What is purple teaming?
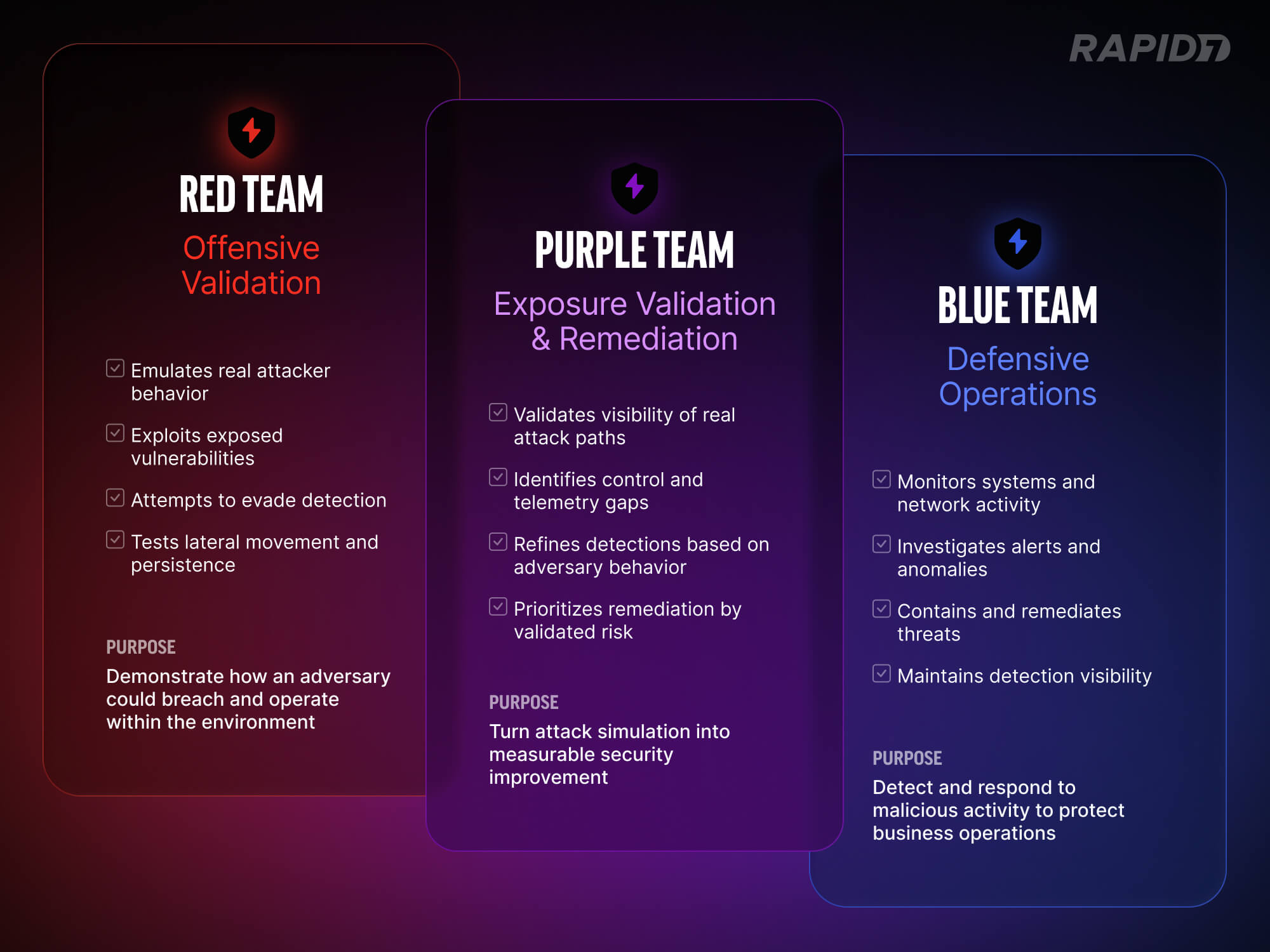
Purple teaming is often described as the collaboration between red teams and blue teams. That definition is accurate, but incomplete. At its core, purple teaming is about exposure validation: deliberately testing whether the threats you believe you can detect and contain are actually visible in your environment.
Red teams simulate attacker behavior. Blue teams defend and respond. Purple teaming ensures those two functions operate in lockstep, sharing telemetry, assumptions, and findings to strengthen detection coverage and close control gaps.
⠀
Unlike traditional penetration testing, which is often point-in-time and compliance-driven, purple teaming is iterative. It is designed to measure, refine, and retest. The goal is not to “win” an exercise. The goal is to improve the organization’s ability to detect, investigate, and contain real attack paths.
Many security programs look mature on paper. Controls are deployed. EDR is in place. Logging is centralized. Dashboards show green indicators. Yet when realistic attacker behavior is exercised inside the environment, gaps often surface quickly. Telemetry may be incomplete. Detection rules may exist but lack tuning. Alerts may trigger without clear ownership or response workflow.
Purple teaming exists to close the gap between perceived protection and actual defensive capability. It replaces assumption with validation.
What purple teaming actually means in 2026
Purple teaming is often described as collaboration between red and blue teams. In practice, it is structured exposure validation conducted in an open-book format.
Offensive operators simulate real-world attack scenarios in coordination with defensive teams. The security operations or incident response team is aware of the exercise from the outset. Together, they define the threat scenarios to test specific response playbooks and detection coverage. The objective is not to surprise the SOC. It is to measure whether detection, telemetry, and response workflows operate as intended and to refine them in real time.
If defensive teams cannot follow a tactic or lack necessary telemetry, activities pause. Gaps are identified and corrected collaboratively. Purple teaming strengthens detection engineering, investigative workflows, and cross-team communication without the pressure of a live incident.
Beyond scorecards: Real-world context matters
Some organizations equate purple teaming with automated breach and attack simulation tools. A sequence of techniques is executed against an assumed compromised host, and a report shows which detection rules are fired. Those metrics can provide visibility into rule coverage. They do not show whether an attacker can exploit real exposures in the environment.
A more contextual approach begins with tailored threat scenarios based on the organization’s actual risk profile. Operators assess real vulnerabilities and misconfigurations rather than firing generic techniques. The focus is not simply to validate rules but to determine whether exploitable exposures exist that blend into legitimate functionality.
Attackers often operate within intended system behavior. They abuse excessive permissions, leverage trust relationships, and exploit architectural weaknesses that were never designed to generate alerts. In these cases, writing a new detection rule does not address the underlying issue. The exposure stems from posture and configuration.
Lateral movement is then executed using access that genuinely exists in the environment. The question becomes whether the organization can observe attacker progression through normal administrative pathways and whether defensive visibility extends beyond initial compromise.
Persistence techniques are established in ways consistent with how an adversary would maintain access in that specific configuration. Detection is measured continuously.
The engagement concludes with a collaborative hunt exercise. The breach lifecycle is recreated without triggering alerts, followed by the intentional generation of a single alert. Teams then work from that signal to reconstruct the attack chain. This phase often reveals how tooling, telemetry, and processes function under structured scrutiny.
Where red teaming fits: Vector Command
It is important to distinguish purple teaming from red teaming.
In a true red team engagement, the SOC and incident response teams are not aware of the breach. Operators attempt to remain undetected for as long as possible. The goal is to emulate a real adversary and test how the organization responds under live conditions.
This is how Vector Command operates. It functions as a continuous red team service, attempting to breach client environments and achieve defined objectives while avoiding detection. If detection occurs during a red team engagement, the SOC response is observed as it would be during a genuine incident. This tests process maturity, investigative speed, and real-world visibility. If and when a breach is detected, the engagement can transition into a collaborative purple team phase. At that point, operators work openly with the SOC to walk through the attack path, identify detection gaps, and refine telemetry and response workflows.
Red teaming measures whether defenses hold up under pressure. Purple teaming refines those defenses collaboratively.
The two approaches are complementary. A red team engagement may identify a successful breach path. After that breach concludes, organizations can transition into purple team activities. Offensive findings are shared openly with defensive teams, and gaps are tuned and remediated. When paired with managed detection and response services, this refinement can occur in coordination with both the customer’s security team and the managed SOC.

⠀
In this model, red teaming exposes real weaknesses. Purple teaming strengthens defenses against them.
What effective purple teaming delivers
Effective purple teaming produces operational improvement rather than a static report.
Detection logic improves because it is tuned against real attacker behavior
Telemetry gaps are identified and corrected
Ownership of investigation workflows becomes clear
Remediation is prioritized against validated attack paths rather than theoretical risk
For senior security leaders, the value is measurable control effectiveness. Purple teaming provides evidence that investments in tools and people translate into improved resilience. It also builds alignment between offensive and defensive teams. That alignment accelerates improvement and reduces friction across security, IT, and operations.
In an environment where attack techniques evolve and exposure surfaces expand, purple teaming offers something concrete: validated insight into how well the organization can detect, investigate, and contain adversary behavior.
Resilience should not be assumed. It should be tested.
Related blog posts

Industry Trends
Red Teaming in 2026: What to Expect at our 2026 Global Cybersecurity Summit
Emma Burdett

Products and Tools
From Vectors to Verdicts: Web App Testing with Vector Command
Ed Montgomery

Products and Tools
From Perimeter to Core: Vector Command Advanced Expands Red Team Coverage
Ed Montgomery

Industry Trends
Key Takeaways from the Take Command Summit 2025: Outpacing the Adversary – Red Teaming in a Complex Threat Landscape
Rapid7