Posts tagged Detection and Response

Detection and Response
Zero Chaos: Scaling Detection Engineering at the Speed of Software, with Detection As Code
Zachary Zeid, James Gallahan
Threat Research
Rapid7 Detection Coverage for Iran-Linked Cyber Activity
Rapid7 Labs

Detection and Response
Alert Fatigue Isn’t Going Away. Here’s How Modern SOCs Are Fighting Back
Rapid7

Detection and Response
Rapid7: 7 years of recognition in Gartner® Magic Quadrant™ for SIEM
Cindy Stanton

Detection and Response
Innovative Tunnelling and Forensic Tool Abuse: IR Tales from the Field
Noah Hemker

Industry Trends
Key Takeaways from the Take Command Summit 2025: Outpacing the Adversary – Red Teaming in a Complex Threat Landscape
Rapid7

Industry Trends
Key Takeaways from the Take Command Summit 2025: Demystifying Cloud Detection & Response – The Future of SOC and MDR
Rapid7

Exposure Management
Active exploitation of SAP NetWeaver Visual Composer CVE-2025-31324
Caitlin Condon

Products and Tools
Password Spray Attacks Taking Advantage of Lax MFA
Chris Boyd

Detection and Response
Fortinet Firewalls Hit with New Zero-Day Attack, Older Data Leak
Caitlin Condon
Detection and Response
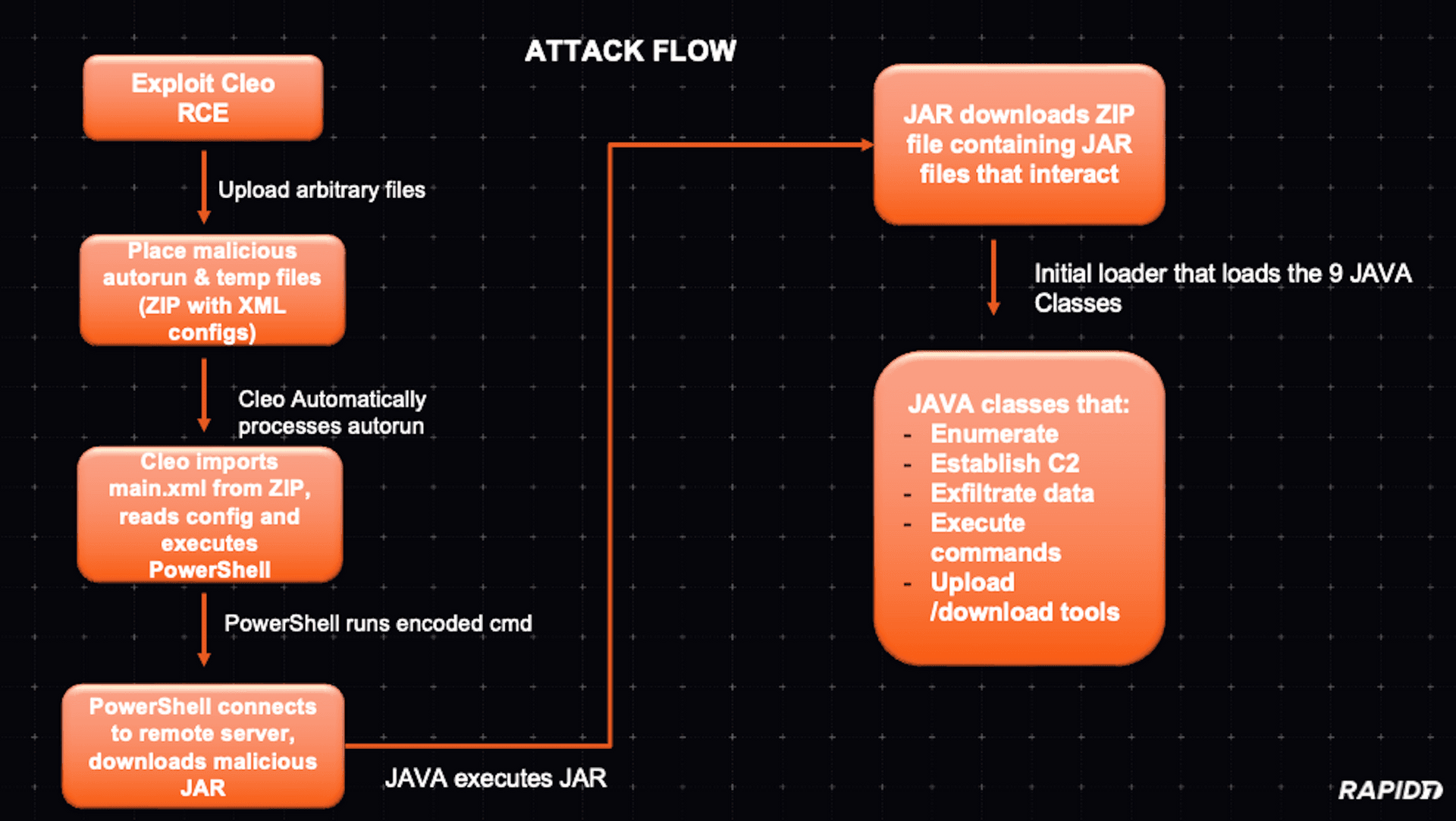
Modular Java Backdoor Dropped in Cleo Exploitation Campaign
Christiaan Beek

Detection and Response
Widespread Exploitation of Cleo File Transfer Software (CVE-2024-55956)
Rapid7

Detection and Response
Investigating a SharePoint Compromise: IR Tales from the Field
Noah Hemker

Detection and Response
Three Recommendations for Creating a Risk-Based Detection and Response Program
Rapid7

Detection and Response
VMware ESXi CVE-2024-37085 Targeted in Ransomware Campaigns
Rapid7

Detection and Response
Supply Chain Compromise Leads to Trojanized Installers for Notezilla, RecentX, Copywhiz
Rapid7

Detection and Response
Malvertising Campaign Leads to Execution of Oyster Backdoor
Rapid7

Vulnerabilities and Exploits
CVE-2024-4978: Backdoored Justice AV Solutions Viewer Software Used in Apparent Supply Chain Attack
Rapid7

Detection and Response
Rapid7 Recognized in the 2024 Gartner® Magic Quadrant™ for SIEM
Meaghan Buchanan

Detection and Response
Ongoing Social Engineering Campaign Linked to Black Basta Ransomware Operators
Rapid7

Detection and Response
Velociraptor 0.7.2 Release: Digging Deeper than Ever with EWF Support, Dynamic DNS and More
Rapid7