For years, cybersecurity professionals have relied on a familiar metric to dictate their day-to-day priorities: the Common Vulnerability Scoring System (CVSS). In today’s hyper-connected, sprawling IT environments, utilizing a static severity score as the ultimate arbiter of risk creates opportunities for threat actors. While defenders chase down theoretical, high-scoring alerts, adversaries are quietly targeting the truly exploitable, business-critical exposures that slip through the cracks.
In a recent report, Gartner® highlighted a projection:
"By 2028, organizations that prioritize exposures using threat intelligence, asset context, exploitability modeling and security control validation will reduce breach likelihood by at least 70% compared to peers relying primarily on CVSS-based vulnerability prioritization." [1]
This affirms what many seasoned practitioners have suspected for years: there’s an abundance of vulnerability findings, but a lack of actionable context.
Static scores. Reactive security.
Most vulnerability management programs evolved during a time when the attack surface was relatively static, adversary tooling was rudimentary, and remediation capacity generally exceeded the volume of new disclosures. Today, enterprises are confronted with vulnerabilities scattered across complex cloud architectures, SaaS applications, and intricate supply chains.
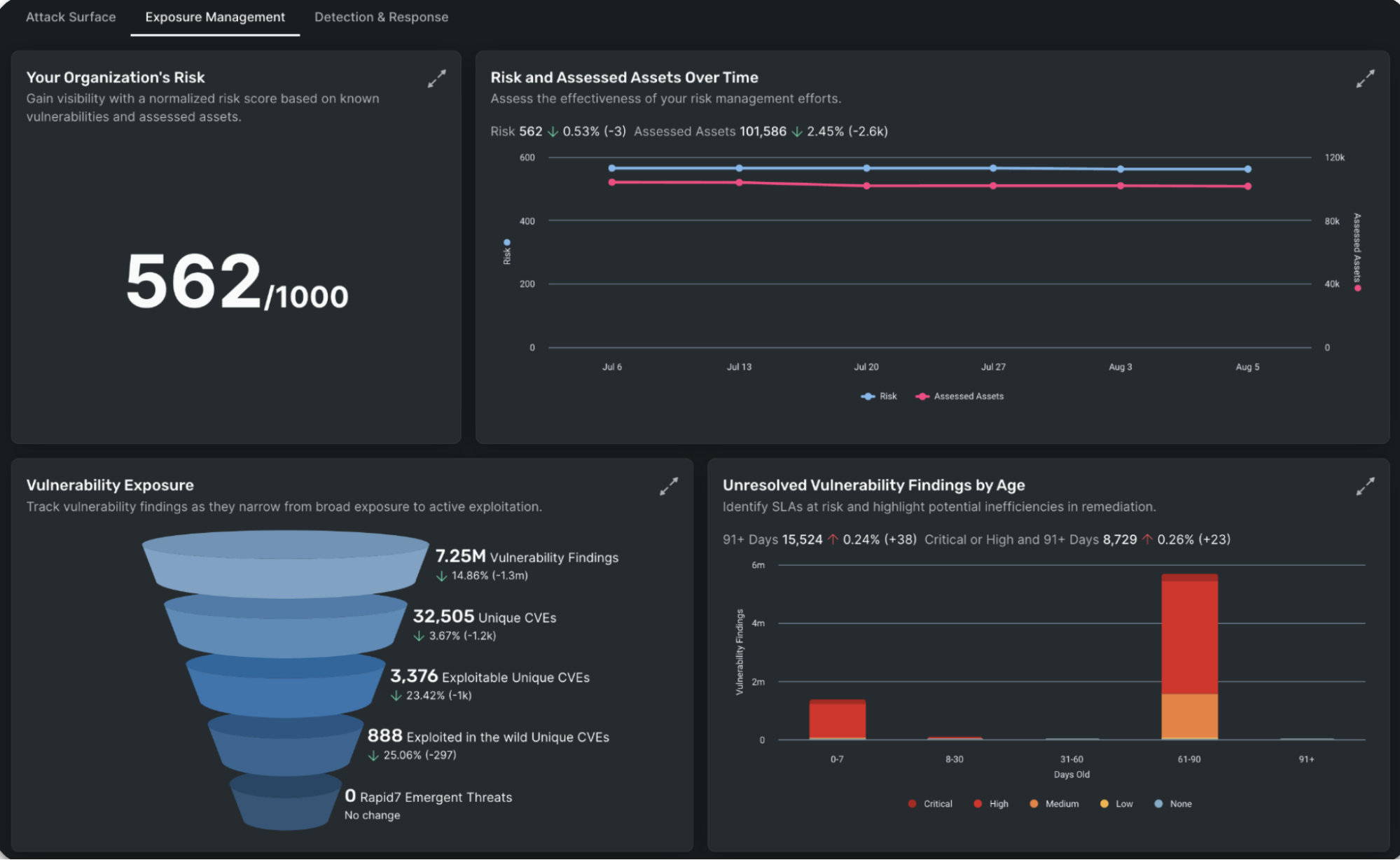
In this modern threat landscape, CVSS alone is insufficient because it measures theoretical severity, does not factor in whether an attacker is actually using the vulnerability in the wild, or consider the business value of any affected assets. According to Gartner®, fewer than 10% of vulnerabilities are exploited, yet most are treated as urgent [1]. This all leads to prioritization paralysis, where security teams spend countless hours patching vulnerabilities that pose low material risk to the business. The legacy approach rewards what is auditable rather than what is genuinely impactful.
The path toward smarter prioritization
To break free from endless patching and ineffective risk reduction practices, security professionals are shifting toward a context-driven model. As Gartner notes, strong exposure prioritization requires integrating four critical elements: threat intelligence, asset context, data science, and security control validation. Organizations are approaching these elements in a few practical ways:
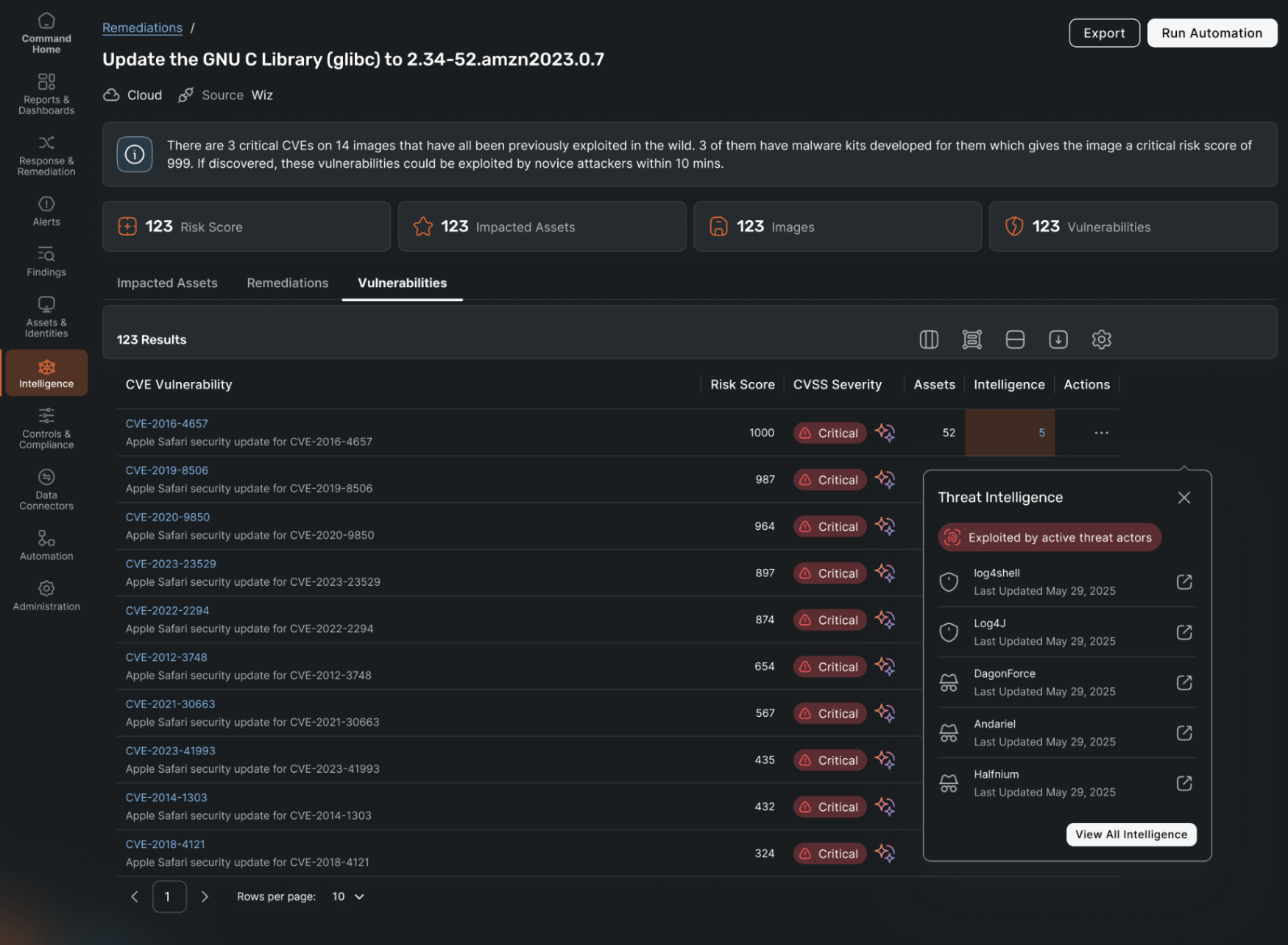
Threat intelligence to establish relevance
Instead of just asking how severe a vulnerability is, modern exposure management asks whether an exposure is relevant to a threat actor who is capable of exploiting it right now. By embedding threat intelligence into each vulnerability finding, teams shift the focus from theoretical to risk active exploitation. It introduces the adversary's perspective by identifying known exploited vulnerabilities, public or private exploit availability, and targeted campaigns. By filtering out exposures with no evidence of attacker interest, organizations can instantly collapse large vulnerability backlogs and focus only on relevant threats.
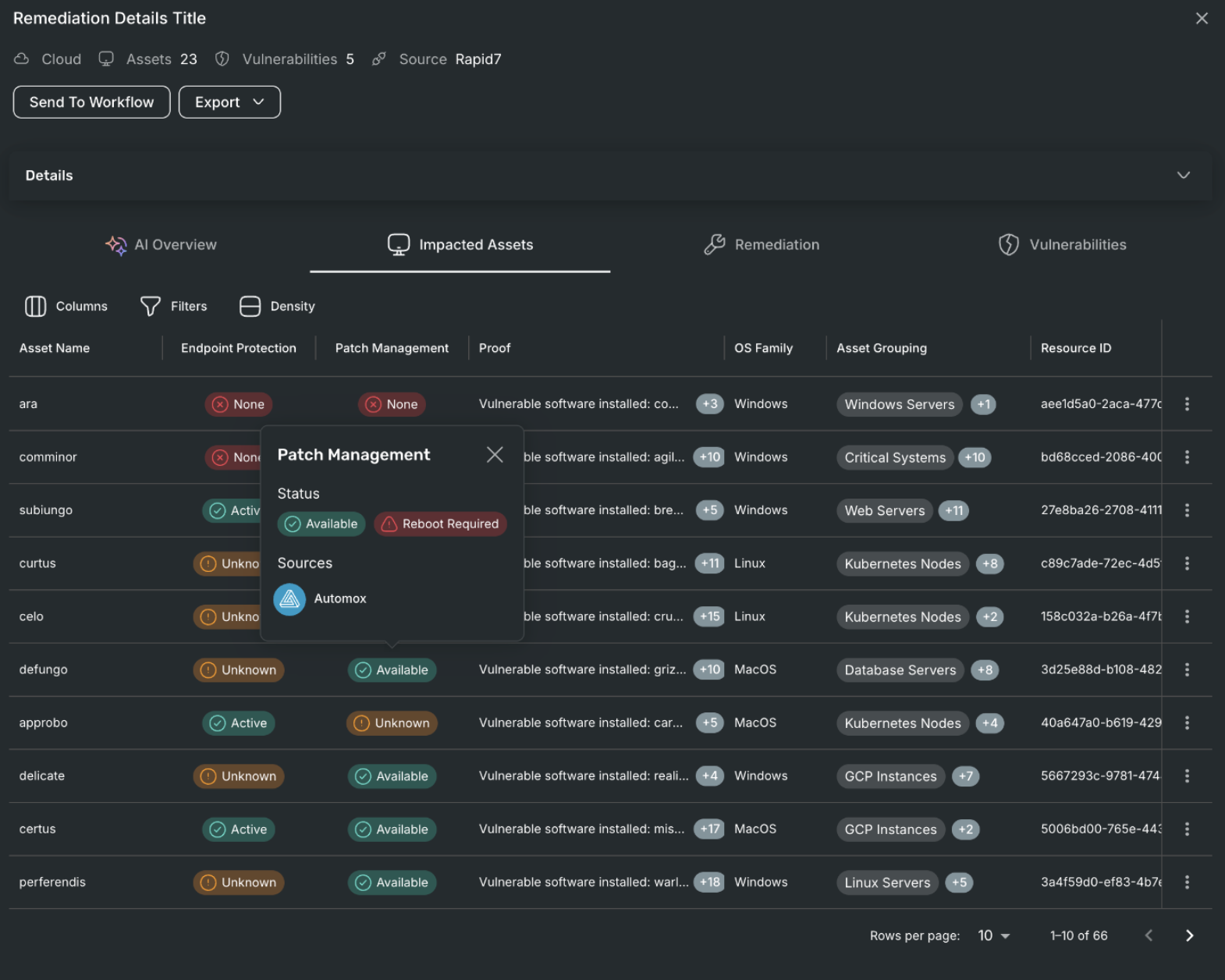
Asset context and business criticality to define impact
Not all assets are created equal. A critical vulnerability on an isolated, internal test server is vastly different from the same vulnerability on a public-facing cloud workload processing customer sensitive data. Asset context enriches exposure data with crucial business information: what the asset is, its external accessibility, and its relationship to core business functions. Without this context, security teams waste disproportionate effort on low-impact systems, treating every critical alert as an equal emergency.
Exploitability modeling for predicting breach likelihood
Security analysts often struggle to assess exploitability given the overwhelming volume of vulnerabilities. By using predictive models like the Exploit Prediction Scoring System (EPSS), organizations can analyze large datasets of historical exploitation to identify latent risks. Exposure assessment platforms should display this data alongside each exposure finding to make it easier to predict the vulnerabilities most likely to become attacks.
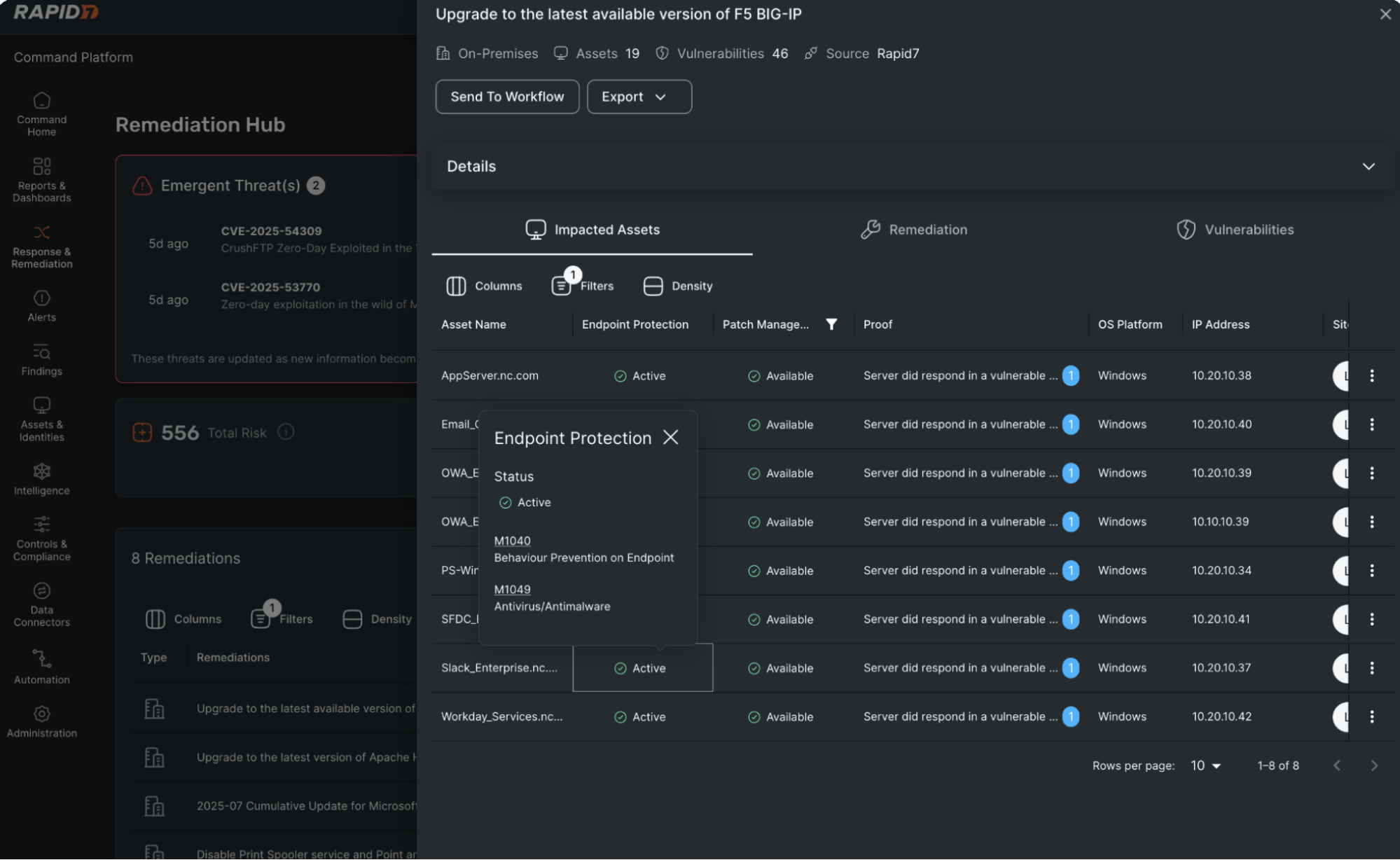
Security control validation
An exposure that appears highly exploitable in theory might be neutralized by existing defenses. By integrating security and policy controls, you can evaluate exposures in the context of endpoint protection and identity management. This passive validation confirms whether an attacker can realistically exploit the exposure in your specific environment.
Unified exposure management
Individually, each element highlighted above provides incremental value, but when integrated, they fundamentally transform how prioritization decisions are made. This integrated model ensures that remediation efforts are mobilized only after priorities have been validated in the context of the business and the current threat landscape. It transitions vulnerability management from a purely technical, tool-centric exercise into a strategic, process-driven risk decision.
Security leaders must measure success not by the sheer number of vulnerabilities closed, but by the demonstrable reduction of exploitable exposures and the alignment of remediation efforts with actual attacker behavior. Operationalizing these four elements requires a unified platform that eliminates the silos between vulnerability management, cloud security, and threat intelligence. You cannot manually stitch together disconnected spreadsheets and hope to outpace modern adversaries. This is where forward-thinking organizations are leaning on comprehensive, end-to-end solutions like Rapid7 Exposure Command that seamlessly aggregate visibility across on-premises and dynamic cloud environments. With deep, native integration of Rapid7 Cloud Security capabilities, teams can instantly map asset criticality and external accessibility within complex, ephemeral cloud architectures. Furthermore, by infusing world-class threat intelligence and active exploit data directly into exposure findings, Rapid7 enables security teams to cut through the noise, validate security controls, and pinpoint the exact exposures that matter most—all with minimal friction.
[1] Gartner, Prioritize What Attackers Will Exploit: 4 Elements of Strong Exposure Prioritization, Jonathan Nunez, 5 March 2026.
Related blog posts

Exposure Management
You Don’t Have a Security Problem, You Have a Visibility Problem
James Davis

Industry Trends
Geopolitics and Cyber Risk: How Global Tensions Shape the Attack Surface
Jeremy Makowski

Industry Trends
Pen, Paper, and Preparedness: What the UK's Latest Cyber Guidance Really Means
Emma Burdett

Exposure Management
Preparing for Unknown Risks: How to Better Prepare for Risks You Can't See Yet
Robin Long

