On Jan. 19, 2019, the @pear Twitter account for the PHP Extension and Application Repository (PEAR) put out a notification that a security breach had been found on the pear.php.net web server. The only information that has been communicated thus far is that a compromised version of the PHP PEAR package manager go-pear.phar was found in the core PEAR filesystem. Administrators have taken down the website while they perform a forensic investigation to determine when they can restore it to clean state. As of Jan. 22, 2019, the site is still serving an outage notification page instead of the usual package archive page.
In later communications, the PEAR administrators noted that “if you have downloaded this go-pear.phar in the past six months, you should get a new copy of the same release version from GitHub (pear/pearweb_phars) and compare file hashes. If different, you may have the infected file.”
They have further notified PHP/PEAR users that the GitHub copy of go-pear.phar is not compromised. To their knowledge, only the copy on the pear.php.net server was impacted.
If you already know what PHP/PEAR is, there is extended guidance below in “What can I do if my organization uses PHP/PEAR?” Given the lack of details on the extent of the breach, it might be wise to do a full integrity check of all your PHP-enabled services and applications. This may sound extreme, but until we know all the actions performed by the PEAR attacker (or attackers), it is difficult to know what level of response is truly warranted.
What is PEAR?
As noted previously, PEAR is short for "PHP Extension and Application Repository." The purpose of PEAR is to provide the following:
- A structured library of open-source code for PHP users
- A system for code distribution and package maintenance
- A standard style for code written in PHP
- The PHP Extension Community Library (PECL)
- A website, mailing lists, and download mirrors to support the PHP/PEAR community
PEAR is similar in nature to Maven (for Java), CPAN (for Perl), CRAN (for R), etc., in that all PEAR packages are registered in and downloaded from a central server at pear.php.net.
Copies of go-pear.phar ship with PHP distributions, but it is possible to manually download the executable. Instructions are provided on how to do that in the “Getting and installing the PEAR package manager” documentation.
What’s the big deal?
PHP powers a significant proportion of websites (nearly 80% of all sites that have detectable server-side components). Everything from content management systems such as WordPress and Drupal to popular e-commerce platforms such as Magento and course management systems like Moodle are powered by PHP. As such, using a supply chain attack—which is what appears to be the case here—to compromise a common reference source for packages and other programming language resources can have a broad impact.
Little is known beyond what the PEAR administrators have already communicated. The fact that this critical of an executable was compromised without notice for potentially six months is an indicator that attackers had the ability to impact the integrity of files on the archive server and more files, executables, and even packages may also be compromised.
What can I do if my organization uses PHP/PEAR?
The known-infected go-pear.phar executable has an MD5 hash of 1e26d9dd3110af79a9595f1a77a82de7, first seen in VirusTotal on Jan. 19, 2019. You should compare all copies of this file in your organization to this hash to determine whether you’ve been directly impacted. Endpoint, network, and server anti-malware defense technologies should have this signature updated soon if they do not already have it in their signature databases.
It appears that the PEAR administrators are using the @pear Twitter account to communicate news about this breach. Rapid7 Labs will be monitoring this account and recommends that your organization do the same to keep up with the latest news.
You should also look at past and ongoing network/server infrastructure monitoring systems for unusual behavior coming from systems that have pulled packages from the PEAR archive for the past six months. Until more is known about the extent of the breach, it may be wise to assume your PHP-based applications are compromised until you verify otherwise.
The current PEAR subdomain is likely only available over http (vs. https). Until the PEAR administrators restore the site, it will show up as untrusted with the following certificate:
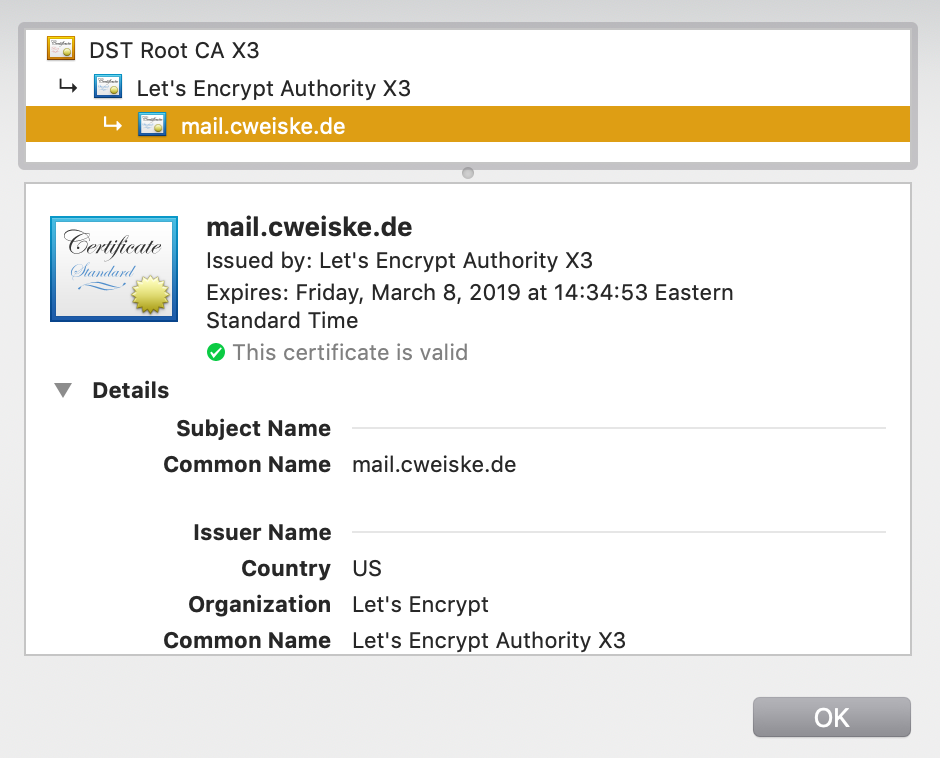
The PEAR administrators are working to update the certificate so that it no longer issues a browser warning but have given no ETA on when they intend to perform the update.
While you’re reviewing your PHP configurations, make sure you’re running a current, patched, and supported version of PHP. Rapid7 Labs noted back in December that there are millions of web-accessible PHP systems that are running woefully unpatched and/or unsupported versions of PHP.
Related blog posts

Detection and Response
Zero Chaos: Scaling Detection Engineering at the Speed of Software, with Detection As Code
Zachary Zeid, James Gallahan
Threat Research
Rapid7 Detection Coverage for Iran-Linked Cyber Activity
Rapid7 Labs

Detection and Response
Alert Fatigue Isn’t Going Away. Here’s How Modern SOCs Are Fighting Back
Rapid7

Detection and Response
Rapid7: 7 years of recognition in Gartner® Magic Quadrant™ for SIEM
Cindy Stanton
