I didn't know it then, but on September 1, 1997, my life changed. That was the day that Fyodor's Nmap was first released to the world, courtesy of the venerable Phrack magazine. At the time, I had just started my legitimate IT career, but boy oh boy, I was in the thick of it when it came to hackery hijinks. I won't admit to any crimes or anything in this, my now-very-legitimate company's blog post, but let me tell you: 1997 was a truly magical time for the nascent field of what would eventually become known as information security.
At the risk of making this sound like a "kids-these-days/back-in-my-day" kind of blog post, let me just say that if you wanted to probe and profile computers — yes, even computers you owned, legitimately — your choices were simultaneously limited and practically unbounded. In order to conduct network scanning, you had a bunch of tools available to you, all of which worked a little differently, ranging from "completely broken" to "kind of okay for some users." People who were into this sort of thing generally got frustrated with the tooling floating around and wrote their own, which meant that their tools tended to only work for them, since these projects were heavily dependent on that one person's local operating system configuration.
Nmap changed all that.
Early infosec’s magic moment
From the outset, Nmap was a simple tool that literally fit in a magazine article about network scanning tactics and tricks. It was two files of about 2,100 lines of code, and unlike many hacker tools of the day, it actually compiled for me on the first try.
Most importantly, Fyodor's code style was weirdly easy to read, even for a non-programmer hacker hobbyist like myself (I didn't get my first "real" IT job until 1998, but I did spend quite a bit of time in university computer labs for… reasons).
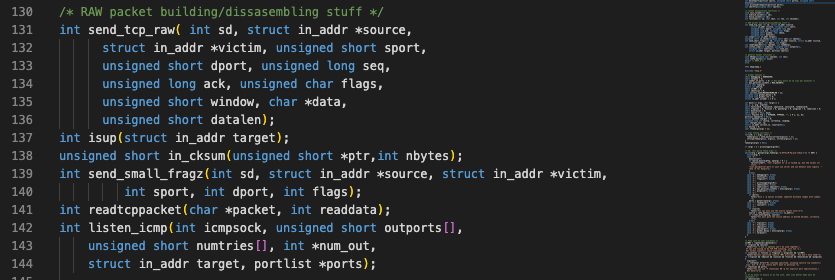
Smack in the middle, you can see elements like `send_tcp_raw()` (pictured above) that directly reflected the language in the TCP/IP standard, RFC 793, so the code was generally accessible to both hobbyists and professionals who had motivation to figure out how this TCP/IP stuff worked, really.
Incidentally, other projects were also popping off at the time, as well — l0phtcrack (a proprietary utility for recovering passwords) was released a few months before, and Nessus (a little open-source vulnerability scanner) was released a few months after, so there was definitely something in the ether during this 12-month period. Hacker tooling was transforming into infosec tooling, which meant more "luser n00bs," like myself, could get themselves enmeshed and enamored of the occult magicks of internet technology. Nmap, at least for me, stood out as a true oracle to the weird ways of packet crafting and network sleight-of-hand you could use in fun, unexpected ways to learn about the world.
Happy Scan-iversary, Nmap. Thanks for the cool career.
Additional reading:
- Pushing Open-Source Security Forward: Insights From Black Hat 2022
- The Hidden Harm of Silent Patches
- 2022 Cloud Misconfigurations Report: A Quick Look at the Latest Cloud Security Breaches and Attack Trends
Related blog posts

Vulnerabilities and Exploits
CVE-2026-0826: How an Old Bug Can Feed AI-Powered Impersonation
Douglas McKee, Director, Vulnerability Intelligence

Vulnerabilities and Exploits
CVE-2026-0826: Critical unauthenticated stack buffer overflow in HP Poly VVX and Trio VoIP Phones (FIXED)
Stephen Fewer

Vulnerabilities and Exploits
Authenticated RCE via Argument Injection in Gogs (FIXED as of June 7, 2026)
Jonah Burgess

Threat Research
Q1 2026 Threat Landscape Report: Zero-clicks, geopolitical tensions, and some wins for law enforcement
Rapid7 Labs

