Earlier this year, we made a significant announcement: Rapid7 partnered with ARMO to add AI-powered cloud application detection and response (CADR) – or cloud runtime security – to our cloud security portfolio. At the time, I published a blog highlighting this two-part approach for modern cloud security that combines preemptive exposure management (understanding the threats that could exist) with proactive runtime security (detecting the threats that are happening).
Today, we are thrilled to announce that this vision is fully realized and integrated with Rapid7 Exposure Command. For our customers, this milestone represents our ability to deliver on the promise of a complete Cloud-Native Application Protection Platform (CNAPP) that helps security teams preemptively identify and proactively thwart attacks.
Exploring the possibilities of this unified CNAPP
At Rapid7, we believe that a CNAPP is unified if it operates from a single, objective source of truth. By integrating cloud runtime security directly into Exposure Command, we are seamlessly merging the preemptive (posture, configurations, identities, and vulnerabilities) with the proactive (runtime behavior and active threats). The table below summarizes this enhancement:
⠀
Today’s Rapid7 Cloud Security solution | What cloud runtime adds | |
Primary Focus | Prevention, risk reduction, and preemptive response | Real-time exposure detection and proactive response |
Core Question | "What is vulnerable and could be attacked?" | "Is an attacker exploiting our environment now?" |
Lifecycle Stage | Pre-deployment, continuous scanning, or periodic intervals | Continuous monitoring of live (in-production) workloads |
What It Finds | Misconfigurations, exposed secrets, software CVEs, missing patches | Active exploits, lateral movement, unauthorized process execution, SQL injection |
⠀
The true power of this unified architecture is best understood through the lens of a security practitioner’s daily battle against cloud threats. The previous blog post discussed this in theory; let’s use this blog to talk about the reality.
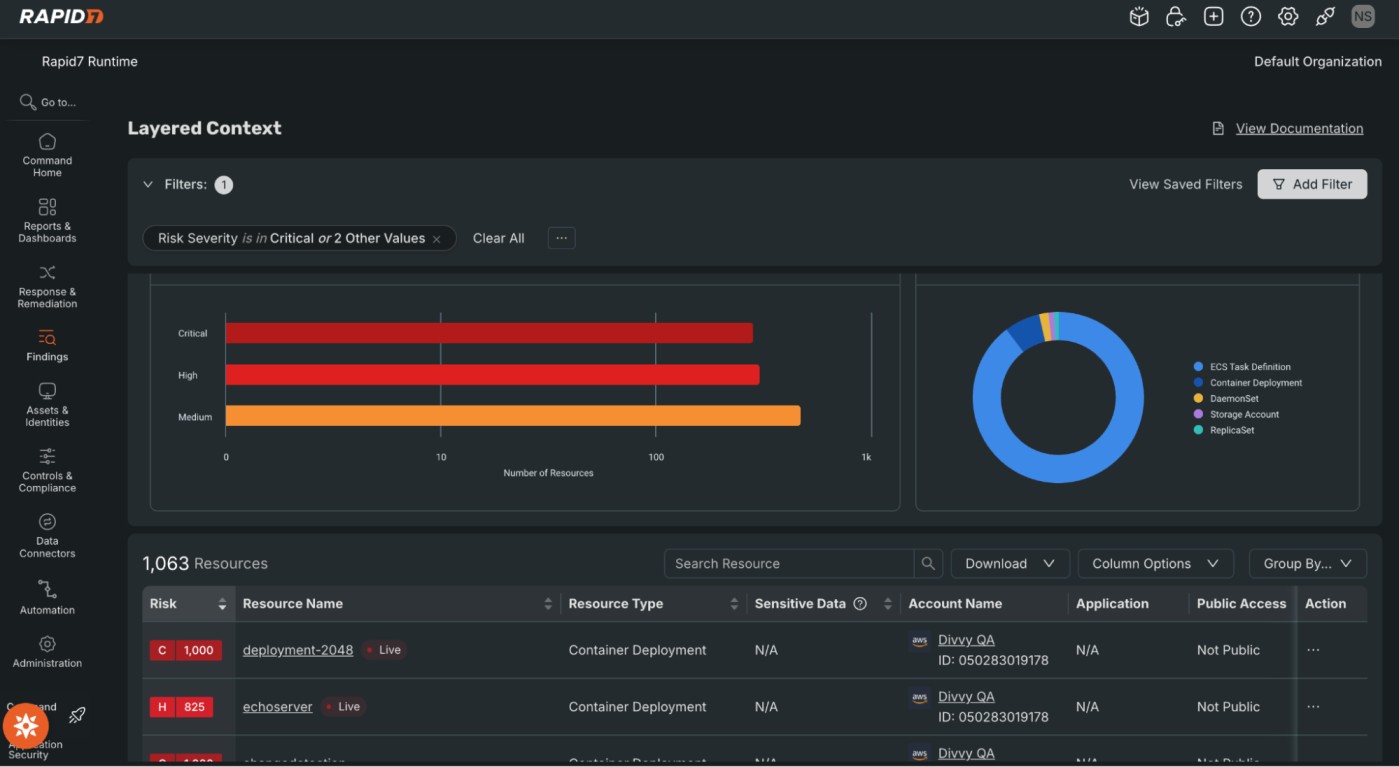
The baseline
Exposure Command continuously scans and assesses your cloud posture to identify whether a container exposure exists in a production cluster. Traditional scanners would stop here, leaving you to prioritize this vulnerability against others. In Exposure Command, this detection is not just part of a static score, but instead it is part of an attack path. Our preemptive security platform tells you, for instance, whether this specific container has internet access and an over-privileged IAM role, making it highly reachable and exploitable. This means that you are not just looking at a CVE; you are looking at the potential blueprint behind a major breach.
The proactive validation
This is where cloud runtime security turns theory into reality. Instead of treating the vulnerability as just a potential risk, the platform utilizes eBPF sensors to provide continuous, direct kernel-level observability and application L7 visibility. Exposure Command analyzes this sensor data, uses AI to establish baseline workload behavior, and uncovers anomalies in real time. For example, security analysts gain instant visibility when that vulnerable container suddenly spawns a reverse shell and initiates an external connection to a known malicious IP, rather than executing its standard database queries.
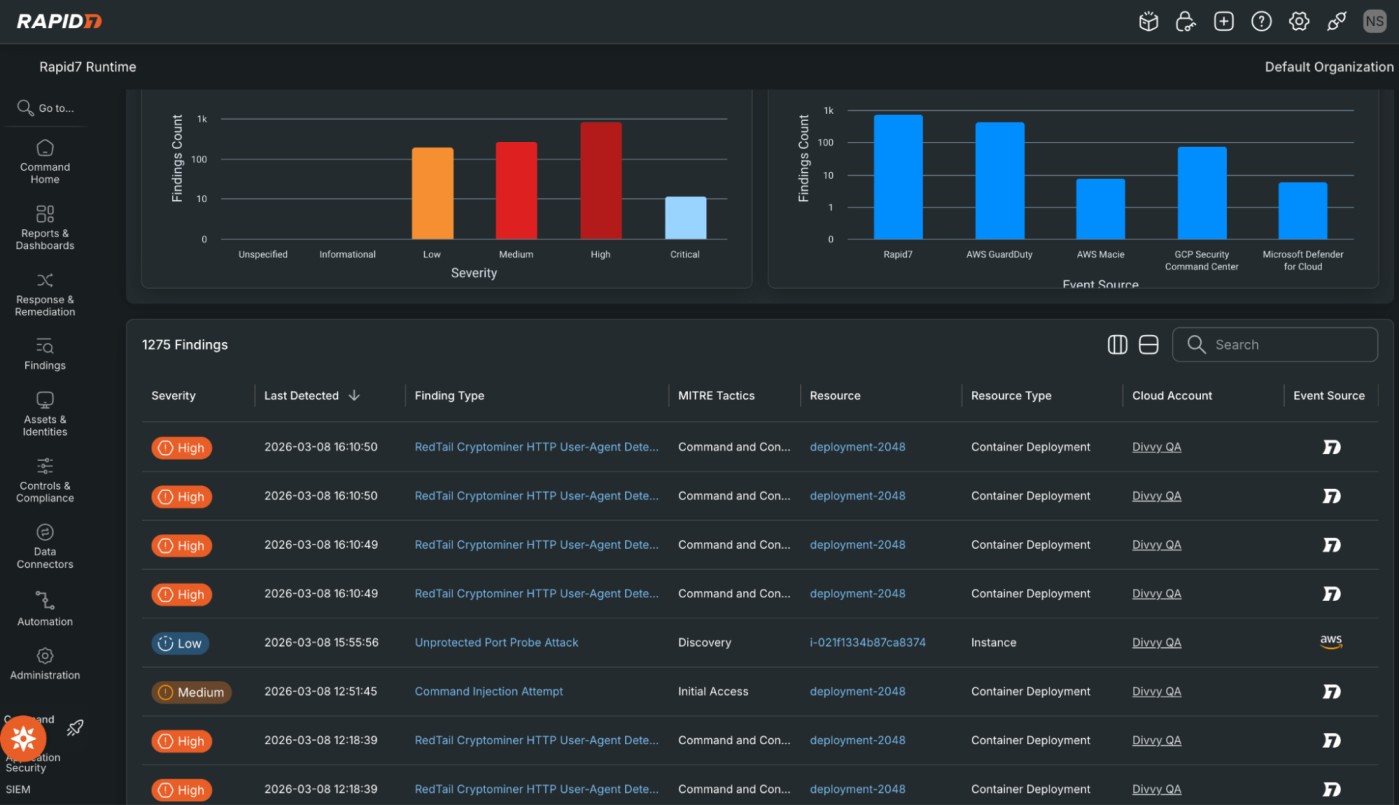
The response
When a runtime anomaly is detected on a high-priority asset, the platform instantly aggregates these events into streamlined alerts. It links the initial application-layer exploit to the infrastructure-level change, such as the attacker attempting a container escape using that over-privileged IAM role. More importantly, the platform can trigger an automated response. By automatically terminating the malicious process, pausing the compromised container, or isolating the namespace, Exposure Command effectively stops an attacker's lateral movement in seconds.
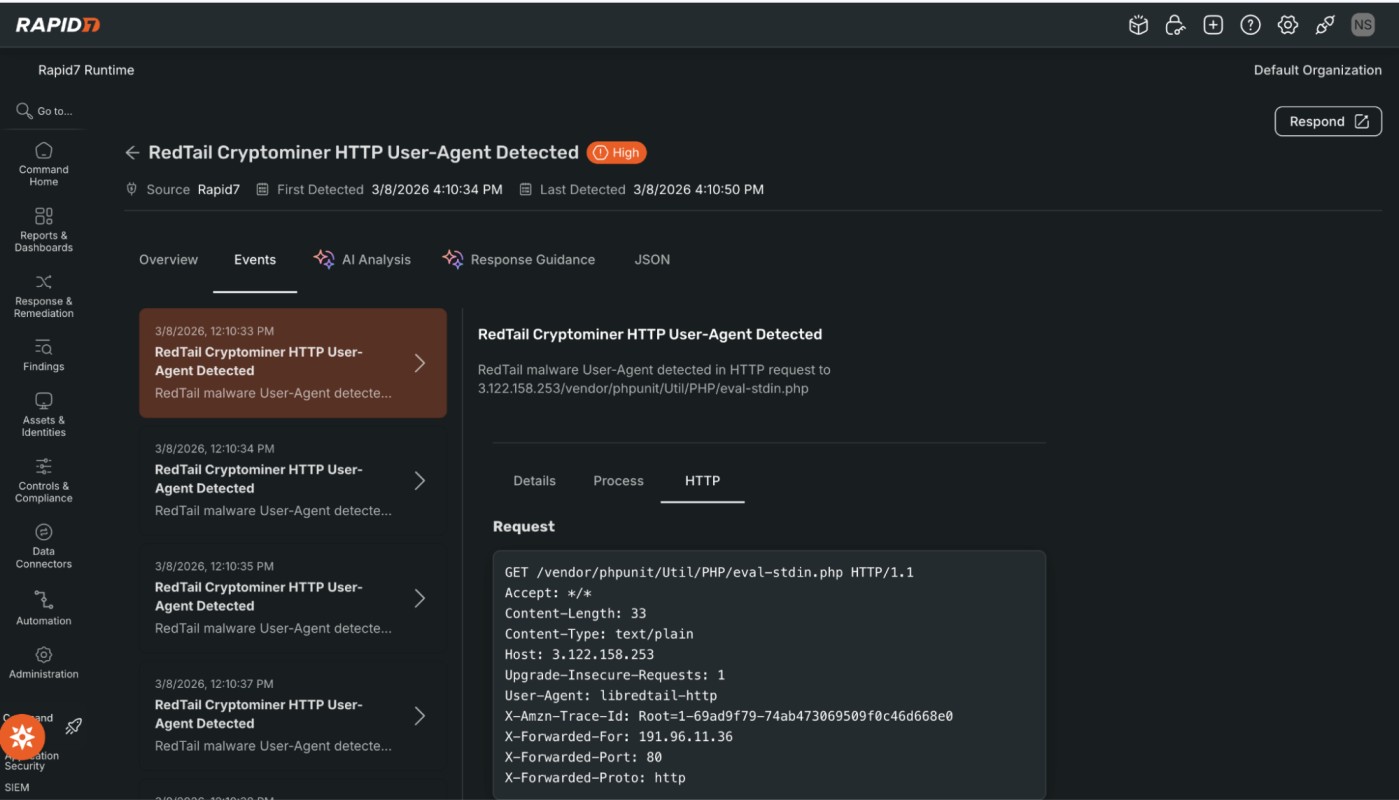
The investigation
Stopping the threat, understanding how it happened, and proving you resolved it, is what creates a truly resilient security program. Rapid7 Exposure Command does not just initially block the attack and leave you sifting through raw kernel logs to truly remediate the threat. Instead, it uses AI-generated remediation summaries to translate complex runtime telemetry into a clear, actionable remediation narrative. It explains exactly how the attacker bypassed initial defenses, what lateral movement they attempted, and the precise root-cause misconfigurations that allowed it. This empowers security teams to confidently report to leadership on the active threats they've neutralized, while providing developers with the exact context and code-level recommendations they need to patch the underlying exposure.
Amplifying signal vs. noise
When you combine predictive exposure analytics with deep application-layer and kernel-level visibility, you fundamentally change your operational efficiency. You stop chasing every theoretical risk and start focusing on what matters most. Exposure Command is a unified solution that eliminates the noisy alerts that tend to overwhelm security operations teams. Teams are able to prioritize remediation not just by CVSS score, but by real-time validation of what is actively loaded into memory and what is currently being exploited (i.e., risk and exposure). This means your developers spend less time patching vulnerabilities that fail to pose an immediate risk, and SecOps spends less time investigating benign container behavior.
With the general availability of cloud runtime security as part of Exposure Command, Rapid7 delivers a strategic, engineering-driven platform that achieves the mission of true CNAPP. We provide the precise answer to, "Could I be compromised?" through preemptive exposure management, and the definitive answer to, "Am I currently compromised?" through proactive runtime security. By closing the loop between these two questions, we allow enterprises to secure their cloud environments with accuracy, speed, and confidence. This is a great example of the wider approach to preemptive security that Rapid7 is delivering across different use cases through the Command Platform’s comprehensive exposure management and threat detection & response capabilities.
Visit Rapid7's CNAPP hub page to learn more about how the fully integrated Rapid7 Exposure Command with cloud runtime security can transform your cloud defense.
Article Tags
Related blog posts

Exposure Management
Why CVSS is No Longer Enough for Exposure Management
Joel Alcon

Exposure Management
Protect What Matters Most: Aligning Sensitive Data with Exposure Risk
Michael Chroney

Exposure Management
The End of the Road for Cisco Kenna: Take a Measured Path into Exposure Management
Michael Chroney

Cloud and Devops Security
Reducing Cloud Chaos: Rapid7 Partners with ARMO to Deliver Cloud Runtime Security
Joel Alcon

