Nearly every team in every organization is using some form of automation to help them scale and keep pace in today’s accelerated business landscape. Marketing teams are automating promotions and communications when customers complete certain activities; sales teams are automating various procurement and administrative processes; and DevOps teams are automating portions of development, testing, and deployment. And, unfortunately, even hackers are automating attacks to move further and faster inside organizations.
To keep up with an ever-evolving environment, stay ahead of attackers, and combat the constraints of an under-resourced industry, security teams must find ways to improve efficiency in their Security Operations Center (SOC). Successful teams leverage automation in their security toolkit to eliminate redundant, manual processes, expedite response, and tap into greater economies of scale when it comes to sourcing and aggregating useful information. For these reasons, Rapid7 continues to invest in making automation more accessible for security professionals across the entire Insight Cloud product suite and our standalone SOAR solution.
Automation in threat detection and response
InsightIDR, Rapid7’s cloud SIEM for modern threat detection and response, is focused on helping teams recognize the efficiencies required to effectively advance their security posture and minimize threats in their environments. These efficiencies are delivered throughout the product experience, from eliminating management overhead via lightweight cloud hosting, to research-backed detections out-of-the-box, to high-context investigation timelines and response tools.
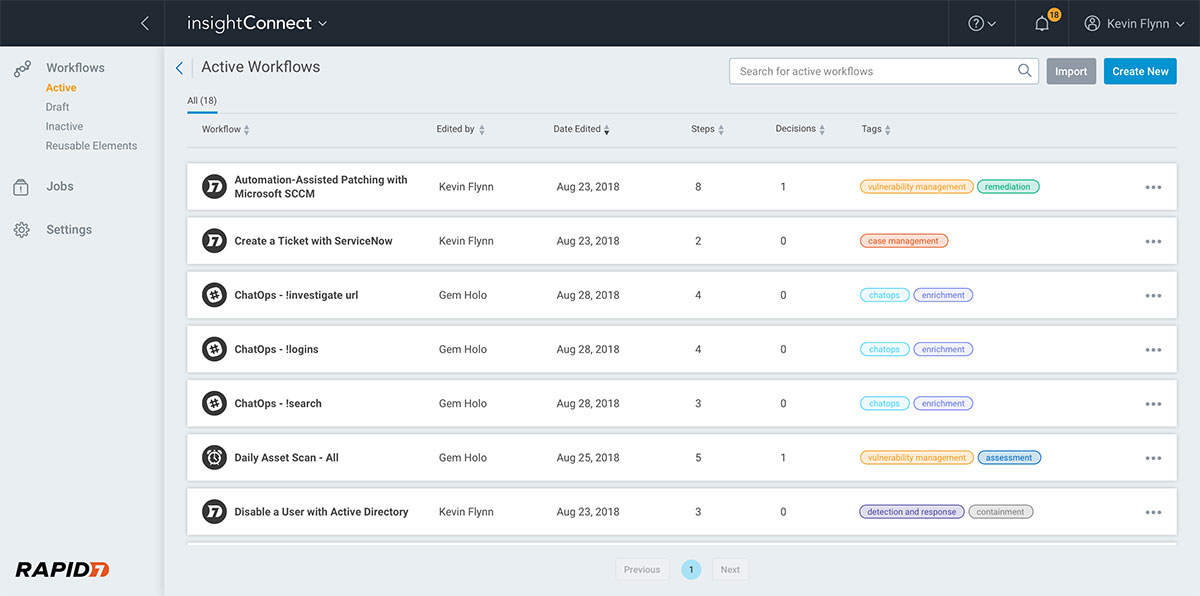
Additionally, InsightIDR customers have access to a number of automation features to double down on these efficiencies. These include prebuilt workflows for things like containing threats on an endpoint, suspending user accounts, or integrating with ticketing systems. To further build on these capabilities, InsightIDR recently added enrichment via open source threat intelligence to this list of workflows, as well as the ability to trigger any of these workflows (or InsightConnect workflows) off of User Behavior Analytics (UBA) alerts.
Leveraging enrichment to expedite detection and response
While good correlation across network data sources can help give analysts a solid understanding of threats and attacker movement, by enriching these alerts with threat intelligence, analysts capitalize on broader industry information and build a richer picture of active threats (which can, in turn, accelerate response times).
There are many different types and sources of threat intelligence. For example, many of the attacker behavior detections within InsightIDR are fueled by threat intelligence from things like the Cyber Threat Alliance, the Metasploit project, Project Sonar internet scans, and our own Managed Detection and Response (MDR) team. There are also a number of open source feeds and third-party vendors focused on aggregating and generating threat intelligence. Practitioners can enrich data with these threat intelligence feeds to understand associations with known bad behaviors or groups. For example, looking up a domain address against a database of active domains can help security professionals understand whether there are known associations to malicious parties.
The alert enrichment workflow in InsightIDR leverages open source threat intelligence to look up:
- IPs and domains with WHOIS
- DNS with Dig
- Hash reputation with Cymru
- URL extension with Unshorten.me
This additional context can be extremely helpful during the investigation process to narrow in on the threat actors at play.
Many organizations may choose to take it one step further and leverage specialized vendors for deeper threat intelligence, such as Recorded Future, ThreatConnect, Cisco ThreatGrid, and others. These advanced threat intelligence tools can offer robust, real-time threat information—which can in turn drive even faster and more informed response. InsightConnect works seamlessly with many of these threat intelligence tools, enabling users to build out custom workflows that incorporate these sources. Customers of InsightIDR and InsightConnect can easily access these advanced enrichment workflows (alongside any other InsightConnect workflows) via the console in InsightIDR. Enrichment is just one type of automation in the arsenal of tools available to security professionals.
Related blog posts

Products and Tools
Rapid7 completes IRAP PROTECTED assessment for Insight Platform solutions
Rapid7

Security Operations
How to Develop a SOAR Workflow to Automate a Critical Daily Task
Ryan Fried

Products and Tools
360-Degree XDR and Attack Surface Coverage With Rapid7
Margaret Wei

Products and Tools
Deploying a SOAR Tool Doesn’t Have to Be Hard: I’ve Done It Twice
Ryan Fried