This is part two of our blog series on testing SMB security with Metasploit Pro. In the previous post, we explained how to use Metasploit Pro’s Task Chains feature to audit SMB passwords automatically. Read it here if you haven’t already.
In today’s blog post, we will talk about how to use a custom resource script in a Task Chain to automatically find some publicly-known high-profile vulnerabilities in SMB. Publicly-known exploits are something no one should underestimate: most network breaches arise from compromise due to stolen passwords or via publicly-known exploits (or a combination of the two).
SMB has its share of high-profile publicly-known exploits (perhaps even more than its share), and they give you SYSTEM access, which is the highest privilege you can get on a Windows system. Our favorites include: MS08-067, and the recent MS17-010 brought to you by the Shadow Brokers. For this demonstration, we will use Metasploit Pro’s Task Chains to find these two vulnerabilities and validate automatically.
Uploading a Resource Script to Metasploit Pro
Before we set up a Task Chain, we need to upload our custom resource scripts to Pro. There are two scripts available for this Task Chain:
● smb_checks.rc: This resource script allows you to find SMB services that are on SMBv1 and are vulnerable to MS08-067 and MS17-010.
● smb_validate.rc: This resource script is optional. It allows you to fire MS08-067 and MS17-010 exploits against the vulnerable SMB services to prove exploitability.
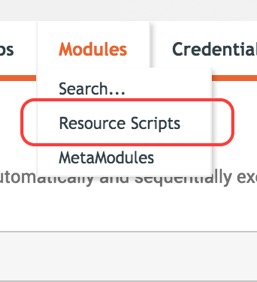
To import a resource script, first go to your workspace and click on the Modules tab. You will see the Resource Scripts option like so:
In the Resource Scripts view, click on the Upload button:
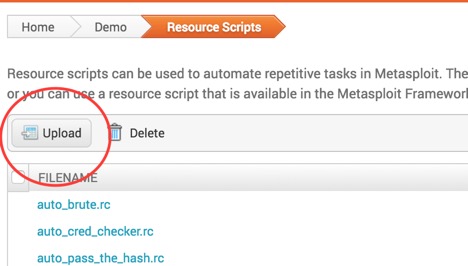
Go ahead and upload the custom resource scripts you just downloaded. The new scripts should appear on the list, and now you are ready to move on to creating the Task Chain.
Getting Started with Task Chains
To set up a task chain for these two SMB vulnerabilities, follow these steps:
- Do an Nmap scan and find all the SMB services that are up and running at the time.
- Launch our custom resource scripts to test these SMB services.
- Generate a report about it.
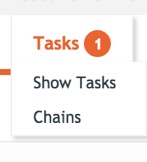
The Task Chains feature can be found in Pro’s workspace. It’s the last button next to Exports:

If you click on that, the menu should expand. The Chains option is what you want:
Task 1: Set up the NMAP Scan
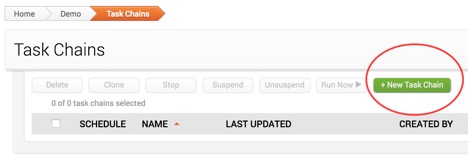
So now you should be looking at the Task Chains view, let’s go ahead and create the vulnerability audit for SMB. First, click on green New Task Chain button:
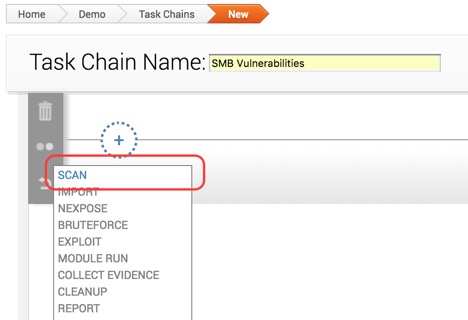
Next, pick a name for your task chain. In my case, I’ll call it “SMB Vulnerabilities”. And then let’s click on the plus sign to assign the first task of the chain, and choose Scan, like this:
The Scan task has quite a lot of settings you can configure, but it is recommended that you at least do the following:
- Set the address range you want to scan.
- Set the custom TCP port range to: 445.
- Uncheck all the discovery settings to save time.
And we’re done configuring this task. Let’s move on to the next one.
Task 2: Set up the SMB Check Resource Script Task
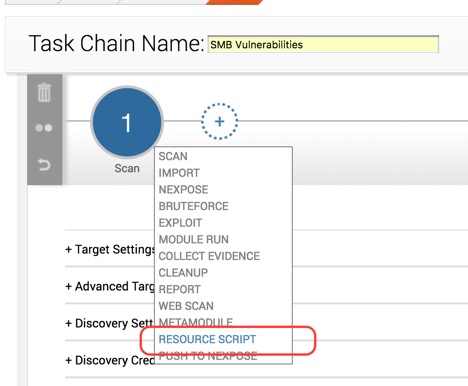
To create the next task, click on the plus sign again, and choose Resource Scripts this time:
The Resource Script option will take you a list of all the resource scripts you could use. Choose smb_checks.rc that you uploaded earlier:
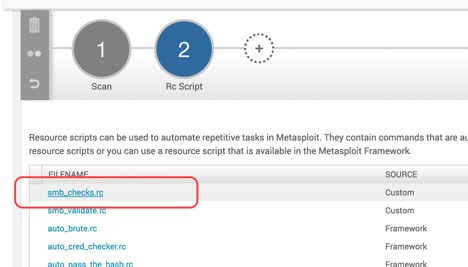
When you choose a script, you will see that you can pass some parameters and view the source code of the script. For smb_checks.rb, there are no parameters to set, and the source code is view-only—you cannot edit it.
At this point, you are set on task 2. Let’s move on to task 3.
Task 3: Set up the SMB Validation Resource Script Task
This step is similar to the previous one, except we are using a different resource script, and it’s actually optional. You only need to create this task if you want to validate the SMB vulnerability findings found by the previous resource script.
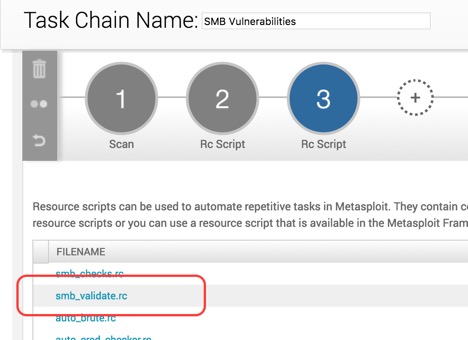
To add this task to the chain, click on the plus sign again, and choose Resource Scripts.
Next, choose smb_validate.rc:
To use smb_validate, you will actually need to set the LHOST (listening host) parameter like the following screenshot. LHOST in this context is for the exploit module’s payload, as well as the handler.
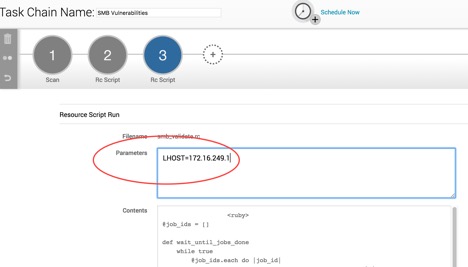
Note: To figure out the LHOST option on Linux and OS X, open the terminal and type ifconfig to find it. If there are multiple IPs, pick the one that’s in the same network as the vulnerable targets. If you are on Windows, you can use ipconfig on command prompt to find this type of information.
And we are done with this step; let’s move on to the last task.
Task 4: Generating a Vulnerability Report
Our final assignment in the chain is to create a validation report. The report will contain information about the vulnerabilities and hosts that got exploited.
The ideal report type in this case should be Compromised and Vulnerable Hosts. The report options should be pretty self-explanatory, so we can leave it to you to decide.
The Report function also has a handy email feature. If you wish to send the report to other people on your team automatically, go ahead and check that as well.
Scheduling the Task Chain
The last step we need to do is actually set a timer for the task chain. If you scroll up on the page, you should see the Schedule Now button:

Click on this icon and you should see a pop-up like the following, which allows you to set up the time:
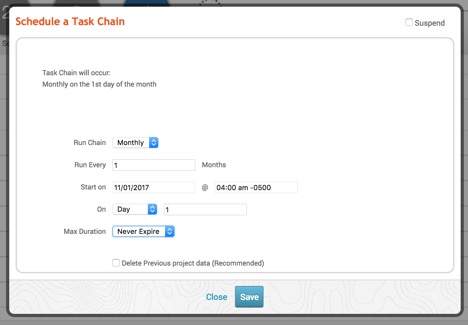
Exactly how often this should kick in depends on your needs. For example:
- If there are other people on the network using these services, pick the time with the least traffic.
- Number of hosts: the more hosts there are, the longer the task takes to finish.
- Network speed
Saving the Task Chain
And finally, we are done configuring the task chain to test SMB vulnerabilities, so let’s save it! The Save button is located here:

After the task chain is saved, it’s ready to go! Now you have an automated process that will search for vulnerable SMB services and (optionally) exploit them, while you can stay productive doing something else.
The SMB protocol provides a great way for us to share information across our network; many of us rely on this to do our jobs all the time without even realizing it. It’s also exactly because it has such a huge user base—and it only takes one shell to lead to a full network compromise for the attacker—that it is difficult to protect. You need some kind of automated process to always be on the lookout for weakness, and Metasploit Pro’s Task Chains feature is perfect for something that needs to be done repeatedly in order to save time and money.
If you are a current Metasploit Pro user, we hope you enjoyed today’s blog post on how to use Task Chains to automate testing SMB vulnerabilities. For those who have never tried Pro, obviously you are missing out. To obtain a trial version of Metasploit Pro, please sign up here.
Want to know whenever Metasploit content is posted? Add us to your RSS feed.
Related blog posts

Products and Tools
Weekly Metasploit Update: Apache ActiveMQ RCE, Gogs Rebase RCE, and Windows Kernel Pointer Enum
Brendan Watters

Products and Tools
Metasploit Wrap Up 05/29/2026
Spencer McIntyre

Products and Tools
Metasploit Wrap Up 05/22/2026
Martin Sutovsky

Products and Tools
Metasploit Wrap-Up 05/15/2026
Martin Sutovsky
