Adding some named pipes to everyone's favorite series of tubes
UserExistsError already added 64-bit named pipe payloads, and this week, we got an extra-special upgrade: now Metasploit has 32-bit named pipe payloads! It may feel wrong not setting a port, but connecting to existing network resources feels so right!

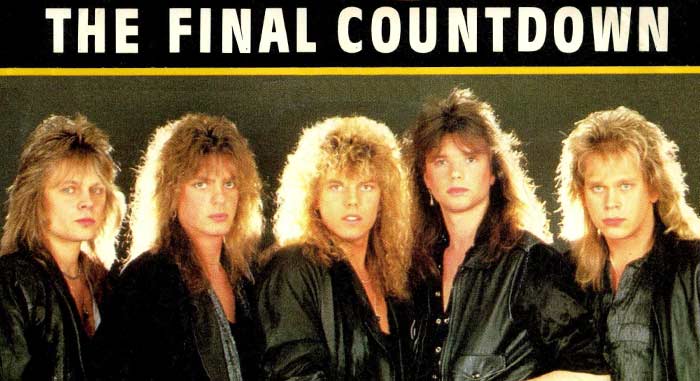
It is the Final Countdown for GSoC!
The final deadline for Google Summer of Code applicants is March 27th, so get your applications in now! We are honored to be a part of the program and thrilled to have so much interest, but we are always happy to see more. Coding starts May 14th! Review our list of project ideas, what we'd like to see in your proposal, and then, apply directly with Google Summer of Code.
Trippin' on TLS
Last Wrapup, we trumpeted the release of Metasploitable3 as seen on our CTF. It turns out that there were some changes in crypto since then, and some people who tried to play at home got errors about creating a secure channel. Thanks to our super-awesome community, that problem has been solved. So, in the words of our communal childhood: Play on!

More Crypto!
In a response to the Marvel argument that Infinity War is the greatest crossover ever, our very own Brent announced the release of LibreSSL 2.7.0 this week. LibreSSL now supports more OpenSSL APIs.
Love/Hate Relationship?
Do you love Metasploit but hate Ruby? Is whitespace more your thing? Do you believe that what makes a function a function is parentheses, and do you think the next great war will be fought over tabs vs. spaces? Well, good news! Our own kind-of-n00b jrobles released a manual for writing Metasploit Python modules!

New Modules
Auxiliary and post modules (1 new)
- HP iLO 4 1.00-2.50 Authentication Bypass Administrator Account Creation by Fabien Perigaud exploits CVE-2017-12542, an authentication bypass, to insert a new administration account on vulnerable HP iLO4 web interfaces.
Recent Improvements
Our very own wvu got so angry at the time it took to get an msfvenom help menu, he snapped and rewrote the ruby loader changed the dependencies so that you can get a little help from your friends here at Metasploit without waiting as long.

Get it
As always, you can update to the latest Metasploit Framework with msfupdate and you can get more details on the changes since the last blog post from GitHub:
To install fresh, check out the open-source-only Nightly Installers, or the binary installers which also include the commercial editions.
PLEASE NOTE that these installers, and Metasploit Framework versions included in distros such as Kali, Parrot, etc., are based off the stable Metasploit 4 branch. If you'd like to try out the newer things going into Metasploit 5, that work is available in the master branch of the Metasploit Framework repo on GitHub.





