After three days of fierce competition, we have the winners of this year's Metasploit community CTF. We've included some high-level stats from the game below; check out the scoreboard. If you played the CTF this weekend and want to let the Metasploit team know which challenges you found exhilarating, interesting, or infuriating (in a good way, of course).
Congratulations to everyone who teamed up with community members, learned something new, or captured flags. The collaboration we saw on Slack and beyond gave us, as they say, all the feels.
| Standing | Team |
|---|---|
| First place | checksec |
| Second place | rememberingAaronSwartz |
| Third place | Shad0wSynd1cate |
We'll be in touch with winners shortly to arrange prize delivery. Big thanks to Ixia and CTFd for providing technology that helped power the game, and thanks to our friends at Hack The Box for chipping in some sweet prizes!
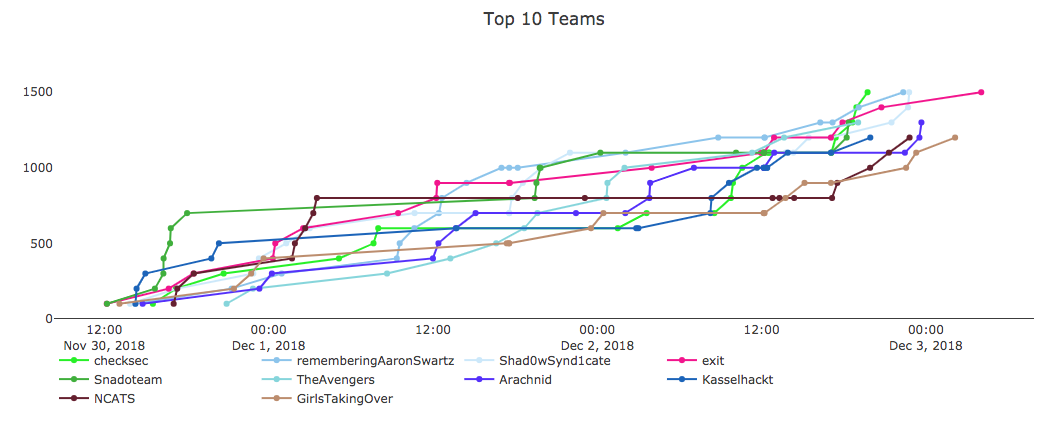
- Nearly 600 teams logged in and played over the course of the game.
- Four teams captured all 15 flags: checksec, rememberingAaronSwartz, Shad0wSynd1cate, and exit. There were a few truly epic challenges; props to everyone who persevered in deconstructing the house of cards the Metasploit engineering team built for the community.
- 214 teams made it onto the scoreboard. Congrats to all of you who captured your first-ever flag in this year's game!
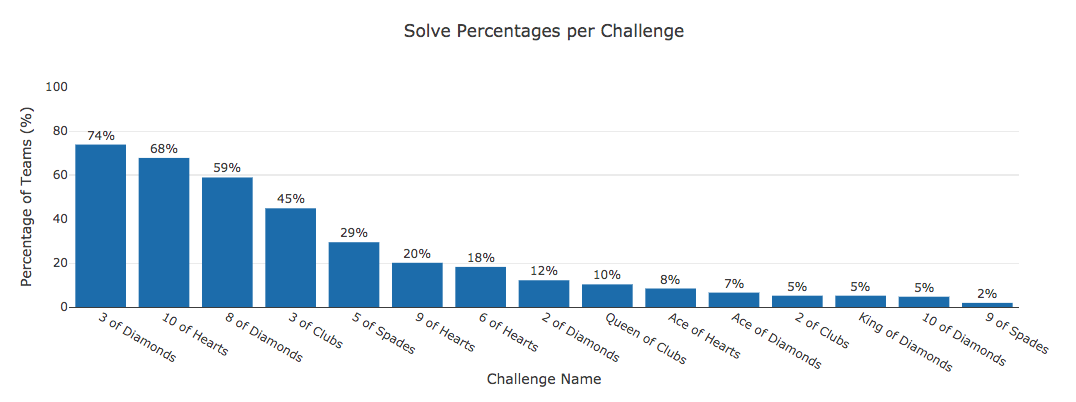
- 3 of Diamonds had the highest number of solves (158), followed closely by 10 of Hearts (145).
- 9 of Spades was our least-solved challenge (a joint sinn3r and shellfail production).
- 786 correct MD5 hashes were submitted. We got 3,431 incorrect submissions. That 8 of Trolls was brutal, we know.
As in previous years, it's possible that the hacker community will come out with detailed write-ups on how they solved some or all of this year's challenges. We'll list these here as they roll in. EDIT: See list at end of post.
Cheers to everyone who made the 2018 competition a memorable affair, not least of all our diabolical yet lovable gamemakers: sinn3r, wvu, space, tychos moose, surefire, shellfail, juggernot, erinbleiweiss, pebarry, and the inimitable busterb. May your shells be merry and bright.
Write-ups
Thanks to B0rn2r00t and the rest of the Metasploit Slack community for getting these together!
- https://www.secjuice.com/metasploit-ctf/
- https://www.securifera.com/blog/2018/12/10/metasploit-community-ctf-2018-writeup/
- https://www.rorroh.net/post/metasploit-ctf-2-diamonds.html
- https://github.com/ant0/ctf_writeups/tree/master/2018_metasploit_community_ctf
- https://medium.com/alertot/metasploit-community-ctf-2018-writeup-23df21a68bc8
- https://ethicalhackers.club/metasploit-community-ctf-2018-2-of-diamonds-write-up/
- https://pentest.com.tr/blog/MetasploitCTF-Write-Up-English-AkkuS.html
- https://www.sigflag.at/blog/




