This post is the third in a series, 12 Days of HaXmas, where we take a look at some of more notable advancements in the Metasploit Framework over the course of 2013.
Over the last quarter of 2013, we here in the Democratic Freehold of Metasploit found that we needed to modernize our flagship remote access toolkit (RAT), Meterpreter. That started with cleaving Meterpreter out of the main Metasploit repository and setting it up with its own repository, and then bringing in a dedicated Meterpreter hacker, the indomitable OJ TheColonial Reeves. We couldn't be happier with the results so far.
OJ has kindly written up an extensive report of what all he's worked on with Meterpreter and post-exploitation on Windows hosts over on his blog. I encourage you to head on over there and read his 3 Months of Meterpreter. For bullet points, the TL;DR is:
- A Sane Build Environment
The biggest complaint we used to get about Meterpreter is the pain and suffering one had to go through just to build the darn thing. OJ has reworked all that from soup to nuts, and now Meterpreter builds cleanly and easily using Microsoft Visual Studio Express. If this is your complaint as well, please take a look at the README and amaze at the single 'make' command to kick things off.
- Rock Solid Stability
Sometimes, Meterpreter would crash out on the target, often for mysterious reasons. No longer! OJ tackled pretty much all of the outstanding bugs having to do with Meterpreter stability, and it's better than ever now.
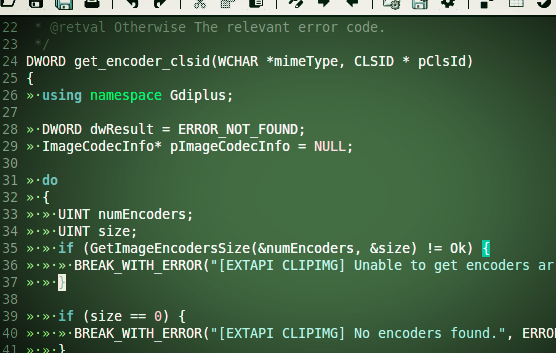
- Securification
Metasploit bread-and-butter exploits tend to be classic stack buffer overflows... so after a code audit, we've patched up all the obvious paths to remote code execution with Meterpreter. While we haven't proven exploitability with the old Meterpreter, we're pretty confident today that you won't get your sessions jacked out from under you by a rival pen-tester. Note, if you're able to successfully subvert a Meterpreter installation, we'd sure appreciate a Metasploit module proving it...
- Enhanced Local Exploits
We've moved the KiTrap0D exploit out of the path for 'getsystem', and promoted it to a proper local exploit for privilege escalation; this has the result of making 'getsystem' procedures a lot more stable in the usual cases, leaving it to the penetration tester to decide if she wants to explore additional avenues of escalating to system privileges. Thanks to the submodule-ing of Stephen Fewer's ReflectiveDLLInjection strategy, we've also refactored the ppr_flatten_rec exploit to be a lot more reliable, as well.
- Bunches of New Features
Along the way with making existing Meterpreter functionality more reliable and easier to use, we've added two heaping handfuls of new functionality; better IPv6 support, refreshed Incognito and mimikatz implementations, more robust environment variable enumeration, a new "Extended API" extension (which incidentally provides a nice roadmap on how to write Meterpreter extensions in general), a framework for interrogating ADSI, and so much more.
- Readable Documentation
Finally, Meterpreter ships with inline, automatically generated documentation using Doxygen, a pretty standard syntax for annotation-based docs. Since you can easily generate the latest docs locally, you no longer have to rely on (or get mislead by) outdated API docs when hacking on Meterpreter.
Again, there's tons of details on all this in OJ's post, so if this kind of thing excites you, feel free to roll up your sleeves and dive into Meterpreter's guts. Payload integration in general is kind of what puts the "meta" in Metasploit -- having all this available to exploit developers and penetration testers should make security R&D move long much faster and cleaner, and get you from proof-of-concept to functional shells in real world situations with less time and effort.
Happy haXmas!