Ransomware is the fastest-growing type of cybercrime, and according to Cybersecurity Ventures, global ransomware damage costs will reach $20 billion by 2021—that’s 57 times more than it was just five years ago. With the increase in remote work this year expanding the attack surface, the threat of ransomware continues to grow, making it even more vital for organizations to stay on top of known and unknown threats in order to protect against malicious operations.
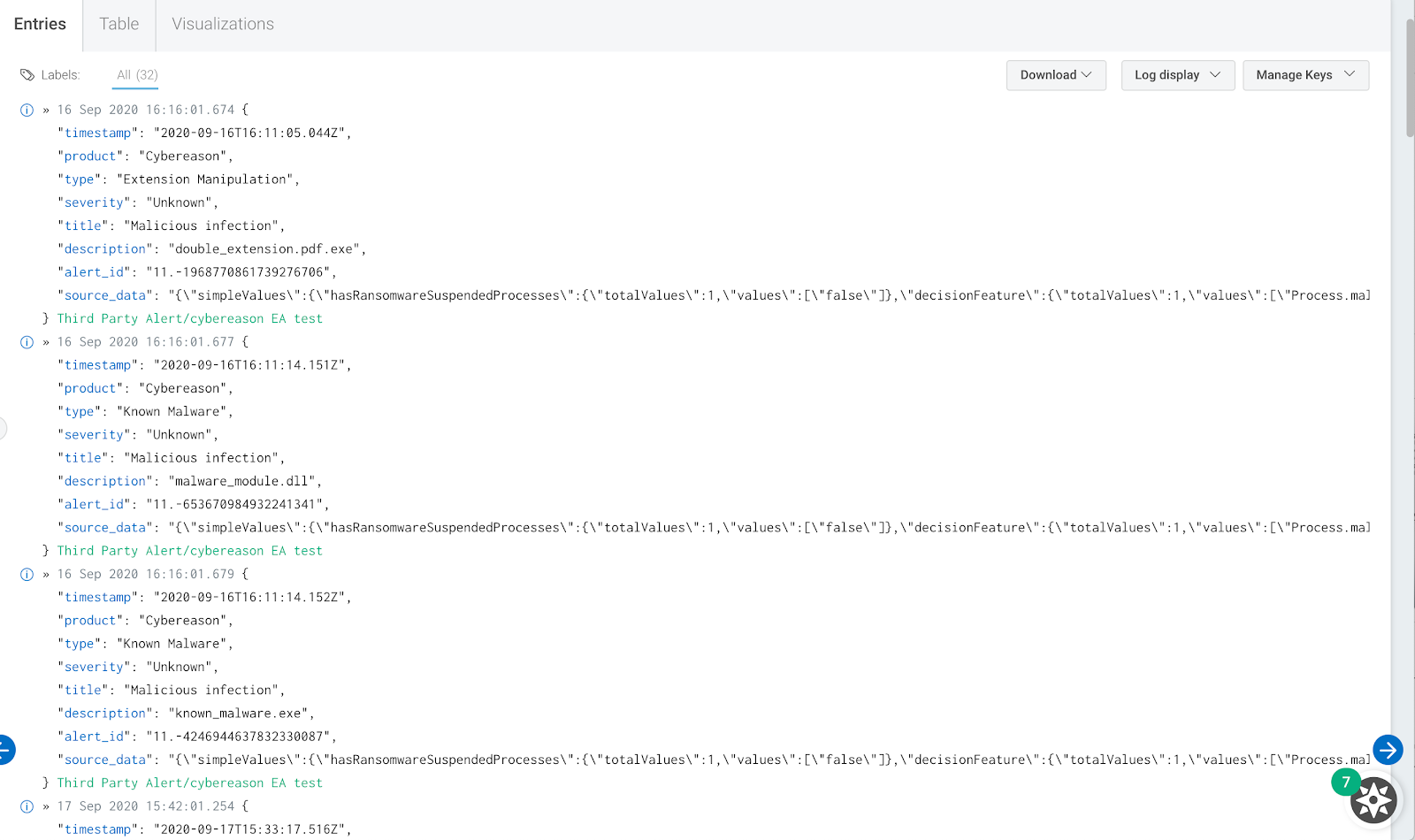
As InsightIDR, our natively cloud SIEM, continues to help teams save time and drive more effective detection and response, we’re excited to announce that customers can now seamlessly integrate with Cybereason. Cybereason’s Endpoint Detection and Response (EDR) platform detects events that signal malicious operations (Malops), which can now be fed as an event source to InsightIDR. With this new integration, every time an alert fires in Cybereason, it will get relayed to InsightIDR, which means less time jumping in and out of multiple tools and more time focusing on investigating and remediating attacks.
Further enhance your investigations with Cybereason data in InsightIDR
This new integration allows InsightIDR customers to enhance their investigations and dataset within InsightIDR in order to gain visibility into mobile devices. For example, say an alert related to lateral movement fires. With Cybereason’s mobile endpoint data, you can see whether it originated from a mobile device alongside all other endpoint data within InsightIDR, giving you a full picture of an attack across the network.
This new integration also lets you extend your threat hunting, enabling you to pull in Cybereason endpoint data to further enhance the built-in endpoint detection and visibility capabilities of InsightIDR.
Cybereason’s endpoint alerts are a great supplement to the out of coverage across users, cloud, logs, and network of InsightIDR. To learn more about the Cybereason event source, see our help docs here.
Article Tags
Related blog posts

Products and Tools
InsightIDR AI Alert Triage Automatically Classifies Alerts with 99.93% Benign Alert Accuracy
Chris Wraight

Detection and Response
New IDR Log Search Enhancements: Accelerate, Streamline, and Simplify Investigations
Rapid7

Products and Tools
What’s New in Rapid7 Products & Services: Q3 2024 in Review
Margaret Wei

Detection and Response
Rapid7 Named a Leader in IDC MarketScape: Worldwide SIEM for SMB and Enterprise
Meaghan Buchanan