Speedup Improvements of MSFVenom & New Modules
This week, we have added new modules to Metasploit Framework targeting Cisco Catalyst SD-WAN controllers and osTicket as well as updates and improvements to Windows service-for-user persistence, and LDAP/ADCS-related modules to automatically report related services resulting in an improved data stream, which can be queried by using the services command.
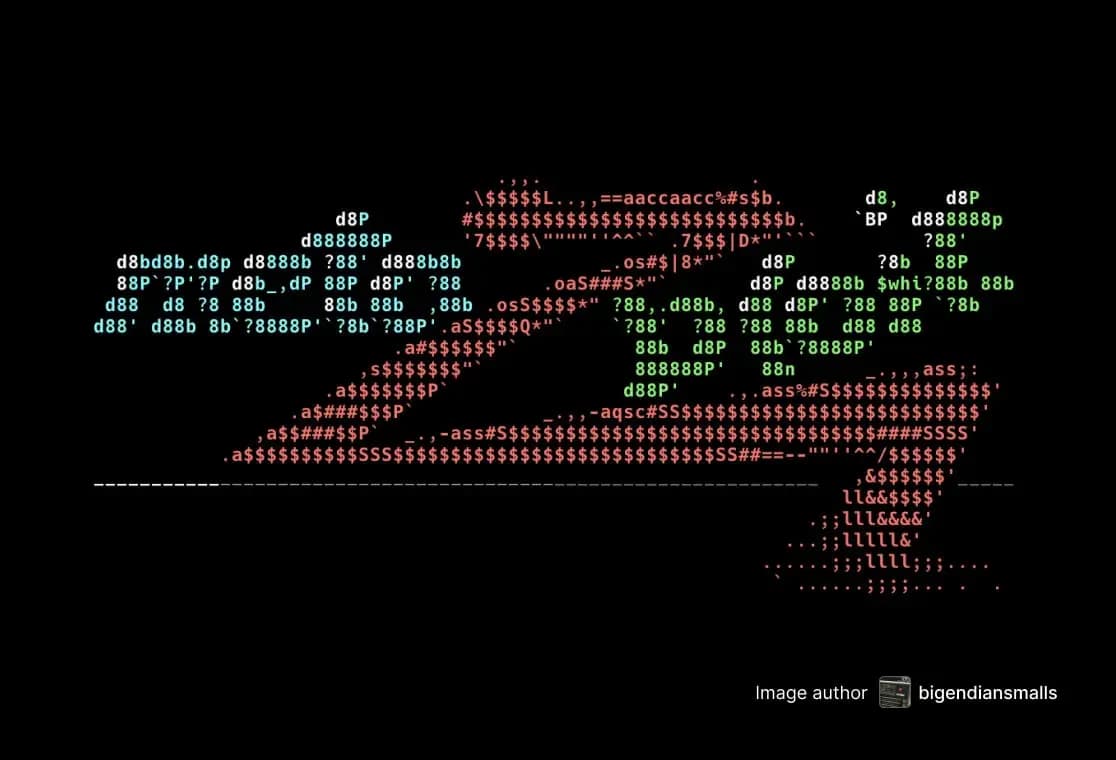
We also landed an improvement to msfvenom’s bootup time, thanks to bcoles, resulting in an approximate two-times speedup.
New module content (4)
AD/CS Authenticated Web Enrollment Services Module
Authors: Spencer McIntyre, bwatters-r7, and jhicks-r7
Type: Auxiliary
Pull request: #20752 contributed by bwatters-r7
Path: admin/http/web_enrollment_cert
Description: This adds a new auxiliary/admin/http/web_enrollment_cert modules that allows certificates to be issued from an Active Directory Certificate Services Web Enrollment portal. Its usage is the same as the auxiliary/admin/http/icpr_cert module but enables operators to issue certificates when the web enrollment portal is accessible but the MS-ICPR service is not.
Cisco Catalyst SD-WAN Controller Authentication Bypass
Author: sfewer-r7
Type: Auxiliary
Pull request: #21158 contributed by sfewer-r7
Path: admin/networking/cisco_sdwan_auth_bypass
AttackerKB reference: CVE-2026-20127
Description: This adds an auxiliary module to exploit an authentication bypass vulnerability, CVE-2026-20127, affecting Cisco Catalyst SD-WAN Controller. Recently exploited in the wild as a zero-day.
osTicket Arbitrary File Read via PHP Filter Chains in mPDF
Authors: Arkaprabha Chakraborty <@t1nt1nsn0wy> and HORIZON3.ai Team
Type: Auxiliary
Pull request: #20948 contributed by ArkaprabhaChakraborty
Path: gather/osticket_arbitrary_file_read
AttackerKB reference: CVE-2026-22200
Description: This adds an auxiliary module to exploit, CVE-2026-22200, an authenticated file read vulnerability in osTicket.
Windows Service for User (S4U) Scheduled Task Persistence - Event Trigger
Authors: Brandon McCann "zeknox" [email protected], Thomas McCarthy "smilingraccoon" [email protected], and h00die
Type: Exploit
Pull request: #20814 contributed by h00die
Path: windows/persistence/service_for_user/event
Description: Updates the Windows service-for-user persistence technique.
Enhancements and features (5)
- #20973 from bitstr3m-48 - This release enables command execution for non-interactive HWBridge sessions via the sessions -c flag. Additionally, the hwbridge/connect module now preserves parsed JSON error bodies from failed HTTP responses, which improves error messaging.
- #20977 from g0tmi1k - This updates the exploit/unix/webapp/php_eval module to have a FORMDATA datastore option, which adds HTTP POST-request support and makes the HEADERS datastore option consistent with other modules.
- #20979 from g0tmi1k - This updates the exploit/unix/webapp/php_include module with additional datastore options and make its usage more consistent with the similar exploit/unix/webapp/php_eval module.
- #21031 from zeroSteiner - Enhances the Metasploit’s LDAP/ADCS-related modules to automatically report related services (LDAP, DCERPC/ICertPassage/ADCS CA) and to improve vulnerability reporting by associating findings with the affected LDAP object’s DN (and, for ADCS template findings, the template name) so results are uniquely keyed and easier to interpret.
- #21229 from bcoles - This updates the msfvenom utility to use the metadata cache. The result is roughly 2x faster execution times when listing modules.
Bugs fixed (1)
- #21153 from Nayeraneru - This fixes an issue with some mutable constant datastore options. Using shared options like CHOST or CPORT are not changing visibility across modules anymore.
Documentation added (1)
- #21221 from cgranleese-r7 - This PR improves module_doc_template.md with examples to better guide contributors.
You can always find more documentation on our docsite at docs.metasploit.com.
Missing rn-* label on Github (3)
PLEASE ADD RN-TAGS TO THESE PULL REQUESTS BEFORE RELEASING THE WRAP UP, AND RERUN THE WRAPUP SCRIPT
- #7 from scriptjunkie - Not written - add release notes directly to the pull request, then regenerate. Do not edit manually without ensuring the pull request has the release note present.
- #20814 from h00die - Not written - add release notes directly to the pull request, then regenerate. Do not edit manually without ensuring the pull request has the release note present.
- #21143 from SaiSakthidar - This bumps the Metasploit payloads to include changes that enable the PHP Meterpreter to open TCP server sockets. This enables operators to listen for inbound connections on compromised hosts and closes a feature gap between PHP and the other Meterpreters.
Get it
As always, you can update to the latest Metasploit Framework with msfupdate and you can get more details on the changes since the last blog post from GitHub:
If you are a git user, you can clone the Metasploit Framework repo (master branch) for the latest. To install fresh without using git, you can use the open-source-only Nightly Installers or the commercial edition Metasploit Pro