Posts tagged Log Management

Detection and Response
Turning Log Lines into Answers: Instant Clarity for SOC Teams
Sean O'Brien
Detection and Response
Want to stay ahead of emerging threats? Here’s how.
Aaron Wells

Detection and Response
Easily Explore Your Log Data with a Single Query in InsightIDR
Eoin Shanley

Detection and Response
Automating the Cloud: AWS Security Done Efficiently
Josh Frantz

Products and Tools
SIEM Delivery Models: Where Do Today’s Risks and Future Technology Lead Us?
Meaghan Buchanan

Products and Tools
Rolling with Your Logs, Part 3: Using Regex to Expand Your Search Options
Teresa Copple

Detection and Response
Rolling with Your Logs, Part 2: Advanced Mode Searches
Teresa Copple

Detection and Response
Rolling with Your Logs, Part 1: Your Guide to Log Search in InsightIDR
Teresa Copple
Products and Tools
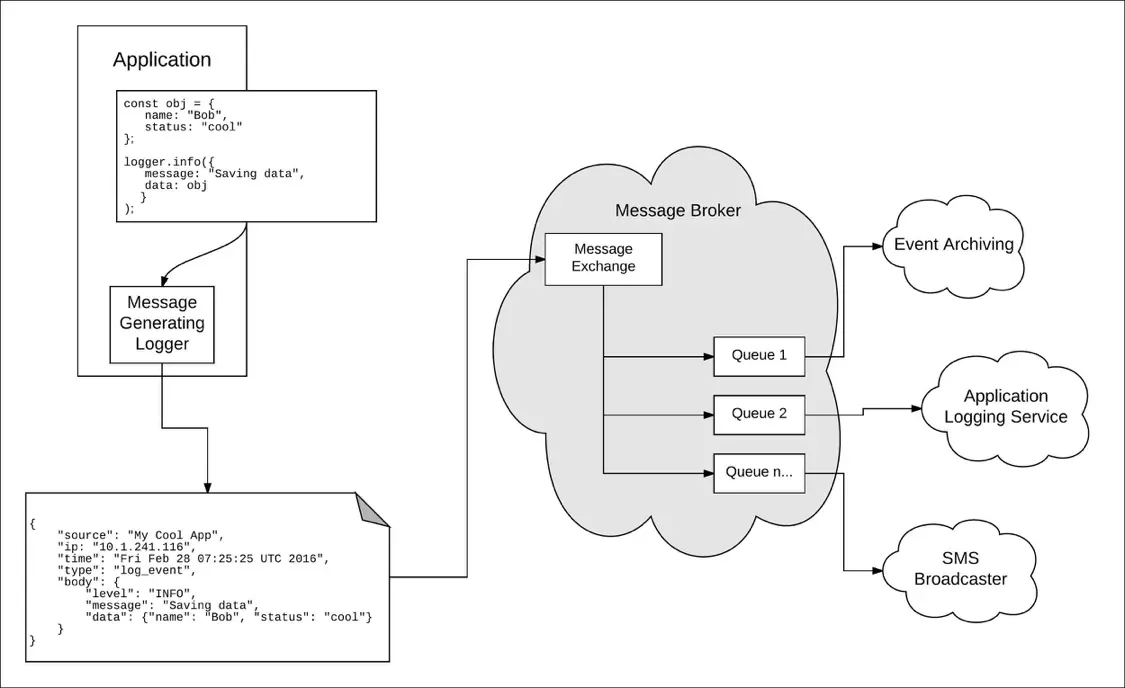
Taking a Message-Based Approach to Logging
Robert Reselman
Detection and Response
6 Best Practices for Effective IT Troubleshooting
Robert Reselman

Security Operations
3 Steps to Building an Effective Log Management Policy
Robert Reselman

Detection and Response
5 Ways to Use Log Data to Analyze System Performance
Rapid7

Detection and Response
What is Syslog?
Rapid7

Detection and Response
Active vs. Passive Server Monitoring
Rapid7

Detection and Response
Announcing InsightOps - Pioneering Endpoint Visibility and Log Analytics
Trevor Parsons

Products and Tools
User Behavior Analytics and Privacy: It's All About Respect
Joseph Busch

Detection and Response
Log Search Simplified
Laura Ellis

Products and Tools
Using Log Data as Forensic Evidence
Annie Hathaway

Products and Tools
Securing Your Metasploit Logs
Justin Buchanan

Products and Tools
10 Best Practices for Log Management and Analytics
Rapid7

Detection and Response
Logentries Joins the Rapid7 Family
Andrew Burton