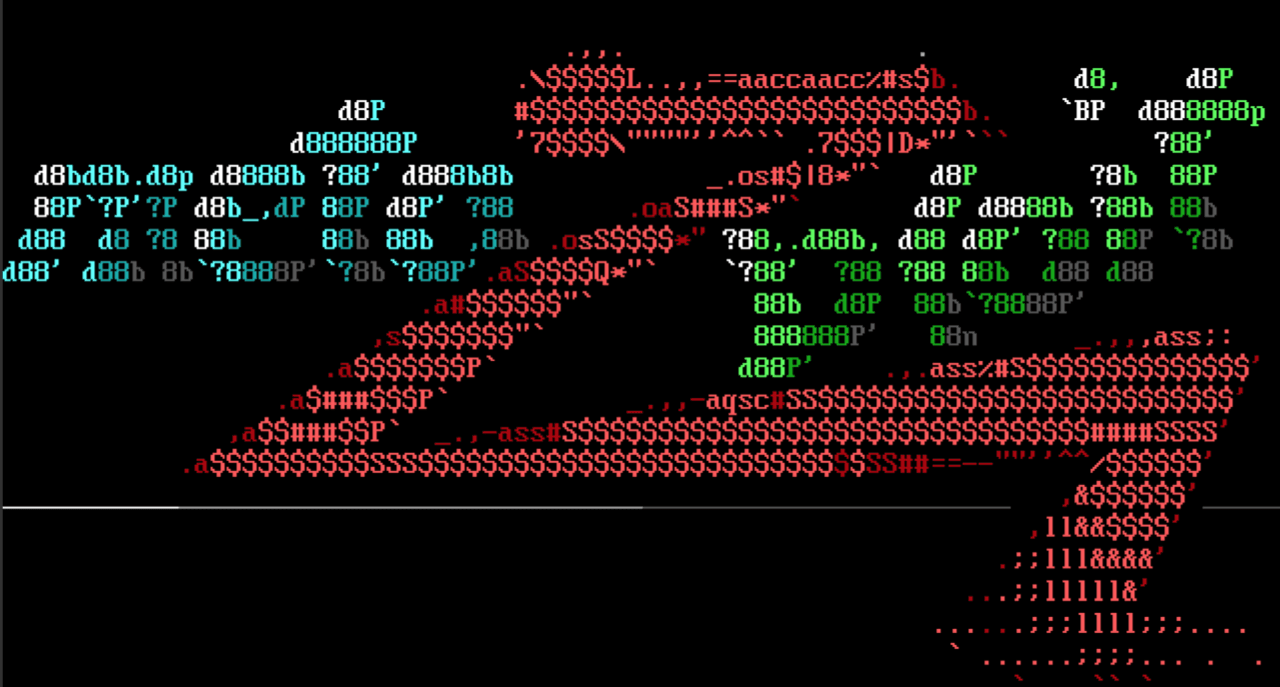
Nexus Repository Manager RCE
This week our very own Will Vu wrote a module for CVE-2020-10199 which targets a remote code execution vulnerability within the Nexus Repository Manager. The vulnerability allows Java Expression Language (JavaEL) code to be executed. While the flaw requires authentication information to leverage it, any account is sufficient. This would allow any registered user to compromise the target server.
Unquoted Service Path LPE
Community contributor h00die made some improvements for the “Trusted Service Path” module. These changes renamed the module from “Trusted Service Path” to “Unquoted Service Path”, making it more easily identified based on recent technique references. The improvements allow it to check each path option for writable permissions, making it work in instances where the C drive is not directly writable but an applicable subdirectory is. Additionally, the module will now leave the executable on disk in the event that it fails to automatically restart the affected service. This allows the operator to wait for the target system to reboot and be executed when the service starts.
.NET Execute Assembly
Community contributor b4rtik added a new post module for executing .NET assemblies in memory using Meterpreter sessions. This provides a lot of options for using tools external to Metasploit (such as GhostPack/Seatbelt) in the context of post-exploitation. Everything is better in memory, and with the rising popularity of C# post exploitation tools, we’re excited to see this functionality put to good use!
Attacker knowledge for the masses
AttackerKB is now available as an open beta! AttackerKB is a new community-driven resource for analyzing, discussing, and sharing different perspectives on which vulnerabilities make the most appealing targets for attackers (and why). The goal of AttackerKB is to help security professionals separate the signal from the noise and make more informed decisions around risk and the impact to their organization.
New modules (8)
- Nexus Repository Manager Java EL Injection RCE by wvu and Alvaro Muñoz, which exploits CVE-2020-10199
- Vesta Control Panel Authenticated Remote Code Execution by Mehmet Ince, which exploits CVE-2020-10808
- TP-Link Archer A7/C7 Unauthenticated LAN Remote Code Execution by Pedro Ribeiro and Radek Domanski, which exploits CVE-2020-10882, CVE-2020-10883, CVE-2020-10844, ZDI-20-334, ZDI-20-335, ZDI-20-336
- Liferay Portal Java Unmarshalling via JSONWS RCE by wvu, Markus Wulftange, and Thomas Etrillard, which exploits CVE-2020-7961
- ThinkPHP Multiple PHP Injection RCEs by wvu, which exploits CVE-2019-9082
- LimeSurvey Zip Path Traversals by Alejandro Parodi, Federico Fernandez, Matthew Aberegg, Michael Burkey, and h00die, which exploits CVE-2019-9960
- Zen Load Balancer Directory Traversal by Basim Alabdullah and Dhiraj Mishra
- Execute .net Assembly (x64 only) by b4rtik
Enhancements and features
- PR #13193 from h00die updated the Windows Unquoted Service Path module (formerly known as Trusted Service Path) to work better with modern Windows targets.
- PR #13216 from adfoster-r7 enables the Metasploit team to more quickly provide detailed and consistent feedback on pull requests.
- PR #13250 from busterb updates some unnecessary YAML warnings.
Get it
As always, you can update to the latest Metasploit Framework with msfupdate
and you can get more details on the changes since the last blog post from
GitHub:
If you are a git user, you can clone the Metasploit Framework repo (master branch) for the latest.
To install fresh without using git, you can use the open-source-only Nightly Installers or the
binary installers (which also include the commercial edition).