Cloud Runtime Security
Secure Clouds at Runtime
Turn noisy alerts into validated exposures by continuously uncovering and automatically responding to active threats the instant they hit your cloud workloads.
Go beyond posture security with runtime detection and response
Posture management
Map your attack surface to identify misconfigurations and exposures before deployment.
Detection and response
Monitor live cloud environments to detect and neutralize active exploits as they happen.
Posture management
Map your attack surface to identify misconfigurations and exposures before deployment.
Detection and response
Monitor live cloud environments to detect and neutralize active exploits as they happen.
Stop chasing alerts. Start understanding behavior.
An integrated AI engine monitors container behavior and automates a response when anomalies arise.
Behavioral, not just rules-based
Rapid7 leverages behavioral detection to identify evolving threats, going beyond rules-based methods that only rely on known signatures.
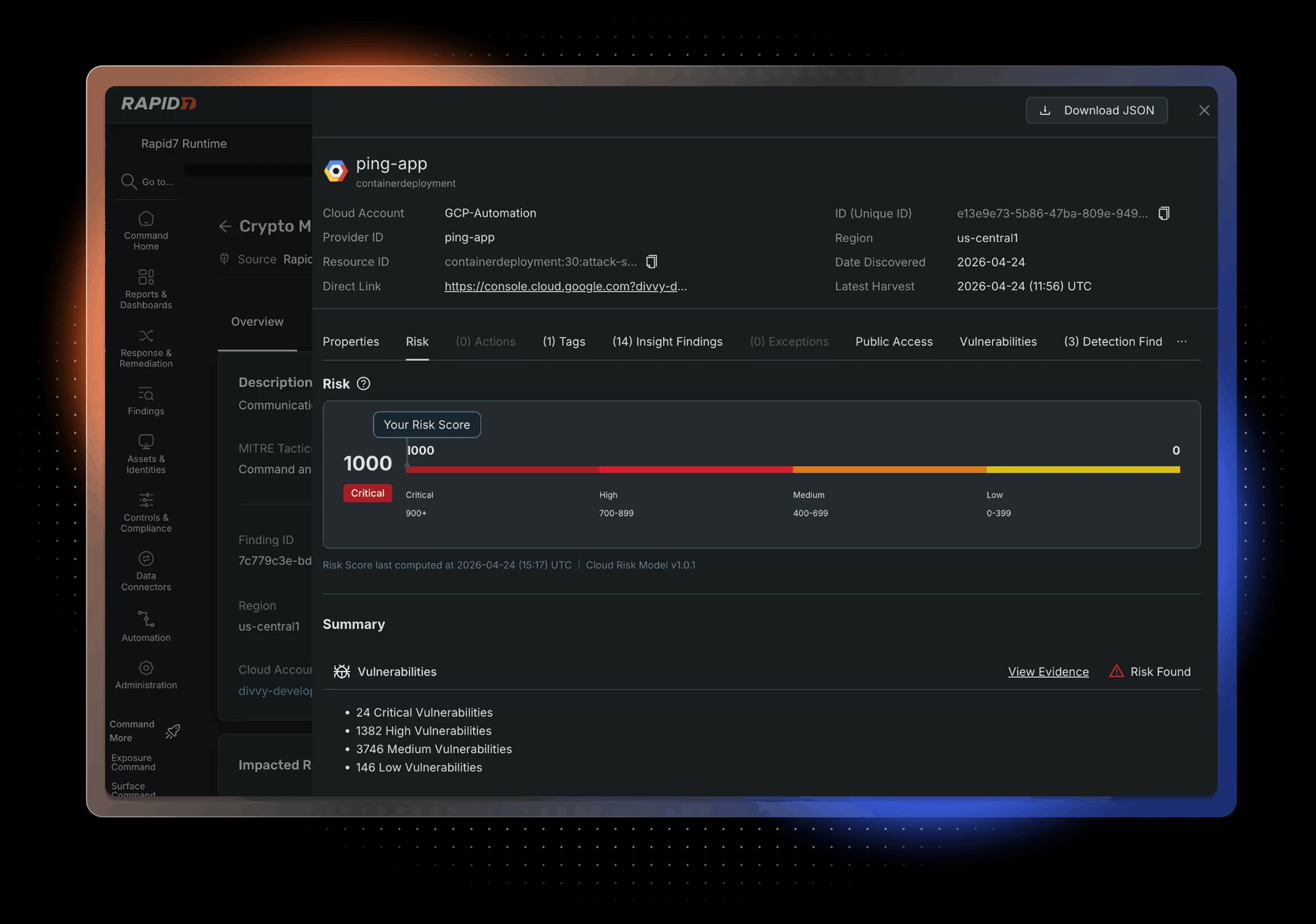
Connect the dots, from runtime to exposure
Rapid7 links container activity to exposures, enabling teams to continuously pinpoint which vulnerabilities are actively at risk.
Contain without disrupting the business
Rapid7 enables automated exposure containment, empowering teams to quickly stop threats and reduce the impact of an attack.
Behavioral, not just rules-based
Rapid7 leverages behavioral detection to identify evolving threats, going beyond rules-based methods that only rely on known signatures.
Connect the dots, from runtime to exposure
Rapid7 links container activity to exposures, enabling teams to continuously pinpoint which vulnerabilities are actively at risk.
Contain without disrupting the business
Rapid7 enables automated exposure containment, empowering teams to quickly stop threats and reduce the impact of an attack.