As any seasoned security practitioner will tell you, dealing with web application vulnerabilities is only half the battle. First and foremost, you have to find those vulnerabilities, which presents a whole new set of challenges. Tasks such as building your portfolio of apps, tweaking your schedules, configuring authentication, and triggering scans are the bread and butter of many security operations centers, but somewhere between configuration and sending vulnerabilities out to your favorite dev team lies another major component of any mature application security program: scan management.
Scanning your web applications for vulnerabilities with InsightAppSec
Knowing what you are scanning, how often, and with how much success is vital to knowing your vulnerability data is accurate, up-to-date, and reflects your security position. But fret not—InsightAppSec was designed to keep both the scan management and vulnerability remediation sides of the house informed and satisfied.
Want to scan your web apps for security vulnerabilities? Sign up for a free InsightAppSec trial today.
Get StartedMonitoring your application's scan activity
As the software development industry increasingly moves toward agile development and adopts streamlined DevOps release cycles on the cloud, it’s never been easier to push new content and features to your web applications. This means dev teams can deliver faster than ever and are committing code on a daily basis. But what impact does this have on your security team? How is it possible to secure a constantly moving target? Web application security scanning is often the obvious solution, but with an ever-expanding portfolio, you need to stay on top of your scanning activity to drive a mature, sustainable security program.
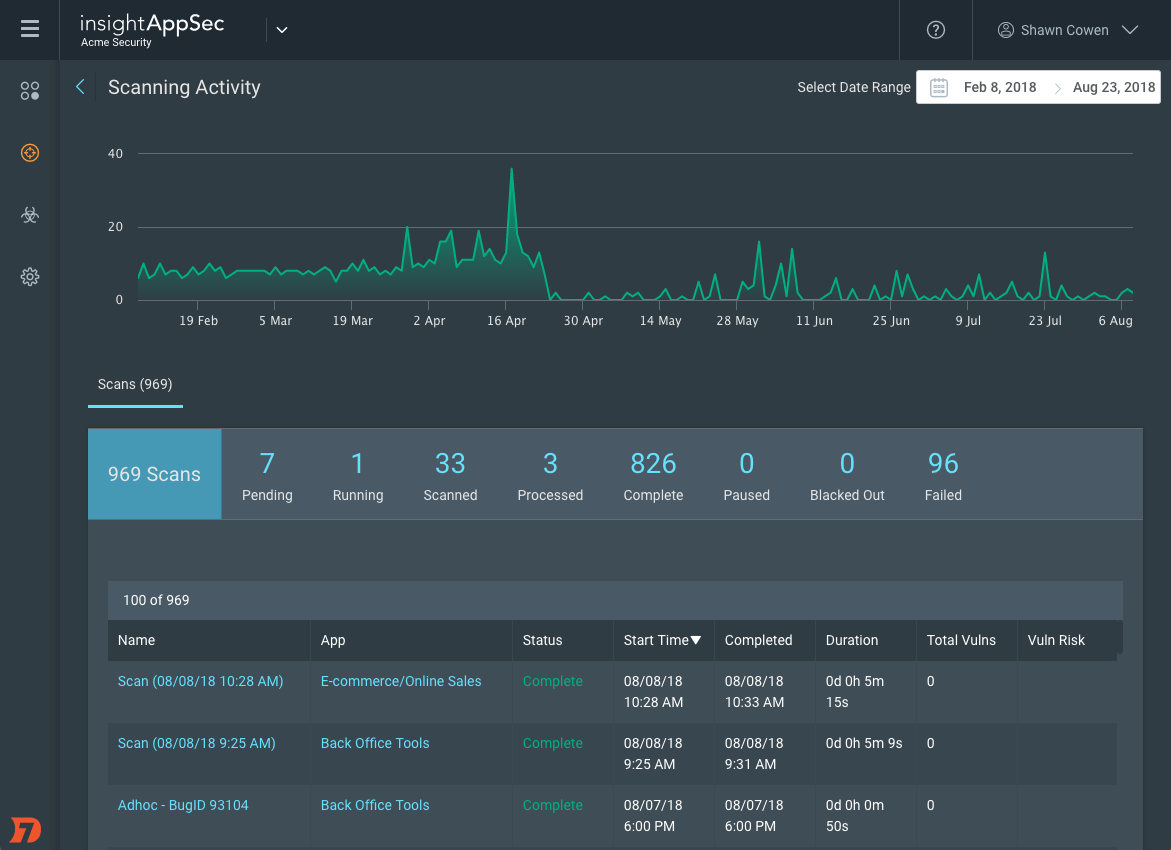
InsightAppSec provides an interactive activity dashboard that details the number and frequency of scans and lets you zero in on specific periods of time. You can take a closer look at significant trends, easily zoom to search within a given date range, and filter based on status. Browsing completed scans shows how recent the vulnerability data for each of your apps really is, with the ability to check whether you have met your scanning targets (for example, every 30 days, or within 14 days of deployment). You can also look for long-running scans that have yet to start or for any that have failed to complete.
Determining why a web app security scan fails
Let’s face it—in software development, not every system or web application plays ball the way we want it to. Refused connections, unexpected outages, and generally misbehaving servers will come as no surprise to most people in the industry. In fact, it would be more alarming if all the alerts suddenly stopped and there was nothing to report! As security operations (SecOps) becomes embedded as a standard component of software development, security teams need to ensure they are not only finding vulnerabilities, but also being vigilant that the scans being cued up are getting the job done.
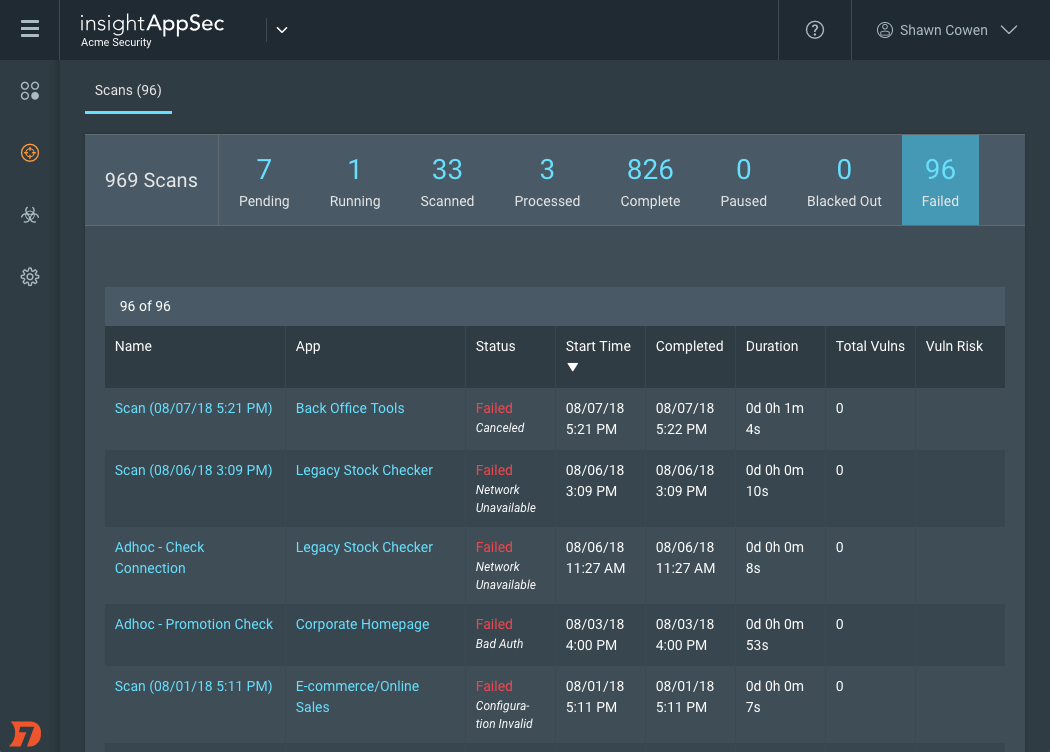
Without up-to-date vulnerability information, how can you be sure you’re fixing the right issues? Knowing your scans are running, successfully delivering results, and giving you coverage across your critical web applications is fundamental to addressing the right vulnerabilities. Having access to the underlying root cause of any incomplete scans will help you quickly identify problems and take action.
With InsightAppSec, it is easy to check at a glance which apps were unreachable and where there were authentication failures for the critical web applications in your portfolio.
More on InsightAppSec
InsightAppSec brings Rapid7’s proven Dynamic Application Security Testing (DAST) technology to the Insight platform, combining powerful application crawling and attack capabilities, flexibility in scan scope and scheduling, and accuracy in results with a modern UI, intuitive workflows, and sensible data organization. This enables you to identify cross-site scripting (XSS), SQL injections (SQLi), cross-site request forgery (CSRF), and other common web application vulnerabilities with ease. The best part? All of these capabilities are delivered via the cloud, so you are up and running in as few as five minutes to identify the critical security risks in your applications.
Uncover security vulnerabilities in your web apps today! Sign up for a free InsightAppSec trial.
Get StartedRelated blog posts

Products and Tools
Rapid7 completes IRAP PROTECTED assessment for Insight Platform solutions
Rapid7

Exposure Management
Enforce and Report on PCI DSS v4 Compliance with Rapid7
Lara Sunday

Products and Tools
InsightAppSec: Improving Scan Speed and Performance
Shane Queeney

Products and Tools
Application Security Posture Management
Rapid7
