The Rapid7 Blog:
Your Signal in the Security Noise
Insights, stories, and guidance from our global security and research teams.
Featured posts
3687 Results

Threat Research
Rsunk your Battleship: An Ocean of Data Exposed through Rsync
Jon Hart
Exposure Management
How to Use the InsightVM Policy Compliance Status Report to Measure Benchmark Configurations
Jesika McEvoy

Exposure Management
Rapid7 Partners with AWS Security Hub for Deeper Vulnerability Reporting
Alfred Chung

Detection and Response
Windows Event Forwarding: The Best Thing You’ve Never Heard Of
Josh Frantz

Threat Research
Charting the Forthcoming PHPocalypse in 2019
boB Rudis

Products and Tools
Metasploit Wrapup 12/14/18
Shelby Pace

Threat Research
Securing Buckets with Amazon S3 Block Public Access
Rapid7

Exposure Management
Metasploit Wrapup 12/7/18
Brendan Watters

Products and Tools
Single-Page Applications: The Journey So Far
Mark Hamill

Security Operations
Seeing Security Scale: Rapid7’s Recap of AWS re:Invent 2018
Jay Brewer

Exposure Management
Did You Remediate That? New InsightVM Executive Report Provides Key Details on Team Progress
Alfred Chung
Products and Tools
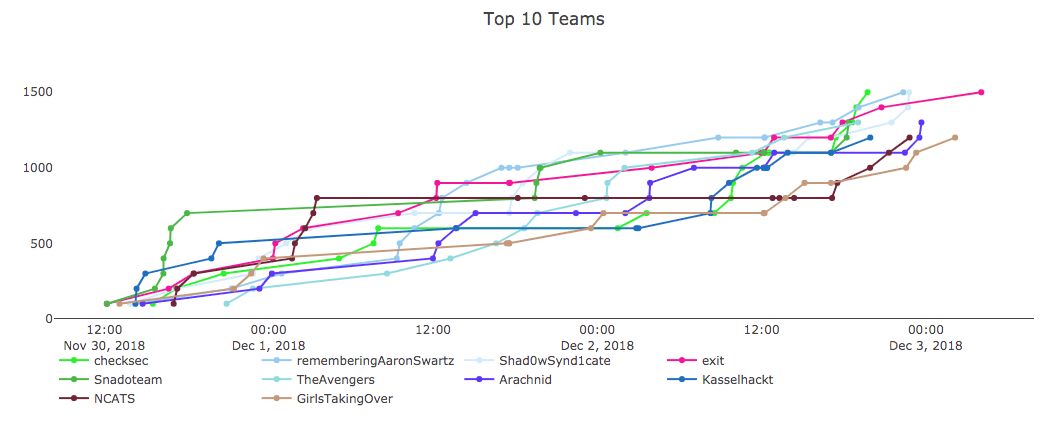
Congrats to the 2018 Metasploit Community CTF Winners
Caitlin Condon
Products and Tools
Metasploit Wrapup 11/30/18
Adam Cammack

Detection and Response
Automation: The Ultimate Enabler for Threat Detection and Response
Eric Sun

Cloud and Devops Security
Deploying Kubernetes Across Multiple Clouds
David Mundy

Threat Research
How Retailers Can Protect Against Magecart This Black Friday and Holiday Season
boB Rudis

Products and Tools
Rolling with Your Logs, Part 3: Using Regex to Expand Your Search Options
Teresa Copple

Products and Tools
Metasploit Wrapup 11/16/18
Matthew Kienow

Products and Tools
5 Tips For Monitoring Network Traffic on Your Network
Rapid7
![[Q&A] Why Every Threat Detection Strategy Needs User Behavior Analytics](/_next/image/?url=%2Fblog-post-image-placeholder.webp&w=1920&q=75)
Detection and Response
[Q&A] Why Every Threat Detection Strategy Needs User Behavior Analytics
Christie Ott

Detection and Response
Rolling with Your Logs, Part 2: Advanced Mode Searches
Teresa Copple