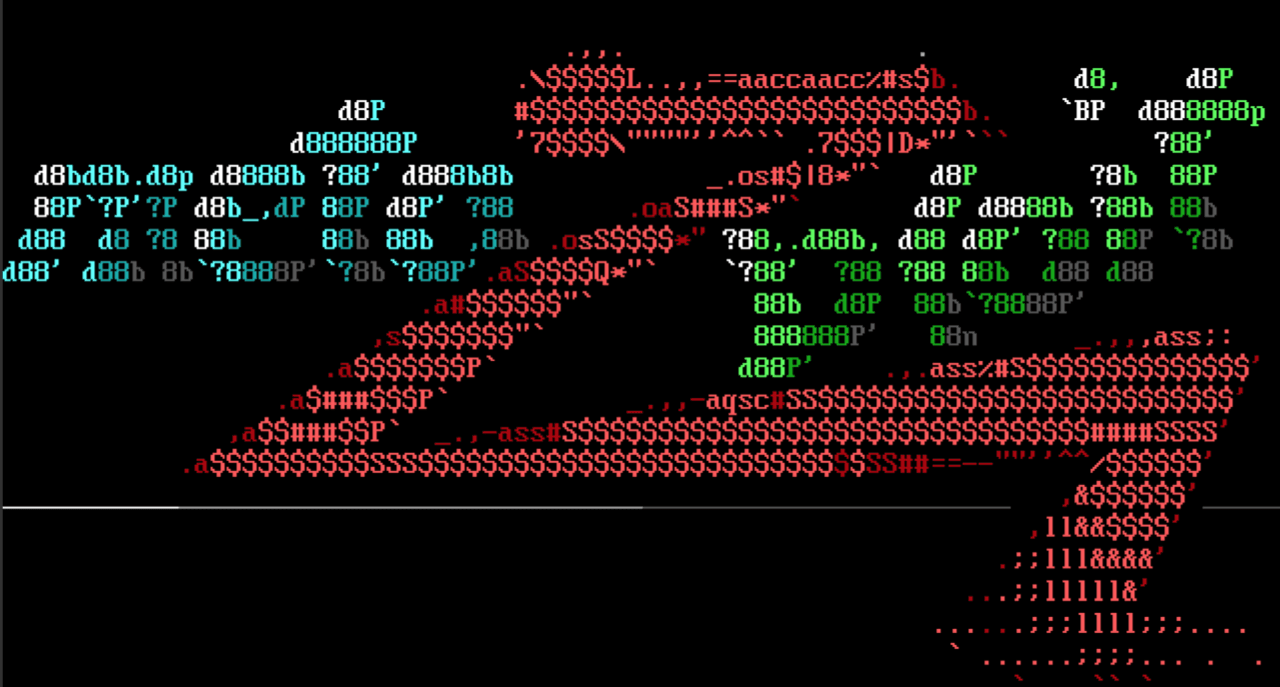
Struts2 Multi Eval OGNL RCE
Our very own zeroSteiner added exploit/multi/http/struts2_multi_eval_ognl, which exploits Struts2 evaluating OGNL expressions in HTML attributes multiple times (CVE-2019-0230 and CVE-2020-17530). The CVE-2019-0230 OGNL chain for remote code execution requires a one-time chain to enable the RCE gadget, which is handled automatically by the module. The OGNL gadget chain for CVE-2020-17530 will echo the command output. Both chains use a simple mathematical expression to ensure that evaluation occurs. These vulnerabilities are application dependent, and the user does need to know which CVE they are targeting. Setting the NAME parameter appropriately and using the check method to ensure evaluation takes place inside an HTML attribute are key to successful exploitation.
JuicyPotato-like Windows privilege escalation exploit
Exploit module exploits/windows/local/bits_ntlm_token_impersonation was added by Metasploit contributor C4ssandre. It exploits BITS connecting to a local Windows Remote Management server (WinRM) at startup time. A fake WinRM server listening on port 5985 is started by a DLL loaded from a previous unprivileged meterpreter session. The fake server triggers BITS and then steals a SYSTEM token from the subsequent authentication request. The token is then used to start a new process and launch powershell.exe as the SYSTEM user. It downloads a malicious PowerShell script and executes it on a second local HTTP server, not writing any files to disk. The exploit is based on decoder's PoC. It has been successfully tested on Windows 10 (10.0 Build 19041) 32 bits.
Pulse Connect Secure Gzip RCE
Metasploit contributor h00die added an exploit that targets Pulse Connect Secure server version 9.1R8 and earlier. The vulnerability was originally discovered by the NCC Group. It achieves authenticated remote code execution as root by uploading an encrypted config that contains an overwrite for a Perl template file. This module was made possible by rxwx, who shared the encryption code with the author. Admin credentials are required for successful root access. The module has been tested against server version 9.1R8.
New modules (8)
- SpamTitan Unauthenticated RCE by Christophe De La Fuente and Felipe Molina, which exploits CVE-2020-11698
- Pulse Secure VPN gzip RCE by David Cash, Richard Warren, Spencer McIntyre, and h00die, which exploits CVE-2020-8260
- Apache Struts 2 Forced Multi OGNL Evaluation by Alvaro Muñoz, Matthias Kaiser, Spencer McIntyre, and ka1n4t, which exploits CVE-2020-17530 and CVE-2019-0230
- SYSTEM token impersonation through NTLM bits authentication on missing WinRM Service. by Andrea Pierini (decoder), Antonio Cocomazzi (splinter_code), Cassandre, and Roberto (0xea31)
- Shodan Host Port by natto97
- WordPress Duplicator File Read Vulnerability by Hoa Nguyen - SunCSR Team and Ramuel Gall, which exploits CVE-2020-11738
- WordPress Easy WP SMTP Password Reset by h00die, which exploits CVE-2020-35234
- WordPress Total Upkeep Unauthenticated Backup Downloader by Wadeek and h00die
Enhancements and features
- PR 14566 from zeroSteiner Module auxiliary/server/socks_proxy replaces modules/auxiliary/server/socks4a.rb and modules/auxiliary/server/socks5.rb.
- PR 14538 from jmartin-r7 Improves Metasploit's XML importer error messages when data is not Base64 encoded.
- PR 14528 from zeroSteiner Clarifies Windows Meterpreter payloads description support of XP SP2 or newer.
- PR 14522 from axxop Replaces the hardcoded default Shiro encryption key with a new datastore option that allows users to specify rememberMe cookie encryption key.
- PR 14517 from timwr Changes the osx/x64/shell_reverse_tcp payload to be generated with Metasm and captures and sends STDERR to msfconsole.
- PR 14509 from egypt This adds a Java target to the Apache Solr RCE exploit module and fixes several payload issues.
- PR 14444 from dwelch-r7 Adds a couple of missing methods from the remote data services for adding and deleting routes.
Bugs fixed
- PR 14589 from timwr Fixes a file download issue with the Android Meterpreter's download command.
- PR 14532 from bcoles Fixes a NoMethodError exception caused by the Msf::Post::Common mixin not being included in post/android/capture/screen.
- PR 14530 from jmartin-r7 Fixes a failing test on macOS caused by IPv6 vs IPv4 result precedence.
- PR 14475 from dwelch-r7 Fixes the EICAR canary check.
- PR 14334 from Summus-git Fixes a x86 linux bind shell payloads socket closing bug.
Get it
As always, you can update to the latest Metasploit Framework with msfupdate
and you can get more details on the changes since the last blog post from
GitHub:
If you are a git user, you can clone the Metasploit Framework repo (master branch) for the latest.
To install fresh without using git, you can use the open-source-only Nightly Installers or the
binary installers (which also include the commercial edition).