Stop me if you’ve heard this before. The scale, speed and complexity of cloud environments — particularly when you introduce containers and microservices — has made the lives of security professionals immensely harder. While it may seem trite, the reason we keep hearing this refrain is because, unfortunately, it’s true. In case you missed it, we discussed how cloud adoption creates a rapidly expanding attack surface in our last post.
One could argue that no subgroup of security professionals is feeling this pain more than the VM team. From elevated expectations, processes, and tooling to pressured budgets, the scale and complexity has made identifying and addressing vulnerabilities in cloud applications and the infrastructure that supports them a seemingly impossible task. During a recent webinar, Rapid7’s Cindy Stanton (SVP, Product and Customer Marketing) and Peter Scott (VP, Product Marketing) dove into this very subject.
Cindy starts off this section by unpacking why modern cloud environments require a fundamentally different approach to implementing and executing a vulnerability management program. The highly ephemeral nature of cloud resources with upwards of 20% of your infrastructure being spun down and replaced on a daily basis makes maintaining continuous and real-time visibility non-negotiable. Teams are also being tasked with managing exponentially larger environments, often consisting of 10s of thousands of instances at any given moment.
To make matters worse, it doesn’t stop at the technical hurdles. Cindy breaks down how ownership of resources and responsibilities related to addressing vulnerabilities once they’re identified has shifted. With traditional approaches it was typical to have a centralized group (typically IT) that owned and was ultimately responsible for the integrity of all resources. Today, the self-serve and democratized nature of cloud environments has created a dynamic in which it can be extremely difficult to track and identify who owns what resource or workload and who is ultimately responsible to remediate an issue when one arises.
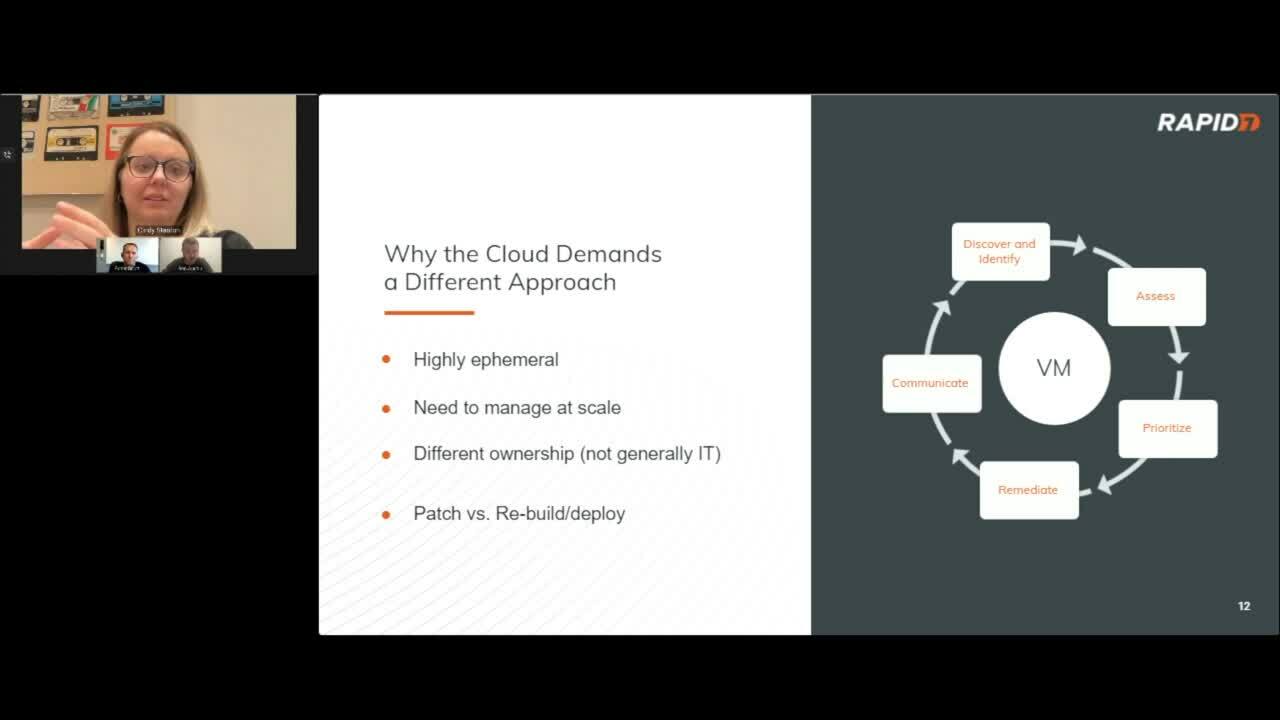
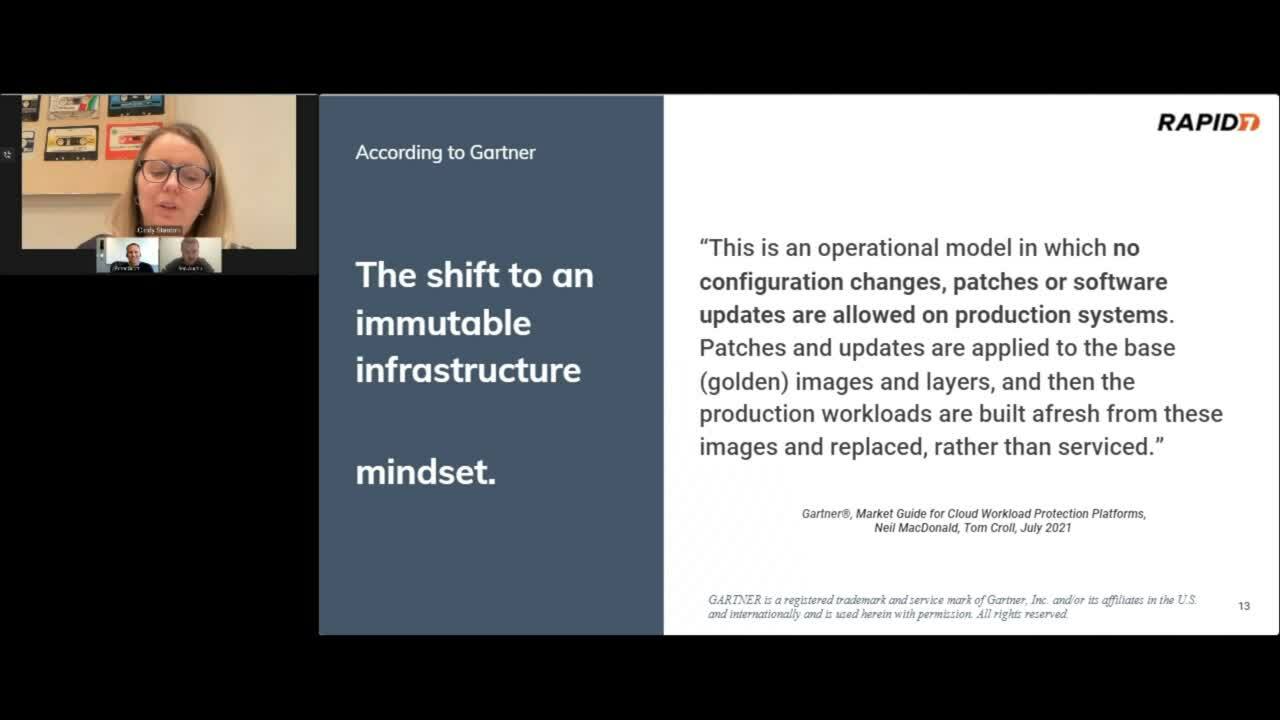
Cindy goes on to outline how drastically remediation processes need to shift when dealing with immutable infrastructure (i.e. containers) and how that also requires a shift in mindset. Instead of playing a game of whack-a-mole in production workloads trying to address vulnerabilities, the use of containers introduces a fundamentally new approach centered around making patches and updates to base images — often referred to as golden images — and then building new workloads from scratch based off of the hardened image rather than updating and retaining the existing workload. As Cindy so eloquently puts it, “the ‘what’ I have to do is relatively unchanged, but the ‘how’ really has to shift to adjust to this different environment.”
Peter follows up Cindy’s assessment of how cloud impacts and forces a fundamentally different approach to VM programs by providing some recommendations and best practices to adapt your program to this new paradigm as well as how to operationalize cloud vulnerability management across your organization. We’ll cover these best practices in our next blog in this series, including shifting your VM program left to catch vulnerabilities earlier on in the development process. We will also discuss enforcing proper tagging strategies and the use of automation to eliminate repetitive tasks and accelerate remediation times. If you’re interested in learning more about Rapid7's InsightCloudSec solution be sure to check out our bi-weekly demo, which goes live every other Wednesday at 1pm EST. Of course, you can always watch the complete replay of this webinar anytime as well!
Related blog posts

Exposure Management
Patch Tuesday - May 2026
Adam Barnett

Artificial Intelligence
Project Glasswing and the Next Challenge for Defenders: Turning Faster Discovery into Faster Action
Craig Adams

Exposure Management
Patch Tuesday - April 2026
Adam Barnett

Products and Tools
Negotiating with the Board: Translating Active Risk into Financial Exposure
Trevor Christiansen

