When you're planning for the year ahead in cybersecurity, there's always part of you that's trying to play fortune-teller. You know what risks matter now, and the processes and resources you need to respond to them, but what threats might emerge over the coming 12 months — or 12 weeks, for that matter? What if the landscape changes before you have a chance to react?
Now, imagine you're doing that crystal-ball-peering exercise while still in your first 6 months in a leadership role. That's the situation a first-year CISO finds themselves in — and while it's a little precarious, it's equally ripe with opportunity.
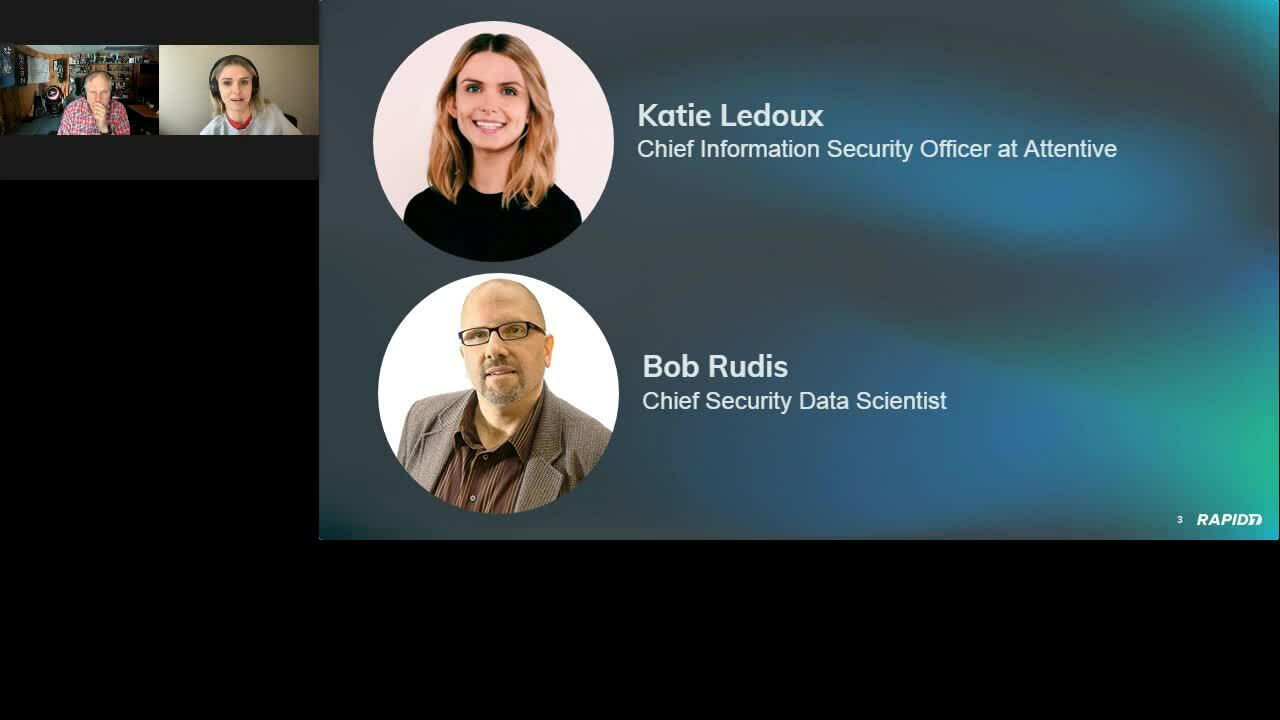
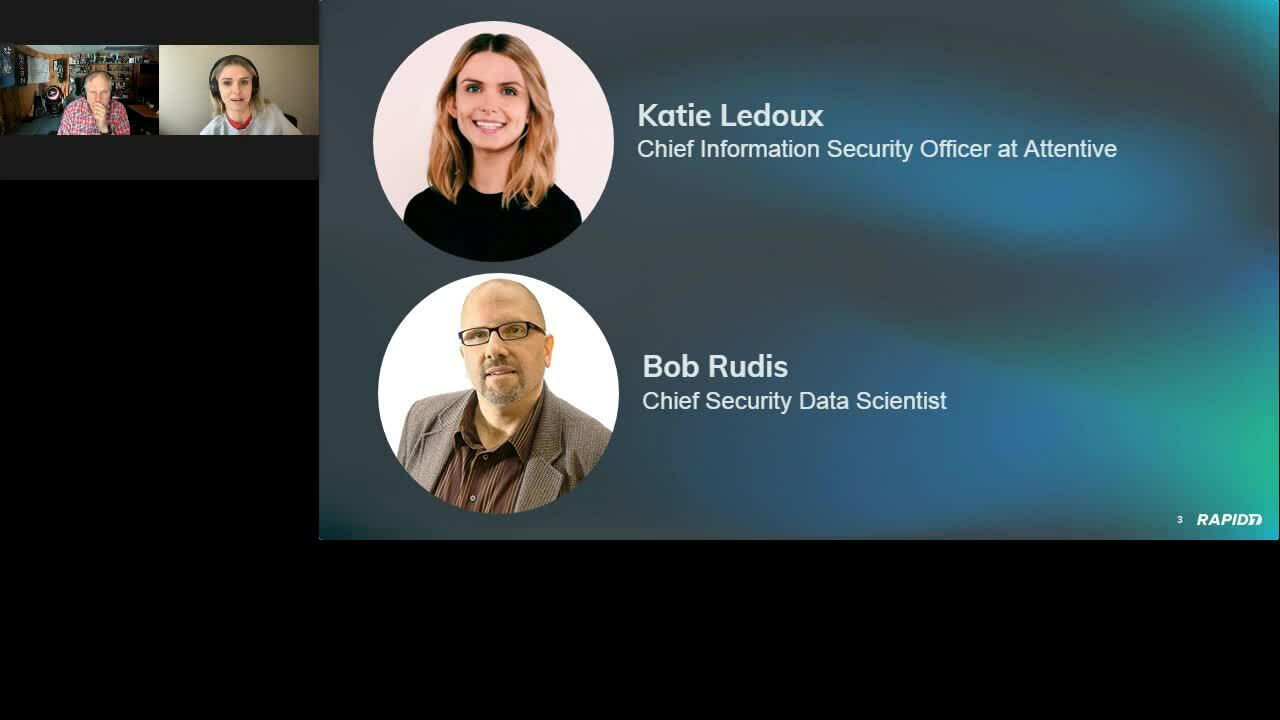
On Thursday, November 17, Rapid7's Chief Security Data Scientist Bob Rudis sat down with Katie Ledoux, Chief Information Security Officer at SMS marketing startup Attentive, to dive into how she's tackling the challenges of planning for her security team's needs in 2022 while navigating her new role.
Freedom to build from the ground up
At just 4 months into her tenure at Attentive as of November 2021, Katie has found a sense of freedom and clarity in being able to start from square one.
"Getting to build a program from scratch is actually kind of amazing... especially because I've made so many mistakes before," she said. It was the process of learning from those mistakes in less high-stakes roles — including a 5-year stint at Rapid7 — and building back more effectively that helped her understand what to prioritize as a new CISO. Now, she has the opportunity start with the things she knows she and her first few hires can do well, addressing lower-complexity, higher-risk areas and seeing progress quickly.
"I'm starting off as very trusted — and I won't lose that trust unless I screw up," she quipped.
The importance of mentorship
For Katie, her own experience is only one part of keeping leadership's trust and avoiding unforced errors. Getting the insights and expertise of others is essential.
“I have the most amazing mentor," she said, going on to note that she cold-LinkedIn-messaged him after hearing him speak on a cybersecurity podcast. He responded, they connected, and the rest is history. He was particularly instrumental in helping her navigate the executive planning process as she ramped into her new role. While she wasn't as well-versed in this area when she started, she leaned on the advice of her mentor and her teammates where she needed to.
"I consider my willingness to very loudly share things that I don't know how to do to be one of my greatest strengths," Katie said. "I'm constantly, constantly asking for help, which I think leads to better outcomes," she continued.
Creating alignment on risk — and budget — priorities
One of the first things Katie's mentor told her was to rethink the way she went about determining top-priority risks.
"I actually don't dictate what our top risks are," Katie said. Instead, she leads and facilitates a security committee and insists on collaborative input.
Head to our 2022 Planning series page for more – full replay available soon!
“You basically lay out the facts and let people decide what the company's risk appetite is," she explained. "They're going to try to get you to tell them what the biggest risks are," she went on to say. But if you simply dictate the risk priorities unilaterally, it's easy to lose buy-in as the months go on.
"They don't really feel ownership over that work," Katie pointed out, "and as soon as other priorities get in the way — you know, the job description that they were hired to do — they drop the security and risk remediation work."
One of the keys of this setup is to keep the committee small — 6 to 8 people, Katie recommended. The right stakeholders will do a better job of ranking risks than one individual ever could.
Plus, with collective buy-in, getting budget for your security priorities becomes easier. For example, at Attentive, Katie shares a budgeting bucket with the engineering team. If the head of engineering helps decide what the top risks are, that makes it a whole lot less likely that Katie will end up in a tug-of-war with them over resources.
A new CISO's top 3 priorities for 2022
With a solid structure in place for collaborative risk prioritization, what core components should CISOs include in their 2022 plan? Katie highlighted 3 key areas to put center-stage.
1. Hiring
It's no secret that there's a cybersecurity skills shortage, and building a pipeline of talent is critical for the coming year. In Katie's case, she came in with a map of functions to hire for, job descriptions, and requisitions to post on the website — only to realize she had to rethink her approach. Her mentor suggested she spend 25% of her time interviewing general security candidates, regardless of whether or not she had a specific job opening for them right now.
There are a few reasons why this approach makes sense. As Bob pointed out, when talent is tough to find, you might not be able to bring in people who are mature enough in their careers to fill a specific niche. Plus, at startups and other fast-moving companies, the problem you had in mind when you posted a job listing might be gone by the time you fill the position.
Now, Katie has several evergreen, general cybersecurity job postings that specifically call out that it's not necessary to have all the skill sets listed. Instead, she prioritizes bringing on talented candidates who can help meaningfully in any of the key areas that matter to the organization.


2. Compliance
While compliance has become something of a dirty word in some security circles, Katie believes it can provide a great floor for a security program. The key is to do it thoughtfully.
After all, working toward a compliance certification like SOC 2 provides a clear priority that you can act on and show progress toward. If you design the components and controls you're using carefully around this framework — and steer clear of the companies that tell you they can get you SOC 2-compliant in a month — you'll avoid having a bunch of check-boxes and instead build a solid base of accountability.
For example, are all your assets really encrypted at rest? If you're touting SOC 2 compliance and actively controlling for those requirements, you'll know — and be able to remediate quickly if needed.
3. Identifying your top risks
Let's face it: If you're a new CISO, you're going to need to go a board meeting some time soon (if you haven't already) and explain what your organization's most urgent risks are — and what you're doing to fix them.
Build an initial risk matrix, and take your findings to your security committee for input and prioritization. From there, you'll have a solid foundation to work from that will help you show the board, leadership, and yourself how you and your team are progressing toward your 2022 priorities.
Measuring success
While others tend to favor quantitative metrics in charting their security plan's progress, Katie suggested going a level above that. The scores and numbers that make sense to security pros might not resonate with the CTO or other leadership.
“The best way for me to measure progress is probably in looking at risk management," she said. "It's my job to mitigate risks at an acceptable level."
The top risks you identify for 2022 should be improving over time — and by 2023, you should have new ones. If you're able to leave last year's risks behind and move onto new ones, that's a good sign you're making progress. And if you need help in charting that course, don't be afraid to rely on others' expertise.
"LinkedIn-message random people and be like, 'How do I do my job?'" Katie recommended, only half-jokingly. "Don't be shy," she went on to insist. "No one knows everything."
So far, the collaborative, advice-seeking strategy is working out for Katie. It won't be long before her own LinkedIn inbox is full of first-year CISOs looking to learn how a seasoned pro gets it done.
Want more 2022 planning tips from industry experts?
Sign up for our webinar seriesArticle Tags
Related blog posts

Exposure Management
Three Ways Gartner® Says Exposure Management Is Reshaping SecOps
Rapid7

Security Operations
20/20 Cybersecurity: Lessons Learned in 2024 and Strategies for a Stronger 2025
Rapid7

Exposure Management
How CISOs’ Roles – and Security Operations – Will Change in 2024
Jaya Baloo

Security Operations
Showcasing SecOps Metrics That Matter
Rapid7
