This post takes a look at some of the investments we've made throughout Q3 2023 to our Detection and Response offerings to provide advanced DFIR capabilities with Velociraptor, more flexibility with custom detection rules, enhancements to our dashboard and log search features, and more.
Stop attacks before they happen with Next-Gen Antivirus in Managed Threat Complete
As endpoint attacks become more elusive and frequent, we know security teams need reliable coverage to keep their organizations safe. To provide teams with protection from both known and unknown threats, we’ve released multilayered prevention with Next-Gen Antivirus in Managed Threat Complete. Available through the Insight Agent, you’ll get immediate coverage with no additional configurations or deployments. With Managed Next-Gen Antivirus you’ll be able to:
- Block known and unknown threats early in the kill chain
- Halt malware that’s built to bypass existing security controls
- Maximize your security stack and ROI with existing Insight Agent
- Leverage the expertise of our MDR team to triage and investigate these alerts
To see more on our Managed Next-Gen Antivirus offering, including a demo walkthrough, visit our Endpoint Hub Page here.
Achieve faster DFIR outcomes with Velociraptor now integrated into the Insight Platform
As security teams are facing more and more persistent threats on their endpoints, it’s crucial to have proactive security measures that can identify attacks early in the kill chain, and the ability to access detailed evidence to drive complete remediation. We’re excited to announce that InsightIDR Ultimate customers can now recognize the value of Velociraptor, Rapid7’s open-source DFIR framework, faster than ever with its new integration into the Insight Platform.
With no additional deployment or configurations required, InsightIDR customers can deploy Velociraptor through their existing Insight Agents for daily threat monitoring and hunting, swift threat response, and expanded threat detection capabilities. For more details, check out our recent blog post here.
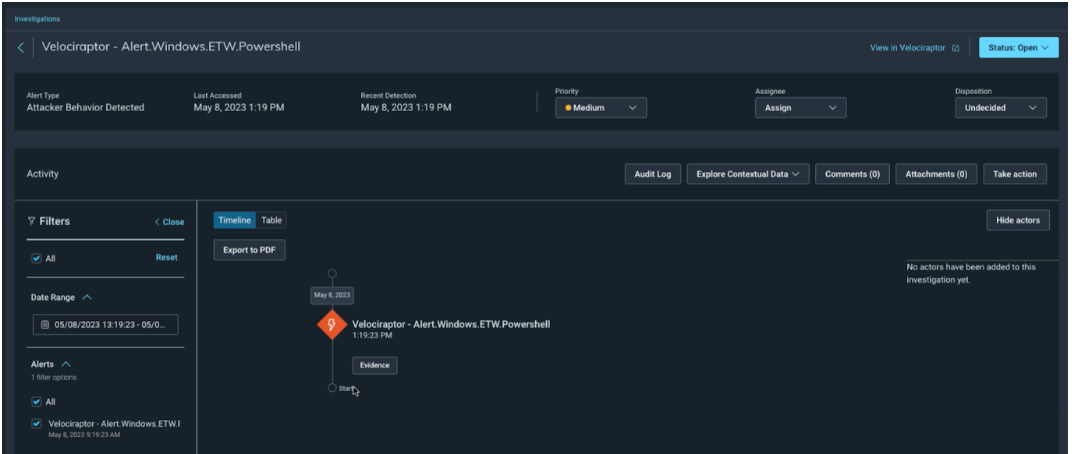
A view of Velociraptor in InsightIDR
Tailor alerts to your unique needs with Custom Detection Rules
We know every organization has unique needs when it comes to detections and alerting on threats. While InsightIDR provides over 3,000 out-of-the-box detection rules to detect malicious behaviors, we've added additional capabilities with Custom Detection Rules to offer teams the ability to author rules tailored to their own individual needs. With Custom Detection Rules, you will be able to:
- Build upon Rapid7’s library of expertly curated detection rules by creating rules that uniquely fit your organization’s security needs
- Use LEQL to write rule logic against a variety of data sources
- Add grouping and threshold conditions to refine your rule logic over specific periods of time to decrease unnecessary noise
- Assess the rules activity before it starts to trigger alerts for downstream teams
- Group alerts by specific keys such as by user or by asset within investigations to reduce triage time
- Create exceptions and view modification history as you would with out-of-the-box ABA detection rules
- Attach InsightConnect automation workflows to your custom rules to mitigate manual tasks such as containing assets and enriching data, or set up notifications when detections occur
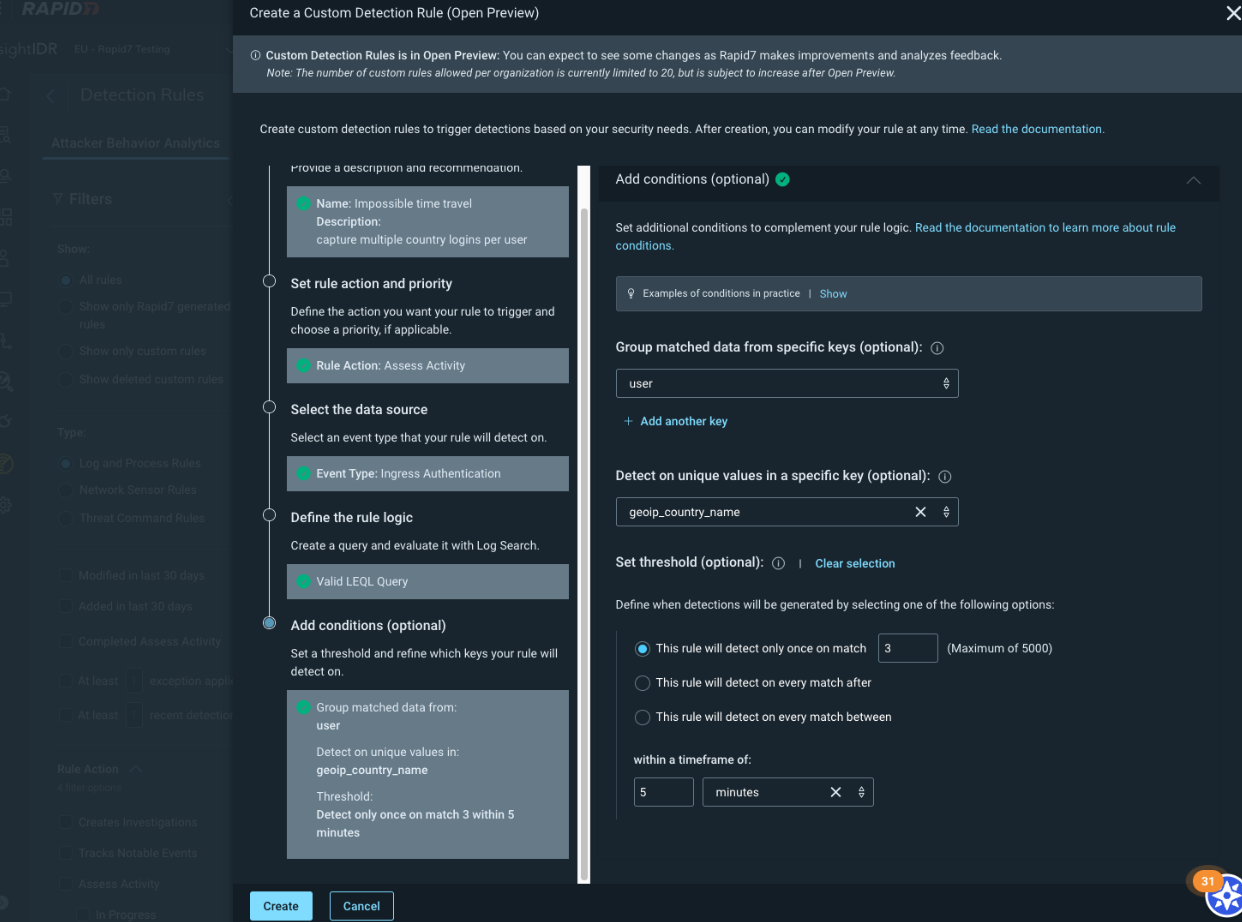
Creating a Custom Detection Rule in InsightIDR
Enhanced Attacker Behavior Analytics (ABA) alert details in Investigations
Easily view information about your ABA alerts that are a part of an investigation with our updated Evidence panel. With these updates, you’ll see more information on alerts, including their source event data and detection rule logic that generated them. Additionally, the Evidence button has also been renamed to Alert Details to more accurately reflect its function.
New alert details include:
- A brief description of the alert and a recommendation for triage
- The detection rule logic that generated the alert and the corresponding key-value payload from your environment
- The process tree, which displays details about the process that occurred when the alert was generated and the processes that occurred before and after (only for MDR customers)
Dashboard Improvements: Revamped card builder and a new heat map visualization
Our recently released revamped card builder provides more functionality to make it faster and easier to build dashboard cards. For a look at what’s new, check out the demo below.
The new calendar heat map visualization allows you to more easily visualize trends in your data over time so you can quickly spot trends and anomalies. To see this new visualization in action, check out the demo below.
Export data locally with new Log Search option
You now have more flexibility when it comes to exporting your log search data, making it easier to gather evidence related to incidents for additional searching, sharing with others in your organization, or gathering evidence associated with incidents.
With this update you can now:
- Use edit key selection to define what columns to export to csv
- Export results from a grouby/calculate query to a csv file
New event sources
- Microsoft Internet Information Services (IIS): A web server that is used to exchange web content with internet users. Read the documentation
- Amazon Security Lake: A security data lake service that allows customers to aggregate & manage security-related logs. Read the documentation
- Salesforce Threat Detection: Uses machine learning to detect threats within a Salesforce organization. Read the documentation
A growing library of actionable detections
In Q3 2023 we added 530 new ABA detection rules. See them in-product or visit the Detection Library for actionable descriptions and recommendations.
Stay tuned!
As always, we’re continuing to work on exciting product enhancements and releases throughout the year. Keep an eye on our blog and release notes as we continue to highlight the latest in detection and response at Rapid7.
Related blog posts

Detection and Response
Zero Chaos: Scaling Detection Engineering at the Speed of Software, with Detection As Code
Zachary Zeid, James Gallahan
Threat Research
Rapid7 Detection Coverage for Iran-Linked Cyber Activity
Rapid7 Labs

Detection and Response
Alert Fatigue Isn’t Going Away. Here’s How Modern SOCs Are Fighting Back
Rapid7

Detection and Response
Rapid7: 7 years of recognition in Gartner® Magic Quadrant™ for SIEM
Cindy Stanton

