To celebrate this first day of Autumn[1], we've got a potpourri of "things Metasploit" for you this week. And it might smell a bit like "pumpkin spice"... Or it might not. Who knows?
Winter is Coming
If you're looking to finish filling your storehouse before the cold sets in, we've got a couple of new gatherer modules to help. This new Linux post module can locate and pull TOR hostname and private key files for TOR hidden services on a target system. If containers are more your thing, this new *nix post module will gather all users' Docker creds from a hosting target. And while your DB is getting stocked up with creds, don't forget to add Fall2017 to your password list[2] ('cause, you know...people).
Uniting People
Last week, some of the Metasploit team joined Rapid7 customers from around the country for Rapid7’s annual UNITED Summit in Boston. Brent Cook offered an overview of what’s next for Metasploit Framework, Wei Chen and James Barnett led an introduction to CTF competitions, and the Metasploit team hosted UNITED’s inaugural CTF for attendees. 62 teams competed for prizes and bragging rights—and for some of them, UNITED marked their first-ever flag capture. Congrats to the winners and first-timers!
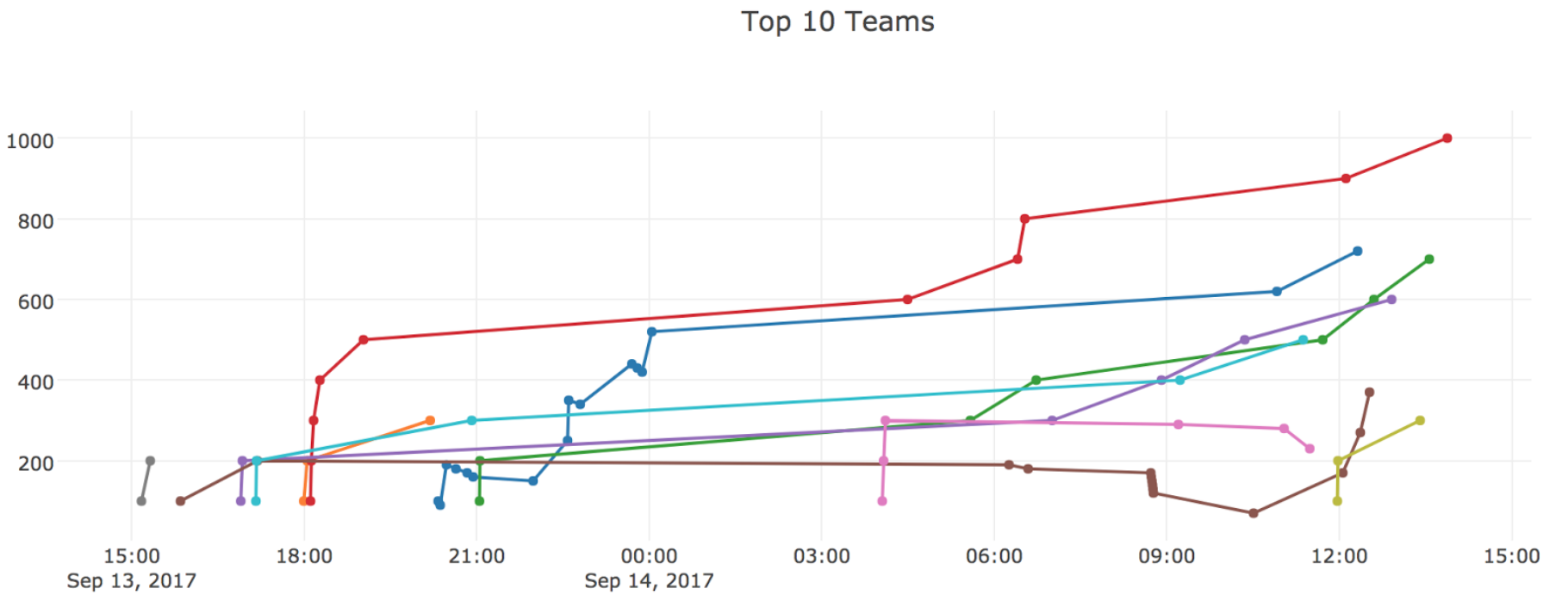
Thanks to everyone who joined us to share knowledge, drop shells, and log face-time in Boston!
Good Things Come in Threes
Today marks the third appearance of the Metasploit Town Hall at DerbyCon. The Town Hall is an interactive panel discussion centered around the current state (and trajectory) of Metasploit, with questions and feedback welcomed. If you're out at Derby this year, drop on by and be a part of the conversation!
Want MOAR?
Check out our YouTube channel for additional Metasploit-related content, including recent (and past!) recordings of the Metasploit team's bi-monthly sprint demo meetings. At best, you'll find out about new Metasploit work and features in progress. At worst, they aren't really long videos. ¯\_(ツ)_/¯
New Modules
Auxiliary and post modules (2 new)
- Linux Gather TOR Hidden Services by Harvey Phillips
- Multi Gather Docker Credentials Collection by Flibustier
Get it
As always, you can update to the latest Metasploit Framework with msfupdate
and you can get more details on the changes since the last blog post from
GitHub:
To install fresh, check out the open-source-only Nightly
Installers, or the binary installers which also include
the commercial editions.