Security teams are flooded with logs, yet every alert demands fast, accurate context. In Verizon’s 2025 Data Breach Investigations Report [1], they analyzed 22,052 security incidents, of which 12,195 (55%) were confirmed breaches, underscoring how much activity teams must sift through to find what matters.
In practice, that means dozens of investigations per shift, each requiring fast judgment with incomplete context. A 2024 SANS survey shows that SOC teams report alert volume, limited context, and lack of automation continue to slow investigation and response [2].
Speed suffers. So does consistency.
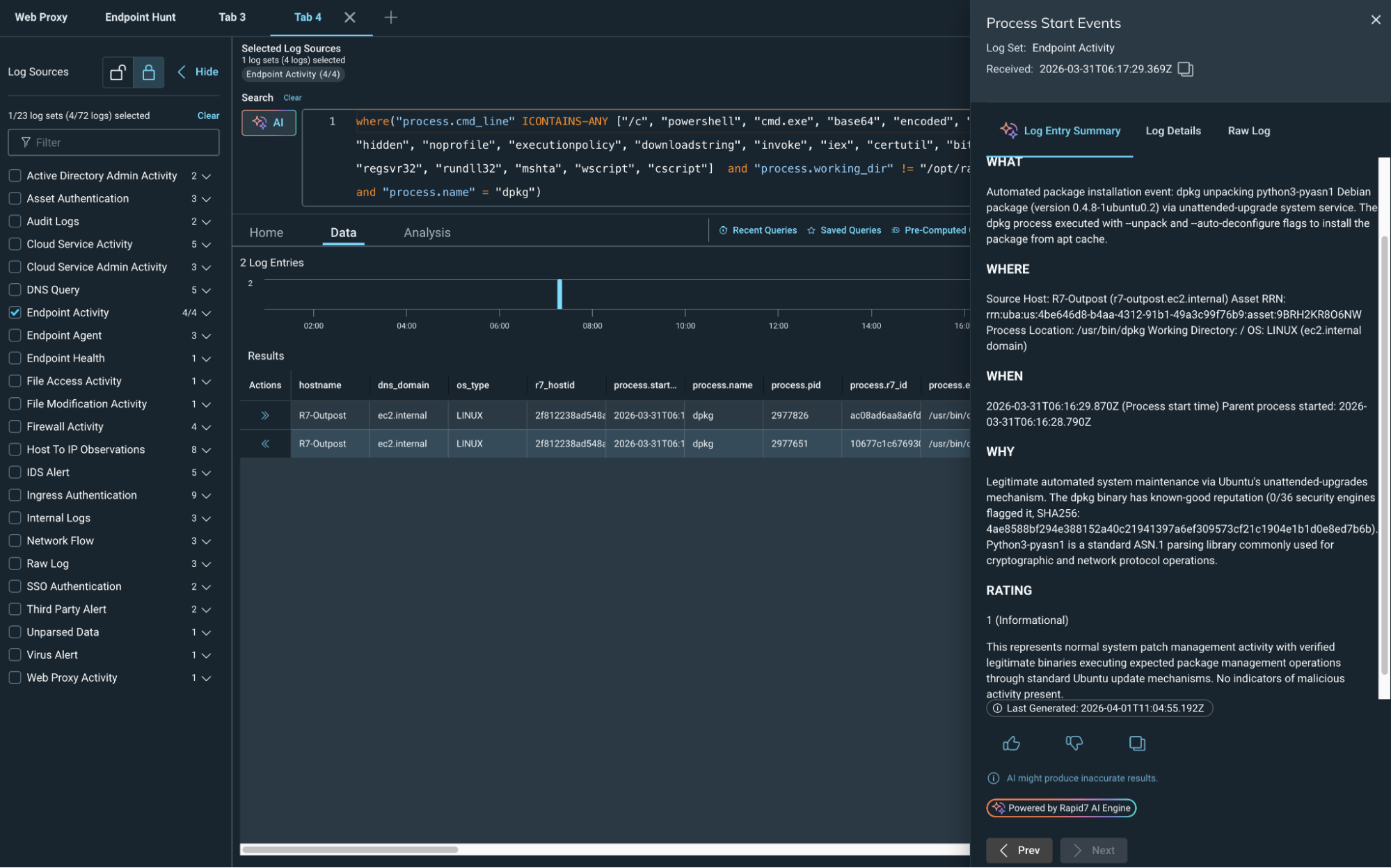
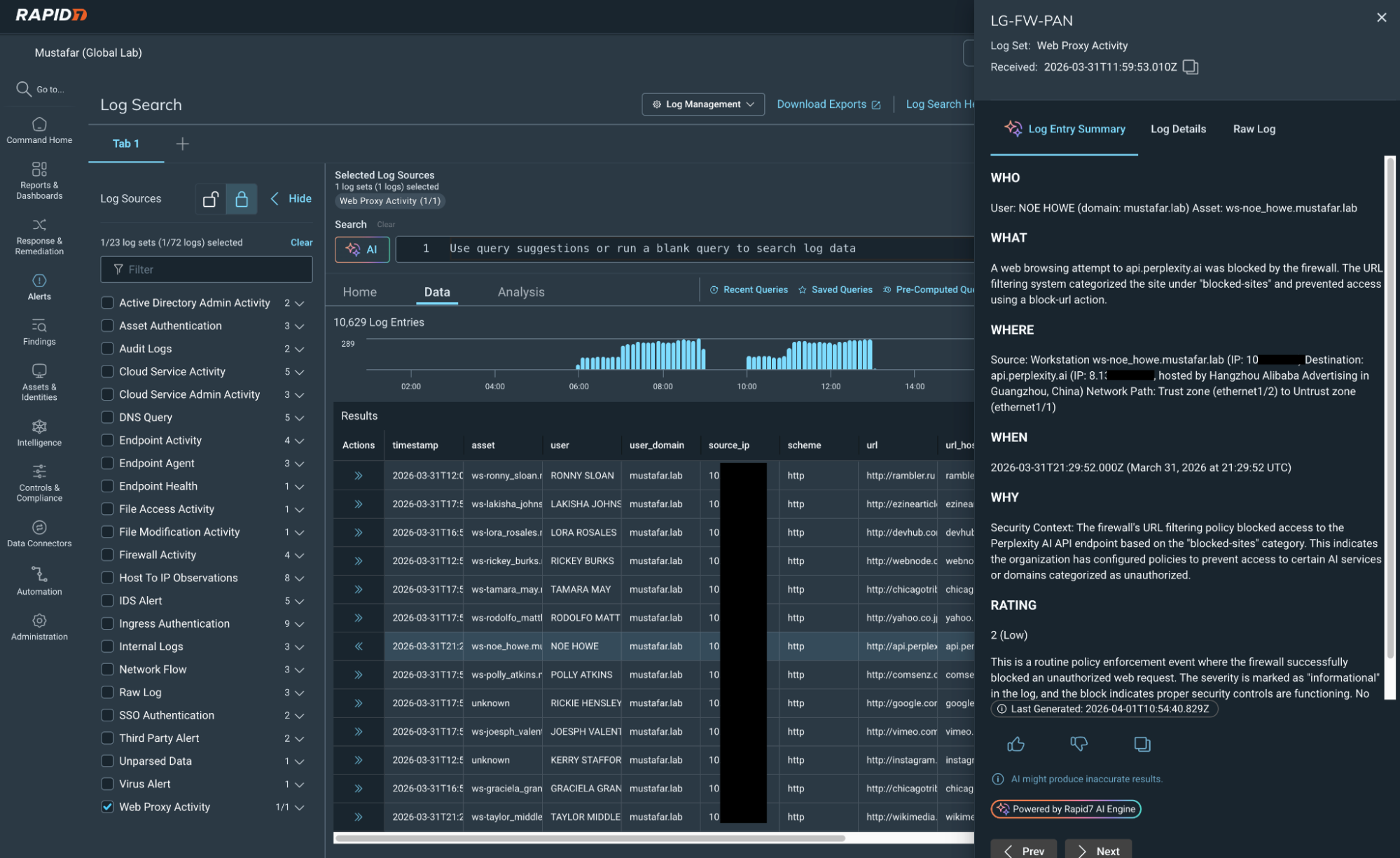
Turn raw logs into a clear narrative
AI-Powered Log Summary in Rapid7 Incident Command transforms raw log data into a clear, concise narrative directly within the investigation workflow. Analysts see what happened, why it matters, and what to do next in seconds, not minutes.
Instead of decoding logs line by line, analysts get:
Instant identification of who initiated the activity.
Fast understanding of exactly which actions occurred.
Clarity into when and where events unfolded.
Connectivity into why that behavior matters.
Analysts stay grounded in the original data, but they no longer have to fight through it to find answers. The summary provides immediate orientation and focus, keeping their focus on what to do next.
Built for real SOC workflows
⠀
AI-Powered Log Summary is embedded directly into the log search workflow. No pivoting, and no context switching. With a single action, analysts generate a contextual summary tailored to their results in seconds. That means faster investigations without breaking flow.
Summaries can be shared with teammates or leadership to communicate findings quickly, without rewriting technical details into plain language. Everyone stays aligned on what happened and what comes next.
AI integration in action
Rapid7 leverages the best available technology to protect our customers' attack surfaces. Our mission drives us to keep abreast of the latest AI advancements to deliver optimal value to customers while effectively managing the inherent risks of the technology. Integrating AI into our core processes enhances our operational security and underscores our commitment to ethical innovation.
At Rapid7, we are dedicated to leading responsibly in the AI space, ensuring that our technological advancements positively contribute to our customers, company, and society. Read more about how our TRiSM (Trust, Risk, and Security Management) is a foundational strategy that guides us in navigating the intricate landscape of AI with confidence and security.
Less noise, more impact
By reducing time spent parsing logs, teams can focus on what matters: containment, remediation, and proactive threat hunting.
⠀
This brings analysts:
Faster triage and investigations.
More consistent analysis across shifts.
Lower cognitive load during high-volume periods.
Clear communication to stakeholders.
Rapid7 is at the vanguard of integrating AI into its products to accelerate outcomes for our customers, with a particular focus on amplifying analyst impact and bringing speed and clarity to SOC operations throughout the threat detection and response lifecycle.
That is how modern SOC teams move faster. Visit the Incident Command page for more information.
⠀
Related blog posts

Products and Tools
Multi-Tenant API Access: Centralize, Scale, and Secure Your Operations
Niall Curry

Detection and Response
Alert Fatigue Isn’t Going Away. Here’s How Modern SOCs Are Fighting Back
Rapid7
Detection and Response
Announcing Rapid7’s Next-Gen SIEM Buyer’s Guide
Rapid7

Detection and Response
The End Of Legacy SIEM: Why It’s Time To Take Command
Rapid7