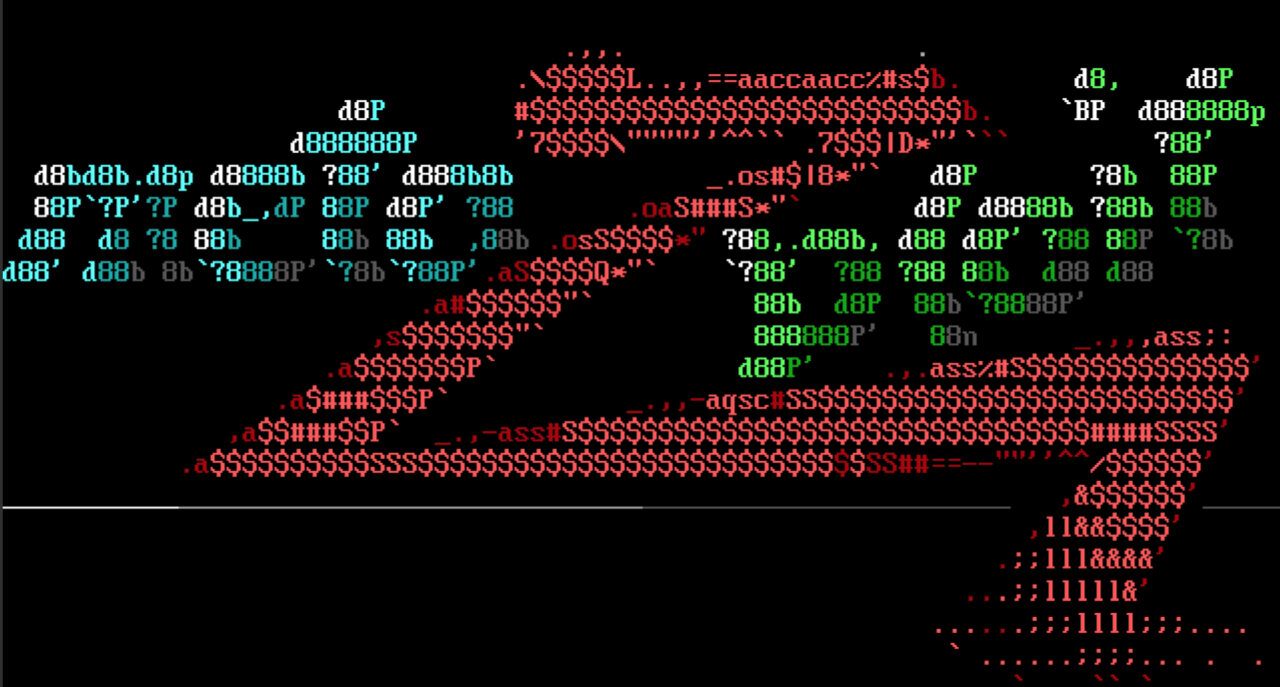
Management delegation of shells
Onur ER contributed the Ajenti auth username command injection exploit module for the vulnerability Jeremy Brown discovered and published a PoC for on 2019-10-13 (EDB 47497) against Ajenti version 2.1.31. Ajenti is an open-source web-based server admin panel written in Python and JS. The application allows admins to remotely perform a variety of server management tasks. The exploit/unix/webapp/ajenti_auth_username_cmd_injection module
achieves arbitrary command execution through the username field of a POST body to the api/core/auth URL.
WordPress plugin giveth
The WordPress Plainview Activity Monitor RCE module by Leo LE BOUTER exploits a vulnerability in the Plainview Activity Monitor plugin. The vulnerability was discovered by LydA(c)ric LEFEBVRE last year (CVE-2018-15877) and achieves authenticated command injection allowing the attacker to execute commands with the same permissions as the web server. The command is injected via the ip field of a POST body to the wp-admin/admin.php URL with a query string of ?page=plainview_activity_monitor&tab=activity_tools to reach the code inside of the plugin module activities_overview.php. The exploits/unix/webapp/wp_plainview_activity_monitor_rce module was tested against WordPress version 4.6 with Plainview Activity Monitor version 20161228 which was confirmed vulnerable, and it is possible that prior versions are vulnerable as well. Remember to keep those WordPress plugins updated!
Document all the things modules
Many thanks to Kenneth LaCroix for taking the time to contribute a total of 12 auxiliary module docs in a move to overthrow h00die’s documentation king status. There are direct links to the contributions in the “Enhancements and features” section below. If you enjoy nostalgic adventures through the Metasploit repo and are looking for a simple first commit consider h00die’s newbie-friendly call for the community to add Auxiliary Scanner Docs.
New modules (3)
- Ajenti auth username Command Injection by Jeremy Brown and Onur ER
- Wordpress Plainview Activity Monitor RCE by Leo LE BOUTER and LydA(c)ric LEFEBVRE, which exploits CVE-2018-15877
- Test SSH Github Access by Wyatt Dahlenburg (@wdahlenb)
Enhancements and features
- PR #12475 by Matteo Cantoni adds options for delay and jitter to the auxiliary/scanner/http/brute_dirs module.
- PR #12509 by acammack-r7 enhances the module run RPC API to include vulnerability check results in the output.
- PR #12607 and PR #12622 by Kenneth LaCroix add a total of 12 new module docs for a variety of auxiliary modules.
- PR #12613 by Jeffrey Martin updates various consumers of the database API to use the correct :workspace key when specifying the workspace for data imports.
- PR #12631 by Jeffrey Martin sets the database workspace inside the handler when the database is active.
- PR #12637 by Jeffrey Martin sets the database workspace inside the RPC web console initialization.
- PR #12646 by bcoles adds reliability and stability information to exploits/windows/smb/ms04_007_killbill.
- PR #12656 by bcoles adds reliability and stability information to exploits/windows/smb/ms06_040_netapi.rb.
Bugs fixed
- PR #12625 by wvu updates print method calls in the DOUBLEPULSAR exploit check method.
- PR #12627 by dwelch-r7 fixes a bug that caused aux modules to incorrectly report that they support check functionality. This bug was only apparent in aux modules that used the scanner mixin.
- PR #12644 by h00die fixes a auxiliary/dos/windows/ftp/iis75_ftpd_iac_bof crash when the returned banner is nil.
- PR #12655 by bcoles modifies automatic TLS certificate generation logic to not occasionally generate certificates that have already expired.
- PR #12657 by wvu improves the suggested scripts given when deprecated Meterpreter scripts are invoked by the user.
Get it
As always, you can update to the latest Metasploit Framework with msfupdate
and you can get more details on the changes since the last blog post from
GitHub:
We recently announced the release of Metasploit 5. You can get it by cloning
the Metasploit Framework repo (master branch). To install fresh without using git,
you can use the open-source-only Nightly Installers or the binary installers
(which also include the commercial editions).