clearly malicious behavior, a series of traps for intruders to trip, and integrations to advanced malware detection, user behavior analytics can help your organization drastically improve your detection times now rather than in 2020.
To learn more about InsightIDR and Rapid7's other solutions for detecting compromised credentials, check out our compromised credentials resource page and make sure to download our complimentary information toolkit.
Article Tags
Related blog posts

Detection and Response
Zero Chaos: Scaling Detection Engineering at the Speed of Software, with Detection As Code
Zachary Zeid, James Gallahan
Threat Research
Rapid7 Detection Coverage for Iran-Linked Cyber Activity
Rapid7 Labs

Detection and Response
Alert Fatigue Isn’t Going Away. Here’s How Modern SOCs Are Fighting Back
Rapid7

Detection and Response
Rapid7: 7 years of recognition in Gartner® Magic Quadrant™ for SIEM
Cindy Stanton