Posts by Eric Sun

Detection and Response
SIEM Security Tools: Six Expensive Misconceptions
Eric Sun

Detection and Response
Why the Modern SIEM Is in the Cloud
Eric Sun
Detection and Response
Securing Your Cloud Environments with InsightIDR, Part 2: Amazon Web Services (AWS)
Eric Sun

Threat Research
Forrester Tech Tide for Detection and Response: Is 2019 the Year of Convergence?
Eric Sun

Detection and Response
Automation: The Ultimate Enabler for Threat Detection and Response
Eric Sun

Exposure Management
Address the NAIC Insurance Data Security Model Law
Eric Sun

Detection and Response
Phishing Attacks Duping Your Users? Here’s a Better Anti-Phishing Strategy.
Eric Sun
Detection and Response
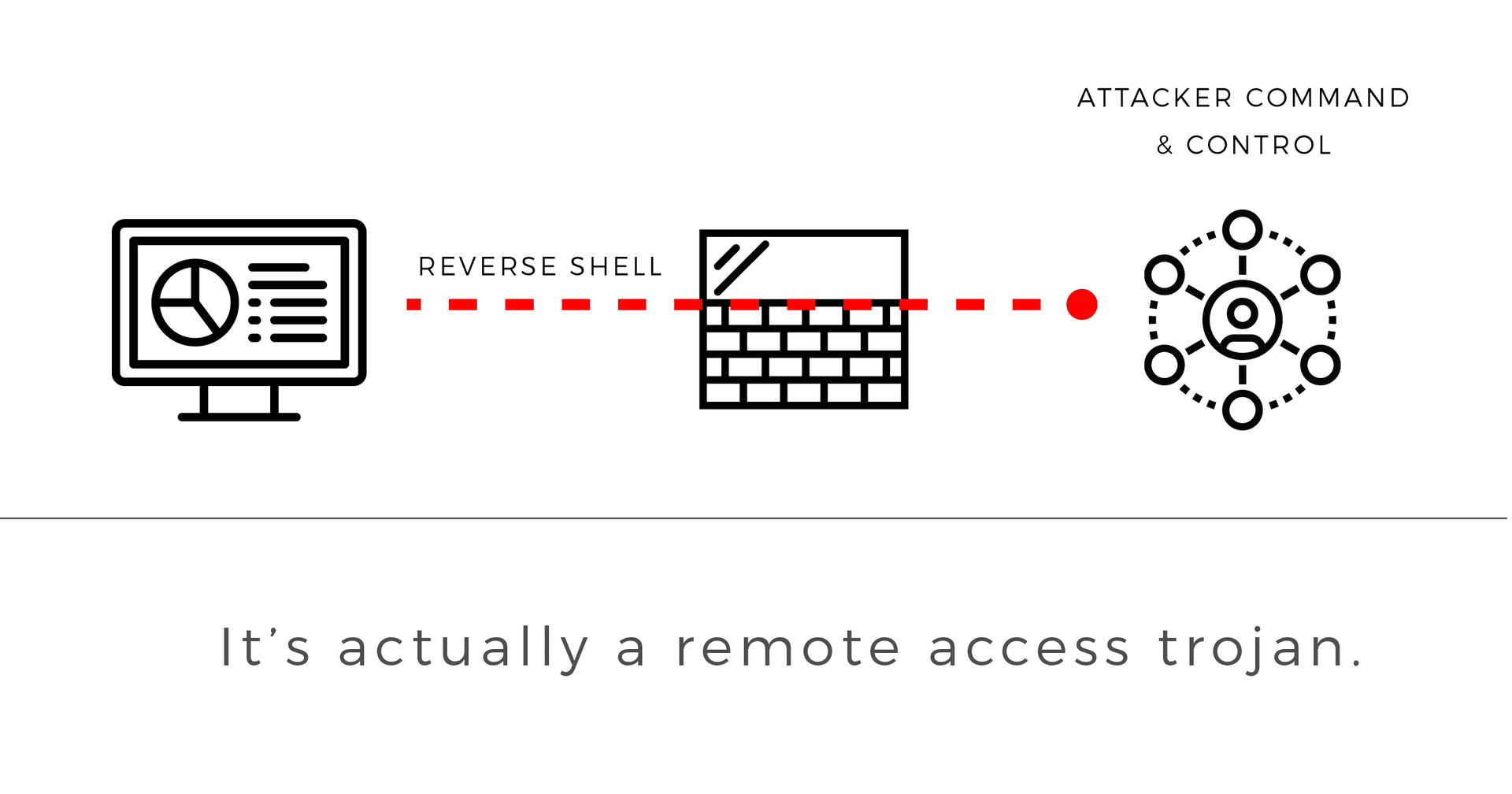
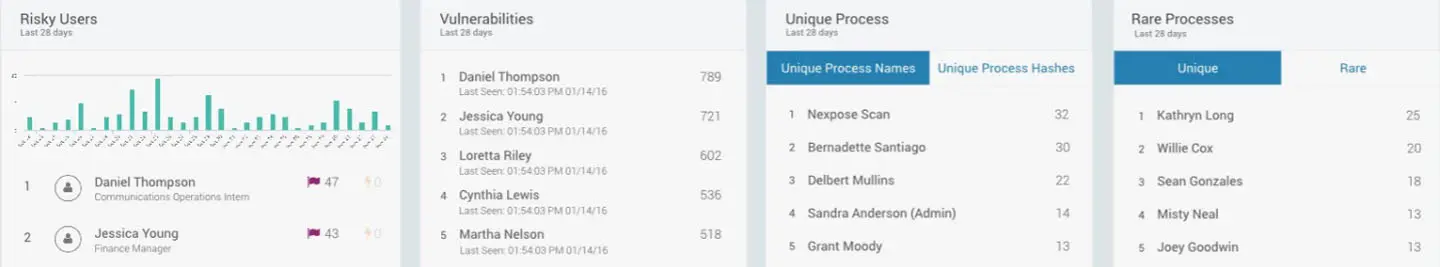
Attacker Behavior Analytics: How SIEM Detects Unknown Threats
Eric Sun
Products and Tools
Why Managed Detection and Response Zeroes In On the Endpoint
Eric Sun

Detection and Response
Prepare for Battle: Let’s Build an Incident Response Plan (Part 4)
Eric Sun

Detection and Response
Prepare for Battle: Let’s Build an Incident Response Plan (Part 3)
Eric Sun

Detection and Response
Prepare for Battle: Let’s Build an Incident Response Plan (Part 2)
Eric Sun

Detection and Response
2017 Gartner Magic Quadrant for SIEM: Rapid7 Named a Visionary
Eric Sun

Detection and Response
Prepare for Battle: Let’s Build an Incident Response Plan (Part 1)
Eric Sun

Detection and Response
InsightIDR Monitors Win, Linux & Mac Endpoints
Eric Sun
Detection and Response
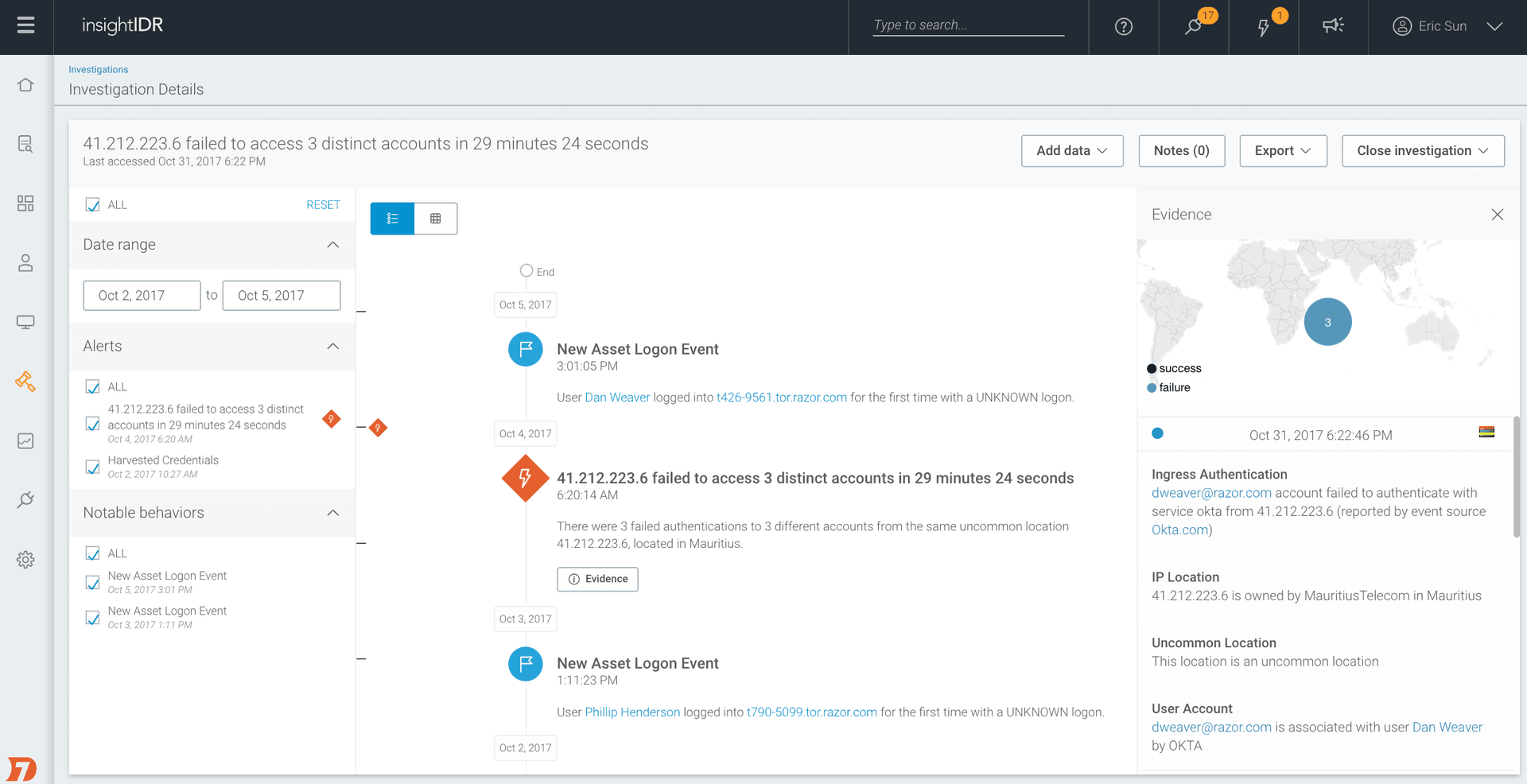
Faster Investigations, Closer Teamwork: InsightIDR Enhancements
Eric Sun

Detection and Response
InsightIDR Now Supports Multi-Factor Auth and Data Archiving
Eric Sun

Detection and Response
Want to Try InsightIDR in Your Environment? Free Trial Now Available
Eric Sun
Detection and Response
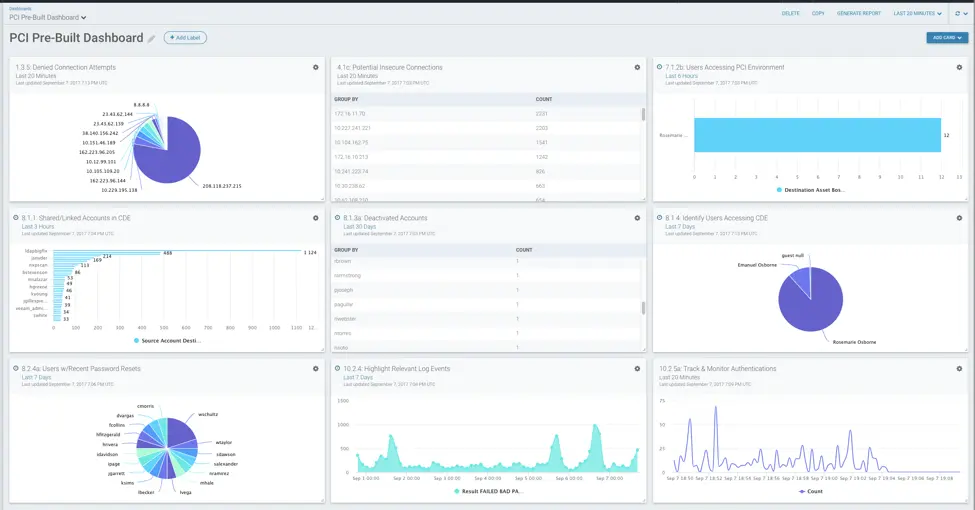
PCI DSS Dashboards in InsightIDR: New Pre-Built Cards
Eric Sun
Rapid7 Blog
How Do You Identify Zero-Days and Fileless Malware? Download (the) RAM.
Eric Sun
Detection and Response
SIEM Tools Aren't Dead, They're Just Shedding Some Extra Pounds
Eric Sun