Integrating InsightVM or Nexpose (Rapid7's vulnerability management solutions) with Metasploit (our penetration testing solution) is a lot like Cupid playing “matchmaker” with vulnerabilities and exploit modules. When a vulnerability scan is imported into Metasploit, many things happen under the hood, outside of generating host, service, and vulnerability data in your workspace. In much the same way that Cupid takes into account the qualities of the individuals he is matchmaking, when a host's service is found to have a vulnerability, Metasploit will check its ever growing store of modules for one that can potentially be run against the host's vulnerabilities. This is referred to as an Automatic Exploitation Match. Match generation takes into account not only the vulnerability, but attributes of the host like platform, architecture, etc. This special set of criteria leads to the generation of module matches that have a pretty high chance of successfully being run on the host. Of course, just like with Cupid's matchmaking, given the uncertain nature of networking environments and other factors, the default configuration for a module may not always work without some tweaking of parameters (e.g. using a bind payload for a target that is behind a NAT). Two people may be compatible, but sometimes things just don't work out.
Modules that have been matched with vulnerable hosts can be viewed at a single vulnerability instance's related modules tab. This is all well and good, but vulnerability instances are attributed to a single host, which means the same Vulnerability definition will show up in several Vulnerability instances, one for each host that has an instance of that Vulnerability. When dealing with a non-trivial environment containing several hosts, the table of Vulnerabilities quickly explodes in number, becoming difficult to manage and make sense of. This can be similar to the feeling of being overwhelmed by the plenty of fish that are out there in the sea: a lot of noise, when you really just want to know which are even compatible. It is difficult to determine which vulnerability instances actually have modules that can be used against them, requiring iteratively clicking on each Vulnerability instance's related modules tab to see. If only there was a way to view the results of matchmaking modules with vulnerabilities in an intuitive and productive way…
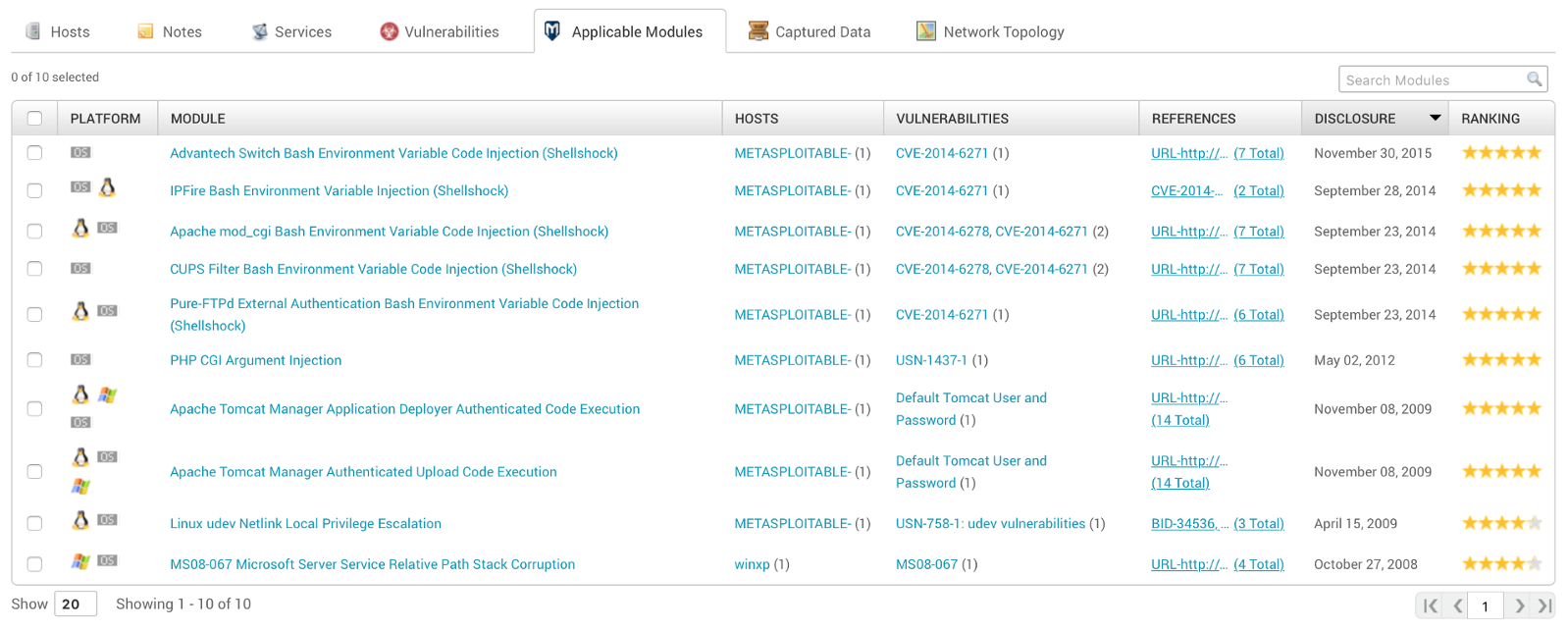
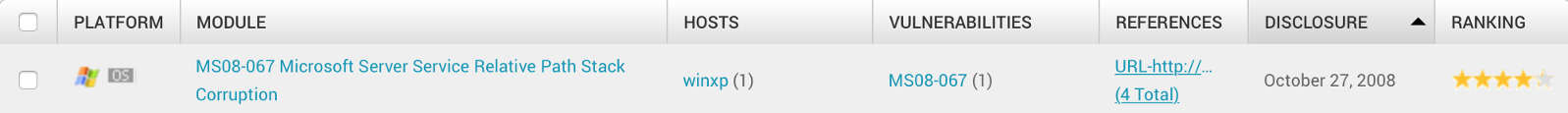
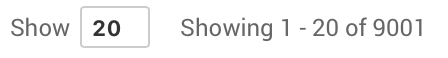
With the latest release of Metasploit Pro, we introduce the Applicable Modules tab to the workspace analysis view. This view aims to solve the problem of making sense of a massive list of vulnerabilities. Similar to the way a single vulnerability page has a related modules tab, the Applicable Modules tab in workspace analysis aggregates a list of related modules across all vulnerable instances in your workspace. Along with each module entry in this list, relevant metadata related to the module are also quickly viewable, including the affected hosts and associated vulnerabilities. Hover over the various metadata entities to view additional information, such as services on a host or a full vulnerability description, without having to navigate away from the page. You can click on a module to autoconfigure a module run with all affected hosts filled in as targets. This list defaults to being sorted by module release date, so you can quickly see the latest hotness Metasploit has to offer that can target hosts in your environment. The Applicable Modules table densely packs and associates host, vuln, and module-matching information that is relevant to your workspace into a single view, allowing for deeper insight at a glance.
Metasploit generates quite a bit of insightful data regarding the relationship of vulnerabilities found in your workspace and their exploitability via modules. The Applicable Modules workspace analysis tab intuitively presents the relevant information relating hosts, vulnerabilities, and the exploit modules within Metasploit by listing modules that can target assets in your environment. Be sure to also catch the other productivity enhancements included in the latest release: “Single Host's modules view as a searchable/sortable table” and “Pushing InsightVM and Nexpose Exceptions and Validations from Task Chains”. All is fair in <3 and Infosec. Happy exploiting, friends!



