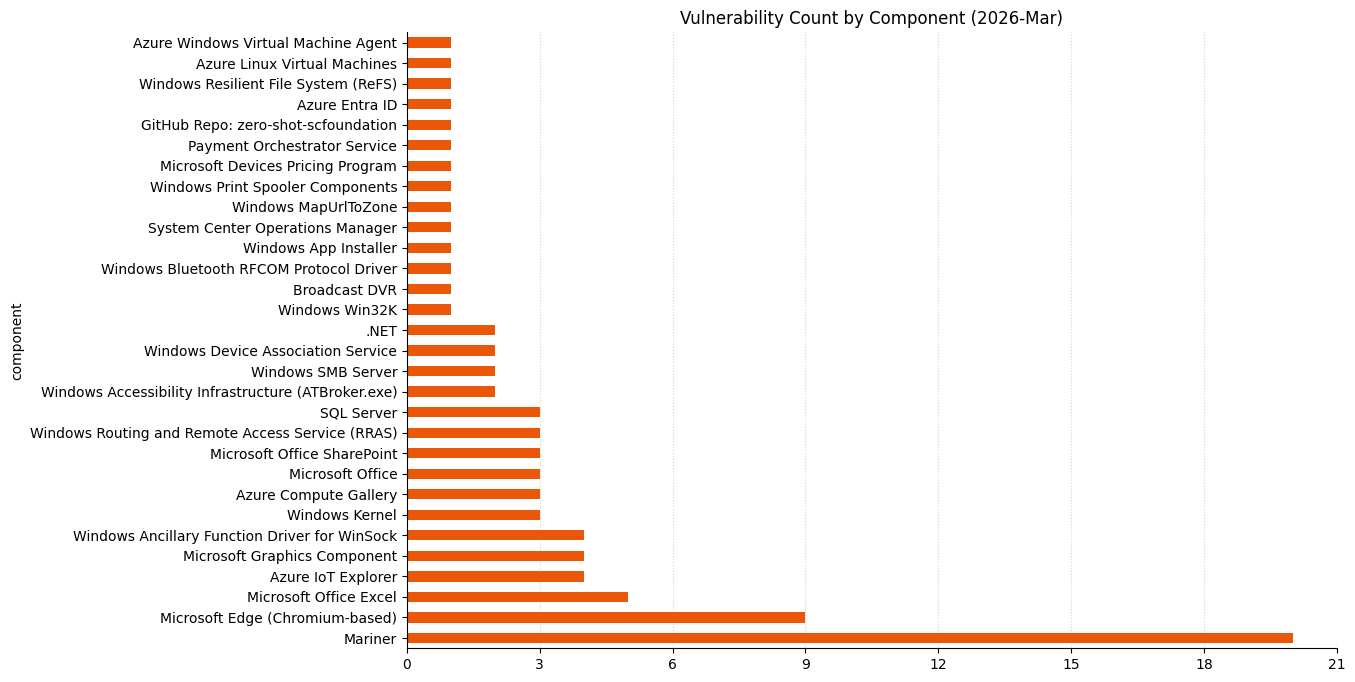
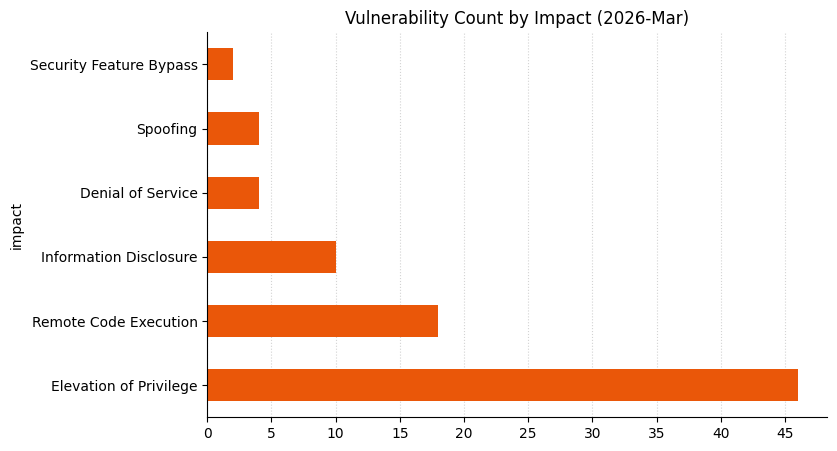
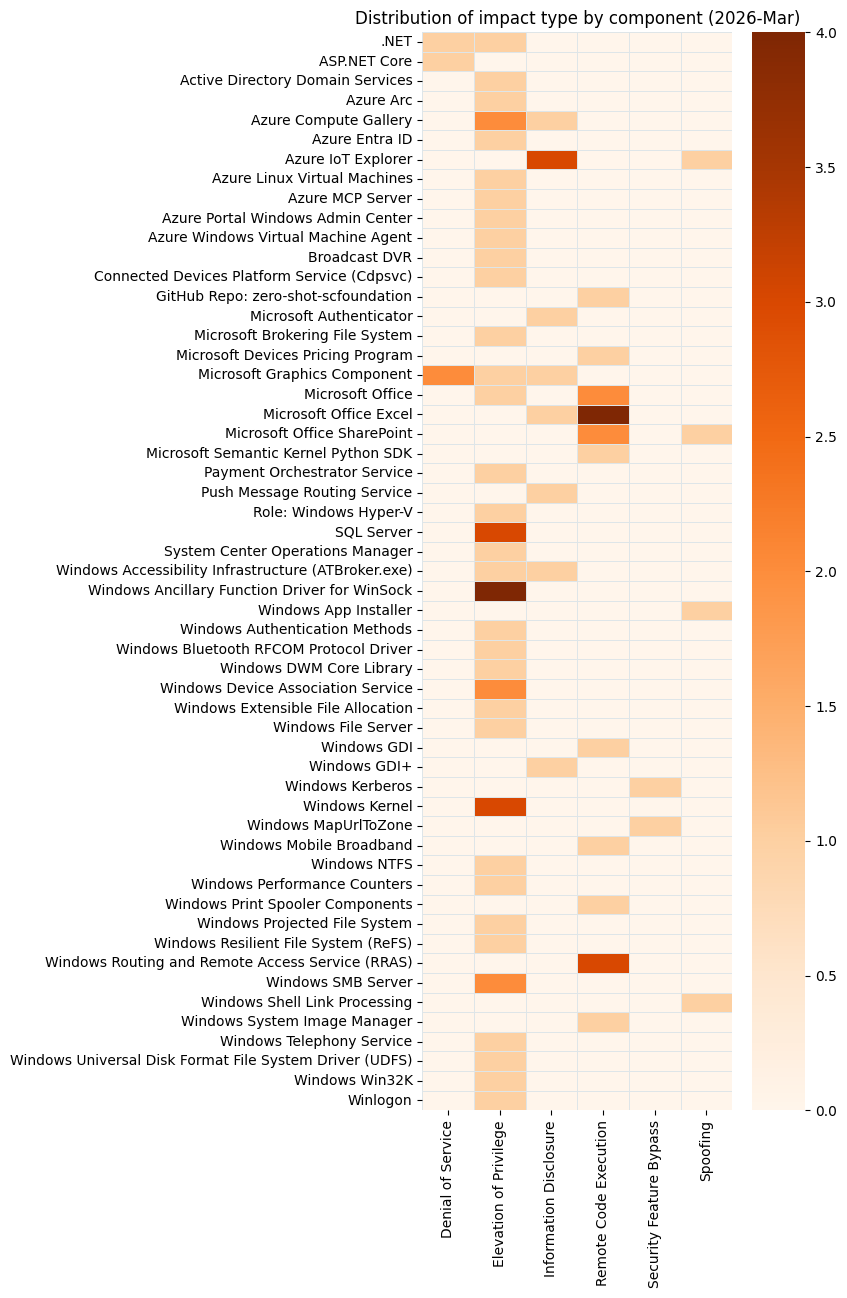
Microsoft is publishing 77 vulnerabilities this March 2026 Patch Tuesday. Microsoft is aware of public disclosure of two of today’s vulnerabilities, but without evidence of exploitation in the wild for any (yet), so there are no Microsoft additions to CISA KEV today. Earlier in the month, Microsoft provided patches to address nine browser vulnerabilities, which are not included in the Patch Tuesday count above.
SQL Server: zero-day remote EoP
SQL Server often goes several months in a row without any mention on Patch Tuesday. Today, however, all versions from the latest and greatest SQL Server 2025 back as far as SQL Server 2016 SP3 receive patches for CVE-2026-21262, a SQL Server elevation of privilege vulnerability. This isn’t just any elevation of privilege vulnerability, either; the advisory notes that an authorized attacker can elevate privileges to sysadmin over a network. The CVSS v3 base score of 8.8 is just below the threshold for critical severity, since low-level privileges are required.
Microsoft is aware of public disclosure, so while they assess the likelihood of exploitation as less likely, it would be a courageous defender who shrugged and deferred the patches for this one. Most SQL Server admins and security teams concluded many years ago that exposing SQL Server directly to the internet was not a good idea. Then again, popular search engines for internet-connected devices describe tens of thousands of SQL Server instances, and they can’t all be honeypots.
What could an attacker do as SQL Server sysadmin? Beyond exfiltrating or interfering with the database itself, the obvious target is xp_cmdshell, which allows direct callouts to the underlying OS. The good news is that xp_cmdshell is disabled by default as far back as SQL Server 2005; the bad news is that anyone acting as SQL Server sysadmin can enable it in seconds. At that point, the attacker is acting with the full privileges of the security context under which SQL Server runs, which is ideally a purpose-built account designed with least privilege in mind. If you want to hear some hair-raising stories, you have only to ask any incident response veteran if they’ve ever seen it set up differently.
Anyone paying for Extended Security Updates (ESU) for SQL Server 2014 or SQL Server 2012 may be forgiven for wondering why there’s no security update for those venerable versions of the world’s most widely deployed closed-source database product. We can hope that the vulnerability described by CVE-2026-21262 was introduced in newer codebases only.
.NET: zero-day DoS
Attackers fond of low-effort denial of service attacks against .NET applications will be checking out CVE-2026-26127 today. Microsoft is aware of public disclosure. While the immediate impact of exploitation is likely contained to denial of service by triggering a crash, opportunities for other types of attacks might emerge during a service reboot. Alternatively, if a log forwarder or security agent is impacted, even for a brief period of time, an attacker might carry out an attack in that moment hoping to evade detection under cover of this artificial darkness. Even if a low-skilled attacker simply causes downtime, in some contexts that could be enough to cause an SLA breach or loss of revenue, or at the very least cause a bleary-eyed defender to get paged in the middle of the night.
Authenticator: QR code impersonation
Microsoft Authenticator mobile app users on both iOS and Android should update to the latest version to prevent exploitation of CVE-2026-26123, which involves a malicious app disguising itself as Microsoft Authenticator. Exploitation succeeds when the malicious app receives enough information to impersonate the user.
Authenticator-type apps are often installed on a personal device, but it's not unusual for them to provide multi-factor authentication (MFA) codes for production services in a bring-your-own-device context. This is as good a time as any for defenders to consider how well their mobile device management policy covers app choice enforcement and patching for MFA apps.
The CVSS v3 base score of 5.5 might appear unremarkable, and exploitation requires user interaction, since the user must install the malicious app in the first place. However, exploitation could begin via an attacker-controlled link, or even a malicious QR code that drives users to the malicious app, and a motivated attacker with a physical presence near the user base might well consider this option.
According to Khaled Mohamed, the researcher who discovered this vulnerability, the legitimate Microsoft Authenticator app did not previously register itself as the handler for deep links into its own custom URL scheme. A malicious app could exploit this gap by simply registering itself as the default handler. He further notes that in this scenario, a user of a mobile device with a malicious app installed only needs to click a generic “Open link” dialog, rather than expressly selecting the malicious app each time. This means that the Microsoft advisory is perhaps too optimistic about how much user interaction is required to trigger exploitation.
Microsoft ranks this vulnerability as important on their proprietary severity scale. The advisory also provides a brief peek behind the curtain, since the executive summary notes that “Cwe is not in rca”. The weakness listed on the advisory is CWE-939: Improper Authorization in Handler for Custom URL Scheme.
Microsoft lifecycle update
There are no significant Microsoft product lifecycle changes this month, unless you are responsible for a Microsoft SQL Server 2012 Parallel Data Warehouse instance, which moves beyond extended support as of March 31st. It would be wise not to count on a last-minute extension, since Microsoft has already granted a six month reprieve.
Summary charts
Summary tables
Apps vulnerabilities
CVE | Title | Exploitation status | Publicly disclosed? | CVSS v3 base score |
|---|---|---|---|---|
| CVE-2026-26123 | Microsoft Authenticator Information Disclosure Vulnerability | Exploitation Less Likely | No | 5.5 |
Azure vulnerabilities
CVE | Title | Exploitation status | Publicly disclosed? | CVSS v3 base score |
|---|---|---|---|---|
| CVE-2026-26117 | Arc Enabled Servers - Azure Connected Machine Agent Elevation of Privilege Vulnerability | Exploitation Unlikely | No | 7.8 |
| CVE-2026-23664 | Azure IoT Explorer Information Disclosure Vulnerability | Exploitation Less Likely | No | 7.5 |
| CVE-2026-23661 | Azure IoT Explorer Information Disclosure Vulnerability | Exploitation Less Likely | No | 7.5 |
| CVE-2026-23662 | Azure IoT Explorer Information Disclosure Vulnerability | Exploitation Less Likely | No | 7.5 |
| CVE-2026-26121 | Azure IOT Explorer Spoofing Vulnerability | Exploitation Less Likely | No | 7.5 |
| CVE-2026-26118 | Azure MCP Server Tools Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 8.8 |
| CVE-2026-26141 | Hybrid Worker Extension (Arc‑enabled Windows VMs) Elevation of Privilege Vulnerability | Exploitation Unlikely | No | 7.8 |
| CVE-2026-23665 | Linux Azure Diagnostic extension (LAD) Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-26148 | Microsoft Azure AD SSH Login extension for Linux Elevation of Privilege Vulnerability | Exploitation Unlikely | No | 8.1 |
| CVE-2026-23660 | Windows Admin Center in Azure Portal Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
Developer Tools vulnerabilities
CVE | Title | Exploitation status | Publicly disclosed? | CVSS v3 base score |
|---|---|---|---|---|
| CVE-2026-26127 | .NET Denial of Service Vulnerability | Exploitation Unlikely | Yes | 7.5 |
| CVE-2026-26131 | .NET Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-26130 | ASP.NET Core Denial of Service Vulnerability | Exploitation Less Likely | No | 7.5 |
ESU vulnerabilities
CVE | Title | Exploitation status | Publicly disclosed? | CVSS v3 base score |
|---|---|---|---|---|
| CVE-2026-25177 | Active Directory Domain Services Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 8.8 |
| CVE-2026-23667 | Broadcast DVR Elevation of Privilege Vulnerability | Exploitation Unlikely | No | 7.0 |
| CVE-2026-25190 | GDI Remote Code Execution Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-25181 | GDI+ Information Disclosure Vulnerability | Exploitation Less Likely | No | 7.5 |
| CVE-2026-23674 | MapUrlToZone Security Feature Bypass Vulnerability | Exploitation Unlikely | No | 7.5 |
| CVE-2026-25165 | Performance Counters for Windows Elevation of Privilege Vulnerability | Exploitation Unlikely | No | 7.8 |
| CVE-2026-24282 | Push message Routing Service Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 5.5 |
| CVE-2026-24285 | Win32k Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.0 |
| CVE-2026-24291 | Windows Accessibility Infrastructure (ATBroker.exe) Elevation of Privilege Vulnerability | Exploitation More Likely | No | 7.8 |
| CVE-2026-25186 | Windows Accessibility Infrastructure (ATBroker.exe) Information Disclosure Vulnerability | Exploitation Less Likely | No | 5.5 |
| CVE-2026-24293 | Windows Ancillary Function Driver for WinSock Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-25176 | Windows Ancillary Function Driver for WinSock Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-25178 | Windows Ancillary Function Driver for WinSock Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.0 |
| CVE-2026-25179 | Windows Ancillary Function Driver for WinSock Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.0 |
| CVE-2026-25171 | Windows Authentication Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.0 |
| CVE-2026-23671 | Windows Bluetooth RFCOM Protocol Driver Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.0 |
| CVE-2026-24292 | Windows Connected Devices Platform Service Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-24295 | Windows Device Association Service Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.0 |
| CVE-2026-24296 | Windows Device Association Service Elevation of Privilege Vulnerability | Exploitation Unlikely | No | 7.0 |
| CVE-2026-25189 | Windows DWM Core Library Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-25174 | Windows Extensible File Allocation Table Elevation of Privilege Vulnerability | Exploitation Unlikely | No | 7.8 |
| CVE-2026-25168 | Windows Graphics Component Denial of Service Vulnerability | Exploitation Less Likely | No | 6.2 |
| CVE-2026-25169 | Windows Graphics Component Denial of Service Vulnerability | Exploitation Less Likely | No | 6.2 |
| CVE-2026-23668 | Windows Graphics Component Elevation of Privilege Vulnerability | Exploitation More Likely | No | 7.0 |
| CVE-2026-25180 | Windows Graphics Component Information Disclosure Vulnerability | Exploitation Less Likely | No | 5.5 |
| CVE-2026-24297 | Windows Kerberos Security Feature Bypass Vulnerability | Exploitation Less Likely | No | 6.5 |
| CVE-2026-24287 | Windows Kernel Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-24289 | Windows Kernel Elevation of Privilege Vulnerability | Exploitation More Likely | No | 7.8 |
| CVE-2026-26132 | Windows Kernel Elevation of Privilege Vulnerability | Exploitation More Likely | No | 7.8 |
| CVE-2026-24288 | Windows Mobile Broadband Driver Remote Code Execution Vulnerability | Exploitation Less Likely | No | 6.8 |
| CVE-2026-25175 | Windows NTFS Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-23669 | Windows Print Spooler Remote Code Execution Vulnerability | Exploitation Less Likely | No | 8.8 |
| CVE-2026-24290 | Windows Projected File System Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-23673 | Windows Resilient File System (ReFS) Elevation of Privilege Vulnerability | Exploitation Unlikely | No | 7.8 |
| CVE-2026-25172 | Windows Routing and Remote Access Service (RRAS) Remote Code Execution Vulnerability | Exploitation Less Likely | No | 8.8 |
| CVE-2026-25173 | Windows Routing and Remote Access Service (RRAS) Remote Code Execution Vulnerability | Exploitation Less Likely | No | 8.0 |
| CVE-2026-26111 | Windows Routing and Remote Access Service (RRAS) Remote Code Execution Vulnerability | Exploitation Less Likely | No | 8.8 |
| CVE-2026-25185 | Windows Shell Link Processing Spoofing Vulnerability | Exploitation Less Likely | No | 5.3 |
| CVE-2026-24294 | Windows SMB Server Elevation of Privilege Vulnerability | Exploitation More Likely | No | 7.8 |
| CVE-2026-26128 | Windows SMB Server Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-25166 | Windows System Image Manager Assessment and Deployment Kit (ADK) Remote Code Execution Vulnerability | Exploitation Unlikely | No | 7.8 |
| CVE-2026-25188 | Windows Telephony Service Elevation of Privilege Vulnerability | Exploitation Unlikely | No | 8.8 |
| CVE-2026-23672 | Windows Universal Disk Format File System Driver (UDFS) Elevation of Privilege Vulnerability | Exploitation Unlikely | No | 7.8 |
| CVE-2026-25187 | Winlogon Elevation of Privilege Vulnerability | Exploitation More Likely | No | 7.8 |
Microsoft Office vulnerabilities
CVE | Title | Exploitation status | Publicly disclosed? | CVSS v3 base score |
|---|---|---|---|---|
| CVE-2026-26144 | Microsoft Excel Information Disclosure Vulnerability | Exploitation Unlikely | No | 7.5 |
| CVE-2026-26112 | Microsoft Excel Remote Code Execution Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-26107 | Microsoft Excel Remote Code Execution Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-26108 | Microsoft Excel Remote Code Execution Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-26109 | Microsoft Excel Remote Code Execution Vulnerability | Exploitation Unlikely | No | 8.4 |
| CVE-2026-26134 | Microsoft Office Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-26113 | Microsoft Office Remote Code Execution Vulnerability | Exploitation Less Likely | No | 8.4 |
| CVE-2026-26110 | Microsoft Office Remote Code Execution Vulnerability | Exploitation Less Likely | No | 8.4 |
| CVE-2026-26114 | Microsoft SharePoint Server Remote Code Execution Vulnerability | Exploitation Less Likely | No | 8.8 |
| CVE-2026-26106 | Microsoft SharePoint Server Remote Code Execution Vulnerability | Exploitation Less Likely | No | 8.8 |
| CVE-2026-26105 | Microsoft SharePoint Server Spoofing Vulnerability | Exploitation Less Likely | No | 8.1 |
| CVE-2026-24285 | Win32k Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.0 |
| CVE-2026-25180 | Windows Graphics Component Information Disclosure Vulnerability | Exploitation Less Likely | No | 5.5 |
Open Source Software vulnerabilities
CVE | Title | Exploitation status | Publicly disclosed? | CVSS v3 base score |
|---|---|---|---|---|
| CVE-2026-26030 | GitHub: CVE-2026-26030 Microsoft Semantic Kernel InMemoryVectorStore filter functionality vulnerable | Exploitation Unlikely | No | 9.9 |
| CVE-2026-23654 | GitHub: Zero Shot SCFoundation Remote Code Execution Vulnerability | Exploitation Unlikely | No | 8.8 |
SQL Server vulnerabilities
CVE | Title | Exploitation status | Publicly disclosed? | CVSS v3 base score |
|---|---|---|---|---|
| CVE-2026-21262 | SQL Server Elevation of Privilege Vulnerability | Exploitation Less Likely | Yes | 8.8 |
| CVE-2026-26115 | SQL Server Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 8.8 |
| CVE-2026-26116 | SQL Server Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 8.8 |
System Center vulnerabilities
CVE | Title | Exploitation status | Publicly disclosed? | CVSS v3 base score |
|---|---|---|---|---|
| CVE-2026-20967 | System Center Operations Manager (SCOM) Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 8.8 |
Windows vulnerabilities
CVE | Title | Exploitation status | Publicly disclosed? | CVSS v3 base score |
|---|---|---|---|---|
| CVE-2026-25177 | Active Directory Domain Services Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 8.8 |
| CVE-2026-23667 | Broadcast DVR Elevation of Privilege Vulnerability | Exploitation Unlikely | No | 7.0 |
| CVE-2026-25190 | GDI Remote Code Execution Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-25181 | GDI+ Information Disclosure Vulnerability | Exploitation Less Likely | No | 7.5 |
| CVE-2026-23674 | MapUrlToZone Security Feature Bypass Vulnerability | Exploitation Unlikely | No | 7.5 |
| CVE-2026-25167 | Microsoft Brokering File System Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.4 |
| CVE-2026-24283 | Multiple UNC Provider Kernel Driver Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 8.8 |
| CVE-2026-25165 | Performance Counters for Windows Elevation of Privilege Vulnerability | Exploitation Unlikely | No | 7.8 |
| CVE-2026-24282 | Push message Routing Service Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 5.5 |
| CVE-2026-24285 | Win32k Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.0 |
| CVE-2026-24291 | Windows Accessibility Infrastructure (ATBroker.exe) Elevation of Privilege Vulnerability | Exploitation More Likely | No | 7.8 |
| CVE-2026-25186 | Windows Accessibility Infrastructure (ATBroker.exe) Information Disclosure Vulnerability | Exploitation Less Likely | No | 5.5 |
| CVE-2026-24293 | Windows Ancillary Function Driver for WinSock Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-25176 | Windows Ancillary Function Driver for WinSock Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-25178 | Windows Ancillary Function Driver for WinSock Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.0 |
| CVE-2026-25179 | Windows Ancillary Function Driver for WinSock Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.0 |
| CVE-2026-23656 | Windows App Installer Spoofing Vulnerability | Exploitation Unlikely | No | |
| CVE-2026-25171 | Windows Authentication Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.0 |
| CVE-2026-23671 | Windows Bluetooth RFCOM Protocol Driver Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.0 |
| CVE-2026-24292 | Windows Connected Devices Platform Service Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-24295 | Windows Device Association Service Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.0 |
| CVE-2026-24296 | Windows Device Association Service Elevation of Privilege Vulnerability | Exploitation Unlikely | No | 7.0 |
| CVE-2026-25189 | Windows DWM Core Library Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-25174 | Windows Extensible File Allocation Table Elevation of Privilege Vulnerability | Exploitation Unlikely | No | 7.8 |
| CVE-2026-25168 | Windows Graphics Component Denial of Service Vulnerability | Exploitation Less Likely | No | 6.2 |
| CVE-2026-25169 | Windows Graphics Component Denial of Service Vulnerability | Exploitation Less Likely | No | 6.2 |
| CVE-2026-23668 | Windows Graphics Component Elevation of Privilege Vulnerability | Exploitation More Likely | No | 7.0 |
| CVE-2026-25180 | Windows Graphics Component Information Disclosure Vulnerability | Exploitation Less Likely | No | 5.5 |
| CVE-2026-25170 | Windows Hyper-V Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.0 |
| CVE-2026-24297 | Windows Kerberos Security Feature Bypass Vulnerability | Exploitation Less Likely | No | 6.5 |
| CVE-2026-24287 | Windows Kernel Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-24289 | Windows Kernel Elevation of Privilege Vulnerability | Exploitation More Likely | No | 7.8 |
| CVE-2026-26132 | Windows Kernel Elevation of Privilege Vulnerability | Exploitation More Likely | No | 7.8 |
| CVE-2026-24288 | Windows Mobile Broadband Driver Remote Code Execution Vulnerability | Exploitation Less Likely | No | 6.8 |
| CVE-2026-25175 | Windows NTFS Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-23669 | Windows Print Spooler Remote Code Execution Vulnerability | Exploitation Less Likely | No | 8.8 |
| CVE-2026-24290 | Windows Projected File System Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-23673 | Windows Resilient File System (ReFS) Elevation of Privilege Vulnerability | Exploitation Unlikely | No | 7.8 |
| CVE-2026-25172 | Windows Routing and Remote Access Service (RRAS) Remote Code Execution Vulnerability | Exploitation Less Likely | No | 8.8 |
| CVE-2026-25173 | Windows Routing and Remote Access Service (RRAS) Remote Code Execution Vulnerability | Exploitation Less Likely | No | 8.0 |
| CVE-2026-26111 | Windows Routing and Remote Access Service (RRAS) Remote Code Execution Vulnerability | Exploitation Less Likely | No | 8.8 |
| CVE-2026-25185 | Windows Shell Link Processing Spoofing Vulnerability | Exploitation Less Likely | No | 5.3 |
| CVE-2026-24294 | Windows SMB Server Elevation of Privilege Vulnerability | Exploitation More Likely | No | 7.8 |
| CVE-2026-26128 | Windows SMB Server Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-25166 | Windows System Image Manager Assessment and Deployment Kit (ADK) Remote Code Execution Vulnerability | Exploitation Unlikely | No | 7.8 |
| CVE-2026-25188 | Windows Telephony Service Elevation of Privilege Vulnerability | Exploitation Unlikely | No | 8.8 |
| CVE-2026-23672 | Windows Universal Disk Format File System Driver (UDFS) Elevation of Privilege Vulnerability | Exploitation Unlikely | No | 7.8 |
| CVE-2026-25187 | Winlogon Elevation of Privilege Vulnerability | Exploitation More Likely | No | 7.8 |
Zero-Day Vulnerabilities: Publicly Disclosed (No known exploitation)
CVE | Title | Exploitation status | Publicly disclosed? | CVSS v3 base score |
|---|---|---|---|---|
| CVE-2026-26127 | .NET Denial of Service Vulnerability | Exploitation Unlikely | Yes | 7.5 |
| CVE-2026-21262 | SQL Server Elevation of Privilege Vulnerability | Exploitation Less Likely | Yes | 8.8 |
Update history
- 2026-03-16: updated section on CVE-2026-26123 to include researcher commentary.