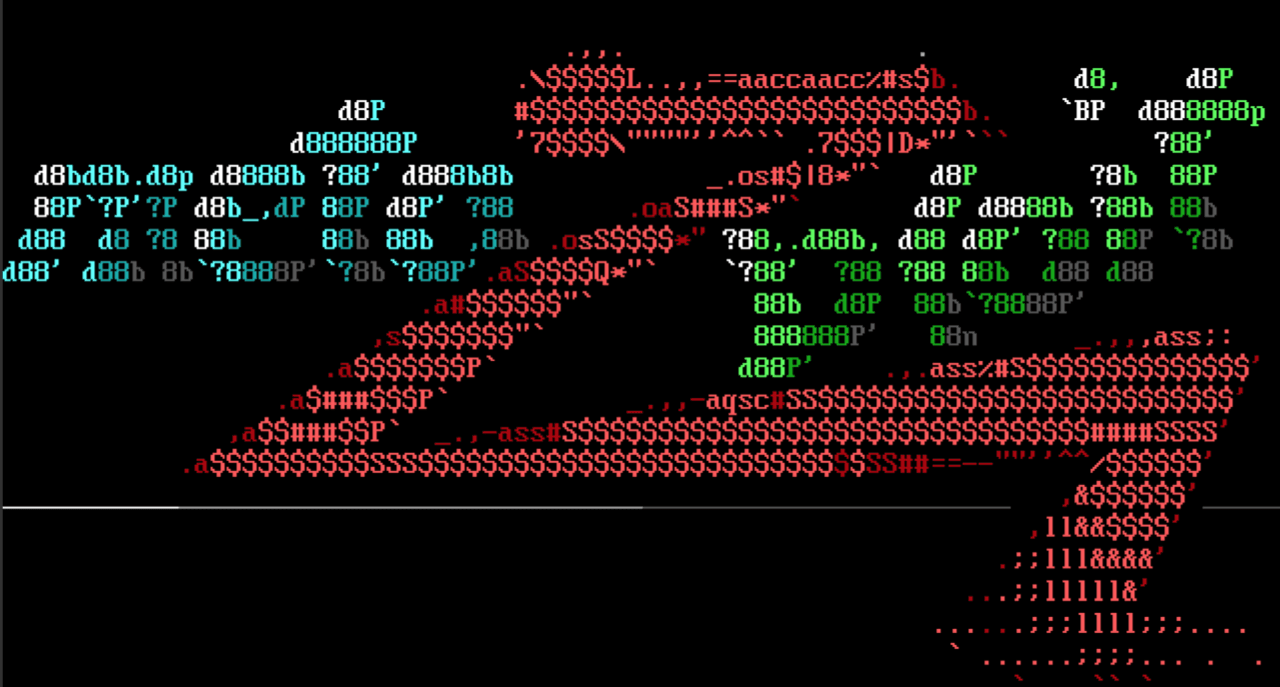
IBM DRM Exploit Chains
Wow, what a week it has been for IBM DRM! We landed three separate PRs from contributor pedrib which exploit CVE-2020-4427, CVE-2020-4428, and CVE-2020-4429. These include a SSH exploit module for a default user/password combination in IBM DRM which can grant root code execution after executing the sudo command, an unauthenticated arbitrary file download module, and a final exploit module that combines these three vulnerabilities to get remote unauthenticated code execution as the root user.
This is definitely one to keep an eye out for if you are doing any pen tests or security audits. Those running IBM DRM are highly encouraged to patch as soon as possible; these are high risk vulnerabilities that grant full access to the affected machines, and can easily be utilized to pivot throughout the network.
Ruby 2.7.x Fixes
Many users have been asking about deprecation errors that have been occurring when they upgraded to Ruby 2.7.0 or higher. Whilst Metasploit Framework has not yet been updated to fully support Ruby 2.7, we have made some updates to at least ease some of the pain.
The first change we made came in PR #13396, a temporary fix which silences all Ruby warnings to prevent users from getting confused or barraged by error messages. The second change we made was in PR #13392, which fixes some of the Rex HTTP warnings that were occurring in Ruby 2.7. We appreciate your patience whilst we work on improving Metasploit Framework to fully support Ruby 2.7. If you have any suggestions for code changes to better support Ruby 2.7, please open a PR and we will be happy to review your contribution!
I Can Haz Windows Privilege Elevation?
This week also added two Windows local privilege escalation exploits: one for CVE-2019-0808 a NULL pointer dereference in Windows 7 x86 that was used in an APT attack that was reported by Google. The module currently supports Windows 7 SP0 and SP1 and will grant a local attacker SYSTEM privileges.
The second local privilege elevation vulnerability is CVE-2020-0668 a trusted file overwrite DLL hijacking vulnerability within Windows Service Tracing. Whilst the vulnerability affects multiple platforms, the module has only been confirmed to work on Windows 10 x64 builds between 17133 and 18362, and grants local attackers SYSTEM privileges.We hope that the addition of these two modules will allow Metasploit users more opportunities to fully compromise affected hosts during pen tests and expand the impact of their pen testing reports.
Deserialization Exploits: Still Going Strong
Finally this week we have not one, but two unauthenticated RCEs involving deserialization bugs! The first module comes from wvu-r7 and is an exploit for ZDI-20-546, aka CVE-2020-10915, a deserialization vulnerability in the HandshakeResult method of VEEAM One Agent before the hotfix versions 9.5.5.4587 and 10.0.1.750 in the 9 and 10 release lines. This module does not require any credentials to exploit the vulnerability and grants attackers remote code execution as the user running VEEAM One Agent. Additionally wvu-r7 also added in a brand new CMD stager which uses Powershell to download and execute a binary with this PR. Way to go!
The second deserialization module comes from aus-hack and is an exploit for CVE-2019-10068, an unauthenticated RCE in the Kentico CMS platform versions 12.0.14 and earlier. The vulnerability occurs due to a lack of appropriate validation in the Staging Service and allows attackers who successfully exploit this vulnerability the ability to execute arbitrary commands as the user running Kentico CMS.
Hopefully the above examples showcase why deserialization vulnerabilites are such a big deal these days. However as a researcher you may be wondering how to create the payloads for these bugs. Well you are in luck, as this release also includes a PR from zeroSteiner to add a .NET deserialization tool, tools/payloads/ysoserial/dot_net.rb, which allows users to generate serialized payloads like YSoSerial.NET does! We look forwards to seeing what users come up with and contribute to the Framework!
New modules (9)
- IBM Data Risk Manager Unauthenticated Remote Code Execution by Pedro Ribeiro, which exploits CVE-2020-4427, CVE-2020-4428, and CVE-2020-4429
- HP Performance Monitoring xglance Priv Esc by Marco Ortisi, Robert Jaroszuk, Tim Brown, and h00die, which exploits CVE-2014-2630
- IBM Data Risk Manager a3user Default Password by Pedro Ribeiro, which exploits CVE-2020-4429
- TrixBox CE endpoint_devicemap.php Authenticated Command Execution by Anastasios Stasinopoulos, which exploits CVE-2020-7351
- Kentico CMS Staging SyncServer Unserialize Remote Command Execution by Justin LeMay, Manoj Cherukuri, and aushack, which exploits CVE-2019-10068
- Service Tracing Privilege Elevation Vulnerability by bwatters-r7 and itm4n, which exploits CVE-2020-0668
- Microsoft Windows NtUserMNDragOver Local Privilege Elevation by Clément Lecigne, Grant Willcox, and timwr, which exploits CVE-2019-0808
- Veeam ONE Agent .NET Deserialization by wvu, Edgar Boda-Majer, and Michael Zanetta, which exploits ZDI-20-546
- IBM Data Risk Manager Arbitrary File Download by Pedro Ribeiro, which exploits CVE-2020-4427 and CVE-2020-4429
Enhancements and features
- PR #13388 from busterb updates the sap_icm_urlscan module to use more up-to-date URLs from newer versions of SAP. It also removes some duplicate entries and normalizes the list. Thanks to Joris van de Vis for providing many of the newer SICF URL’s that were used in this PR!
- PR #13373 from adamgalway-r7improves the "No DB Connected" error message to provide more helpful error output.
- PR #13367 from adfoster-r7 adds enhancements to ensure that developer provided error messages are properly surfaced to users, which should allow users to better debug why errors are occurring.
- PR #13364 from zeroSteiner adds a .NET deserialization tool, tools/payloads/ysoserial/dot_net.rb, which allows users to generate serialized payloads like YSoSerial.NET does for research purposes.
- PR #13342 from HacKurx improves the logic for detecting PaX on Linux hosts by adding a new set of binaries to check for and by updating an outdated check in the pax_installed function of lib/msf/core/post/linux/kernel.rb.
- PR #13325 from cn-kali-team improves Meterpreter's ls command to support expanding environment variables in the path argument on Windows systems.
- PR #13313 from wvu-r7 adds improvements to msfconsole to warn the user that changing the current SSL options' value with set ssl true or set ssl false may require changing the RPORT value as well.
Bugs fixed
- PR #13406from zeroSteiner fixes 4 separate issues in the Rex DNS resolver implementation related to DNS enumeration, which were discovered whilst trying to land PR #12234.
- PR #13375 from VoidSec updates encoder/x86/unicode_upper and encoder/x86/unicode_mixed to require the BufferRegister option, which fixes issue #13372 reported by adfoster-r7.
- PR #13386 from timwr updates msfvenom to display an error when an Android stageless payload is used with the -x option. This a temporary fix for issue #10181 reported by xmagickx until the underlying issue can be resolved.