This blog is the ninth post in our annual 12 Days of HaXmas series.
Another year, another 701 patched Microsoft vulnerabilities: just a 2% increase from 2017's count of 686. This may be more reflective of Microsoft's bandwidth for fixing vulnerabilities than it is of a consistent number of flaws being discovered, but that's pure speculation.
Speaking of speculation! The year got off to a rollicking start as Microsoft released out-of-band mitigations for the Meltdown and Spectre speculative execution side-channel vulnerabilities late on Jan. 3, due to a developer embargo being lifted earlier than originally planned. Nothing like a Patch Thursday to get the new year going! This also had the notable effect of disabling all security updates for any systems running antivirus software that didn’t set a specific compatibility registry key for several months.
As evidenced by the 26 revisions to Microsoft's guidance page, Meltdown and Spectre continued to haunt Microsoft (and the rest of the industry) throughout much of the year. But it's HaXmas, not Halloween, so let's get on with the 2018 Patch Tuesday roundup.
Overview
By month
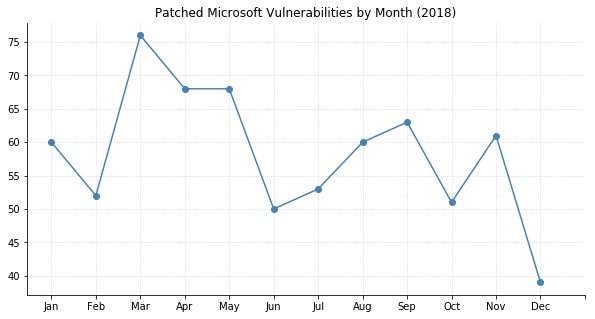
On average, 58 Microsoft vulnerabilities were patched each month. March was the biggest, with 76 vulnerabilities, and December the smallest, with around half that.
By component
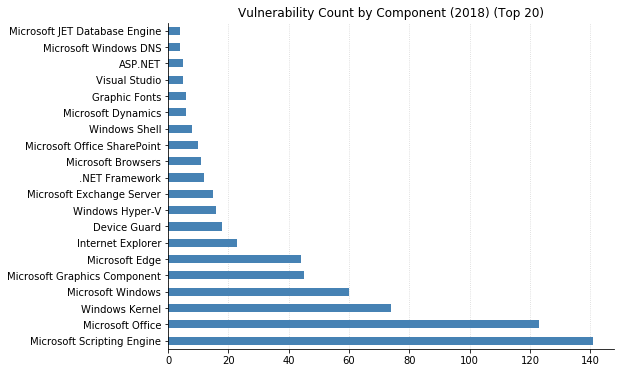
Once again, browser technology dominated in terms of sheer number of CVEs fixed. The Microsoft Scripting Engine alone had more vulnerabilities than any other component, even before considering any IE- or Edge-specific vulnerabilities. We can hope the situation might improve once Edge is based on Chromium, though Google Chrome is no stranger to vulnerabilities itself (to be fair, far fewer are directly classified as code execution).
Microsoft Office came in second place with over 120 separate security flaws patched, followed by more core components such as the Kernel and Microsoft Graphics Component.
By impact
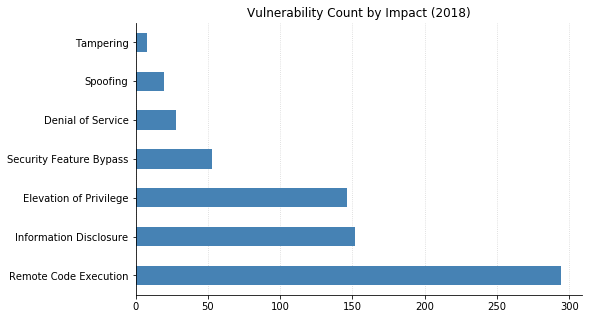
Remote Code Execution (RCE) accounted for 42% of Microsoft's vulnerabilities in 2018, nearly twice the count of the Information Disclosure (22%) and Elevation of Privilege (21%) bugs they fixed. Proportionally, this is down slightly from the 44% that RCE made up in 2017. Information Disclosure is also down from 28%, with Elevation of Privilege making up most of the difference (up from 13%). Also, 179 of the RCEs were considered Critical.
By severity
Microsoft still published a Severity for each CVE, categorized as Low, Moderate, Important, or Critical. Similar to 2017, together the two least severe categories only accounted for 17 (2.5%) of this year’s CVEs. There were 187 vulnerabilities Microsoft rated as Critical in 2018, meaning they could allow code to be executed without any user interaction. The remaining 70% were merely "Important." The Common Vulnerability Scoring System (CVSS), while not perfect, provides a more granular ranking:
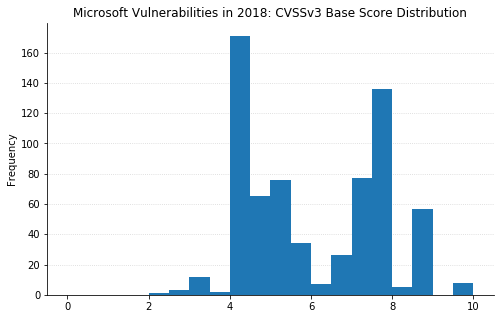
Like last year, there are spikes around the "Moderate" (4) and "High" (7) qualitative boundaries. There are eight vulnerabilities this year with a base score of 9.8, up from three last year:
- CVE-2018-8154 (May) Microsoft Exchange Memory Corruption Vulnerability
- CVE-2018-8327 (July) PowerShell Editor Services Remote Code Execution Vulnerability
- CVE-2018-8319 (July) MSR JavaScript Cryptography Library Security Feature Bypass Vulnerability
- CVE-2018-8273 (August) Microsoft SQL Server Remote Code Execution Vulnerability
- CVE-2018-8302 (August) Microsoft Exchange Memory Corruption Vulnerability
- CVE-2018-8421 (September) .NET Framework Remote Code Execution Vulnerability
- CVE-2018-8500 (October) Scripting Engine Memory Corruption Vulnerability
- CVE-2018-8626 (December) Windows DNS Server Heap Overflow Vulnerability
Most of these are server-side, and although CVE-2018-8500 is a Scripting Engine vulnerability, it seems to have been fixed in ChakraCore before making it into a public release of Edge. However, having a higher score does not mean a vulnerability carries more risk. There are quite a few vulns hovering around the 8.8 mark, and most of these are in Microsoft Office. A user who can be successfully phished and convinced to open a malicious document remains, as ever, one of the most appealing targets for attackers.
A quick note about the charts and statistics above: They only include vulnerabilities where Microsoft itself published the CVE identifier. This excludes the ADV-style advisories used for CVEs that are for other vendors, such as Adobe Flash Player or the speculative execution side channel vulnerabilities.
0-days
More so than a scalar number based on theoretical potential, one thing that elevates a vulnerability’s risk considerably is knowledge that it is already being exploited in the wild. Like the frigid winds of a polar vortex, learning of a new zero-day vulnerability can chill a system administrator to the bone. In 2018, there were 10 Microsoft vulnerabilities with exploitation detected before the patch was made available (for example, this doesn't include the aforementioned speculative execution side-channel vulns, nor the Flash 0-day from earlier this month):
- CVE-2018-0802 (January) Microsoft Office Memory Corruption Vulnerability
- CVE-2018-8120 (May) Win32k Elevation of Privilege Vulnerability
- CVE-2018-8174 (May) Windows VBScript Engine Remote Code Execution Vulnerability
- CVE-2018-8373 (August) Scripting Engine Memory Corruption Vulnerability
- CVE-2018-8414 (August) Windows Shell Remote Code Execution Vulnerability
- CVE-2018-8440 (September) Windows ALPC Elevation of Privilege Vulnerability
- CVE-2018-8453 (October) Win32k Elevation of Privilege Vulnerability
- CVE-2018-8589 (November) Windows Win32k Elevation of Privilege Vulnerability
- CVE-2018-8611 (December) Windows Kernel Elevation of Privilege Vulnerability
- CVE-2018-8653 (December 19th out-of-band) Scripting Engine Memory Corruption Vulnerability
Patches and supersedence
Microsoft referenced a total of 696 unique KB identifiers as fixes in 2018. As new updates come out, they may “supersede” previous fixes for the a product or component. This means only the newest patch in a supersedence chain needs to be installed. Here’s a visualization of 2018’s KBs, linked to the KBs they supersede (if any) and colored by the component being patched.
Just a bit of eye candy to ring in the New Year. Happy HaXmas! And may all your patches install cleanly.