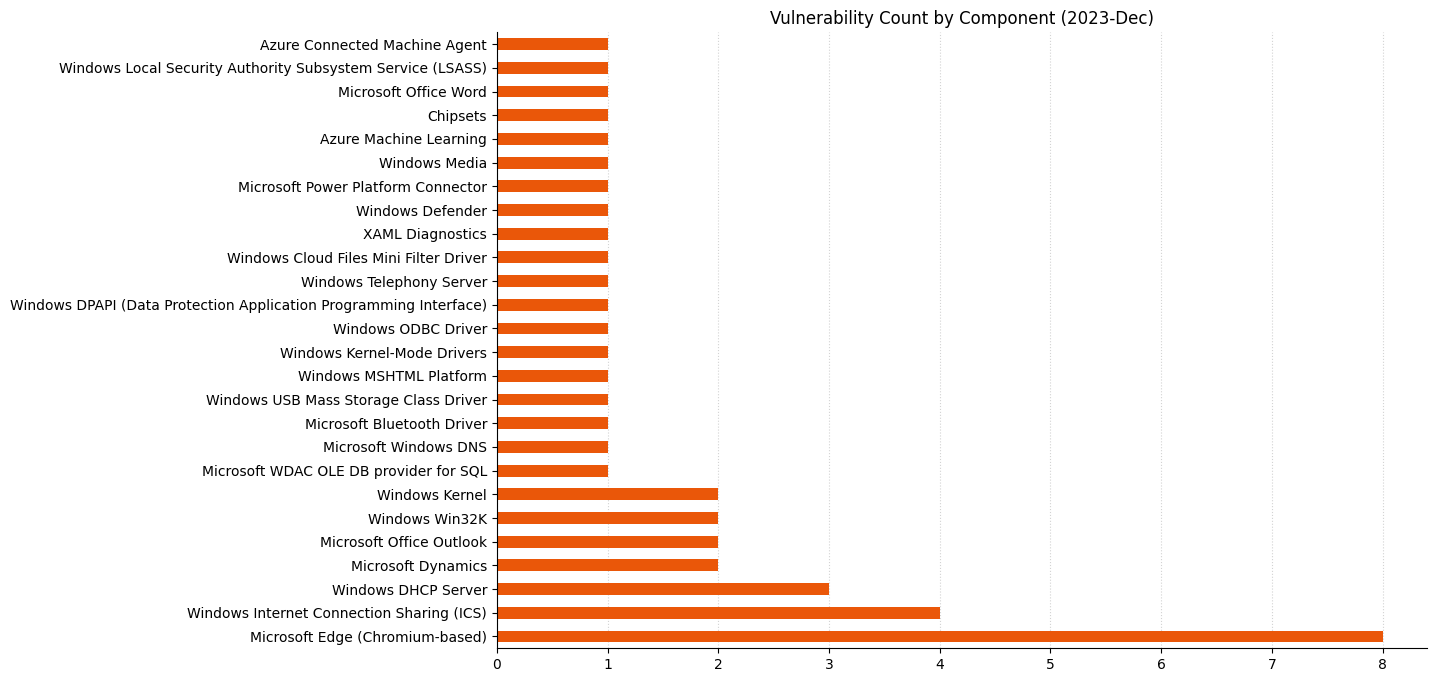
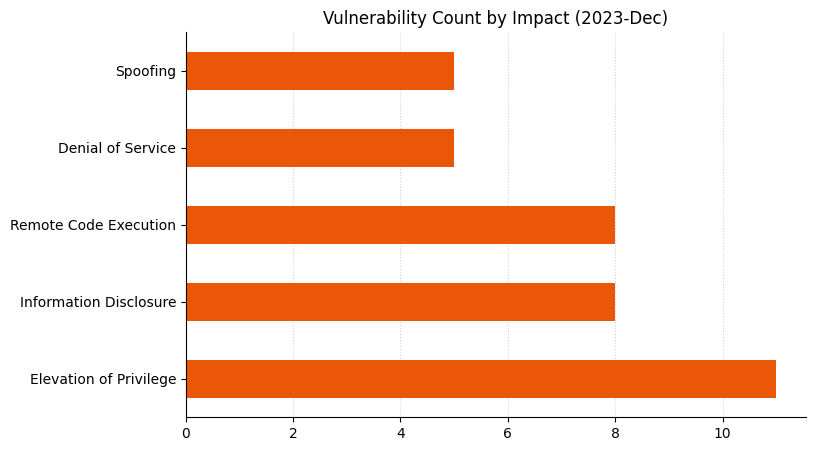
Microsoft is addressing 34 vulnerabilities this December Patch Tuesday, including a single zero-day vulnerability and three critical remote code execution (RCE) vulnerabilities. December Patch Tuesday has historically seen fewer patches than a typical month, and this trend continues in 2023. This total does not include eight browser vulnerabilities published earlier this month. At time of writing, none of the vulnerabilities patched today are yet added to the CISA KEV list.
Certain AMD processors: zero-day information disclosure
This month’s lone zero-day vulnerability is CVE-2023-20588, which describes a potential information disclosure due to a flaw in certain AMD processor models as listed on the AMD advisory. AMD states that a divide-by-zero on these processor models could potentially return speculative data. AMD believes the potential impact of the vulnerability is low since local access is required; however, Microsoft ranks severity as important under its own proprietary severity scale. The vulnerability is patched at the OS level in all supported versions of Windows, even as far back as Windows Server 2008 for Azure-hosted assets participating in the Extended Security Update (ESU) program.
Outlook: no-interaction critical RCE
CVE-2023-35628 describes a critical RCE vulnerability in the MSHTML proprietary browser engine still used by Outlook, among others, to render HTML content. Of particular note: the most concerning exploitation scenario leads to exploitation as soon as Outlook retrieves and processes the specially crafted malicious email. This means that exploitation could occur before the user interacts with the email in any way; not even the Preview Pane is required in this scenario. Other attack vectors exist: the user could also click a malicious link received via email, instant message, or other medium. Assets where Internet Explorer 11 has been fully disabled are still vulnerable until patched; the MSHTML engine remains installed within Windows regardless of the status of IE11.
Internet Connection Sharing: critical RCE
This month also brings patches for a pair of critical RCE vulnerabilities in Internet Connection Sharing. CVE-2023-35630 and CVE-2023-35641 share a number of similarities: a base CVSS v3.1 score of 8.8, Microsoft critical severity ranking, low attack complexity, and presumably execution in SYSTEM context on the target machine, although the advisories do not specify execution context. Description of the exploitation method does differ between the two, however.
CVE-2023-35630 requires the attacker to modify an option->length field in a DHCPv6 DHCPV6_MESSAGE_INFORMATION_REQUEST input message. Exploitation of CVE-2023-35641 is also via a maliciously crafted DHCP message to an ICS server, but the advisory gives no further clues.
A broadly similar ICS vulnerability in September 2023 led to RCE in a SYSTEM context on the ICS server. In all three cases, a mitigating factor is the requirement for the attack to be launched from the same network segment as the ICS server. It seems improbable that either of this month’s ICS vulnerabilities are exploitable against a target on which ICS is not running; Microsoft did not explicitly deny the possibility, but a subsequent update to the advisory for CVE-2023-35641 does clarify that exploitation requires that ICS is enabled.
Holiday season update
Notable by their absence this month: no security patches for Exchange, SharePoint, Visual Studio/.NET, or SQL Server. There are also no lifecycle transitions for Microsoft products this month, although a number of Windows Server 2019 editions and Office components will transition out of mainstream support and into extended support from January 2024.
Summary Charts

Summary Tables
Azure vulnerabilities
| CVE | Title | Exploited? | Publicly disclosed? | CVSSv3 base score |
|---|---|---|---|---|
| CVE-2023-35624 | Azure Connected Machine Agent Elevation of Privilege Vulnerability | No | No | 7.3 |
| CVE-2023-35625 | Azure Machine Learning Compute Instance for SDK Users Information Disclosure Vulnerability | No | No | 4.7 |
Browser vulnerabilities
| CVE | Title | Exploited? | Publicly disclosed? | CVSSv3 base score |
|---|---|---|---|---|
| CVE-2023-35618 | Microsoft Edge (Chromium-based) Elevation of Privilege Vulnerability | No | No | 9.6 |
| CVE-2023-36880 | Microsoft Edge (Chromium-based) Information Disclosure Vulnerability | No | No | 4.8 |
| CVE-2023-38174 | Microsoft Edge (Chromium-based) Information Disclosure Vulnerability | No | No | 4.3 |
| CVE-2023-6512 | Chromium: CVE-2023-6512 Inappropriate implementation in Web Browser UI | No | No | N/A |
| CVE-2023-6511 | Chromium: CVE-2023-6511 Inappropriate implementation in Autofill | No | No | N/A |
| CVE-2023-6510 | Chromium: CVE-2023-6510 Use after free in Media Capture | No | No | N/A |
| CVE-2023-6509 | Chromium: CVE-2023-6509 Use after free in Side Panel Search | No | No | N/A |
| CVE-2023-6508 | Chromium: CVE-2023-6508 Use after free in Media Stream | No | No | N/A |
ESU Windows vulnerabilities
| CVE | Title | Exploited? | Publicly disclosed? | CVSSv3 base score |
|---|---|---|---|---|
| CVE-2023-36006 | Microsoft WDAC OLE DB provider for SQL Server Remote Code Execution Vulnerability | No | No | 8.8 |
| CVE-2023-35639 | Microsoft ODBC Driver Remote Code Execution Vulnerability | No | No | 8.8 |
| CVE-2023-35641 | Internet Connection Sharing (ICS) Remote Code Execution Vulnerability | No | No | 8.8 |
| CVE-2023-35630 | Internet Connection Sharing (ICS) Remote Code Execution Vulnerability | No | No | 8.8 |
| CVE-2023-35628 | Windows MSHTML Platform Remote Code Execution Vulnerability | No | No | 8.1 |
| CVE-2023-21740 | Windows Media Remote Code Execution Vulnerability | No | No | 7.8 |
| CVE-2023-35633 | Windows Kernel Elevation of Privilege Vulnerability | No | No | 7.8 |
| CVE-2023-35632 | Windows Ancillary Function Driver for WinSock Elevation of Privilege Vulnerability | No | No | 7.8 |
| CVE-2023-36011 | Win32k Elevation of Privilege Vulnerability | No | No | 7.8 |
| CVE-2023-36005 | Windows Telephony Server Elevation of Privilege Vulnerability | No | No | 7.5 |
| CVE-2023-36004 | Windows DPAPI (Data Protection Application Programming Interface) Spoofing Vulnerability | No | No | 7.5 |
| CVE-2023-35622 | Windows DNS Spoofing Vulnerability | No | No | 7.5 |
| CVE-2023-35643 | DHCP Server Service Information Disclosure Vulnerability | No | No | 7.5 |
| CVE-2023-35638 | DHCP Server Service Denial of Service Vulnerability | No | No | 7.5 |
| CVE-2023-35629 | Microsoft USBHUB 3.0 Device Driver Remote Code Execution Vulnerability | No | No | 6.8 |
| CVE-2023-35642 | Internet Connection Sharing (ICS) Denial of Service Vulnerability | No | No | 6.5 |
| CVE-2023-36012 | DHCP Server Service Information Disclosure Vulnerability | No | No | 5.3 |
| CVE-2023-20588 | AMD: CVE-2023-20588 AMD Speculative Leaks Security Notice | No | Yes | N/A |
Microsoft Dynamics vulnerabilities
| CVE | Title | Exploited? | Publicly disclosed? | CVSSv3 base score |
|---|---|---|---|---|
| CVE-2023-36020 | Microsoft Dynamics 365 (on-premises) Cross-site Scripting Vulnerability | No | No | 7.6 |
| CVE-2023-35621 | Microsoft Dynamics 365 Finance and Operations Denial of Service Vulnerability | No | No | 7.5 |
Microsoft Dynamics Azure vulnerabilities
| CVE | Title | Exploited? | Publicly disclosed? | CVSSv3 base score |
|---|---|---|---|---|
| CVE-2023-36019 | Microsoft Power Platform Connector Spoofing Vulnerability | No | No | 9.6 |
Microsoft Office vulnerabilities
| CVE | Title | Exploited? | Publicly disclosed? | CVSSv3 base score |
|---|---|---|---|---|
| CVE-2023-35636 | Microsoft Outlook Information Disclosure Vulnerability | No | No | 6.5 |
| CVE-2023-36009 | Microsoft Word Information Disclosure Vulnerability | No | No | 5.5 |
| CVE-2023-35619 | Microsoft Outlook for Mac Spoofing Vulnerability | No | No | 5.3 |
System Center vulnerabilities
| CVE | Title | Exploited? | Publicly disclosed? | CVSSv3 base score |
|---|---|---|---|---|
| CVE-2023-36010 | Microsoft Defender Denial of Service Vulnerability | No | No | 7.5 |
Windows vulnerabilities
| CVE | Title | Exploited? | Publicly disclosed? | CVSSv3 base score |
|---|---|---|---|---|
| CVE-2023-35634 | Windows Bluetooth Driver Remote Code Execution Vulnerability | No | No | 8 |
| CVE-2023-35644 | Windows Sysmain Service Elevation of Privilege | No | No | 7.8 |
| CVE-2023-36696 | Windows Cloud Files Mini Filter Driver Elevation of Privilege Vulnerability | No | No | 7.8 |
| CVE-2023-35631 | Win32k Elevation of Privilege Vulnerability | No | No | 7.8 |
| CVE-2023-36391 | Local Security Authority Subsystem Service Elevation of Privilege Vulnerability | No | No | 7.8 |
| CVE-2023-36003 | XAML Diagnostics Elevation of Privilege Vulnerability | No | No | 6.7 |
| CVE-2023-35635 | Windows Kernel Denial of Service Vulnerability | No | No | 5.5 |
Updates
- 2023-12-14: Microsoft updated the advisory for CVE-2023-35641 to confirm that ICS must be enabled for exploitation to be possible.
Related blog posts

Exposure Management
Patch Tuesday - May 2026
Adam Barnett

Artificial Intelligence
Project Glasswing and the Next Challenge for Defenders: Turning Faster Discovery into Faster Action
Craig Adams

Exposure Management
Patch Tuesday - April 2026
Adam Barnett

Products and Tools
Negotiating with the Board: Translating Active Risk into Financial Exposure
Trevor Christiansen