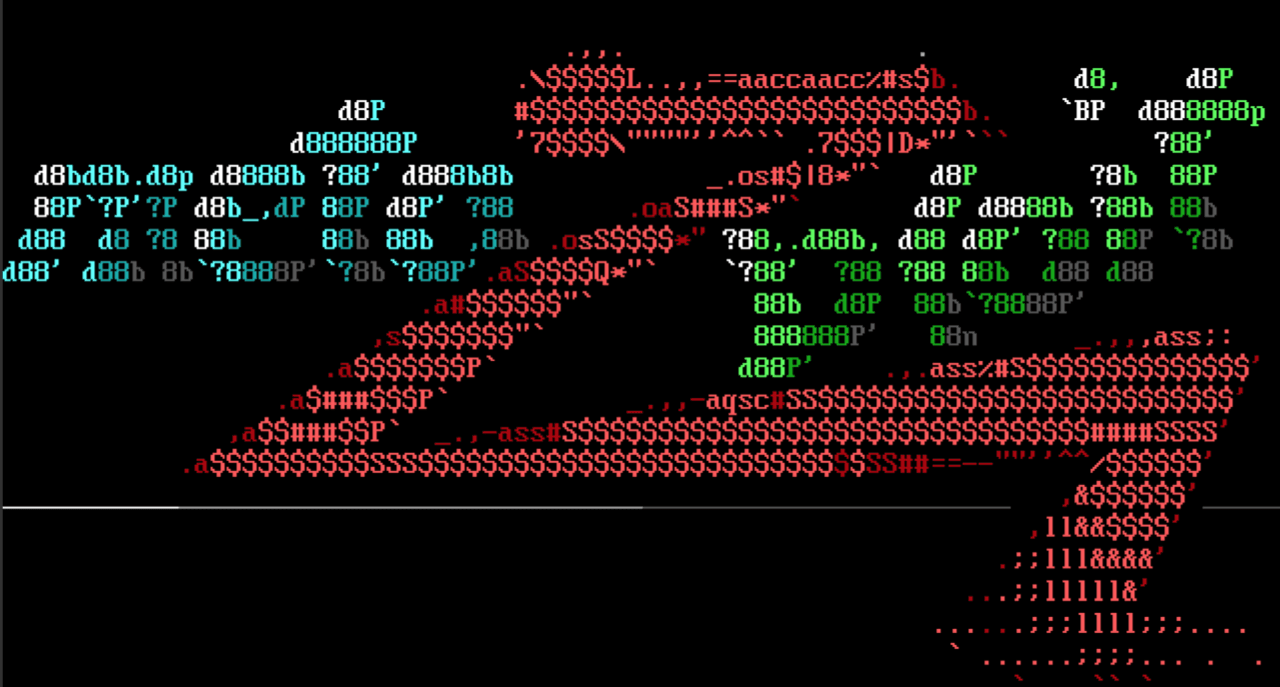
Zimbra Auth Bypass to Shell
Ron Bowes added an exploit module that targets multiple versions of Zimbra Collaboration Suite. The module leverages an authentication bypass (CVE-2022-37042) and a directory traversal vulnerability (CVE-2022-27925) to gain code execution as the zimbra user. The auth bypass functionality correctly checks for a valid session; however, the function that performs the check does not return and instead proceeds with execution. Because of this, an attacker only needs a valid account to get a shell. The directory traversal vulnerability lives in Zimbra’s Zip file extraction functionality, enabling an attacker to write an arbitrary file to a web directory. Coupling those two vulnerabilities together, the module writes a JSP shell to the target via a POST request to the /mboximport endpoint. These vulnerabilities have been reported as exploited in the wild.
Another Deserialization Flaw in Exchange
Our very own zeroSteiner submitted a new module that exploits an authenticated .Net deserialization vulnerability in Microsoft Exchange. The vulnerability is due to a flaw in the ChainedSerializationBinder, a type validator for serialized data. Provided the attacker has credentials for at least a low-privileged user, this exploit will result in code execution as NT AUTHORITY\SYSTEM.
New module content (2)
- Zip Path Traversal in Zimbra (mboximport) (CVE-2022-27925) by Ron Bowes, Volexity Threat Research, and Yang_99's Nest, which exploits CVE-2022-37042 - adds a module for CVE-2022-27925 and CVE-2022-37042. An attacker can exploit these issues to bypass authentication and then exploit a ZIP file path directory traversal vulnerability to gain RCE as the zimbra user.
- #16915 from zeroSteiner - A new module has been added for CVE-2022-23277 which is another ChainedSerializationBinder bypass that results in RCE on vulnerable versions of Exchange prior to the March 8th 2022 security updates.
Enhancements and features (6)
- #16701 from jbaines-r7 - This improves the original auxiliary/scanner/http/cisco_asa_asdm scanner module by adding the ability to brute force the Cisco ASA's Clientless SSL VPN (webvpn) interface. The old module has been replaced by two new modules, this one and auxiliary/scanner/http/cisco_asa_asdm_bruteforce, which provide brute force of the Cisco ASA's ASDM interface directly.
- #16898 from bcoles - This adds a Msf::Post::Windows::Accounts.domain_controller? method and removes is_dc? methods from several modules in favor of using the new method.
- #16899 from bcoles - This removes the domain_list_gen Meterpreter script which has been replaced by the post/windows/gather/enum_domain_group_users post module.
- #16907 from bcoles - This improves the MS10-092 LPE exploit module. It uses the new task manager mixin, adds additional module metadata, and documentation.
- #16912 from bcoles - This removes the sound recorder Meterpreter script. It has been replaced by the record_mic post module.
- #16938 from zeroSteiner - The ldap_query module has been updated to allow the stored query templates to specify a Base DN prefix. Additionally, two ADCS-related queries that then use this to enumerate certificate authorities and certificate templates.
Bugs fixed (4)
- #16925 from rbowes-r7 - This fixes some issues with the payload generation in the UnRAR generic exploit module (CVE-2022-30333). This also adds the option to provide its own custom payload.
- #16931 from bcoles - A bug has been fixed in Rex::Post::Meterpreter::Extensions::Stdapi::AudioOutput.play_file where a channel would be opened before the path parameter was verified. This could lead to dangling channels being opened which would not be closed until Meterpreter was shut down.
- #16935 from adfoster-r7 - Fixes multiple SSH warnings when loading msfconsole on Ubuntu 22.04 or the latest Kali version.
- #16936 from adfoster-r7 - Fixes a crash when using evasion modules when mingw is not present on the host machine for generating encrypted payloads.
Get it
As always, you can update to the latest Metasploit Framework with msfupdate
and you can get more details on the changes since the last blog post from
GitHub:
If you are a git user, you can clone the Metasploit Framework repo (master branch) for the latest.
To install fresh without using git, you can use the open-source-only Nightly Installers or the
binary installers (which also include the commercial edition).