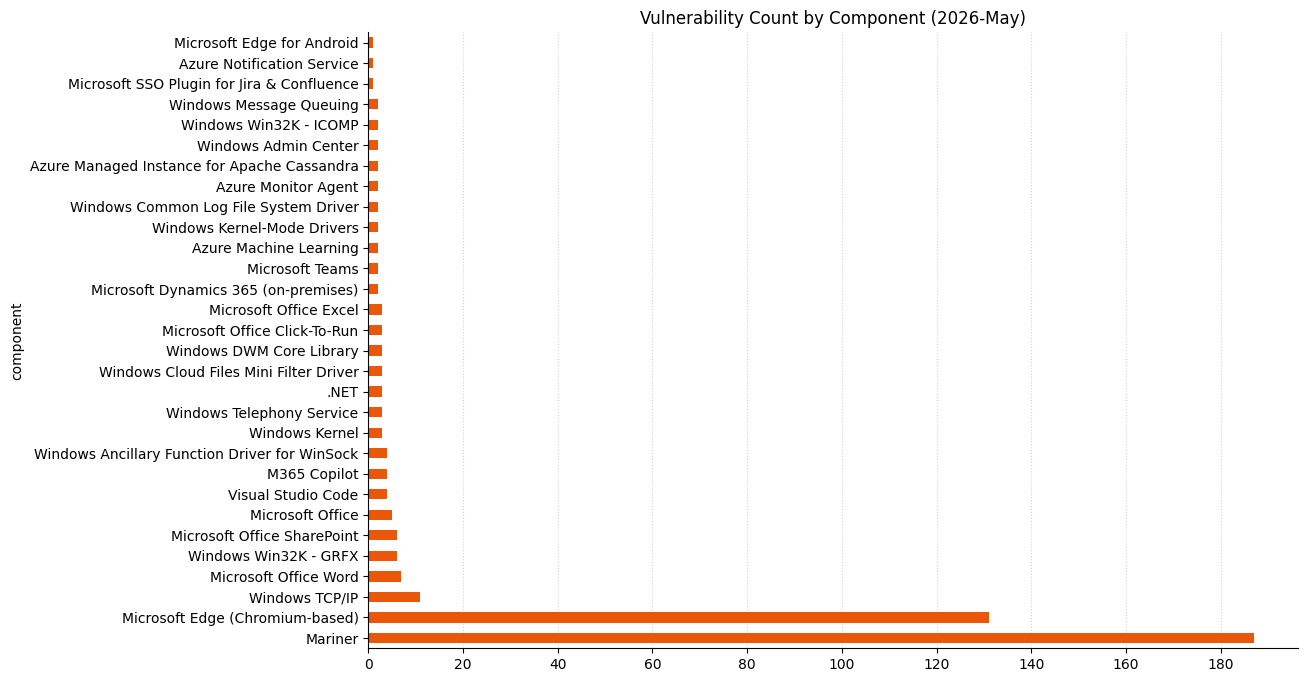
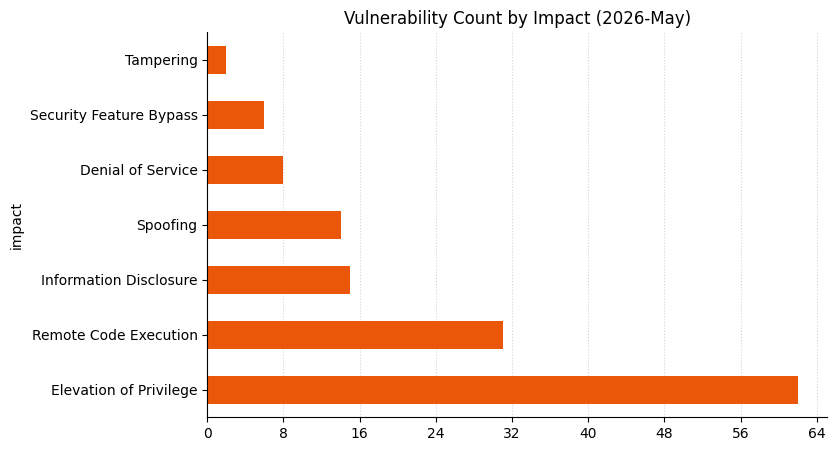
Microsoft is publishing 137 vulnerabilities on May 2026 Patch Tuesday. Microsoft is not aware of exploitation in the wild or public disclosure for any of these vulnerabilities. So far this month, Microsoft has provided patches to address 133 browser vulnerabilities, which are not included in the Patch Tuesday count above.
Windows Netlogon: critical RCE
Anyone responsible for securing a domain controller should prioritize remediation of CVE-2026-41089, which is a critical stack-based buffer overflow in Windows Netlogon with a CVSS v3 base score of 9.8. Exploitation leads to execution in the context of the Netlogon service, so that’s SYSTEM privileges on the domain controller. For most pentesters, that’s the point at which the customer report more or less writes itself. No privileges or user interaction are required, and attack complexity is low, which suggests that creation of a reliable exploit might not be especially difficult for anyone with knowledge of the specific mechanism.
Microsoft assesses exploitation as less likely, but since those exploitability assessments are provided without an accompanying explanation, it’s not clear how much reassurance defenders should take. Anyone who remembers the much-discussed CVE-2020-1472 (aka ZeroLogon) back in 2020 will note that CVE-2026-41089 offers an attacker more immediate control of a domain controller. Patches are available for all versions of Windows Server from 2012 onwards.
Windows DNS Client: critical RCE
An attacker looking for a master key for Windows assets will pay attention to CVE-2026-41096, a critical RCE in the Windows DNS client implementation. A modern computer talks to DNS the way a child in the back of a car asks “are we there yet?” The variable and complex structure of DNS responses means that DNS client implementations are also complex and thus prone to flaws. Microsoft assesses exploitation as less likely, and we can hope that modern mitigations such as heap address randomization and optional-but-recommended encrypted channel DNS will make weaponization significantly more challenging by putting barriers across specific paths to exploitation. The DNS client on Windows runs as the NetworkService role, rather than SYSTEM, but a foothold is a foothold, and skilled attackers expect to chain exploits together.
JIRA/Confluence Entra ID auth plugin: critical EoP
If you’re still self-hosting Atlassian JIRA or Confluence and relying on the Microsoft Entra ID authentication plugin, you’ll want to know about CVE-2026-41103. This critical elevation of privilege vulnerability allows an unauthorized attacker to impersonate an existing user by presenting forged credentials, thus bypassing Entra ID. Microsoft expects that exploitation is more likely. Even if you can’t always find what you want on the corporate Confluence, a motivated attacker probably will. Curiously, the patch links on the advisory lead to older versions of the plugins published in 2024.
Microsoft WARP team
Microsoft’s WARP team is credited with multiple critical vulnerabilities today, after making their first appearance in MSRC advisory acknowledgements in last month’s Patch Tuesday. We can speculate that they likely know a great deal about the current state of AI-powered vulnerability research as it applies to Microsoft products.
Microsoft lifecycle update
There are no significant Microsoft product lifecycle changes this month. Microsoft .NET 9 STS (Standard Term Support, as distinct from Long Term Support) was originally scheduled to move past the end of support in May 2026, but late last year, Microsoft granted a six-month extension, so that .NET 9 STS now reaches end of support on November 10, 2026.
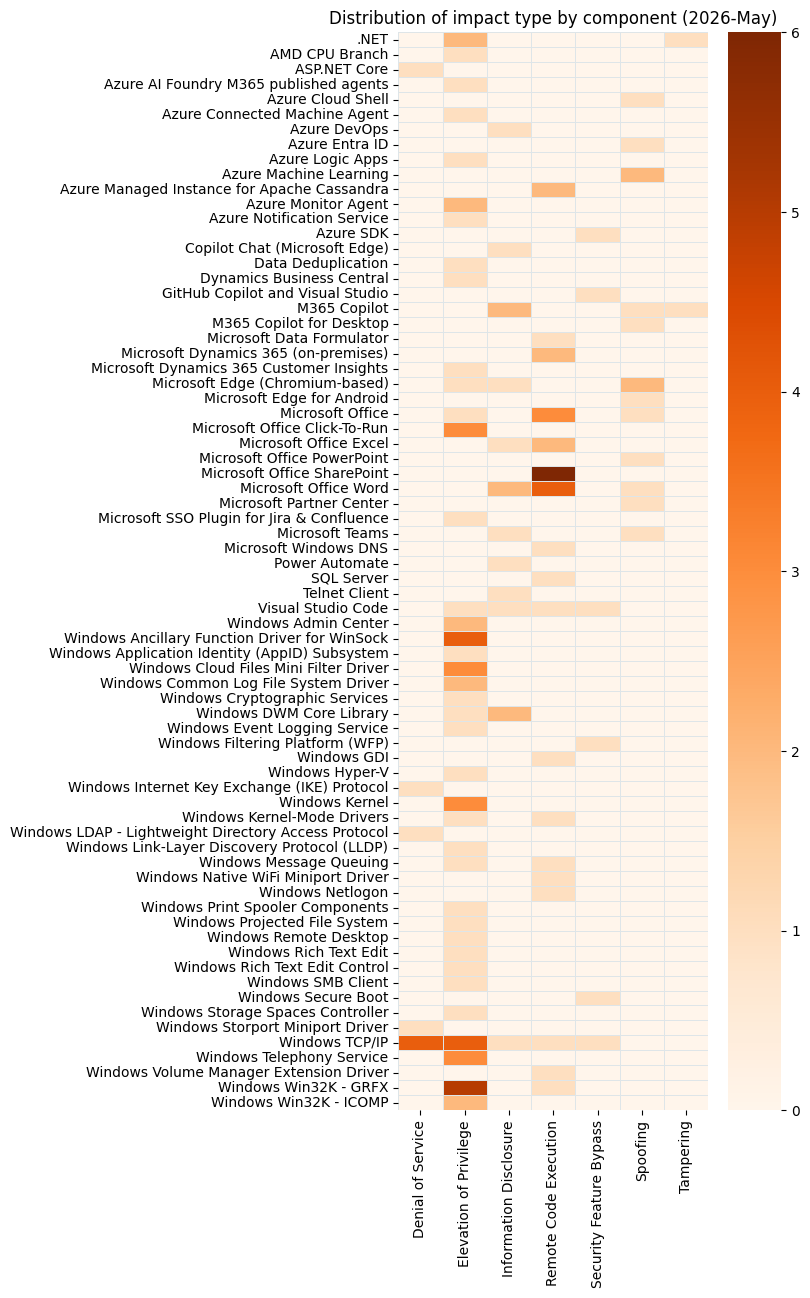
Summary charts
Summary tables
Apps vulnerabilities
CVE | Title | Exploitation status | Publicly disclosed? | CVSS v3 base score |
|---|---|---|---|---|
| CVE-2026-26129 | M365 Copilot Information Disclosure Vulnerability | N/A | No | 7.5 |
| CVE-2026-26164 | M365 Copilot Information Disclosure Vulnerability | Exploitation Less Likely | No | 7.5 |
| CVE-2026-41614 | M365 Copilot for Desktop Spoofing Vulnerability | Exploitation Less Likely | No | 6.2 |
| CVE-2026-41100 | Microsoft 365 Copilot for Android Spoofing Vulnerability | Exploitation Unlikely | No | 4.4 |
| CVE-2026-42832 | Microsoft Office Spoofing Vulnerability | Exploitation Unlikely | No | 7.7 |
| CVE-2026-41101 | Microsoft Word for Android Spoofing Vulnerability | Exploitation Unlikely | No | 7.1 |
Azure vulnerabilities
CVE | Title | Exploitation status | Publicly disclosed? | CVSS v3 base score |
|---|---|---|---|---|
| CVE-2026-35435 | Azure AI Foundry Elevation of Privilege Vulnerability | Exploitation More Likely | No | 8.6 |
| CVE-2026-35428 | Azure Cloud Shell Spoofing Vulnerability | N/A | No | 9.6 |
| CVE-2026-32207 | Azure Machine Learning Notebook Spoofing Vulnerability | n/a | No | 8.8 |
| CVE-2026-33109 | Azure Managed Instance for Apache Cassandra Remote Code Execution Vulnerability | N/A | No | 9.9 |
| CVE-2026-33844 | Azure Managed Instance for Apache Cassandra Remote Code Execution Vulnerability | N/A | No | 9.0 |
| CVE-2026-41105 | Azure Monitor Action Group Notification System Elevation of Privilege Vulnerability | N/A | No | 8.1 |
| CVE-2026-40379 | Microsoft Enterprise Security Token Service (ESTS) Spoofing Vulnerability | N/A | No | 9.3 |
| CVE-2026-34327 | Microsoft Partner Center Spoofing Vulnerability | N/A | No | 8.2 |
| CVE-2026-40381 | Azure Connected Machine Agent Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-42823 | Azure Logic Apps Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 9.9 |
| CVE-2026-33833 | Azure Machine Learning Notebook Spoofing Vulnerability | Exploitation Less Likely | No | 8.2 |
| CVE-2026-32204 | Azure Monitor Agent Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-42830 | Azure Monitor Agent Metrics Extension Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 6.5 |
| CVE-2026-33117 | Azure SDK for Java Security Feature Bypass Vulnerability | Exploitation Unlikely | No | 9.1 |
| CVE-2026-41103 | Microsoft SSO Plugin for Jira & Confluence Elevation of Privilege Vulnerability | Exploitation More Likely | No | 9.1 |
| CVE-2026-41086 | Windows Admin Center in Azure Portal Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 8.8 |
Browser vulnerabilities
CVE | Title | Exploitation status | Publicly disclosed? | CVSS v3 base score |
|---|---|---|---|---|
| CVE-2026-7898 | Chromium: CVE-2026-7898 Use after free in Chromoting | n/a | No | |
| CVE-2026-7899 | Chromium: CVE-2026-7899 Out of bounds read and write in V8 | n/a | No | |
| CVE-2026-7900 | Chromium: CVE-2026-7900 Heap buffer overflow in ANGLE | n/a | No | |
| CVE-2026-7901 | Chromium: CVE-2026-7901 Use after free in ANGLE | n/a | No | |
| CVE-2026-7902 | Chromium: CVE-2026-7902 Out of bounds memory access in V8 | n/a | No | |
| CVE-2026-7903 | Chromium: CVE-2026-7903 Integer overflow in ANGLE | n/a | No | |
| CVE-2026-7904 | Chromium: CVE-2026-7904 Out of bounds read in Fonts | n/a | No | |
| CVE-2026-7906 | Chromium: CVE-2026-7906 Use after free in SVG | n/a | No | |
| CVE-2026-7907 | Chromium: CVE-2026-7907 Use after free in DOM | n/a | No | |
| CVE-2026-7908 | Chromium: CVE-2026-7908 Use after free in Fullscreen | n/a | No | |
| CVE-2026-7909 | Chromium: CVE-2026-7909 Inappropriate implementation in ServiceWorker | n/a | No | |
| CVE-2026-7910 | Chromium: CVE-2026-7910 Use after free in Views | n/a | No | |
| CVE-2026-7911 | Chromium: CVE-2026-7911 Use after free in Aura | n/a | No | |
| CVE-2026-7914 | Chromium: CVE-2026-7914 Type Confusion in Accessibility | n/a | No | |
| CVE-2026-7916 | Chromium: CVE-2026-7916 Insufficient data validation in InterestGroups | n/a | No | |
| CVE-2026-7917 | Chromium: CVE-2026-7917 Use after free in Fullscreen | n/a | No | |
| CVE-2026-7918 | Chromium: CVE-2026-7918 Use after free in GPU | n/a | No | |
| CVE-2026-7919 | Chromium: CVE-2026-7919 Use after free in Aura | n/a | No | |
| CVE-2026-7920 | Chromium: CVE-2026-7920 Use after free in Skia | n/a | No | |
| CVE-2026-7921 | Chromium: CVE-2026-7921 Use after free in Passwords | n/a | No | |
| CVE-2026-7922 | Chromium: CVE-2026-7922 Use after free in ServiceWorker | n/a | No | |
| CVE-2026-7923 | Chromium: CVE-2026-7923 Out of bounds write in Skia | n/a | No | |
| CVE-2026-7924 | Chromium: CVE-2026-7924 Uninitialized Use in Dawn | n/a | No | |
| CVE-2026-7925 | Chromium: CVE-2026-7925 Use after free in Chromoting | n/a | No | |
| CVE-2026-7926 | Chromium: CVE-2026-7926 Use after free in PresentationAPI | n/a | No | |
| CVE-2026-7927 | Chromium: CVE-2026-7927 Type Confusion in Runtime | n/a | No | |
| CVE-2026-7928 | Chromium: CVE-2026-7928 Use after free in WebRTC | n/a | No | |
| CVE-2026-7929 | Chromium: CVE-2026-7929 Use after free in MediaRecording | n/a | No | |
| CVE-2026-7930 | Chromium: CVE-2026-7930 Insufficient validation of untrusted input in Cookies | n/a | No | |
| CVE-2026-7932 | Chromium: CVE-2026-7932 Insufficient policy enforcement in Downloads | n/a | No | |
| CVE-2026-7933 | Chromium: CVE-2026-7933 Out of bounds read in WebCodecs | n/a | No | |
| CVE-2026-7934 | Chromium: CVE-2026-7934 Insufficient validation of untrusted input in Popup Blocker | n/a | No | |
| CVE-2026-7935 | Chromium: CVE-2026-7935 Inappropriate implementation in Speech | n/a | No | |
| CVE-2026-7936 | Chromium: CVE-2026-7936 Object lifecycle issue in V8 | n/a | No | |
| CVE-2026-7937 | Chromium: CVE-2026-7937 Insufficient policy enforcement in DevTools | n/a | No | |
| CVE-2026-7938 | Chromium: CVE-2026-7938 Use after free in CSS | n/a | No | |
| CVE-2026-7939 | Chromium: CVE-2026-7939 Inappropriate implementation in SanitizerAPI | n/a | No | |
| CVE-2026-7940 | Chromium: CVE-2026-7940 Use after free in V8 | n/a | No | |
| CVE-2026-7942 | Chromium: CVE-2026-7942 Integer overflow in ANGLE | n/a | No | |
| CVE-2026-7943 | Chromium: CVE-2026-7943 Insufficient validation of untrusted input in ANGLE | n/a | No | |
| CVE-2026-7944 | Chromium: CVE-2026-7944 Insufficient validation of untrusted input in Persistent Cache | n/a | No | |
| CVE-2026-7945 | Chromium: CVE-2026-7945 Insufficient validation of untrusted input in COOP | n/a | No | |
| CVE-2026-7946 | Chromium: CVE-2026-7946 Insufficient policy enforcement in WebUI | n/a | No | |
| CVE-2026-7947 | Chromium: CVE-2026-7947 Insufficient validation of untrusted input in Network | n/a | No | |
| CVE-2026-7948 | Chromium: CVE-2026-7948 Race in Chromoting | n/a | No | |
| CVE-2026-7949 | Chromium: CVE-2026-7949 Out of bounds read in Skia | n/a | No | |
| CVE-2026-7950 | Chromium: CVE-2026-7950 Out of bounds read and write in GFX | n/a | No | |
| CVE-2026-7951 | Chromium: CVE-2026-7951 Out of bounds write in WebRTC | n/a | No | |
| CVE-2026-7952 | Chromium: CVE-2026-7952 Insufficient policy enforcement in Extensions | n/a | No | |
| CVE-2026-7953 | Chromium: CVE-2026-7953 Insufficient validation of untrusted input in Omnibox | n/a | No | |
| CVE-2026-7954 | Chromium: CVE-2026-7954 Race in Shared Storage | n/a | No | |
| CVE-2026-7955 | Chromium: CVE-2026-7955 Uninitialized Use in GPU | n/a | No | |
| CVE-2026-7956 | Chromium: CVE-2026-7956 Use after free in Navigation | n/a | No | |
| CVE-2026-7957 | Chromium: CVE-2026-7957 Out of bounds write in Media | n/a | No | |
| CVE-2026-7958 | Chromium: CVE-2026-7958 Inappropriate implementation in ServiceWorker | n/a | No | |
| CVE-2026-7959 | Chromium: CVE-2026-7959 Inappropriate implementation in Navigation | n/a | No | |
| CVE-2026-7960 | Chromium: CVE-2026-7960 Race in Speech | n/a | No | |
| CVE-2026-7961 | Chromium: CVE-2026-7961 Insufficient validation of untrusted input in Permissions | n/a | No | |
| CVE-2026-7962 | Chromium: CVE-2026-7962 Insufficient policy enforcement in DirectSockets | n/a | No | |
| CVE-2026-7963 | Chromium: CVE-2026-7963 Inappropriate implementation in ServiceWorker | n/a | No | |
| CVE-2026-7964 | Chromium: CVE-2026-7964 Insufficient validation of untrusted input in FileSystem | n/a | No | |
| CVE-2026-7965 | Chromium: CVE-2026-7965 Insufficient validation of untrusted input in DevTools | n/a | No | |
| CVE-2026-7966 | Chromium: CVE-2026-7966 Insufficient validation of untrusted input in SiteIsolation | n/a | No | |
| CVE-2026-7967 | Chromium: CVE-2026-7967 Insufficient validation of untrusted input in Navigation | n/a | No | |
| CVE-2026-7968 | Chromium: CVE-2026-7968 Insufficient validation of untrusted input in CORS | n/a | No | |
| CVE-2026-7969 | Chromium: CVE-2026-7969 Integer overflow in Network | n/a | No | |
| CVE-2026-7970 | Chromium: CVE-2026-7970 Use after free in TopChrome | n/a | No | |
| CVE-2026-7971 | Chromium: CVE-2026-7971 Inappropriate implementation in ORB | n/a | No | |
| CVE-2026-7972 | Chromium: CVE-2026-7972 Uninitialized Use in GPU | n/a | No | |
| CVE-2026-7973 | Chromium: CVE-2026-7973 Integer overflow in Dawn | n/a | No | |
| CVE-2026-7974 | Chromium: CVE-2026-7974 Use after free in Blink | n/a | No | |
| CVE-2026-7975 | Chromium: CVE-2026-7975 Use after free in DevTools | n/a | No | |
| CVE-2026-7976 | Chromium: CVE-2026-7976 Use after free in Views | n/a | No | |
| CVE-2026-7977 | Chromium: CVE-2026-7977 Inappropriate implementation in Canvas | n/a | No | |
| CVE-2026-7978 | Chromium: CVE-2026-7978 Inappropriate implementation in Companion | n/a | No | |
| CVE-2026-7979 | Chromium: CVE-2026-7979 Inappropriate implementation in Media | n/a | No | |
| CVE-2026-7980 | Chromium: CVE-2026-7980 Use after free in WebAudio | n/a | No | |
| CVE-2026-7981 | Chromium: CVE-2026-7981 Out of bounds read in Codecs | n/a | No | |
| CVE-2026-7982 | Chromium: CVE-2026-7982 Uninitialized Use in WebCodecs | n/a | No | |
| CVE-2026-7983 | Chromium: CVE-2026-7983 Out of bounds read in Dawn | n/a | No | |
| CVE-2026-7984 | Chromium: CVE-2026-7984 Use after free in ReadingMode | n/a | No | |
| CVE-2026-7985 | Chromium: CVE-2026-7985 Use after free in GPU | n/a | No | |
| CVE-2026-7986 | Chromium: CVE-2026-7986 Insufficient policy enforcement in Autofill | n/a | No | |
| CVE-2026-7987 | Chromium: CVE-2026-7987 Use after free in WebRTC | n/a | No | |
| CVE-2026-7988 | Chromium: CVE-2026-7988 Type Confusion in WebRTC | n/a | No | |
| CVE-2026-7989 | Chromium: CVE-2026-7989 Insufficient data validation in DataTransfer | n/a | No | |
| CVE-2026-7990 | Chromium: CVE-2026-7990 Insufficient validation of untrusted input in Updater | n/a | No | |
| CVE-2026-7991 | Chromium: CVE-2026-7991 Use after free in UI | n/a | No | |
| CVE-2026-7992 | Chromium: CVE-2026-7992 Insufficient validation of untrusted input in UI | n/a | No | |
| CVE-2026-7994 | Chromium: CVE-2026-7994 Inappropriate implementation in Chromoting | n/a | No | |
| CVE-2026-7995 | Chromium: CVE-2026-7995 Out of bounds read in AdFilter | n/a | No | |
| CVE-2026-7996 | Chromium: CVE-2026-7996 Insufficient validation of untrusted input in SSL | n/a | No | |
| CVE-2026-7997 | Chromium: CVE-2026-7997 Insufficient validation of untrusted input in Updater | n/a | No | |
| CVE-2026-7998 | Chromium: CVE-2026-7998 Insufficient validation of untrusted input in Dialog | n/a | No | |
| CVE-2026-7999 | Chromium: CVE-2026-7999 Inappropriate implementation in V8 | n/a | No | |
| CVE-2026-8000 | Chromium: CVE-2026-8000 Insufficient validation of untrusted input in ChromeDriver | n/a | No | |
| CVE-2026-8001 | Chromium: CVE-2026-8001 Use after free in Printing | n/a | No | |
| CVE-2026-8002 | Chromium: CVE-2026-8002 Use after free in Audio | n/a | No | |
| CVE-2026-8003 | Chromium: CVE-2026-8003 Insufficient validation of untrusted input in TabGroups | n/a | No | |
| CVE-2026-8004 | Chromium: CVE-2026-8004 Insufficient policy enforcement in DevTools | n/a | No | |
| CVE-2026-8005 | Chromium: CVE-2026-8005 Insufficient validation of untrusted input in Cast | n/a | No | |
| CVE-2026-8006 | Chromium: CVE-2026-8006 Insufficient policy enforcement in DevTools | n/a | No | |
| CVE-2026-8007 | Chromium: CVE-2026-8007 Insufficient validation of untrusted input in Cast | n/a | No | |
| CVE-2026-8008 | Chromium: CVE-2026-8008 Inappropriate implementation in DevTools | n/a | No | |
| CVE-2026-8009 | Chromium: CVE-2026-8009 Inappropriate implementation in Cast | n/a | No | |
| CVE-2026-8010 | Chromium: CVE-2026-8010 Insufficient validation of untrusted input in SiteIsolation | n/a | No | |
| CVE-2026-8011 | Chromium: CVE-2026-8011 Insufficient policy enforcement in Search | n/a | No | |
| CVE-2026-8012 | Chromium: CVE-2026-8012 Inappropriate implementation in MHTML | n/a | No | |
| CVE-2026-8013 | Chromium: CVE-2026-8013 Insufficient validation of untrusted input in FedCM | n/a | No | |
| CVE-2026-8014 | Chromium: CVE-2026-8014 Inappropriate implementation in Preload | n/a | No | |
| CVE-2026-8015 | Chromium: CVE-2026-8015 Inappropriate implementation in Media | n/a | No | |
| CVE-2026-8016 | Chromium: CVE-2026-8016 Use after free in WebRTC | n/a | No | |
| CVE-2026-8017 | Chromium: CVE-2026-8017 Side-channel information leakage in Media | n/a | No | |
| CVE-2026-8018 | Chromium: CVE-2026-8018 Insufficient policy enforcement in DevTools | n/a | No | |
| CVE-2026-8019 | Chromium: CVE-2026-8019 Insufficient policy enforcement in WebApp | n/a | No | |
| CVE-2026-8021 | Chromium: CVE-2026-8021 Script injection in UI | n/a | No | |
| CVE-2026-8022 | Chromium: CVE-2026-8022 Inappropriate implementation in MHTML | n/a | No | |
| CVE-2026-33111 | Copilot Chat (Microsoft Edge) Information Disclosure Vulnerability | Exploitation Less Likely | No | 7.5 |
| CVE-2026-7896 | Chromium: CVE-2026-7896 Integer overflow in Blink | n/a | No | |
| CVE-2026-7897 | Chromium: CVE-2026-7897 Use after free in Mobile | n/a | No | |
| CVE-2026-7905 | Chromium: CVE-2026-7905 Insufficient validation of untrusted input in Media | n/a | No | |
| CVE-2026-7912 | Chromium: CVE-2026-7912 Integer overflow in GPU | n/a | No | |
| CVE-2026-7913 | Chromium: CVE-2026-7913 Insufficient policy enforcement in DevTools | n/a | No | |
| CVE-2026-7915 | Chromium: CVE-2026-7915 Insufficient data validation in DevTools | n/a | No | |
| CVE-2026-7931 | Chromium: CVE-2026-7931 Insufficient validation of untrusted input in iOS | n/a | No | |
| CVE-2026-7941 | Chromium: CVE-2026-7941 Insufficient validation of untrusted input in Mobile | n/a | No | |
| CVE-2026-7993 | Chromium: CVE-2026-7993 Insufficient validation of untrusted input in Payments | n/a | No | |
| CVE-2026-8020 | Chromium: CVE-2026-8020 Uninitialized Use in GPU | n/a | No | |
| CVE-2026-42838 | Microsoft Edge (Chromium-based) Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 5.4 |
| CVE-2026-42891 | Microsoft Edge (Chromium-based) for Android Spoofing Vulnerability | Exploitation Unlikely | No | 6.5 |
| CVE-2026-35429 | Microsoft Edge (Chromium-based) for Android Spoofing Vulnerability | Exploitation Unlikely | No | 4.3 |
| CVE-2026-40416 | Microsoft Edge (Chromium-based) for Android Spoofing Vulnerability | Exploitation Unlikely | No | 4.3 |
| CVE-2026-41107 | Microsoft Edge (Chromium-based) Information Disclosure Vulnerability | Exploitation Less Likely | No | 7.4 |
Developer Tools vulnerabilities
CVE | Title | Exploitation status | Publicly disclosed? | CVSS v3 base score |
|---|---|---|---|---|
| CVE-2026-42826 | Azure DevOps Information Disclosure Vulnerability | N/A | No | 10.0 |
| CVE-2026-32175 | .NET Core Tampering Vulnerability | Exploitation Less Likely | No | 4.3 |
| CVE-2026-32177 | .NET Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.3 |
| CVE-2026-35433 | .NET Elevation of Privilege Vulnerability | Exploitation Unlikely | No | 7.3 |
| CVE-2026-42899 | ASP.NET Core Denial of Service Vulnerability | Exploitation Unlikely | No | 7.5 |
| CVE-2026-41109 | GitHub Copilot and Visual Studio Code Security Feature Bypass Vulnerability | Exploitation Less Likely | No | 8.8 |
| CVE-2026-41094 | Microsoft Data Formulator Remote Code Execution Vulnerability | Exploitation Less Likely | No | 8.8 |
| CVE-2026-41613 | Visual Studio Code Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 8.8 |
| CVE-2026-41612 | Visual Studio Code Information Disclosure Vulnerability | Exploitation Less Likely | No | 5.5 |
| CVE-2026-41611 | Visual Studio Code Remote Code Execution Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-41610 | Visual Studio Code Security Feature Bypass Vulnerability | Exploitation Less Likely | No | 6.3 |
ESU vulnerabilities
CVE | Title | Exploitation status | Publicly disclosed? | CVSS v3 base score |
|---|---|---|---|---|
| CVE-2025-54518 | AMD: CVE-2025-54518 CPU OP Cache Corruption | Exploitation Unlikely | No | |
| CVE-2026-41095 | Data Deduplication Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-35424 | Internet Key Exchange (IKE) Protocol Denial of Service Vulnerability | Exploitation Unlikely | No | 7.5 |
| CVE-2026-40377 | Microsoft Cryptographic Services Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-34329 | Microsoft Message Queuing (MSMQ) Remote Code Execution Vulnerability | Exploitation Less Likely | No | 8.8 |
| CVE-2026-41097 | Secure Boot Security Feature Bypass Vulnerability | Exploitation Less Likely | No | 6.7 |
| CVE-2026-33839 | Win32k Elevation of Privilege Vulnerability | Exploitation Unlikely | No | 7.0 |
| CVE-2026-34330 | Win32k Elevation of Privilege Vulnerability | Exploitation Unlikely | No | 7.8 |
| CVE-2026-34331 | Win32k Elevation of Privilege Vulnerability | Exploitation Unlikely | No | 7.0 |
| CVE-2026-35423 | Windows 11 Telnet Client Information Disclosure Vulnerability | Exploitation Unlikely | No | 5.4 |
| CVE-2026-34344 | Windows Ancillary Function Driver for WinSock Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-34345 | Windows Ancillary Function Driver for WinSock Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.0 |
| CVE-2026-35416 | Windows Ancillary Function Driver for WinSock Elevation of Privilege Vulnerability | Exploitation More Likely | No | 7.0 |
| CVE-2026-41088 | Windows Ancillary Function Driver for WinSock Elevation of Privilege Vulnerability | Exploitation Unlikely | No | 7.8 |
| CVE-2026-34343 | Windows Application Identity (AppID) Subsystem Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-35418 | Windows Cloud Files Mini Filter Driver Elevation of Privilege Vulnerability | Exploitation Unlikely | No | 7.8 |
| CVE-2026-33835 | Windows Cloud Files Mini Filter Driver Elevation of Privilege Vulnerability | Exploitation More Likely | No | 7.8 |
| CVE-2026-34337 | Windows Cloud Files Mini Filter Driver Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-40407 | Windows Common Log File System Driver Elevation of Privilege Vulnerability | Exploitation Unlikely | No | 7.8 |
| CVE-2026-40397 | Windows Common Log File System Driver Elevation of Privilege Vulnerability | Exploitation More Likely | No | 7.8 |
| CVE-2026-34336 | Windows DWM Core Library Information Disclosure Vulnerability | Exploitation Unlikely | No | 7.8 |
| CVE-2026-33834 | Windows Event Logging Service Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-32209 | Windows Filtering Platform (WFP) Security Feature Bypass Vulnerability | Exploitation Unlikely | No | 4.4 |
| CVE-2026-35421 | Windows GDI Remote Code Execution Vulnerability | Exploitation Unlikely | No | 7.8 |
| CVE-2026-40403 | Windows Graphics Component Remote Code Execution Vulnerability | Exploitation Less Likely | No | 8.8 |
| CVE-2026-33841 | Windows Kernel Elevation of Privilege Vulnerability | Exploitation More Likely | No | 7.8 |
| CVE-2026-35420 | Windows Kernel Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-34339 | Windows Lightweight Directory Access Protocol (LDAP) Denial of Service Vulnerability | Exploitation Less Likely | No | 5.5 |
| CVE-2026-34341 | Windows Link-Layer Discovery Protocol (LLDP) Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.0 |
| CVE-2026-33838 | Windows Message Queuing (MSMQ) Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-32161 | Windows Native WiFi Miniport Driver Remote Code Execution Vulnerability | Exploitation Less Likely | No | 7.5 |
| CVE-2026-41089 | Windows Netlogon Remote Code Execution Vulnerability | Exploitation Less Likely | No | 9.8 |
| CVE-2026-34342 | Windows Print Spooler Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.0 |
| CVE-2026-34340 | Windows Projected File System Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.0 |
| CVE-2026-40398 | Windows Remote Desktop Services Elevation of Privilege Vulnerability | Exploitation More Likely | No | 7.8 |
| CVE-2026-21530 | Windows Rich Text Edit Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 6.7 |
| CVE-2026-32170 | Windows Rich Text Edit Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 6.7 |
| CVE-2026-40410 | Windows SMB Client Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.0 |
| CVE-2026-35415 | Windows Storage Spaces Controller Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-40414 | Windows TCP/IP Denial of Service Vulnerability | Exploitation Unlikely | No | 7.4 |
| CVE-2026-40401 | Windows TCP/IP Denial of Service Vulnerability | Exploitation Unlikely | No | 7.1 |
| CVE-2026-40413 | Windows TCP/IP Denial of Service Vulnerability | Exploitation Less Likely | No | 7.4 |
| CVE-2026-35422 | Windows TCP/IP Driver Security Feature Bypass Vulnerability | Exploitation Unlikely | No | 6.5 |
| CVE-2026-34351 | Windows TCP/IP Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-40399 | Windows TCP/IP Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-34334 | Windows TCP/IP Elevation of Privilege Vulnerability | Exploitation Unlikely | No | 7.8 |
| CVE-2026-40406 | Windows TCP/IP Information Disclosure Vulnerability | Exploitation Less Likely | No | 7.5 |
| CVE-2026-33837 | Windows TCP/IP Local Elevation of Privilege Vulnerability | Exploitation More Likely | No | 7.8 |
| CVE-2026-40415 | Windows TCP/IP Remote Code Execution Vulnerability | Exploitation Unlikely | No | 8.1 |
| CVE-2026-42825 | Windows Telephony Service Elevation of Privilege Vulnerability | Exploitation Unlikely | No | 7.0 |
| CVE-2026-34338 | Windows Telephony Service Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-40382 | Windows Telephony Service Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-40380 | Windows Volume Manager Extension Driver Remote Code Execution Vulnerability | Exploitation Less Likely | No | 6.2 |
| CVE-2026-40408 | Windows WAN ARP Driver Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-34333 | Windows Win32k Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-34347 | Windows Win32k Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.0 |
| CVE-2026-35417 | Windows Win32k Elevation of Privilege Vulnerability | Exploitation More Likely | No | 7.8 |
Mariner vulnerabilities
CVE | Title | Exploitation status | Publicly disclosed? | CVSS v3 base score |
|---|---|---|---|---|
| CVE-2026-7598 | libssh2 userauth.c userauth_password integer overflow | n/a | No | 7.3 |
| CVE-2026-43870 | Apache Thrift: Node.js web_server.js multi-vulnerability | n/a | No | 7.3 |
| CVE-2026-43868 | Apache Thrift: Rust implementation vulnerable to CVE-2020-13949 pattern | n/a | No | 5.3 |
| CVE-2026-43869 | Apache Thrift: TSSLTransportFactory.java hostname verification | n/a | No | 7.3 |
Microsoft Dynamics vulnerabilities
CVE | Title | Exploitation status | Publicly disclosed? | CVSS v3 base score |
|---|---|---|---|---|
| CVE-2026-33821 | Microsoft Dynamics 365 Customer Insights Elevation of Privilege Vulnerability | N/A | No | 7.7 |
| CVE-2026-40417 | Microsoft Dynamics 365 Business Central Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-42898 | Microsoft Dynamics 365 On-Premises Remote Code Execution Vulnerability | Exploitation Unlikely | No | 9.9 |
| CVE-2026-42833 | Microsoft Dynamics 365 On-Premises Remote Code Execution Vulnerability | Exploitation Less Likely | No | 9.1 |
| CVE-2026-40374 | Microsoft Power Automate Desktop Information Disclosure Vulnerability | Exploitation Less Likely | No | 6.5 |
Open Source Software vulnerabilities
CVE | Title | Exploitation status | Publicly disclosed? | CVSS v3 base score |
|---|---|---|---|---|
| CVE-2026-31706 | ksmbd: validate num_aces and harden ACE walk in smb_inherit_dacl() | n/a | No | 8.8 |
| CVE-2026-31723 | usb: gadget: f_subset: Fix net_device lifecycle with device_move | n/a | No | 7.8 |
| CVE-2026-31724 | usb: gadget: f_eem: Fix net_device lifecycle with device_move | n/a | No | 7.8 |
| CVE-2026-43053 | xfs: close crash window in attr dabtree inactivation | n/a | No | 5.5 |
| CVE-2026-43048 | HID: core: Mitigate potential OOB by removing bogus memset() | n/a | No | 8.8 |
| CVE-2026-31777 | ALSA: ctxfi: Check the error for index mapping | n/a | No | 7.0 |
| CVE-2026-31722 | usb: gadget: f_rndis: Fix net_device lifecycle with device_move | n/a | No | 7.8 |
| CVE-2026-43036 | net: use skb_header_pointer() for TCPv4 GSO frag_off check | n/a | No | 5.5 |
| CVE-2026-31769 | gpib: fix use-after-free in IO ioctl handlers | n/a | No | |
| CVE-2026-31707 | ksmbd: validate response sizes in ipc_validate_msg() | n/a | No | 7.1 |
| CVE-2026-31725 | usb: gadget: f_ecm: Fix net_device lifecycle with device_move | n/a | No | 7.8 |
| CVE-2026-43049 | HID: logitech-hidpp: Prevent use-after-free on force feedback initialisation failure | n/a | No | 7.0 |
| CVE-2026-43022 | Bluetooth: hci_sync: hci_cmd_sync_queue_once() return -EEXIST if exists | n/a | No | |
| CVE-2026-43042 | mpls: add seqcount to protect the platform_label{,s} pair | n/a | No | 7.1 |
| CVE-2026-31771 | Bluetooth: hci_event: move wake reason storage into validated event handlers | n/a | No | 8.1 |
| CVE-2026-43052 | wifi: mac80211: check tdls flag in ieee80211_tdls_oper | n/a | No | 7.0 |
| CVE-2026-31709 | smb: client: validate the whole DACL before rewriting it in cifsacl | n/a | No | 8.8 |
| CVE-2026-43021 | Bluetooth: hci_sync: fix leaks when hci_cmd_sync_queue_once fails | n/a | No | |
| CVE-2026-31712 | ksmbd: require minimum ACE size in smb_check_perm_dacl() | n/a | No | 8.3 |
| CVE-2026-43010 | bpf: Reject sleepable kprobe_multi programs at attach time | n/a | No | 5.5 |
| CVE-2026-43019 | Bluetooth: hci_conn: fix potential UAF in set_cig_params_sync | n/a | No | 7.8 |
| CVE-2026-31729 | usb: typec: ucsi: validate connector number in ucsi_notify_common() | n/a | No | 7.0 |
| CVE-2026-43045 | mshv: Fix error handling in mshv_region_pin | n/a | No | |
| CVE-2026-43009 | bpf: Fix incorrect pruning due to atomic fetch precision tracking | n/a | No | 7.8 |
| CVE-2026-31715 | f2fs: fix UAF caused by decrementing sbi->nr_pages[] in f2fs_write_end_io() | n/a | No | 5.5 |
| CVE-2026-31697 | crypto: ccp: Don't attempt to copy ID to userspace if PSP command failed | n/a | No | 7.1 |
| CVE-2026-31721 | usb: gadget: f_hid: move list and spinlock inits from bind to alloc | n/a | No | 7.8 |
| CVE-2026-31711 | smb: server: fix active_num_conn leak on transport allocation failure | n/a | No | 7.5 |
| CVE-2026-31699 | crypto: ccp: Don't attempt to copy CSR to userspace if PSP command failed | n/a | No | 7.1 |
| CVE-2026-31694 | fuse: reject oversized dirents in page cache | n/a | No | 7.8 |
| CVE-2026-31705 | ksmbd: fix out-of-bounds write in smb2_get_ea() EA alignment | n/a | No | 9.8 |
| CVE-2026-43033 | crypto: authencesn - Do not place hiseq at end of dst for out-of-place decryption | n/a | No | 7.8 |
| CVE-2026-31696 | rxrpc: Fix missing validation of ticket length in non-XDR key preparsing | n/a | No | 5.5 |
| CVE-2026-31698 | crypto: ccp: Don't attempt to copy PDH cert to userspace if PSP command failed | n/a | No | 7.1 |
| CVE-2026-31704 | ksmbd: use check_add_overflow() to prevent u16 DACL size overflow | n/a | No | 7.5 |
| CVE-2026-31702 | f2fs: fix use-after-free of sbi in f2fs_compress_write_end_io() | n/a | No | 7.8 |
| CVE-2026-31708 | smb: client: fix OOB read in smb2_ioctl_query_info QUERY_INFO path | n/a | No | 8.1 |
| CVE-2026-31700 | net/packet: fix TOCTOU race on mmap'd vnet_hdr in tpacket_snd() | n/a | No | 7.8 |
| CVE-2026-7598 | libssh2 userauth.c userauth_password integer overflow | n/a | No | 7.3 |
| CVE-2026-43058 | media: vidtv: fix pass-by-value structs causing MSAN warnings | n/a | No | 7.1 |
| CVE-2026-37457 | n/a | No | 7.5 | |
| CVE-2026-43964 | n/a | No | 3.7 | |
| CVE-2026-43037 | ip6_tunnel: clear skb2->cb[] in ip4ip6_err() | n/a | No | 7.0 |
| CVE-2026-33190 | CoreDNS TSIG authentication bypass on encrypted DNS transports | n/a | No | |
| CVE-2026-33489 | CoreDNS transfer plugin subzone ACL bypass via lexicographic zone comparison | n/a | No | |
| CVE-2026-32936 | CoreDNS DoH GET path missing size validation causes CPU and memory amplification | n/a | No | |
| CVE-2026-32934 | CoreDNS DNS-over-QUIC unbounded goroutine growth leads to denial of service | n/a | No | |
| CVE-2026-35579 | CoreDNS TSIG authentication bypass on gRPC, QUIC, DoH, and DoH3 transports | n/a | No | |
| CVE-2026-43073 | x86-64: rename misleadingly named '__copy_user_nocache()' function | n/a | No | 2.5 |
| CVE-2026-42151 | Prometheus Azure AD remote write OAuth client secret exposed via config API | n/a | No | 7.5 |
| CVE-2026-42154 | Prometheus: remote read endpoint allows denial of service via crafted snappy payload | n/a | No | 7.5 |
| CVE-2026-43125 | dlm: validate length in dlm_search_rsb_tree | n/a | No | 7.8 |
| CVE-2026-43248 | vhost: move vdpa group bound check to vhost_vdpa | n/a | No | 7.1 |
| CVE-2026-43176 | wifi: rtw89: pci: validate release report content before using for RTL8922DE | n/a | No | 7.0 |
| CVE-2026-43204 | ASoC: qcom: q6asm: drop DSP responses for closed data streams | n/a | No | 5.5 |
| CVE-2026-43131 | drm/amd/pm: Fix null pointer dereference issue | n/a | No | 5.5 |
| CVE-2026-43126 | ALSA: mixer: oss: Add card disconnect checkpoints | n/a | No | 5.5 |
| CVE-2026-43127 | ntfs3: fix circular locking dependency in run_unpack_ex | n/a | No | 5.5 |
| CVE-2026-43161 | iommu/vt-d: Skip dev-iotlb flush for inaccessible PCIe device without scalable mode | n/a | No | 5.5 |
| CVE-2026-43198 | tcp: fix potential race in tcp_v6_syn_recv_sock() | n/a | No | 4.8 |
| CVE-2026-43245 | ntfs: ->d_compare() must not block | n/a | No | 7.1 |
| CVE-2025-71290 | misc: ti_fpc202: fix a potential memory leak in probe function | n/a | No | 5.5 |
| CVE-2026-43137 | ASoC: SOF: Intel: hda: Fix NULL pointer dereference | n/a | No | 5.5 |
| CVE-2026-43115 | srcu: Use irq_work to start GP in tiny SRCU | n/a | No | 5.5 |
| CVE-2026-43234 | team: avoid NETDEV_CHANGEMTU event when unregistering slave | n/a | No | 5.5 |
| CVE-2025-71293 | drm/amdgpu/ras: Move ras data alloc before bad page check | n/a | No | 5.5 |
| CVE-2026-43172 | wifi: iwlwifi: fix 22000 series SMEM parsing | n/a | No | 5.3 |
| CVE-2025-71285 | net: qrtr: Drop the MHI auto_queue feature for IPCR DL channels | n/a | No | 4.7 |
| CVE-2026-43197 | netconsole: avoid OOB reads, msg is not nul-terminated | n/a | No | 5.5 |
| CVE-2026-43185 | ksmbd: fix signededness bug in smb_direct_prepare_negotiation() | n/a | No | 5.5 |
| CVE-2025-71273 | wifi: rtw88: Use devm_kmemdup() in rtw_set_supported_band() | n/a | No | 5.3 |
| CVE-2026-43118 | btrfs: fix zero size inode with non-zero size after log replay | n/a | No | 3.3 |
| CVE-2026-43109 | x86: shadow stacks: proper error handling for mmap lock | n/a | No | 7.1 |
| CVE-2026-43153 | xfs: remove xfs_attr_leaf_hasname | n/a | No | 7.1 |
| CVE-2026-43129 | ima: verify the previous kernel's IMA buffer lies in addressable RAM | n/a | No | 5.5 |
| CVE-2026-43116 | netfilter: ctnetlink: ensure safe access to master conntrack | n/a | No | 7.1 |
| CVE-2026-43274 | mailbox: mchp-ipc-sbi: fix out-of-bounds access in mchp_ipc_get_cluster_aggr_irq() | n/a | No | 7.1 |
| CVE-2026-43244 | kcm: fix zero-frag skb in frag_list on partial sendmsg error | n/a | No | 5.5 |
| CVE-2026-43191 | drm/amd/display: Adjust PHY FSM transition to TX_EN-to-PLL_ON for TMDS on DCN35 | n/a | No | 5.5 |
| CVE-2026-43258 | alpha: fix user-space corruption during memory compaction | n/a | No | 5.5 |
| CVE-2025-71289 | fs/ntfs3: handle attr_set_size() errors when truncating files | n/a | No | 7.1 |
| CVE-2026-43107 | xfrm: account XFRMA_IF_ID in aevent size calculation | n/a | No | 5.5 |
| CVE-2026-43243 | drm/amd/display: Add signal type check for dcn401 get_phyd32clk_src | n/a | No | 5.5 |
| CVE-2025-71294 | drm/amdgpu: fix NULL pointer issue buffer funcs | n/a | No | 5.5 |
| CVE-2026-43250 | usb: chipidea: udc: fix DMA and SG cleanup in _ep_nuke() | n/a | No | 7.1 |
| CVE-2026-43237 | drm/amdgpu: Refactor amdgpu_gem_va_ioctl for Handling Last Fence Update and Timeline Management v4 | n/a | No | 5.5 |
| CVE-2026-43201 | APEI/GHES: ARM processor Error: don't go past allocated memory | n/a | No | 5.5 |
| CVE-2026-43219 | net: cpsw_new: Fix potential unregister of netdev that has not been registered yet | n/a | No | 7.1 |
| CVE-2026-43165 | hwmon: (nct7363) Fix a resource leak in nct7363_present_pwm_fanin | n/a | No | 5.5 |
| CVE-2026-43088 | net: af_key: zero aligned sockaddr tail in PF_KEY exports | n/a | No | 7.1 |
| CVE-2026-43195 | drm/amdgpu: validate user queue size constraints | n/a | No | 7.1 |
| CVE-2025-71272 | most: core: fix resource leak in most_register_interface error paths | n/a | No | 5.5 |
| CVE-2026-43213 | wifi: rtw89: pci: validate sequence number of TX release report | n/a | No | 7.0 |
| CVE-2026-43228 | hfs: Replace BUG_ON with error handling for CNID count checks | n/a | No | 7.1 |
| CVE-2026-43216 | net: Drop the lock in skb_may_tx_timestamp() | n/a | No | 5.5 |
| CVE-2026-43119 | Bluetooth: hci_sync: annotate data-races around hdev->req_status | n/a | No | 5.3 |
| CVE-2026-43267 | wifi: rtw89: fix potential zero beacon interval in beacon tracking | n/a | No | 7.0 |
| CVE-2026-43101 | ipv6: ioam: fix potential NULL dereferences in __ioam6_fill_trace_data() | n/a | No | 7.0 |
| CVE-2026-43199 | net/mlx5e: Fix "scheduling while atomic" in IPsec MAC address query | n/a | No | 7.0 |
| CVE-2026-43083 | net: ioam6: fix OOB and missing lock | n/a | No | 7.0 |
| CVE-2026-43870 | Apache Thrift: Node.js web_server.js multi-vulnerability | n/a | No | 7.3 |
| CVE-2026-43868 | Apache Thrift: Rust implementation vulnerable to CVE-2020-13949 pattern | n/a | No | 5.3 |
| CVE-2026-33523 | Apache HTTP Server: multiple modules: HTTP response splitting forwarding malicious status line | n/a | No | 6.5 |
| CVE-2026-23918 | Apache HTTP Server: http2: double free and possible RCE on early reset | n/a | No | 8.8 |
| CVE-2026-34059 | Apache HTTP Server: mod_proxy_ajp: Heap Over-Read and memory disclosure in ajp_parse_data() | n/a | No | 7.5 |
| CVE-2026-34032 | Apache HTTP Server: mod_proxy_ajp: Heap Buffer Over-Read Due to Missing Null-Termination Check (ajp_msg_get_string) | n/a | No | 5.3 |
| CVE-2026-24072 | Apache HTTP Server: mod_rewrite elevation of privileges via ap_expr | n/a | No | 8.8 |
| CVE-2026-33006 | Apache HTTP Server: mod_auth_digest timing attack | n/a | No | 4.8 |
| CVE-2026-33007 | Apache HTTP Server: mod_authn_socache crash | n/a | No | 5.3 |
| CVE-2026-29169 | Apache HTTP Server: mod_dav_lock indirect lock crash | n/a | No | 7.5 |
| CVE-2026-29168 | Apache HTTP Server: mod_md unrestricted OCSP response | n/a | No | 7.3 |
| CVE-2026-33857 | Apache HTTP Server: Off-by-one OOB reads in AJP getter functions | n/a | No | 5.3 |
| CVE-2026-41672 | xmldom: XML node injection through unvalidated comment serialization | n/a | No | |
| CVE-2026-41674 | xmldom: XML injection through unvalidated DocumentType serialization | n/a | No | |
| CVE-2026-41675 | xmldom: XML node injection through unvalidated processing instruction serialization | n/a | No | |
| CVE-2026-41673 | xmldom: Denial of service via uncontrolled recursion in XML serialization | n/a | No | |
| CVE-2026-25243 | redis-server RESTORE invalid memory access may allow remote code execution | n/a | No | |
| CVE-2026-23631 | redis-server Lua use-after-free may allow remote code execution | n/a | No | |
| CVE-2026-31717 | ksmbd: validate owner of durable handle on reconnect | n/a | No | 8.8 |
| CVE-2026-31718 | ksmbd: fix use-after-free in __ksmbd_close_fd() via durable scavenger | n/a | No | 9.8 |
| CVE-2026-23479 | redis-server use-after-free in unblock client flow may allow remote code execution | n/a | No | |
| CVE-2026-25588 | RedisTimeSeries RESTORE invalid memory access may allow remote code execution | n/a | No | |
| CVE-2026-25589 | RedisBloom RESTORE invalid memory access may allow remote code execution | n/a | No | |
| CVE-2026-43474 | fs: init flags_valid before calling vfs_fileattr_get | n/a | No | |
| CVE-2026-43338 | btrfs: reserve enough transaction items for qgroup ioctls | n/a | No | |
| CVE-2025-71302 | drm/panthor: fix for dma-fence safe access rules | n/a | No | |
| CVE-2026-43318 | drm/amdgpu: fix sync handling in amdgpu_dma_buf_move_notify | n/a | No | 7.1 |
| CVE-2026-43309 | md raid: fix hang when stopping arrays with metadata through dm-raid | n/a | No | 5.5 |
| CVE-2026-43416 | powerpc, perf: Check that current->mm is alive before getting user callchain | n/a | No | |
| CVE-2025-71299 | spi: cadence-quadspi: Parse DT for flashes with the rest of the DT parsing | n/a | No | 5.5 |
| CVE-2026-43284 | xfrm: esp: avoid in-place decrypt on shared skb frags | n/a | No | 7.8 |
| CVE-2026-43352 | i3c: mipi-i3c-hci: Correct RING_CTRL_ABORT handling in DMA dequeue | n/a | No | 5.5 |
| CVE-2026-43300 | drm/panel: Fix a possible null-pointer dereference in jdi_panel_dsi_remove() | n/a | No | 5.5 |
| CVE-2026-43331 | x86/kexec: Disable KCOV instrumentation after load_segments() | n/a | No | |
| CVE-2026-43320 | drm/amd/display: Fix dsc eDP issue | n/a | No | |
| CVE-2026-43306 | bpf: crypto: Use the correct destructor kfunc type | n/a | No | 7.0 |
| CVE-2026-43443 | ASoC: amd: acp-mach-common: Add missing error check for clock acquisition | n/a | No | |
| CVE-2026-43317 | most: core: fix leak on early registration failure | n/a | No | |
| CVE-2026-43319 | spi: spidev: fix lock inversion between spi_lock and buf_lock | n/a | No | |
| CVE-2026-43303 | mm/page_alloc: clear page->private in free_pages_prepare() | n/a | No | 7.0 |
| CVE-2026-43344 | perf/x86/intel/uncore: Fix die ID init and look up bugs | n/a | No | |
| CVE-2026-43321 | bpf: Properly mark live registers for indirect jumps | n/a | No | 7.8 |
| CVE-2026-43456 | bonding: fix type confusion in bond_setup_by_slave() | n/a | No | 5.5 |
| CVE-2026-43305 | drm/amd/display: Fix mismatched unlock for DMUB HW lock in HWSS fast path | n/a | No | 5.5 |
| CVE-2026-43298 | drm/amdgpu: Skip vcn poison irq release on VF | n/a | No | 7.8 |
| CVE-2026-43299 | btrfs: do not ASSERT() when the fs flips RO inside btrfs_repair_io_failure() | n/a | No | 5.5 |
| CVE-2026-43400 | drm/amdgpu: add upper bound check on user inputs in signal ioctl | n/a | No | |
| CVE-2026-43310 | media: verisilicon: Avoid G2 bus error while decoding H.264 and HEVC | n/a | No | 5.5 |
| CVE-2026-43294 | drm: renesas: rz-du: mipi_dsi: fix kernel panic when rebooting for some panels | n/a | No | 5.5 |
| CVE-2026-43353 | i3c: mipi-i3c-hci: Fix race in DMA ring dequeue | n/a | No | 7.8 |
| CVE-2026-43292 | mm/vmalloc: prevent RCU stalls in kasan_release_vmalloc_node | n/a | No | 5.5 |
| CVE-2026-43398 | drm/amdgpu: add upper bound check on user inputs in wait ioctl | n/a | No | |
| CVE-2026-43311 | soc/tegra: pmc: Fix unsafe generic_handle_irq() call | n/a | No | 5.5 |
| CVE-2026-43421 | usb: gadget: f_ncm: Fix net_device lifecycle with device_move | n/a | No | |
| CVE-2026-43308 | btrfs: don't BUG() on unexpected delayed ref type in run_one_delayed_ref() | n/a | No | 5.5 |
| CVE-2026-37458 | n/a | No | 6.5 | |
| CVE-2026-37459 | n/a | No | 7.5 | |
| CVE-2026-33846 | Gnutls: gnutls: denial of service via heap buffer overflow in dtls handshake fragment reassembly | n/a | No | 7.5 |
| CVE-2026-6664 | PgBouncer integer overflow in PgBouncer network packet parsing | n/a | No | 7.5 |
| CVE-2026-6665 | PgBouncer buffer overflow in SCRAM | n/a | No | 8.1 |
| CVE-2026-6667 | PgBouncer missing authorization check in KILL_CLIENT admin command | n/a | No | 4.3 |
| CVE-2026-6666 | PgBouncer crash in kill_pool_logins_server_error | n/a | No | 5.9 |
| CVE-2026-45130 | Vim: Heap Buffer Overflow in spell file loading | n/a | No | 6.6 |
| CVE-2026-44656 | Vim: OS Command Injection via 'path' completion | n/a | No | |
| CVE-2026-33811 | Crash when handling long CNAME response in net | n/a | No | 7.5 |
| CVE-2026-33814 | Infinite loop in HTTP/2 transport when given bad SETTINGS_MAX_FRAME_SIZE in net/http/internal/http2 in golang.org/x/net | n/a | No | 7.5 |
| CVE-2026-39817 | Invoking "go tool pack" does not sanitize output paths in cmd/go | n/a | No | 5.9 |
| CVE-2026-39819 | Invoking "go bug" follows symlinks in predictable temporary filenames in cmd/go | n/a | No | 5.3 |
| CVE-2026-39820 | Quadratic string concatentation in consumeComment in net/mail | n/a | No | 7.5 |
| CVE-2026-39823 | Bypass of meta content URL escaping causes XSS in html/template | n/a | No | 6.1 |
| CVE-2026-39825 | ReverseProxy forwards queries with more than urlmaxqueryparams parameters in net/http/httputil | n/a | No | 5.3 |
| CVE-2026-39826 | Escaper bypass leads to XSS in html/template | n/a | No | 6.1 |
| CVE-2026-39836 | Panic in Dial and LookupPort when handling NUL byte on Windows in net | n/a | No | 7.5 |
| CVE-2026-42499 | Quadratic string concatenation in consumePhrase in net/mail | n/a | No | 7.5 |
| CVE-2026-42501 | Malicious module proxy can bypass checksum database in cmd/go | n/a | No | 7.5 |
| CVE-2026-33079 | Mistune ReDoS in LINK_TITLE_RE allows denial of service with crafted Markdown titles | n/a | No | |
| CVE-2026-41889 | pgx: SQL Injection via placeholder confusion with dollar quoted string literals | n/a | No | |
| CVE-2026-42257 | net-imap: Command Injection via "raw" arguments to multiple commands | n/a | No | |
| CVE-2026-42258 | net-imap: Command Injection via unvalidated Symbol inputs | n/a | No | |
| CVE-2026-42256 | net-imap: Denial of service via high iteration count for `SCRAM-*` authentication | n/a | No | |
| CVE-2026-42246 | net-imap vulnerable to STARTTLS stripping via invalid response timing | n/a | No | |
| CVE-2026-45186 | n/a | No | 2.9 | |
| CVE-2026-7261 | SoapServer session-persisted object use-after-free via SOAP header fault | n/a | No | |
| CVE-2026-7258 | Out-of-bounds read in urldecode() on NetBSD | n/a | No | |
| CVE-2026-6722 | Use-After-Free in SOAP using Apache map | n/a | No | |
| CVE-2026-6735 | XSS within PHP-FPM status endpoint | n/a | No | |
| CVE-2026-7262 | NULL pointer dereference in SOAP apache:Map decoder with missing <value> | n/a | No | |
| CVE-2025-14179 | SQL injection in pdo_firebird via NUL bytes in quoted strings | n/a | No | |
| CVE-2026-7568 | Signed integer overflow in metaphone() | n/a | No | |
| CVE-2026-7259 | Null pointer dereference in php_mb_check_encoding() via mb_ereg_search_init() | n/a | No | |
| CVE-2026-43500 | rxrpc: Also unshare DATA/RESPONSE packets when paged frags are present | n/a | No | 7.8 |
SQL Server vulnerabilities
CVE | Title | Exploitation status | Publicly disclosed? | CVSS v3 base score |
|---|---|---|---|---|
| CVE-2026-40370 | SQL Server Remote Code Execution Vulnerability | Exploitation Less Likely | No | 8.8 |
Windows vulnerabilities
CVE | Title | Exploitation status | Publicly disclosed? | CVSS v3 base score |
|---|---|---|---|---|
| CVE-2025-54518 | AMD: CVE-2025-54518 CPU OP Cache Corruption | Exploitation Unlikely | No | |
| CVE-2026-41095 | Data Deduplication Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-35424 | Internet Key Exchange (IKE) Protocol Denial of Service Vulnerability | Exploitation Unlikely | No | 7.5 |
| CVE-2026-40377 | Microsoft Cryptographic Services Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-34329 | Microsoft Message Queuing (MSMQ) Remote Code Execution Vulnerability | Exploitation Less Likely | No | 8.8 |
| CVE-2026-41097 | Secure Boot Security Feature Bypass Vulnerability | Exploitation Less Likely | No | 6.7 |
| CVE-2026-33839 | Win32k Elevation of Privilege Vulnerability | Exploitation Unlikely | No | 7.0 |
| CVE-2026-33840 | Win32k Elevation of Privilege Vulnerability | Exploitation More Likely | No | 7.8 |
| CVE-2026-34330 | Win32k Elevation of Privilege Vulnerability | Exploitation Unlikely | No | 7.8 |
| CVE-2026-34331 | Win32k Elevation of Privilege Vulnerability | Exploitation Unlikely | No | 7.0 |
| CVE-2026-35423 | Windows 11 Telnet Client Information Disclosure Vulnerability | Exploitation Unlikely | No | 5.4 |
| CVE-2026-35438 | Windows Admin Center Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 8.3 |
| CVE-2026-34344 | Windows Ancillary Function Driver for WinSock Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-34345 | Windows Ancillary Function Driver for WinSock Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.0 |
| CVE-2026-35416 | Windows Ancillary Function Driver for WinSock Elevation of Privilege Vulnerability | Exploitation More Likely | No | 7.0 |
| CVE-2026-41088 | Windows Ancillary Function Driver for WinSock Elevation of Privilege Vulnerability | Exploitation Unlikely | No | 7.8 |
| CVE-2026-34343 | Windows Application Identity (AppID) Subsystem Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-35418 | Windows Cloud Files Mini Filter Driver Elevation of Privilege Vulnerability | Exploitation Unlikely | No | 7.8 |
| CVE-2026-33835 | Windows Cloud Files Mini Filter Driver Elevation of Privilege Vulnerability | Exploitation More Likely | No | 7.8 |
| CVE-2026-34337 | Windows Cloud Files Mini Filter Driver Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-40407 | Windows Common Log File System Driver Elevation of Privilege Vulnerability | Exploitation Unlikely | No | 7.8 |
| CVE-2026-40397 | Windows Common Log File System Driver Elevation of Privilege Vulnerability | Exploitation More Likely | No | 7.8 |
| CVE-2026-41096 | Windows DNS Client Remote Code Execution Vulnerability | Exploitation Unlikely | No | 9.8 |
| CVE-2026-42896 | Windows DWM Core Library Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-35419 | Windows DWM Core Library Information Disclosure Vulnerability | Exploitation Less Likely | No | 5.5 |
| CVE-2026-34336 | Windows DWM Core Library Information Disclosure Vulnerability | Exploitation Unlikely | No | 7.8 |
| CVE-2026-33834 | Windows Event Logging Service Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-32209 | Windows Filtering Platform (WFP) Security Feature Bypass Vulnerability | Exploitation Unlikely | No | 4.4 |
| CVE-2026-35421 | Windows GDI Remote Code Execution Vulnerability | Exploitation Unlikely | No | 7.8 |
| CVE-2026-40403 | Windows Graphics Component Remote Code Execution Vulnerability | Exploitation Less Likely | No | 8.8 |
| CVE-2026-40402 | Windows Hyper-V Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 9.3 |
| CVE-2026-33841 | Windows Kernel Elevation of Privilege Vulnerability | Exploitation More Likely | No | 7.8 |
| CVE-2026-35420 | Windows Kernel Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-40369 | Windows Kernel Elevation of Privilege Vulnerability | Exploitation More Likely | No | 7.8 |
| CVE-2026-34332 | Windows Kernel-Mode Driver Remote Code Execution Vulnerability | Exploitation Unlikely | No | 8.0 |
| CVE-2026-34339 | Windows Lightweight Directory Access Protocol (LDAP) Denial of Service Vulnerability | Exploitation Less Likely | No | 5.5 |
| CVE-2026-34341 | Windows Link-Layer Discovery Protocol (LLDP) Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.0 |
| CVE-2026-33838 | Windows Message Queuing (MSMQ) Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-32161 | Windows Native WiFi Miniport Driver Remote Code Execution Vulnerability | Exploitation Less Likely | No | 7.5 |
| CVE-2026-41089 | Windows Netlogon Remote Code Execution Vulnerability | Exploitation Less Likely | No | 9.8 |
| CVE-2026-34342 | Windows Print Spooler Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.0 |
| CVE-2026-34340 | Windows Projected File System Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.0 |
| CVE-2026-40398 | Windows Remote Desktop Services Elevation of Privilege Vulnerability | Exploitation More Likely | No | 7.8 |
| CVE-2026-21530 | Windows Rich Text Edit Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 6.7 |
| CVE-2026-32170 | Windows Rich Text Edit Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 6.7 |
| CVE-2026-40410 | Windows SMB Client Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.0 |
| CVE-2026-35415 | Windows Storage Spaces Controller Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-34350 | Windows Storport Miniport Driver Denial of Service Vulnerability | Exploitation Unlikely | No | 6.5 |
| CVE-2026-40405 | Windows TCP/IP Denial of Service Vulnerability | Exploitation Less Likely | No | 7.5 |
| CVE-2026-40414 | Windows TCP/IP Denial of Service Vulnerability | Exploitation Unlikely | No | 7.4 |
| CVE-2026-40401 | Windows TCP/IP Denial of Service Vulnerability | Exploitation Unlikely | No | 7.1 |
| CVE-2026-40413 | Windows TCP/IP Denial of Service Vulnerability | Exploitation Less Likely | No | 7.4 |
| CVE-2026-35422 | Windows TCP/IP Driver Security Feature Bypass Vulnerability | Exploitation Unlikely | No | 6.5 |
| CVE-2026-34351 | Windows TCP/IP Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-40399 | Windows TCP/IP Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-34334 | Windows TCP/IP Elevation of Privilege Vulnerability | Exploitation Unlikely | No | 7.8 |
| CVE-2026-40406 | Windows TCP/IP Information Disclosure Vulnerability | Exploitation Less Likely | No | 7.5 |
| CVE-2026-33837 | Windows TCP/IP Local Elevation of Privilege Vulnerability | Exploitation More Likely | No | 7.8 |
| CVE-2026-40415 | Windows TCP/IP Remote Code Execution Vulnerability | Exploitation Unlikely | No | 8.1 |
| CVE-2026-42825 | Windows Telephony Service Elevation of Privilege Vulnerability | Exploitation Unlikely | No | 7.0 |
| CVE-2026-34338 | Windows Telephony Service Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-40382 | Windows Telephony Service Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-40380 | Windows Volume Manager Extension Driver Remote Code Execution Vulnerability | Exploitation Less Likely | No | 6.2 |
| CVE-2026-40408 | Windows WAN ARP Driver Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-34333 | Windows Win32k Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-34347 | Windows Win32k Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.0 |
| CVE-2026-35417 | Windows Win32k Elevation of Privilege Vulnerability | Exploitation More Likely | No | 7.8 |
Critical RCEs and EoPs
CVE | Title | Exploitation status | Publicly disclosed? | CVSS v3 base score |
|---|---|---|---|---|
| CVE-2026-33109 | Azure Managed Instance for Apache Cassandra Remote Code Execution Vulnerability | N/A | No | 9.9 |
| CVE-2026-33844 | Azure Managed Instance for Apache Cassandra Remote Code Execution Vulnerability | N/A | No | 9.0 |
| CVE-2026-42823 | Azure Logic Apps Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 9.9 |
| CVE-2026-42898 | Microsoft Dynamics 365 On-Premises Remote Code Execution Vulnerability | Exploitation Unlikely | No | 9.9 |
| CVE-2026-42833 | Microsoft Dynamics 365 On-Premises Remote Code Execution Vulnerability | Exploitation Less Likely | No | 9.1 |
| CVE-2026-41103 | Microsoft SSO Plugin for Jira & Confluence Elevation of Privilege Vulnerability | Exploitation More Likely | No | 9.1 |
| CVE-2026-41096 | Windows DNS Client Remote Code Execution Vulnerability | Exploitation Unlikely | No | 9.8 |
| CVE-2026-40402 | Windows Hyper-V Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 9.3 |
| CVE-2026-41089 | Windows Netlogon Remote Code Execution Vulnerability | Exploitation Less Likely | No | 9.8 |