INCIDENT COMMAND
AI Powered Next-Gen SIEM
Move beyond legacy SIEM with unified visibility, instant total attack surface context, and AI that transforms signals into decisive action.
Scaling your SOC with speed and confidence
Incident Command delivers a new standard for detection and response built for scale, speed, and clarity across your entire threat landscape.
Unified data, instant clarity
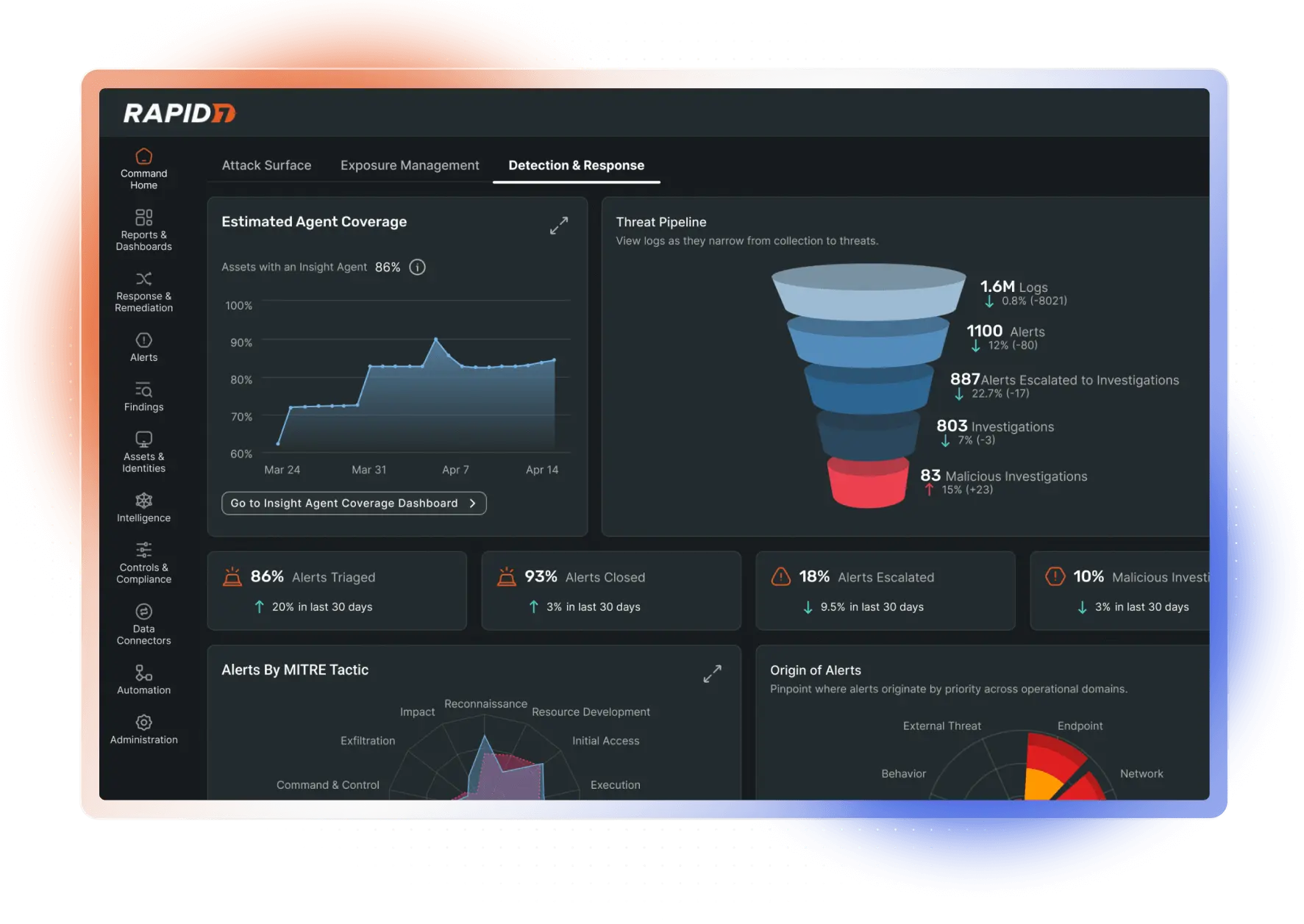
Combine logs, telemetry, and asset context from cloud, SaaS, endpoints, and your hybrid environment in a single, actionable view. No more blind spots, just continuous, full-spectrum visibility that powers your investigations from the start.
Zero in on what matters with the AI SOC
AI-driven behavioral detections, triage, and contextual enrichment cut through alert fatigue and surface the threats that matter. Accelerate threat hunting and response with AI-powered natural language search across billions of records.
Respond with speed and confidence
Every alert is enriched with exposure, vulnerability, threat intelligence, 3rd party, and asset risk data, so your team always knows what’s urgent and what to do next. SOAR automation and guided AI response shrink dwell time and take the guesswork out of necessary action.
Unified data, instant clarity
Combine logs, telemetry, and asset context from cloud, SaaS, endpoints, and your hybrid environment in a single, actionable view. No more blind spots, just continuous, full-spectrum visibility that powers your investigations from the start.
Zero in on what matters with the AI SOC
AI-driven behavioral detections, triage, and contextual enrichment cut through alert fatigue and surface the threats that matter. Accelerate threat hunting and response with AI-powered natural language search across billions of records.
Respond with speed and confidence
Every alert is enriched with exposure, vulnerability, threat intelligence, 3rd party, and asset risk data, so your team always knows what’s urgent and what to do next. SOAR automation and guided AI response shrink dwell time and take the guesswork out of necessary action.
Analyst Recognition
2025 SIEM Magic Quadrant™ Is Here
Rapid7 has been included in the 2025 Gartner® Magic Quadrant™ for SIEM. Explore how our cloud-native platform helps SOC teams detect faster, automate confidently, and scale securely across hybrid environments.
Features
Next-gen SIEM
Attack Surface Management
AI Alert Triage
Endpoint Detection and Response
Network Traffic Analysis
User & Entity Behavior Analytics
Cloud and Integrations
Digital Forensics and Incident Response
Expertly Vetted Threat Intelligence
Agentic AI Investigation Workflows
AI-powered Natural Language Log Search
Embedded Threat Intelligence
MITRE ATT&CK® Alignment
Deception Technology
Digital Forensics, Incident Response & Investigations
Automation & Response (SOAR)
Next-gen SIEM
Attack Surface Management
AI Alert Triage
Endpoint Detection and Response
Network Traffic Analysis
User & Entity Behavior Analytics
Cloud and Integrations
Digital Forensics and Incident Response
Expertly Vetted Threat Intelligence
Agentic AI Investigation Workflows
AI-powered Natural Language Log Search
Embedded Threat Intelligence
MITRE ATT&CK® Alignment
Deception Technology
Digital Forensics, Incident Response & Investigations
Automation & Response (SOAR)
SIEM Packages
Incident Command is built to meet you where you are
Essentials
Streamlined SIEM with smarter threat hunting and full attack surface visibility.
Advanced
Accelerate investigations with AI triage, deception technology, and deep threat intel.
Ultimate
Go beyond SIEM with full XDR capabilities & embedded DFIR in a single lightweight agent.
Essentials
Streamlined SIEM with smarter threat hunting and full attack surface visibility.
Advanced
Accelerate investigations with AI triage, deception technology, and deep threat intel.
Ultimate
Go beyond SIEM with full XDR capabilities & embedded DFIR in a single lightweight agent.
How Rapid7 accelerates security
Built on 20 years of data, Rapid7’s AI engine automatically assesses vulnerability risk to proactively improve your security posture and optimizes SOC workflows to detect threats as they happen.