Posts tagged Hacking
Threat Research
Introducing Hacktics and Telemetry, a Podcast from Rapid7 Labs
Douglas McKee, Director, Vulnerability Intelligence

Threat Research
Iran’s Cyber Playbook in the Escalating Regional Conflict
Rapid7 Labs
Industry Trends
Hacktivism and the Winter Olympics 2026: What We’re Seeing and What it Signals
Emma Burdett

Exposure Management
25 Years of Nmap: Happy Scan-iversary!
Tod Beardsley

Exposure Management
OWASP Top 10 Deep Dive: Injection and Stack Traces From a Hacker's Perspective
Julius Callahan

Exposure Management
Hack Back Is Still Wack
Jen Ellis

Exposure Management
Metasploit Hackathon Wrap-Up: What We Worked On
Brent Cook
Exposure Management
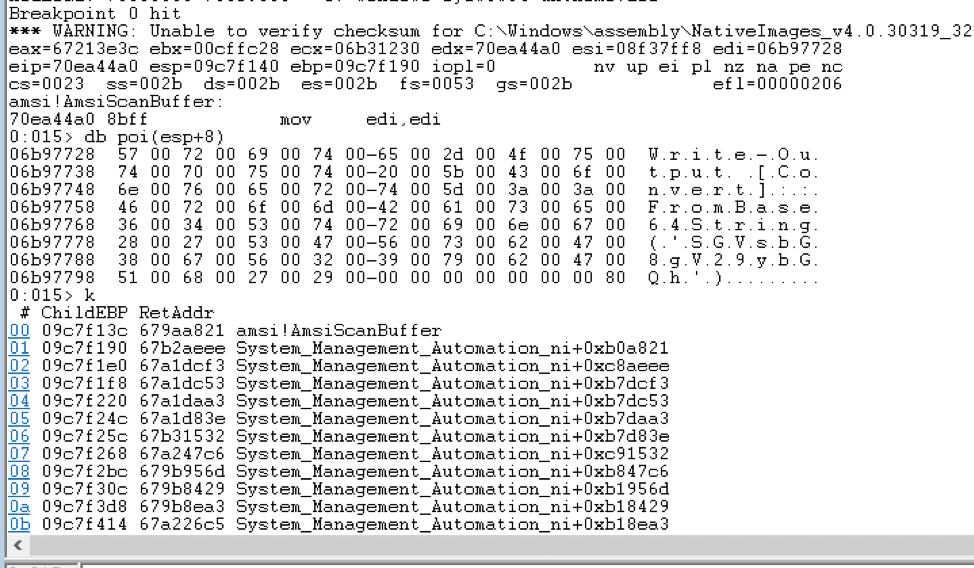
Hiding Metasploit Shellcode to Evade Windows Defender
Wei Chen

Exposure Management
Building a Car Hacking Development Workbench: Part 3
Andrew Bindner

Exposure Management
Building a Car Hacking Development Workbench: Part 2
Andrew Bindner

Exposure Management
Building a Car Hacking Development Workbench: Part 1
Andrew Bindner

Exposure Management
Rapid7 Supports Researcher Protections in Michigan Vehicle Hacking Law
Harley Geiger

Exposure Management
SNMP Data Harvesting During Penetration Testing
Deral Heiland

Exposure Management
Revisiting an Info Leak
Juan Vazquez

Exposure Management
SOC Monkey's Week in Review - 3.23.12
socmonkey