The Rapid7 Blog:
Your Signal in the Security Noise
Insights, stories, and guidance from our global security and research teams.
Featured posts
3723 Results

Industry Trends
The Top Threat Actors Targeting Financial Services Organizations
Itay Kozuch

Rapid7 Blog
Analysis of the Ticketmaster Breach
Rapid7

Exposure Management
Address the NAIC Insurance Data Security Model Law
Eric Sun
Exposure Management
Scan Management with InsightAppSec: There’s More to Application Security than Long Lists of Vulnerabilities
Mark Hamill

Rapid7 Blog
A Tale of Security Summer Camp: Rapid7's 2018 Recap of Black Hat and Beyond
Gwen Betts
Exposure Management
Patch Tuesday - August 2018
Greg Wiseman

Detection and Response
CIS Critical Security Control 19: Steps for Crafting an Efficient Incident Response and Management Strategy
Christy Draicchio

Products and Tools
Metasploit Wrapup 8/10/18
James Barnett

Exposure Management
CIS Critical Security Control 18: Breaking Down the Control Chaos of Application Software Security
Rapid7

Products and Tools
Metasploit Wrapup 8/3/18
Wei Chen

Exposure Management
Major Carding Site Replacement: How Altenen.nz Rose From the Ashes of Altenen.com
Orin Mor

Exposure Management
CIS Critical Security Control 17: Some Assembly Required for Your Security Awareness and Training Program
Brian Carey
Products and Tools
Metasploit Wrapup: 7/27/18
Aaron Soto

Detection and Response
Q&A with Rebekah Brown, Rapid7 Threat Intel Lead, on Attacker Behavior Analytics
Christie Ott

Rapid7 Blog
Beyond RASP Security
Rapid7
Products and Tools
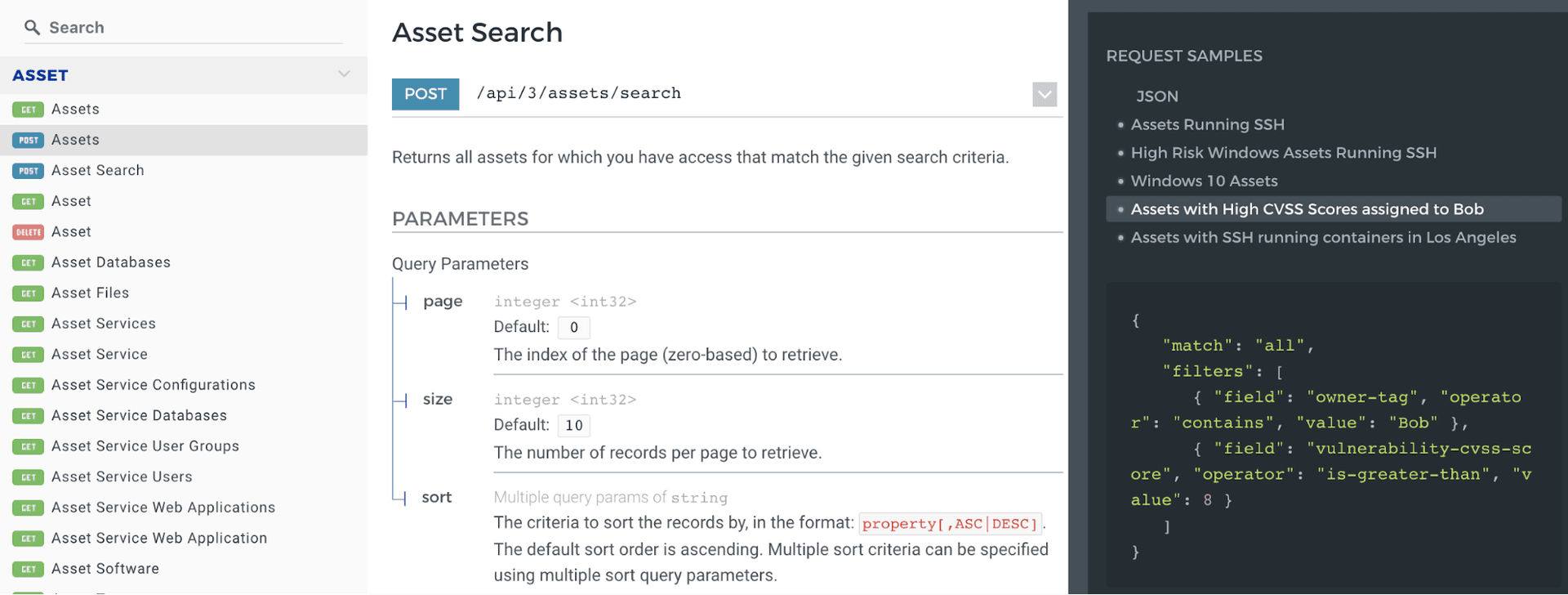
Your Guide to InsightVM’s RESTful API
Justin Prince

Threat Research
Digital Footprints, Breadcrumbs, and How Hackers Exploit Them
Ariel Ainhoren

Exposure Management
Under the Hoodie 2018: Lessons from a Season of Penetration Testing
Tod Beardsley

Products and Tools
Metasploit Wrapup: 7/20/18
Jacob Robles
Products and Tools
MAC Address Tracker: Generating a Network Inventory Database Using Network Traffic Analysis
Rapid7

Exposure Management
Password Tips from a Pen Tester: What is Your Company’s Default Password?
Patrick Laverty