Regardless of where you’re at in your application security maturity, dynamic application security testing (DAST) is a program staple in a few key ways:
It satisfies compliance requirements for runtime-related vulnerabilities.
DAST catches vulnerabilities in the running web application, yielding findings that may be missed in static code testing.
It is security-driven with little overhead in configuration/maintenance from development or application teams.
Due to the nature of web apps powering mission-critical operations – hyperscaled of course by AI protocols that automate key processes within these apps – continuous DAST is essential to identifying and remediating potential weaknesses that could quickly lead to costly data breaches.
Compliance requirements
DAST helps satisfy multiple compliance requirements by simulating real-world attacks so it can test a running application for vulnerabilities.. While DAST alone doesn’t make you compliant, it supports key controls in many security standards and regulations. Get to know 7 of today’s top standards and frameworks, see which requirements they satisfy, and learn how DAST helps secure the following:
PCI DSS
Payment Card Industry Data Security Standard (PCI DSS) is the global security standard for any organization that stores, processes, or transmits payment-card data. DAST directly supports PCI compliance by performing vulnerability scans against live web apps.
Requirements satisfied:
Requirement 6.1 & 6.2: Identifying and addressing vulnerabilities.
Requirement 6.6: All public-facing web applications must be either:
Protected with application-layer firewall (WAF), or
Tested for vulnerabilities (e.g., via DAST) at least annually.
OWASP Top Ten
While the Open Worldwide Application Security Project (OWASP) is not a compliance framework, the nonprofit organization is often referenced by industry and regulatory standards.
Requirements satisfied:
DAST tools are often tested against OWASP Top 10 vulnerabilities (e.g., XSS, SQLi, SSRF).
HIPAA
The Health Insurance Portability and Accountability Act (HIPAA) sets national standards for protecting electronic protected health information (ePHI). DAST supports risk assessment by identifying live vulnerabilities with the potential to expose such information.
Requirements satisfied:
Security Rule (45 CFR § 164.308 & § 164.312):
Requires organizations to perform regular risk assessments.
Includes application-level vulnerabilities as part of overall system security.
ISO/IEC 27001
ISO/International Electrotechnical Commission (ISO/IEC) is the international standard that specifies requirements for an information security management system (ISMS). DAST helps fulfill this requirement by scanning running applications for known and exploitable vulnerabilities.
Requirements satisfied:
Annex A.12.6.1: Management of technical vulnerabilities – Requires timely detection and remediation of vulnerabilities.
NIST SP 800-53/800-171
The National Institute of Standards and Technology (NIST) is a U.S. federal agency that develops measurement science, standards, and tech to boost innovation and economic security. DAST can be used to meet these technical controls.
Requirements satisfied:
RA-5 (vulnerability scanning): Requires scanning of systems and applications.
SI-2 (faw remediation): Identify, report, and fix flaws in software.
SOC 2
System and Organization Controls 2 (SOC2) is an independent attestation report (from a licensed CPA firm) that evaluates whether a service organization’s controls are suitably designed. DAST contributes evidence for audit logs and control effectiveness over time.
Requirements satisfied:
Under the "Security" Trust Services Criteria, particularly:
CC4.1: Monitor infrastructure for new threats.
CC7.1/CC7.2: Detect and mitigate vulnerabilities.
GDPR
General Data Protection Regulation (GDPR) harmonizes privacy rules across the EU and sets requirements for how organizations collect, use, share, and protect personal data. DAST can be part of regular security testing under GDPR, especially if the app processes personal data.
Requirements satisfied:
Article 32 – Security of Processing:
Organizations must ensure the ongoing confidentiality, integrity, availability of systems.
Requires regular testing and evaluation of security measures.
Missed findings
Static application security testing (SAST) tools are effective at flagging insecure values on their own, but they often miss the broader application context needed to assess whether those values actually introduce risk. Here are some examples of findings that can be overlooked:
Forced browsing
Forced browsing (also called insecure direct object reference or unauthorized resource access) occurs when:
A user can manually access restricted resources (files, endpoints, or actions) by guessing or modifying a URL.
There are missing access controls or authorization checks.
Example: A user modifies a URL
https://example.com/admin/settingsEven though they’re not an admin, the app still serves the page because it lacks proper access controls.
SAST struggles to detect these findings due to:
Lack of visibility into runtime access control
SAST scans source code, but can’t simulate user roles or sessions.
It doesn’t know who should or shouldn't be able to access a specific path.
Abstracted access control logic
Authorization might be handled via middleware, annotations, config files, or external services (e.g., OAuth).
SAST often can’t follow the full enforcement logic, especially if it's custom or dynamic.
Lack of awareness around routing and resource exposure
SAST doesn’t map which endpoints exist versus which are intended to be public.
It can’t verify which files/resources are accessible through URLs.
Out-of-band (OOB) cross-site scripting (XSS)
Out-of-band cross-site-scripting OOB XSS (a subtype of stored or blind XSS) occurs when:
A malicious script is injected into an application (e.g., a form, comment, or field).
The script doesn’t execute immediately but instead fires later, often:
In a different user’s browser (e.g., an admin viewing logs).
In an email client (e.g., via notification messages).
In a third-party system or admin dashboard.
These attacks are asynchronous and context-shifted, meaning they don’t happen in the direct request-response flow. SAST struggles to detect these findings due to:
Missing runtime context: SAST analyzes source code statically, line by line, without executing it. It doesn’t track:
Where the injected payload ends up.
How or where it's later rendered.
Whether it’s rendered in a dangerous context (HTML, JS, email, etc.).
Visibility is limited to code flow: SAST typically can’t follow data across storage layers or external systems. OOB XSS often spans:
User-submitted input → stored in DB.
Later retrieved → rendered in admin UI or email.
Unable to observe execution: The XSS payload doesn't fire in the original request, so SAST has no way to "see" the exploit being triggered because it doesn't execute code.
Web config findings
Settings defined in the web config file can pose challenges for SAST tools. Depending on the tooling, these files may not be properly parsed, potentially causing the tool to miss important findings due to a lack of contextual understanding, such as:
Custom error handling depends on deployment mode
<customErrors mode="RemoteOnly" />⠀
✔ Looks fine in static analysis; it shows friendly errors to remote users.
✖ Contextual issue: If the app is misconfigured to treat all users as local, then stack traces are exposed even with this setting.
SSL enforcement logic in code, not in config.
<rewrite>
<!-- Missing rule for HTTPS redirection -->
</rewrite>⠀
✔ SAST flags the absence of HTTPS redirection in web.config, which is a valid finding.
✖ Contextual issue: If HTTPS redirection is handled in middleware or at a reverse proxy (like NGINX or Azure App Gateway), then this isn't actually a security risk. SAST can’t always know that.
Authentication mode
<authentication mode="None" />⠀
✔ SAST will likely flag this as a critical issue.
✖ Contextual issue: If the app is a microservice behind an API gateway that handles auth, this may be acceptable. A SAST tool unaware of deployment architecture may raise false positives.
Debug enabled in a non-prod environment
<compilation debug="true" />⠀
✔ Flagged by SAST, correctly so in most cases.
✖ Contextual issue: If this web.config is only used in a staging or development slot, it might be intentional and not a production risk.
Authorization settings ignored in custom pipelines
<authorization>
<deny users="?" />
</authorization>⠀
✔ This looks like it blocks anonymous access.
✖ Contextual issue: If a custom authentication mechanism bypasses ASP.NET authorization modules, this setting may be ineffective, but a SAST tool won't see that unless it's deeply integrated with the entire codebase.
Developer overhead
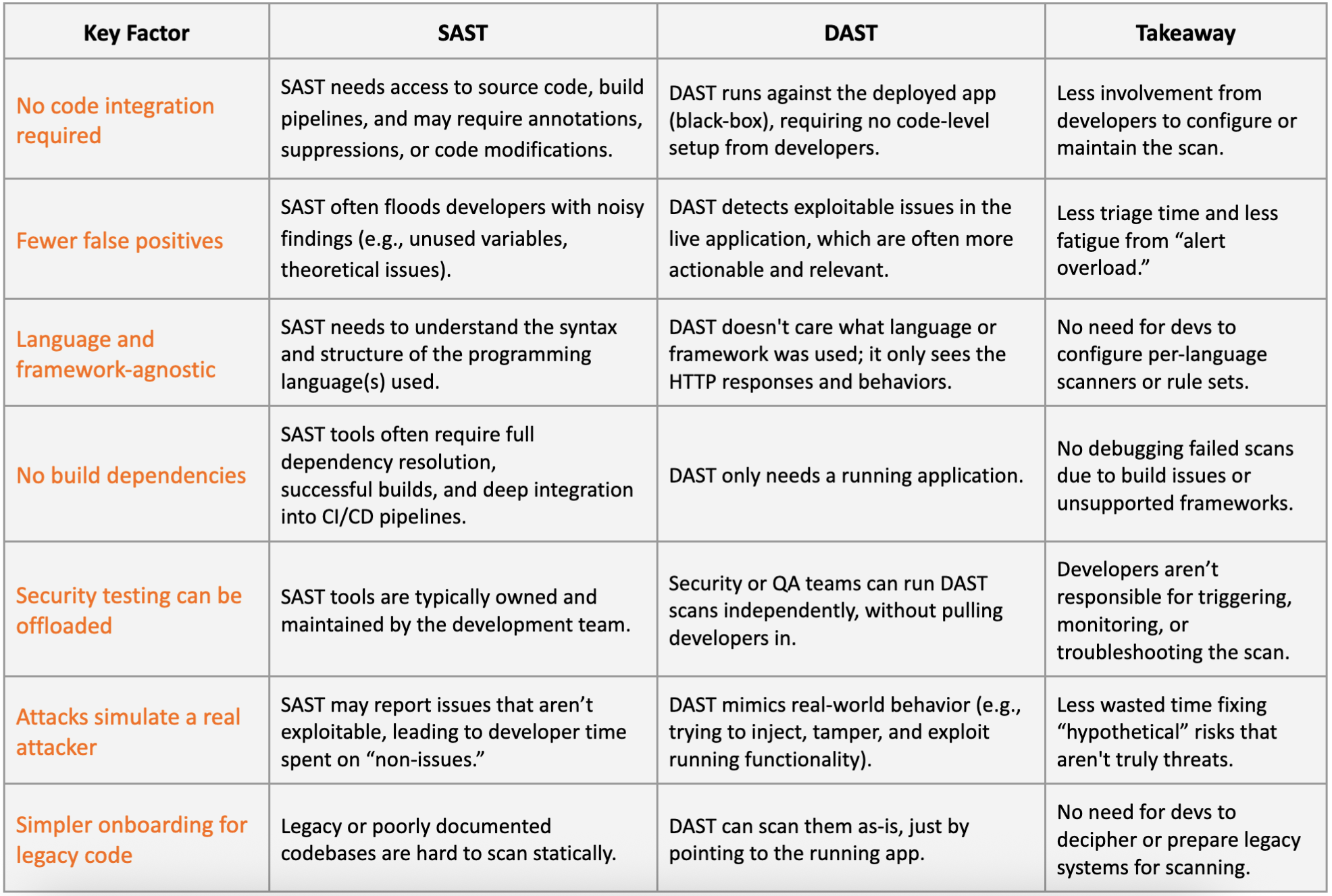
For organizations seeking to minimize developer burden, DAST is frequently the preferred option over SAST. DAST processes evolve alongside your web applications, continuing to scan them so that your business can promptly identify and remediate emerging issues. Let’s finish by taking a look at a range of underlying dynamics that make DAST an easy decision for developers looking to fortify application security – table below.
⠀
Related blog posts

Products and Tools
Test for React2Shell with Application Security using New Functionality
Rapid7

Products and Tools
InsightAppSec: Time-based One-Time Passwords, MFA Automation Using Macros
Shane Queeney

Products and Tools
Application Security Posture Management
Rapid7

Security Operations
NEW RESEARCH: Artificial intelligence and Machine Learning Can Be Used to Stop DAST Attacks Before they Start
Tom Caiazza
