Series co-written with Jeremiah Dewey, Rapid7 Director of Incident Response.
Part 2: Reviewing The Incident Response Plan
In our first part of this series, we covered key considerations when drafting an incident response (IR) plan. Today, let’s cover what plan review looks like and the best way to get buy-in from key stakeholders in the company. Collaborative study helps ensure that all involved parties—including those not in security—understand their roles over the course of an incident.
Prepare Each Player for Incident Response
An effective incident response plan should take into account the organization’s accepted level of risk and prepare for the most probable threats your company and industry will face. For example, if the security function isn’t getting the full attention it deserves, the incident response plan should reveal those weaknesses. If that is the case, priority should be focused on stopping opportunistic, non-targeted threats, as there may be limited capability to detect a targeted attack.

Exhibit A: Preventative controls against a well-funded attacker.
Once the plan provides context on probable attacks, take the time to define roles. All listed personnel should understand what steps to take and where they stand in the process. This includes communication guidelines. If there is general panic and a constant need for updates during an incident, this will frustrate and ultimately slow down the efficacy of your team.
Also, see if anyone hasn’t been included in the plan and add accordingly. Talk with executives, stakeholders, and non-security people and ask, "Are you able to help with these responses? What needs to be done?” When reviewing the IR plan, be sure to update any drafted public relations (PR) content to reflect the latest changes.
Review the Roles and Protocols in Your Incident Response Plan
Ensure that if there is a suspected incident, departments know how to report it, whether it’s via phone, email, communications apps, or in person. And if the suspected incident is on a collaboration system (i.e., email), it's best NOT to use that system to report it.
The security team should have a general incident triage workflow in order to build context and eliminate false positives; this helps stakeholders understand which items merit higher escalation. From there, all other cross-functional stakeholders should have clear processes to aid with response.
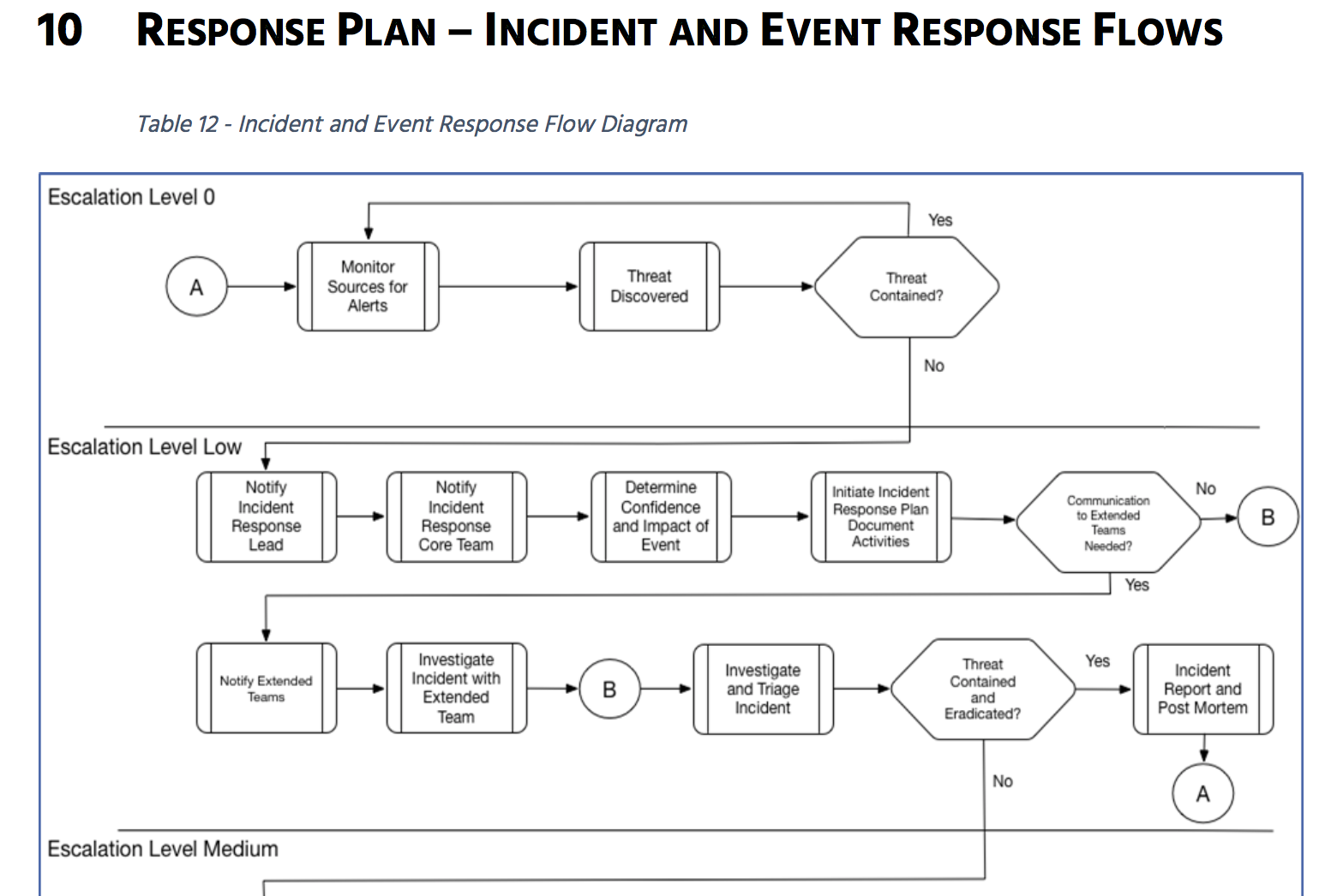
Next, all players should review the protocols for communications during an incident. For example, alternate communication channels should be mapped out when there’s potential that primary channels are compromised, thus protecting remediation plans from the prying eyes of attackers. Communication should be on a need-to-know basis, avoiding unnecessary chatter.
Review for Flaws; Plan for Adjustments
This is the time to really evaluate your ability to detect malicious behavior. Our recommendation is to map your detection capabilities to the attack chain—make a diagram mapping out the steps required to breach your organization. For example, if a remote worker’s endpoint or cloud service credentials are compromised, how might an attacker then gain access to critical internal network assets?
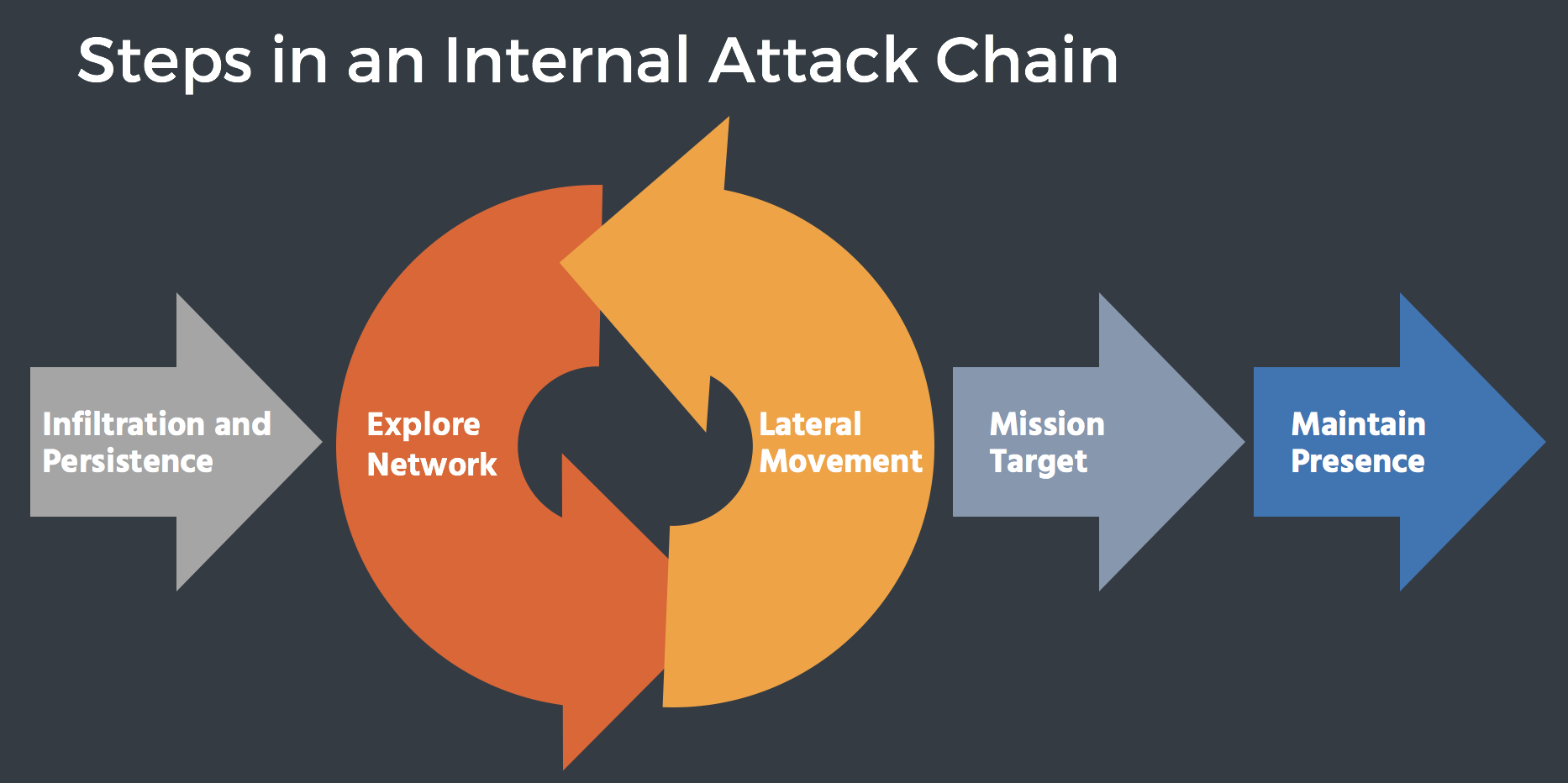
We have found that teams largely have detection coverage gaps early in the attack chain. This includes detections for network scans, the use of stolen credentials, and lateral movement—attackers using privileged credentials to move elsewhere on the internal network. See how our incident detection and response solution can help with thi.
The incident response plan should be detailed enough to cover the most frequently encountered incident types, yet flexible enough to allow for changes to meet evolving threats. Reviewing and adjusting the plan to accommodate these evolutions will help close any gaps in containing an attack.
In the meantime, also review for gaps in your response capabilities. Teams will become overwhelmed and side-tracked if they cannot effectively investigate an incident when confronted with one.
When to Review Your Incident Response Plan
To get the most out of reviews, define regular intervals for them. While quarterly is ideal, yearly is mandated by compliance standards that require explicit response plans and annual certifications.
Having an incident response plan puts you way ahead of the curve. In order to make the most of this effort, you have to put the plan to the test. Just as all warriors must spar to gain power—or at least undergo a training montage—successful response demands mental preparation and muscle memory. In the next post, we’ll cover best practices for putting your incident response plan to the test, including attack simulations and tabletop exercises. Stay tuned, and please share your own findings and suggestions below.
Keep going with Part 3: Putting the Incident Response Plan to the Test here.
Article Tags
Related blog posts

Detection and Response
Zero Chaos: Scaling Detection Engineering at the Speed of Software, with Detection As Code
Zachary Zeid, James Gallahan
Threat Research
Rapid7 Detection Coverage for Iran-Linked Cyber Activity
Rapid7 Labs

Detection and Response
Alert Fatigue Isn’t Going Away. Here’s How Modern SOCs Are Fighting Back
Rapid7

Detection and Response
Rapid7: 7 years of recognition in Gartner® Magic Quadrant™ for SIEM
Cindy Stanton