The Rapid7 Blog:
Your Signal in the Security Noise
Insights, stories, and guidance from our global security and research teams.
Featured posts
3725 Results

Vulnerabilities and Exploits
Using InsightVM to Find Apache Log4j CVE-2021-44228
Greg Wiseman

Exposure Management
Update on Log4Shell’s Impact on Rapid7 Solutions and Systems
Rapid7

Vulnerabilities and Exploits
Driver-Based Attacks: Past and Present
Jake Baines

Threat Research
Metasploit Wrap-Up 12/10/21
Jeffrey Martin

Exposure Management
Widespread Exploitation of Critical Remote Code Execution in Apache Log4j
boB Rudis

Products and Tools
Stay Ahead of Threats With Cloud Workload Protection
Alon Berger

Industry Trends
Simplifying Complex Cybersecurity Regulations
Harley Geiger

Products and Tools
A Dream Team-Up: Integrate InsightAppSec With ServiceNow ITSM
Tom Caiazza

Exposure Management
Patch Now: SonicWall Fixes Multiple Vulnerabilities in SMA 100 Devices
Glenn Thorpe

Products and Tools
Demystifying XDR: A Forrester Analyst Lays the Foundation
Jesse Mack

Exposure Management
Oh No, Zoho: Active Exploitation of CVE-2021-44077 Allowing Unauthenticated Remote Code Execution
Glenn Thorpe

Detection and Response
3 Strategies That Are More Productive Than Hack Back
boB Rudis
Products and Tools
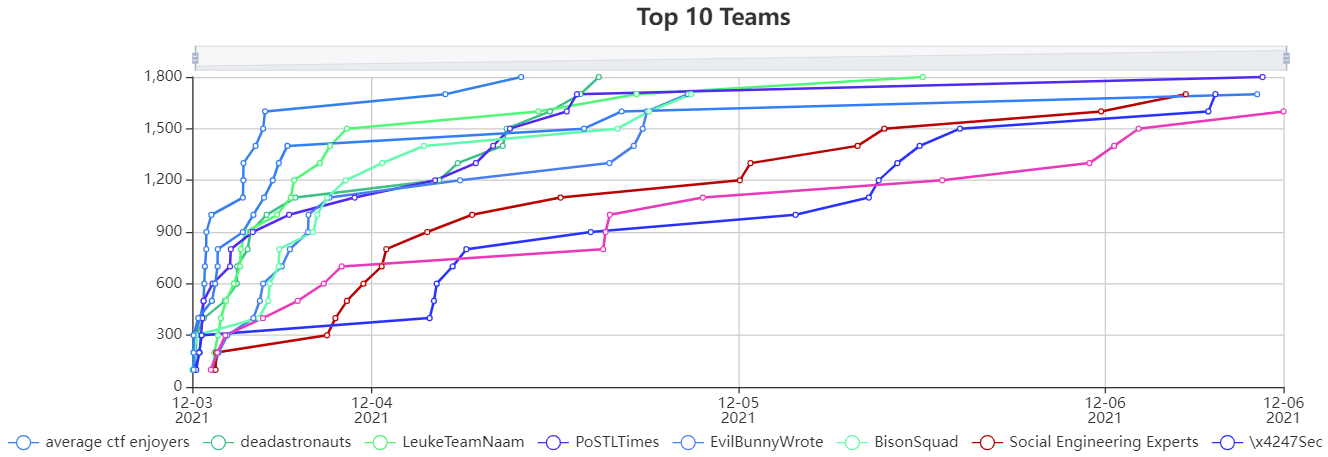
Congrats to the Winners of the 2021 Metasploit Community CTF
Spencer McIntyre

Products and Tools
Kubernetes Guardrails: Bringing DevOps and Security Together on Cloud
Alon Berger

Exposure Management
Deepfakes: A Nascent Cybersecurity Threat
Yotam Katz

Products and Tools
InsightCloudSec Supports 12 New AWS Services Announced at re:Invent
Chris DeRamus

Threat Research
Metasploit Wrap-Up: 12/3/21
Spencer McIntyre

Rapid7 Blog
Hacky Holidays From Rapid7! Announcing Our New Festive Blog Series
Jesse Mack
Cloud and Devops Security
OWASP Top 10 Deep Dive: Identification and Authentication Failures
Nathaniel Hierseman

Exposure Management
Ongoing Exploitation of Windows Installer CVE-2021-41379
Glenn Thorpe

Exposure Management
Active Exploitation of Apache HTTP Server CVE-2021-40438
Caitlin Condon